U.S. and Allies Dismantle Major IoT Botnets Linked to Record DDoS Attacks and Extortion Schemes
Published on: 2026-03-20
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
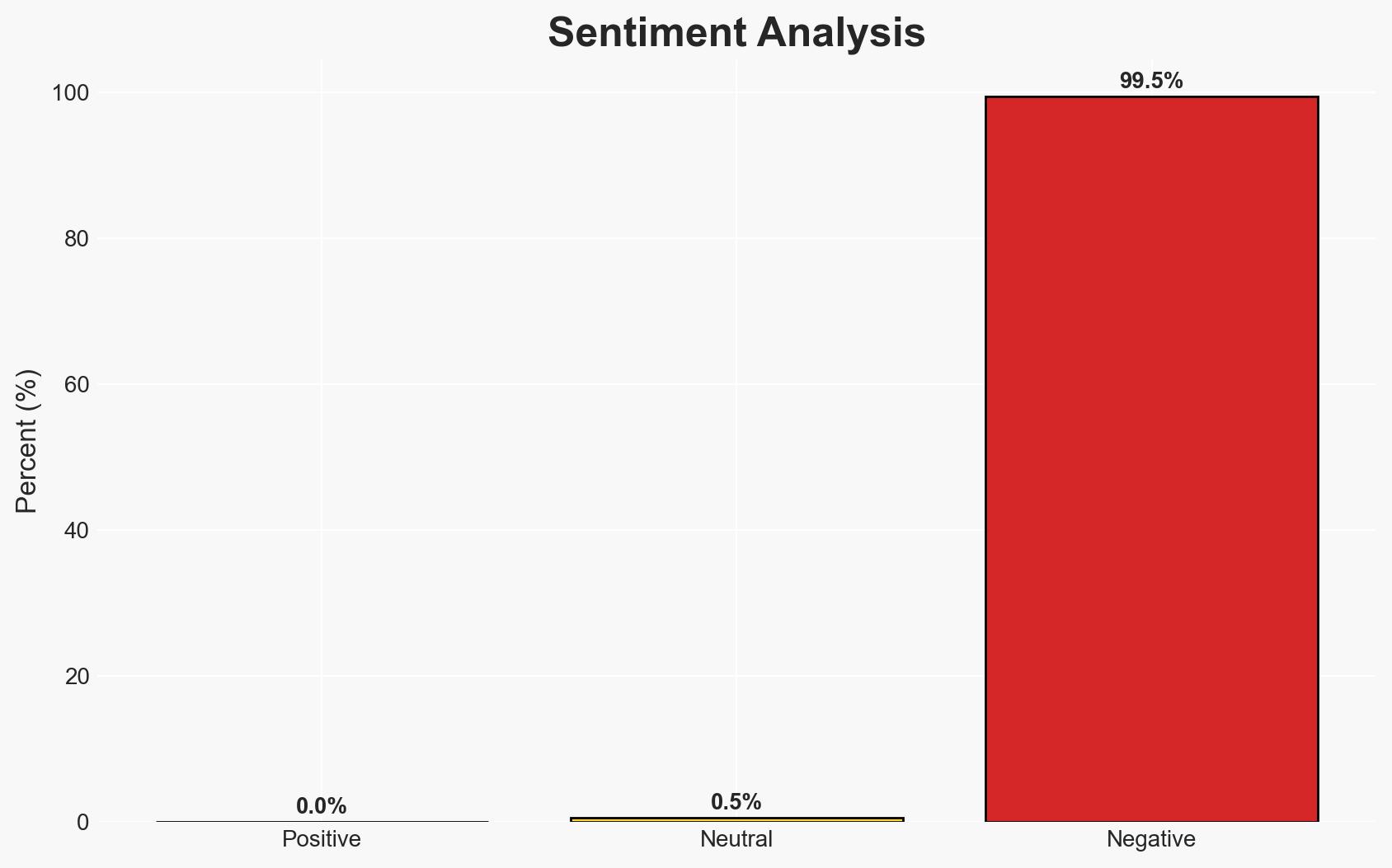
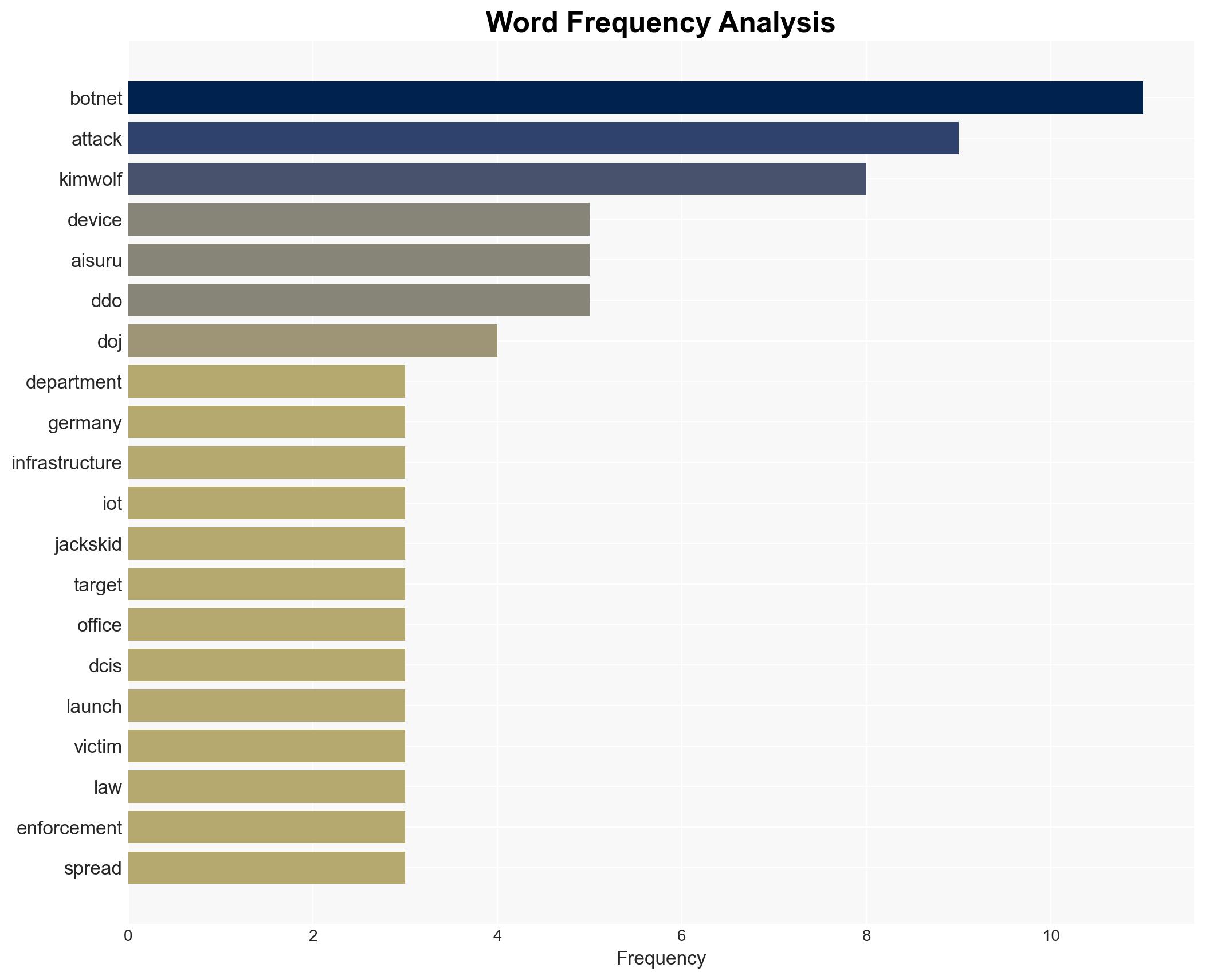
Intelligence Report: Feds Disrupt IoT Botnets Behind Huge DDoS Attacks
1. BLUF (Bottom Line Up Front)
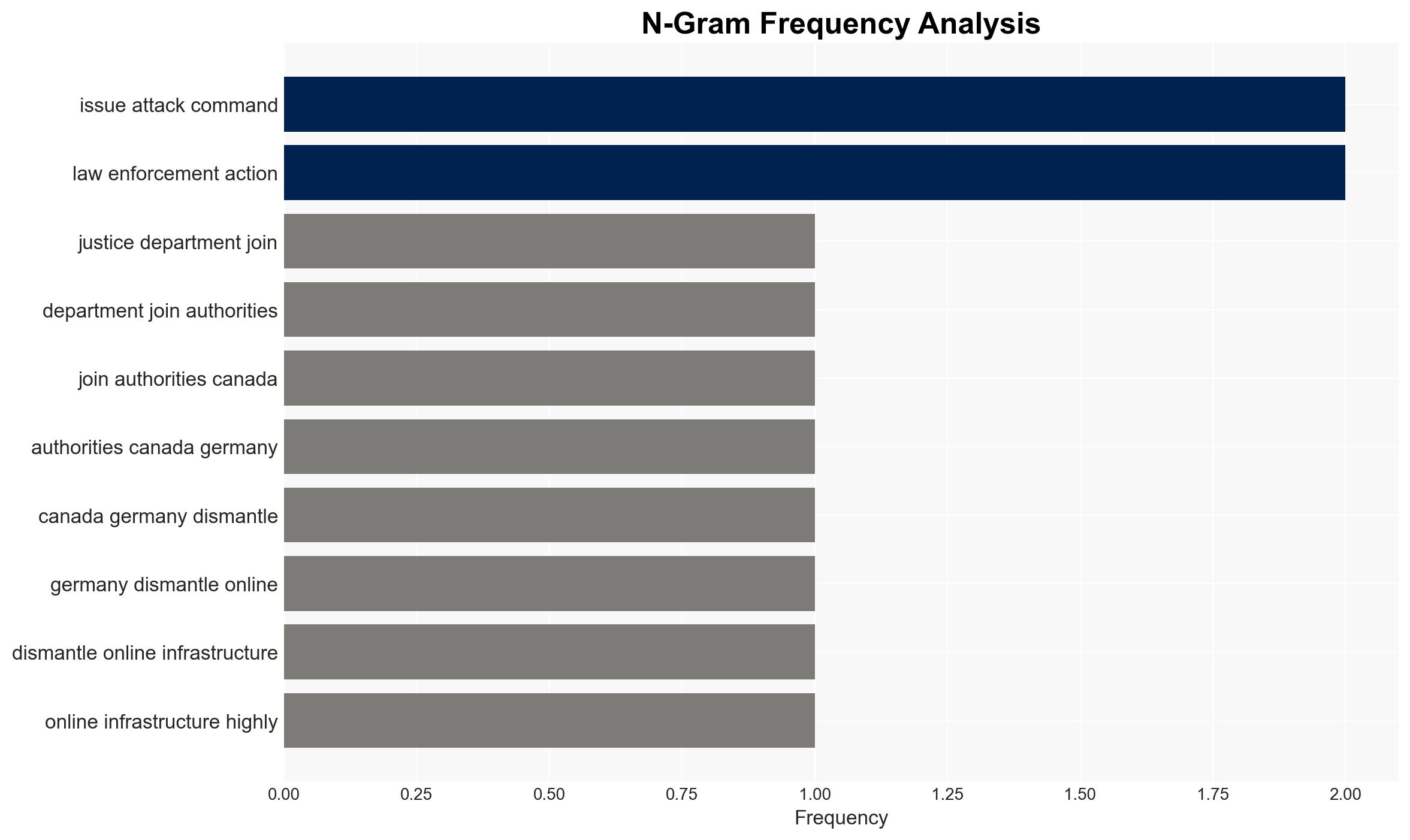
The U.S. Justice Department, in collaboration with Canadian and German authorities, dismantled the infrastructure of four IoT botnets responsible for extensive DDoS attacks. This action significantly reduces the immediate threat posed by these botnets, though the emergence of similar threats remains a concern. The operation highlights the importance of international cooperation in cyber defense. Overall confidence in this assessment is moderate due to potential information gaps regarding the botnet operators and their future capabilities.
2. Competing Hypotheses
- Hypothesis A: The dismantling of the botnets will significantly reduce the frequency and impact of DDoS attacks in the near term. This is supported by the seizure of critical infrastructure and international cooperation. However, uncertainties remain about the operators’ ability to regroup or launch new botnets.
- Hypothesis B: The disruption is temporary, and similar or more sophisticated botnets will soon emerge, potentially using the same or improved techniques. This is supported by the historical pattern of rapid adaptation by cybercriminals and the disclosure of vulnerabilities that could be exploited by others.
- Assessment: Hypothesis A is currently better supported due to the immediate impact of the infrastructure seizure and the involvement of multiple international law enforcement agencies. However, indicators such as the emergence of new botnets or reports of similar attacks could shift this judgment towards Hypothesis B.
3. Key Assumptions and Red Flags
- Assumptions: The operators of the botnets lack the immediate capability to reconstitute their infrastructure; international cooperation will continue to be effective; IoT device vulnerabilities will not be rapidly exploited by new actors.
- Information Gaps: Identities and capabilities of the botnet operators; potential undisclosed vulnerabilities in IoT devices; the full scope of international law enforcement actions.
- Bias & Deception Risks: Potential over-reliance on official statements without independent verification; possibility of misinformation from botnet operators to mislead law enforcement.
4. Implications and Strategic Risks
This development could lead to a temporary decrease in DDoS attacks but may also incentivize cybercriminals to develop more resilient botnets. The disruption may also prompt increased scrutiny and regulation of IoT security standards.
- Political / Geopolitical: Strengthens international cyber cooperation frameworks; potential diplomatic tensions if botnet operators are linked to state actors.
- Security / Counter-Terrorism: Reduces immediate DDoS threat to critical infrastructure but highlights ongoing vulnerabilities in IoT devices.
- Cyber / Information Space: May lead to increased investment in IoT security and the development of new defensive technologies.
- Economic / Social: Potential reduction in economic losses from DDoS attacks; increased public awareness and demand for secure IoT devices.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of IoT networks for signs of new botnet activity; engage with international partners to share intelligence and best practices.
- Medium-Term Posture (1–12 months): Develop and implement IoT security standards; foster public-private partnerships to improve cyber resilience.
- Scenario Outlook:
- Best: Sustained reduction in DDoS attacks due to improved IoT security and international cooperation.
- Worst: Emergence of more sophisticated botnets exploiting new vulnerabilities.
- Most-Likely: Temporary reduction in attacks with gradual re-emergence of similar threats.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
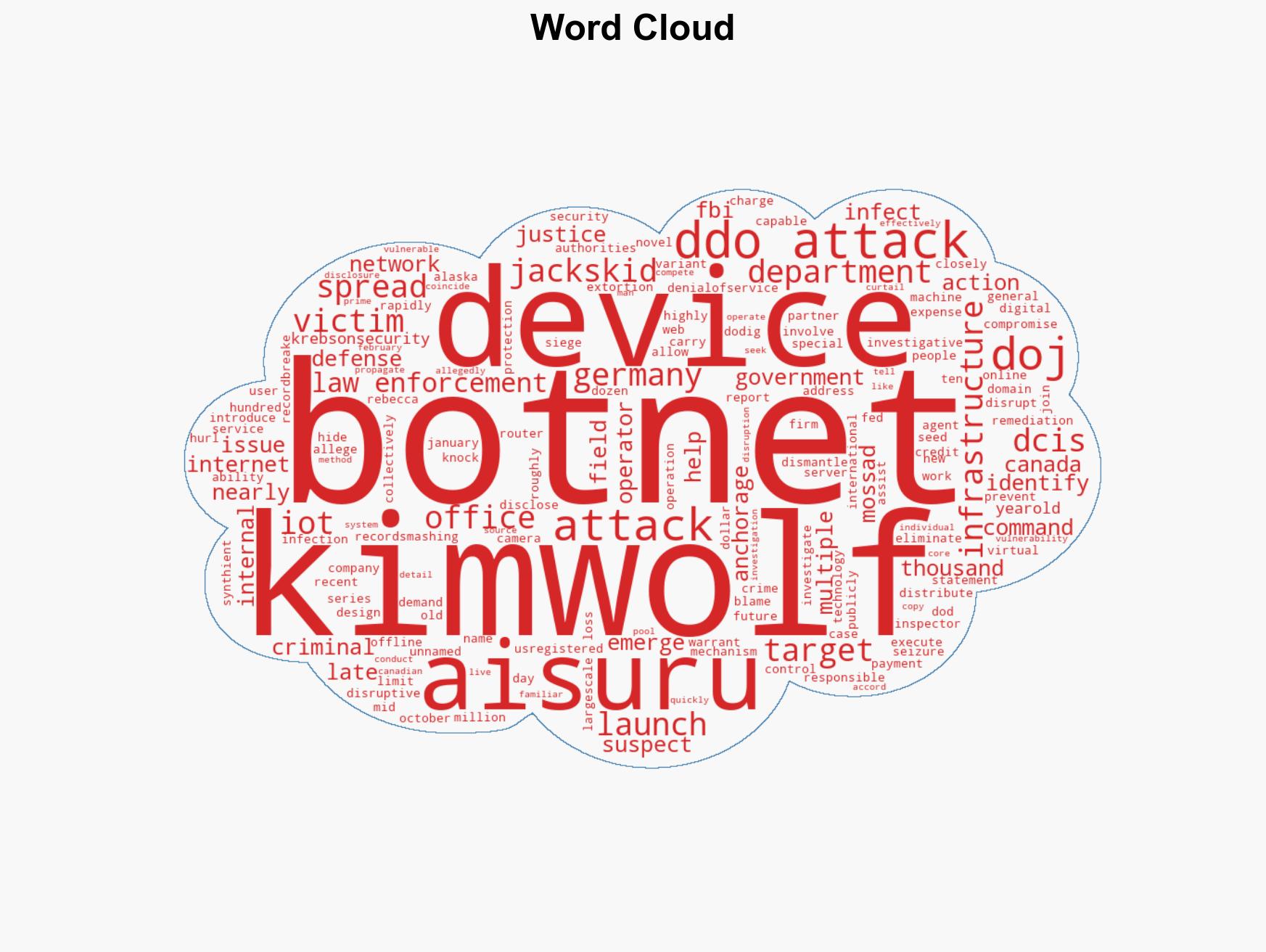
cybersecurity, international cooperation, IoT vulnerabilities, DDoS attacks, law enforcement, cybercrime, infrastructure protection
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us