APT28 Hackers Target Ukrainian Government Using Zimbra Vulnerability for Remote Code Execution Attacks
Published on: 2026-03-19
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Russian hackers exploit Zimbra flaw in Ukrainian govt attacks
1. BLUF (Bottom Line Up Front)
APT28, a Russian state-backed group, is exploiting a Zimbra vulnerability to target Ukrainian government entities, notably the State Hydrology Agency. This campaign, leveraging a high-severity flaw, poses significant risks to Ukrainian critical infrastructure. The most likely hypothesis is that this is part of a broader Russian cyber strategy against Ukraine. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
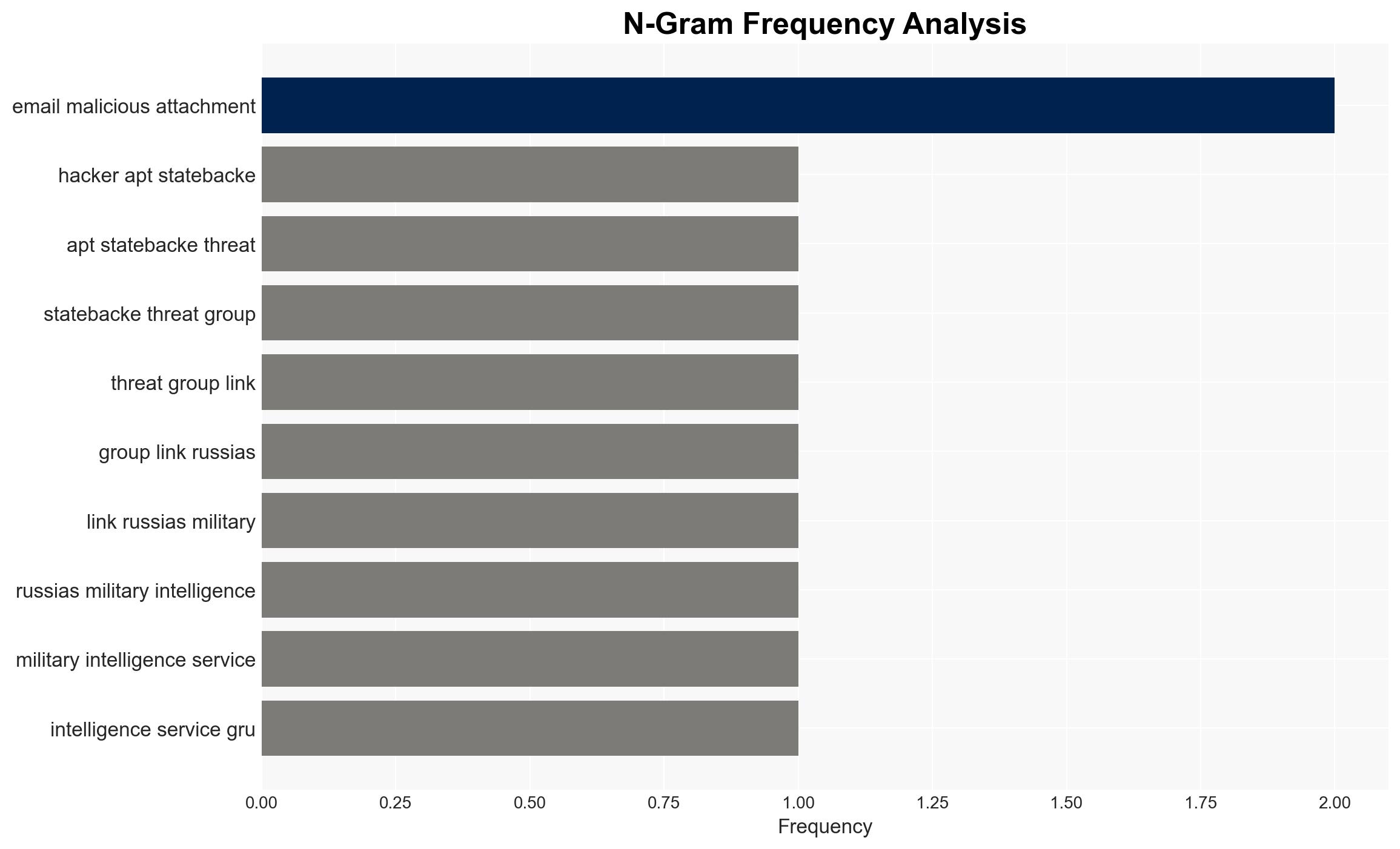
- Hypothesis A: APT28’s exploitation of the Zimbra flaw is a targeted operation to disrupt Ukrainian government operations and gather intelligence. This is supported by the specific targeting of critical infrastructure and the use of sophisticated phishing tactics. However, the full extent of the campaign’s objectives remains unclear.
- Hypothesis B: The exploitation is part of a broader, opportunistic campaign by Russian state-backed groups to exploit known vulnerabilities globally, with Ukraine being one of many targets. This is supported by historical patterns of Russian cyber operations. Contradicting this is the focused nature of the current campaign on Ukrainian entities.
- Assessment: Hypothesis A is currently better supported due to the targeted nature of the attacks on Ukrainian critical infrastructure. Indicators such as increased cyber activity against Ukraine or similar tactics used in other regions could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: APT28 is acting under Russian state directives; the Zimbra vulnerability is not yet fully patched across all Ukrainian government systems; the campaign is primarily intelligence-gathering.
- Information Gaps: Detailed objectives of the campaign; the full scope of affected entities; potential undisclosed vulnerabilities being exploited.
- Bias & Deception Risks: Potential bias in attributing the attack solely to APT28 without considering other actors; reliance on open-source reports which may be incomplete or influenced by reporting entities.
4. Implications and Strategic Risks
This development could exacerbate tensions between Ukraine and Russia, potentially leading to increased cyber and kinetic confrontations. It may also prompt NATO and allied countries to bolster cyber defenses and support for Ukraine.
- Political / Geopolitical: Escalation in cyber hostilities could lead to broader geopolitical tensions and influence diplomatic engagements.
- Security / Counter-Terrorism: Increased cyber threat level for Ukrainian and allied infrastructure, necessitating enhanced security measures.
- Cyber / Information Space: Potential for further cyber operations targeting NATO-aligned entities, leveraging similar vulnerabilities.
- Economic / Social: Disruption of critical infrastructure could have cascading effects on economic stability and public trust in government systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently patch Zimbra vulnerabilities across all critical systems; increase monitoring for similar phishing campaigns; enhance information sharing with international partners.
- Medium-Term Posture (1–12 months): Develop resilience measures including regular security audits; strengthen partnerships with cybersecurity agencies; invest in cyber defense capabilities.
- Scenario Outlook:
- Best: Successful mitigation of vulnerabilities and no further significant breaches.
- Worst: Escalation of cyber attacks leading to significant disruption of critical infrastructure.
- Most-Likely: Continued cyber skirmishes with periodic breaches mitigated by improved defenses.
6. Key Individuals and Entities
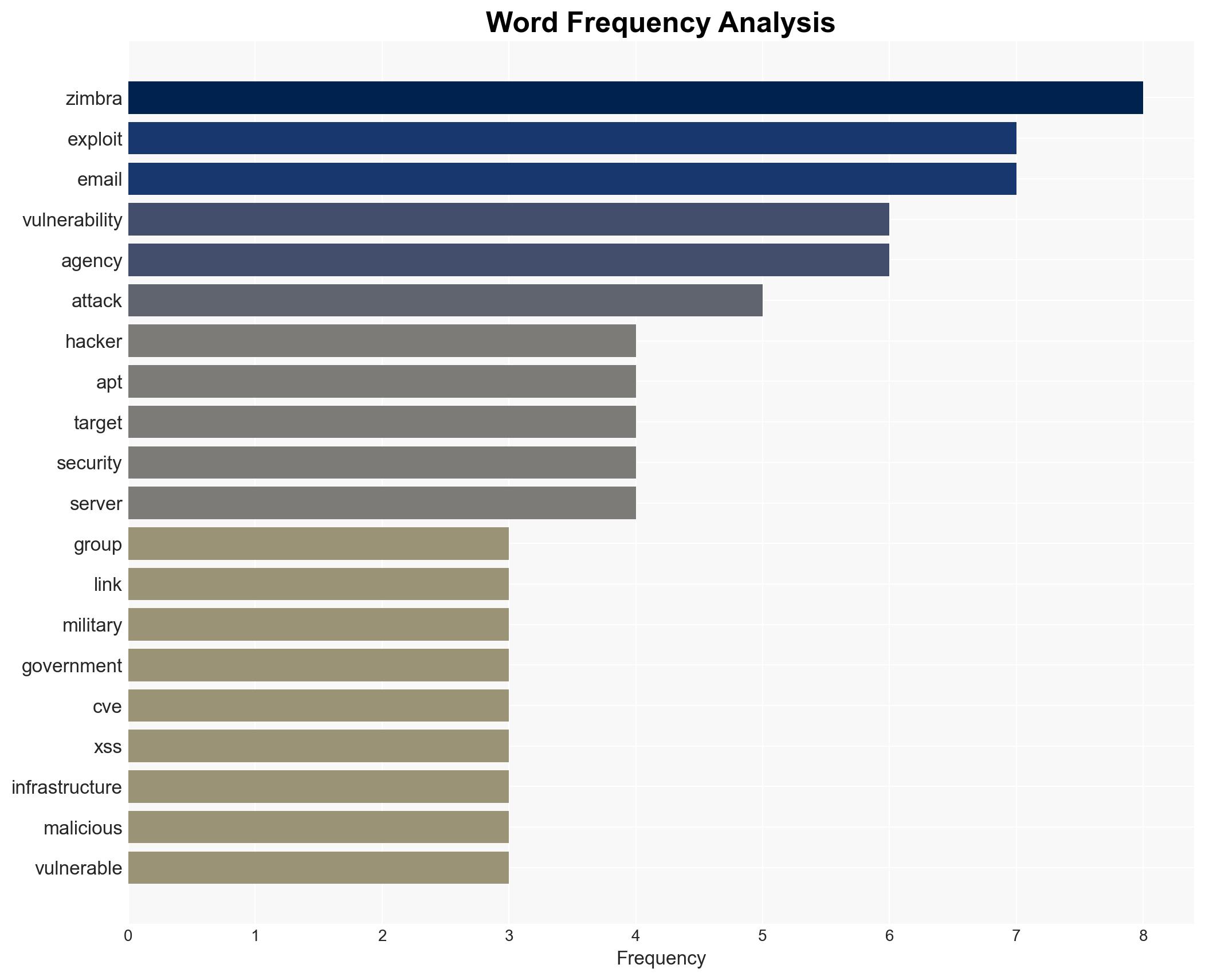
- APT28 (Fancy Bear, Strontium)
- Ukrainian State Hydrology Agency
- Cybersecurity and Infrastructure Security Agency (CISA)
- Seqrite Labs
- Federal Civilian Executive Branch (FCEB) agencies
7. Thematic Tags
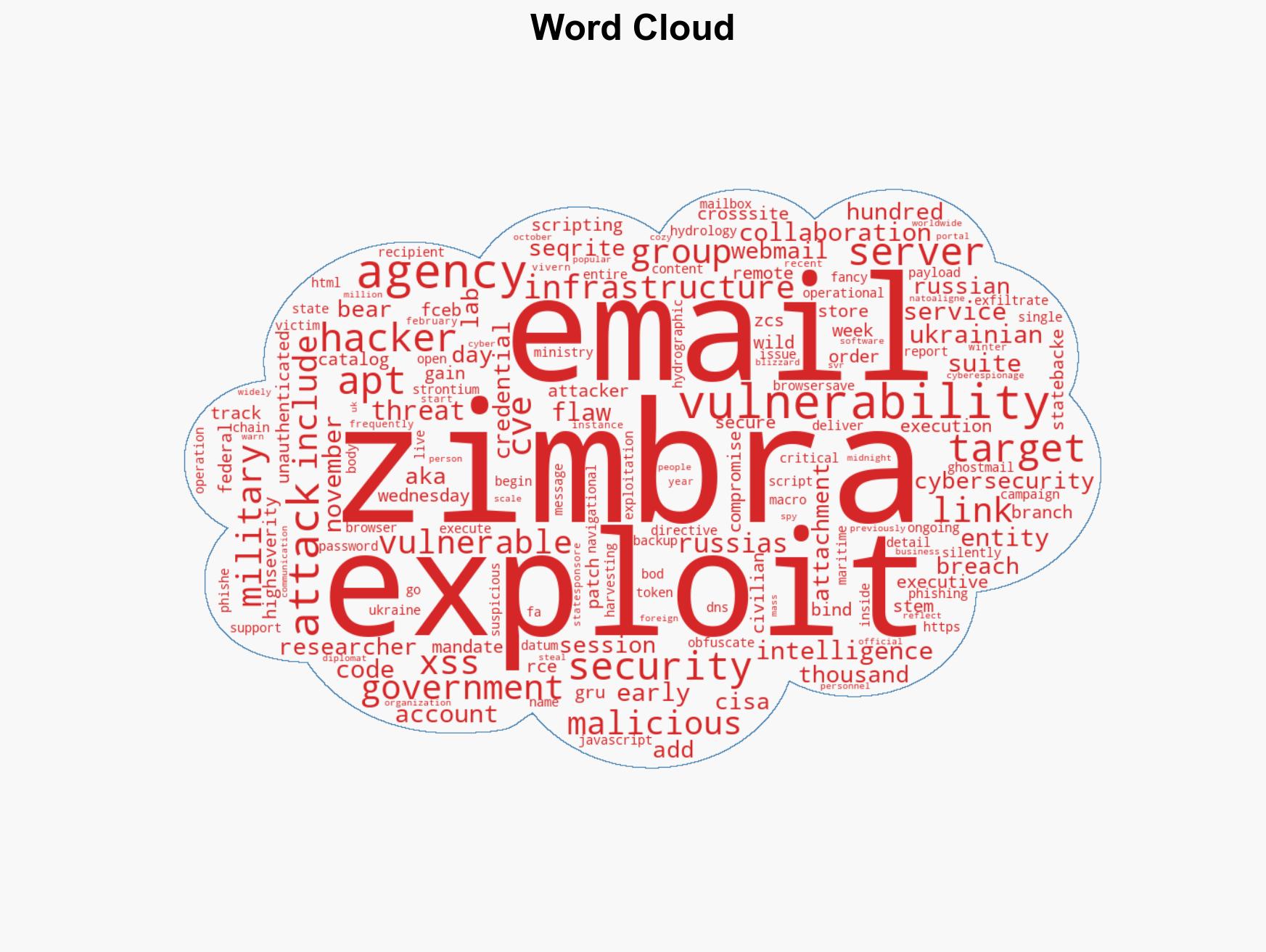
cybersecurity, cyber-espionage, Russian state-sponsored hacking, critical infrastructure, Ukraine-Russia conflict, cybersecurity vulnerabilities, phishing campaigns, intelligence gathering
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us