CISA advises U.S. organizations to enhance Microsoft Intune security following Stryker cyberattack
Published on: 2026-03-19
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: CISA urges US orgs to secure Microsoft Intune systems after Stryker breach
1. BLUF (Bottom Line Up Front)
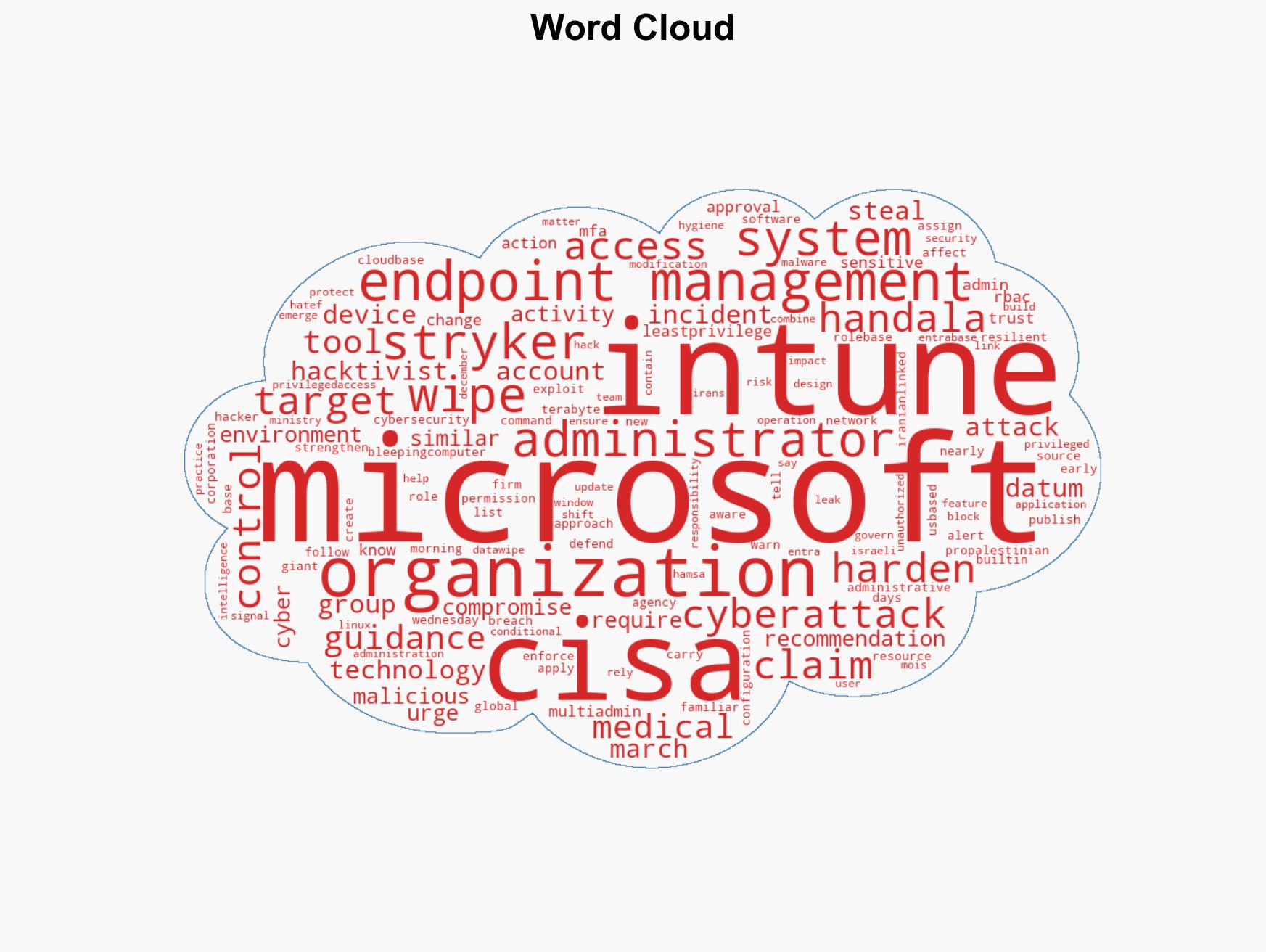
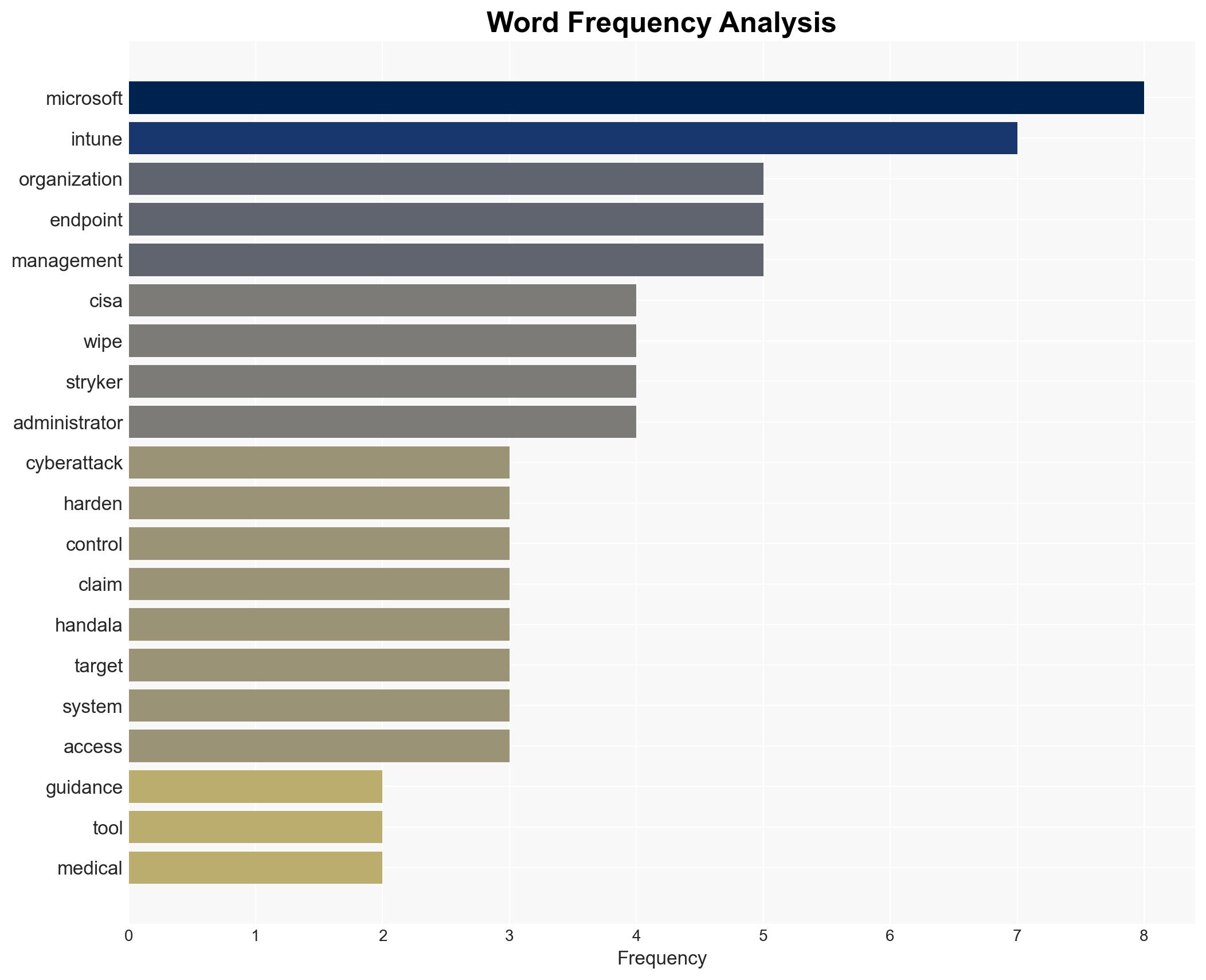
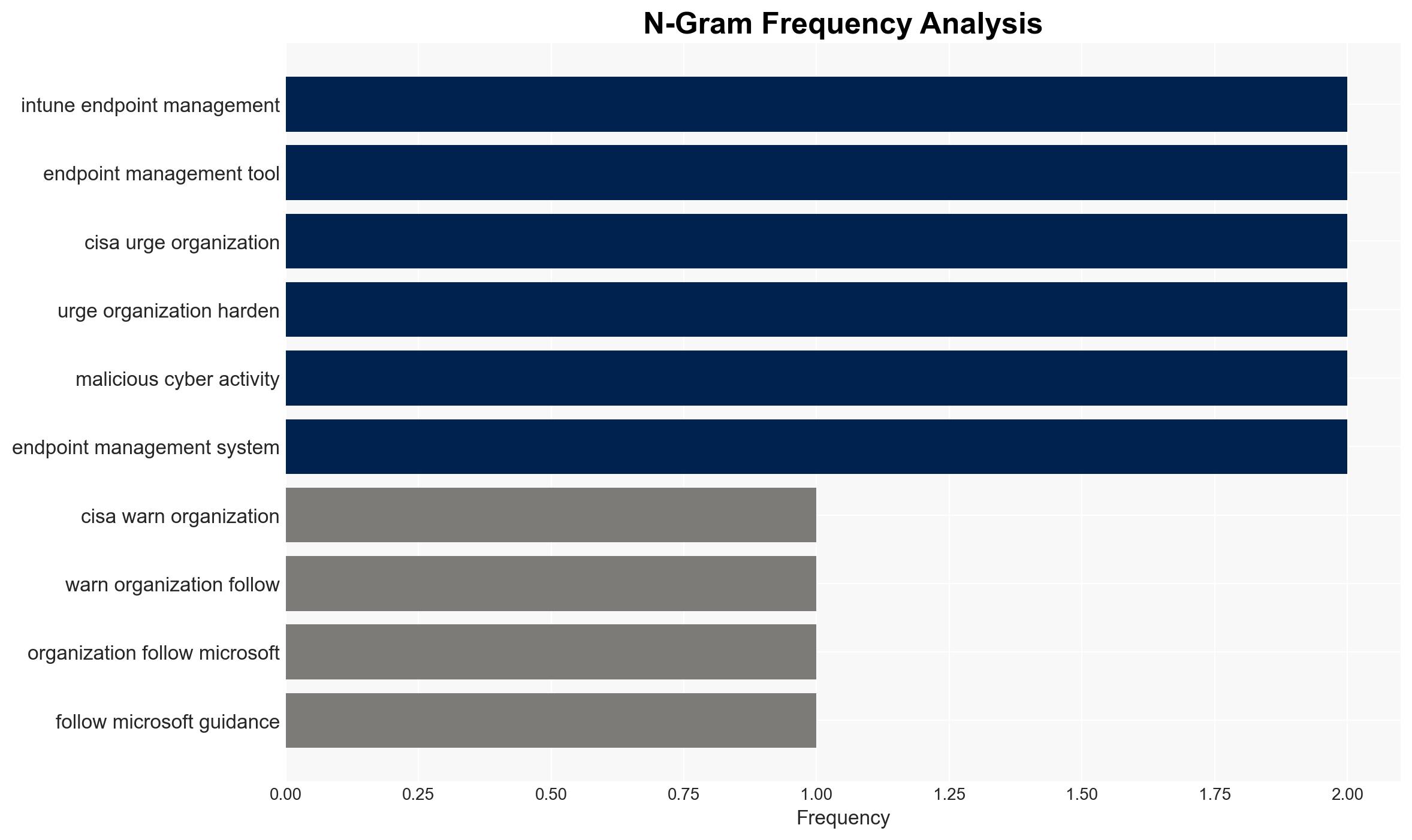
The recent cyberattack on Stryker Corporation, attributed to the Iranian-linked hacktivist group Handala, exploited vulnerabilities in Microsoft’s Intune endpoint management system. CISA has issued guidance for U.S. organizations to enhance their cybersecurity posture. The most likely hypothesis is that this attack is part of a broader campaign targeting U.S. infrastructure, with moderate confidence in this assessment due to the group’s known affiliations and past activities.
2. Competing Hypotheses
- Hypothesis A: The attack on Stryker is an isolated incident aimed at disrupting a specific U.S. company for financial or ideological reasons. Supporting evidence includes the targeted nature of the attack and the specific use of data-wiping malware. However, the group’s broader targeting history suggests a more strategic intent.
- Hypothesis B: The attack is part of a coordinated campaign by Handala, potentially supported by Iranian state actors, to disrupt U.S. critical infrastructure. This is supported by the group’s known affiliations and the sophisticated nature of the attack. Contradicting evidence includes the lack of direct state attribution and the hacktivist group’s typical focus on ideological targets.
- Assessment: Hypothesis B is currently better supported due to the group’s history and the strategic implications of targeting a major U.S. medical technology firm. Key indicators that could shift this judgment include further attacks on similar targets or evidence of state sponsorship.
3. Key Assumptions and Red Flags
- Assumptions: The attack was conducted by Handala; Microsoft Intune vulnerabilities were the primary vector; CISA’s guidance will mitigate similar future attacks; Handala has links to Iranian state actors.
- Information Gaps: Specific technical details of the exploit; confirmation of data exfiltration extent; direct evidence of state sponsorship.
- Bias & Deception Risks: Potential bias in attributing the attack to state actors without conclusive evidence; reliance on open-source information may omit classified insights.
4. Implications and Strategic Risks
This development could lead to increased cybersecurity measures across U.S. organizations, potentially escalating cyber tensions between the U.S. and Iran. It may also prompt further hacktivist activities targeting U.S. infrastructure.
- Political / Geopolitical: Potential for heightened U.S.-Iran tensions and retaliatory cyber actions.
- Security / Counter-Terrorism: Increased threat to U.S. critical infrastructure from hacktivist groups.
- Cyber / Information Space: Emphasis on hardening endpoint management systems and improving cyber hygiene.
- Economic / Social: Potential economic impact on targeted firms and increased public concern over cybersecurity.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Implement CISA’s recommendations, enhance monitoring of endpoint management systems, and conduct vulnerability assessments.
- Medium-Term Posture (1–12 months): Develop partnerships for information sharing, invest in cybersecurity training, and strengthen incident response capabilities.
- Scenario Outlook: Best: Improved cybersecurity posture deters future attacks. Worst: Escalation of cyberattacks on U.S. infrastructure. Most-Likely: Continued sporadic attacks with incremental improvements in defenses.
6. Key Individuals and Entities
- Handala (Hacktivist Group)
- Stryker Corporation (U.S.-based Medical Technology Firm)
- Microsoft (Technology Company)
- CISA (U.S. Cybersecurity and Infrastructure Security Agency)
7. Thematic Tags
cybersecurity, hacktivism, U.S.-Iran relations, endpoint management, cyber defense, data breach, critical infrastructure
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us