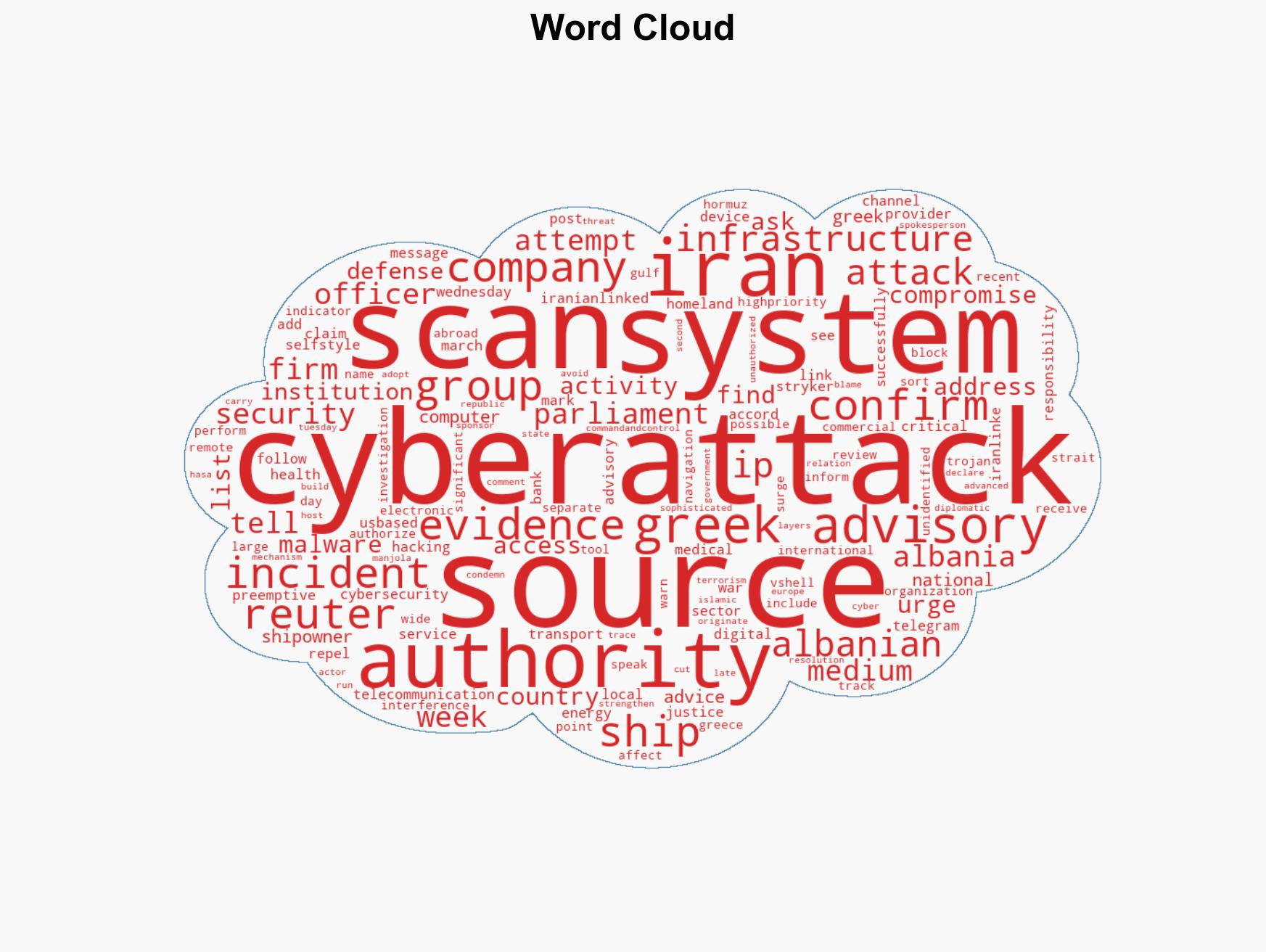
Greek Companies Conduct Cybersecurity Scans Amid Heightened Threats Linked to Iran Conflict
Published on: 2026-03-18
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Greek Firms Scan Computer Systems as Iran War Raises Cyberattack Risks Sources Say
1. BLUF (Bottom Line Up Front)
Greek companies are proactively scanning their computer systems for cyber threats linked to Iranian actors, following advisories from the National Cybersecurity Authority. This action is in response to recent cyber incidents attributed to Iran-linked groups. The situation poses a moderate risk to critical sectors, including shipping and telecommunications, with moderate confidence in the assessment due to limited direct evidence of significant attacks on Greek infrastructure.
2. Competing Hypotheses
- Hypothesis A: Iranian-linked groups are actively targeting Greek and regional infrastructure as part of a broader cyber campaign. Evidence includes recent advisories and confirmed attacks on U.S. and Albanian entities. However, direct evidence of significant attacks on Greek infrastructure remains limited.
- Hypothesis B: The increased cyber vigilance is primarily precautionary, with no immediate threat to Greek infrastructure. The advisory may be a response to regional tensions and previous incidents rather than current, direct threats to Greece.
- Assessment: Hypothesis A is currently better supported due to the pattern of regional cyber activities linked to Iranian actors and the issuance of high-priority advisories. Indicators such as confirmed breaches in neighboring countries could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Iranian-linked groups are capable of targeting Greek infrastructure; Greek cybersecurity measures are currently effective; regional tensions are influencing cyber threat levels.
- Information Gaps: Detailed evidence of cyber activities targeting Greek systems; specific motivations behind Iran-linked cyber operations.
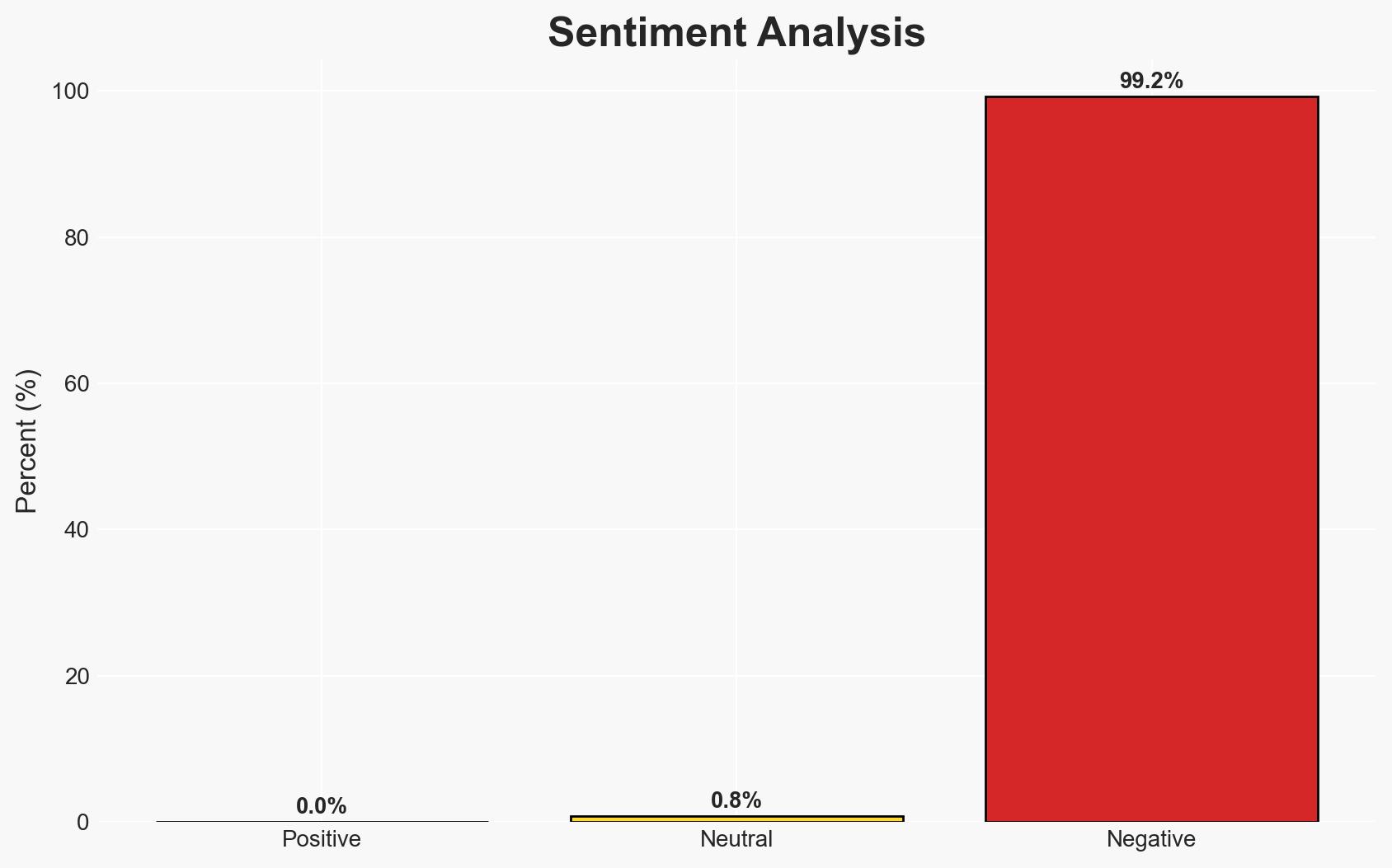
- Bias & Deception Risks: Potential bias in attributing cyber activities to Iranian actors without conclusive evidence; risk of overestimating threat based on regional tensions.
4. Implications and Strategic Risks
The ongoing cyber vigilance in Greece may lead to increased cybersecurity measures across critical sectors, influencing regional cyber defense strategies.
- Political / Geopolitical: Potential escalation in regional cyber tensions, impacting diplomatic relations, particularly with Iran.
- Security / Counter-Terrorism: Heightened alert could improve readiness but also strain resources if threats are not substantiated.
- Cyber / Information Space: Increased focus on cyber defense could lead to enhanced capabilities but also provoke retaliatory cyber actions.
- Economic / Social: Potential disruptions in sectors like shipping and telecommunications could affect economic stability and public confidence.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of critical infrastructure, share threat intelligence with regional partners, and conduct cybersecurity drills.
- Medium-Term Posture (1–12 months): Develop resilience measures, strengthen international cybersecurity partnerships, and invest in advanced threat detection technologies.
- Scenario Outlook:
- Best: No significant attacks occur, and regional tensions de-escalate.
- Worst: Successful cyberattacks disrupt critical sectors, leading to economic and political instability.
- Most-Likely: Continued cyber vigilance with sporadic, low-impact incidents.
6. Key Individuals and Entities
- National Cybersecurity Authority (Greece)
- Homeland Justice Group (Iran-linked)
- Greek shipping companies
- Albanian government
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, Iran-linked cyber threats, national security, critical infrastructure, regional tensions, cyber defense, maritime security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us