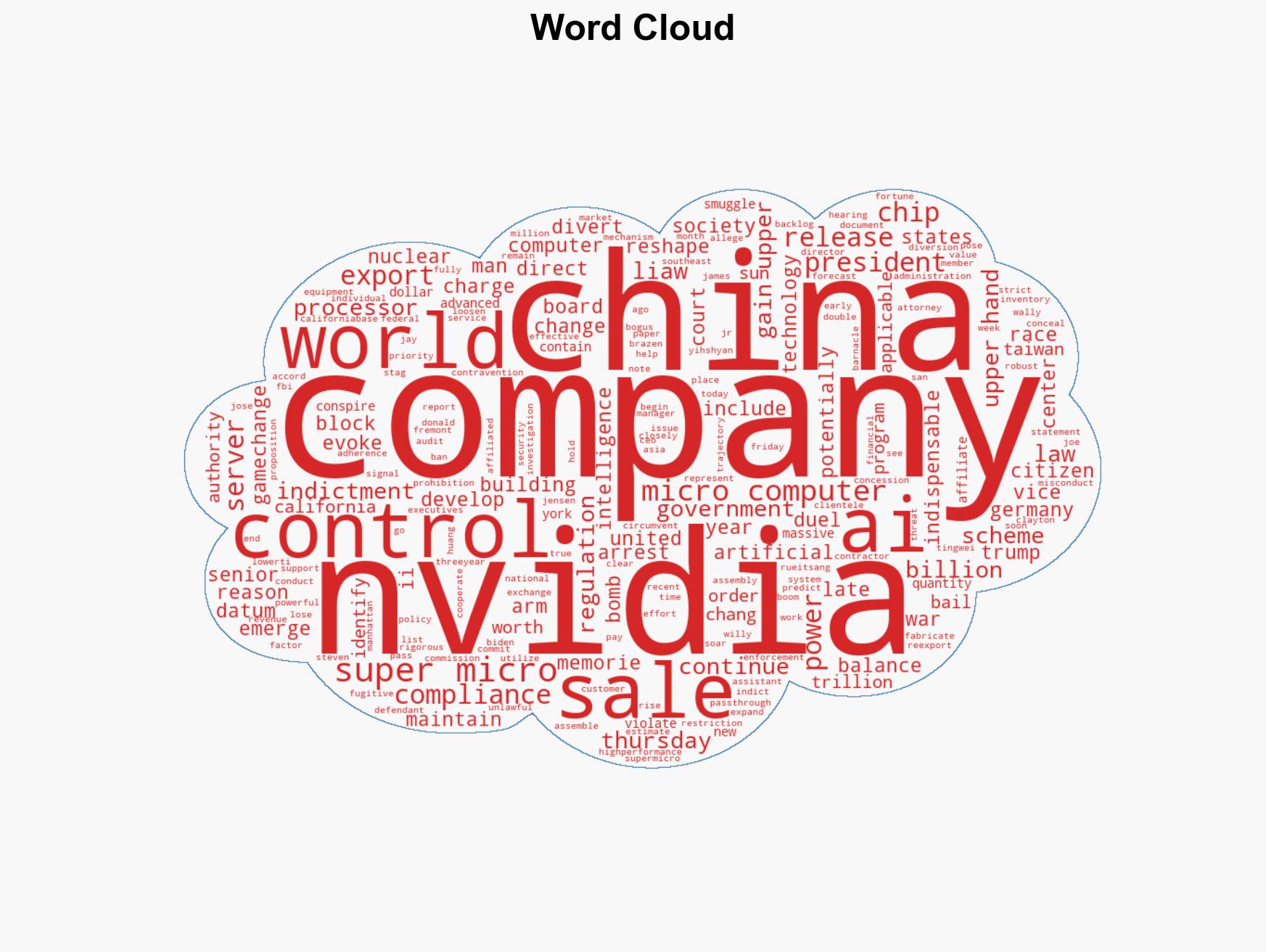
Three individuals indicted for allegedly plotting to illegally export advanced AI servers to China
Published on: 2026-03-20
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: 3 men are charged with conspiring to smuggle US artificial intelligence to China
1. BLUF (Bottom Line Up Front)
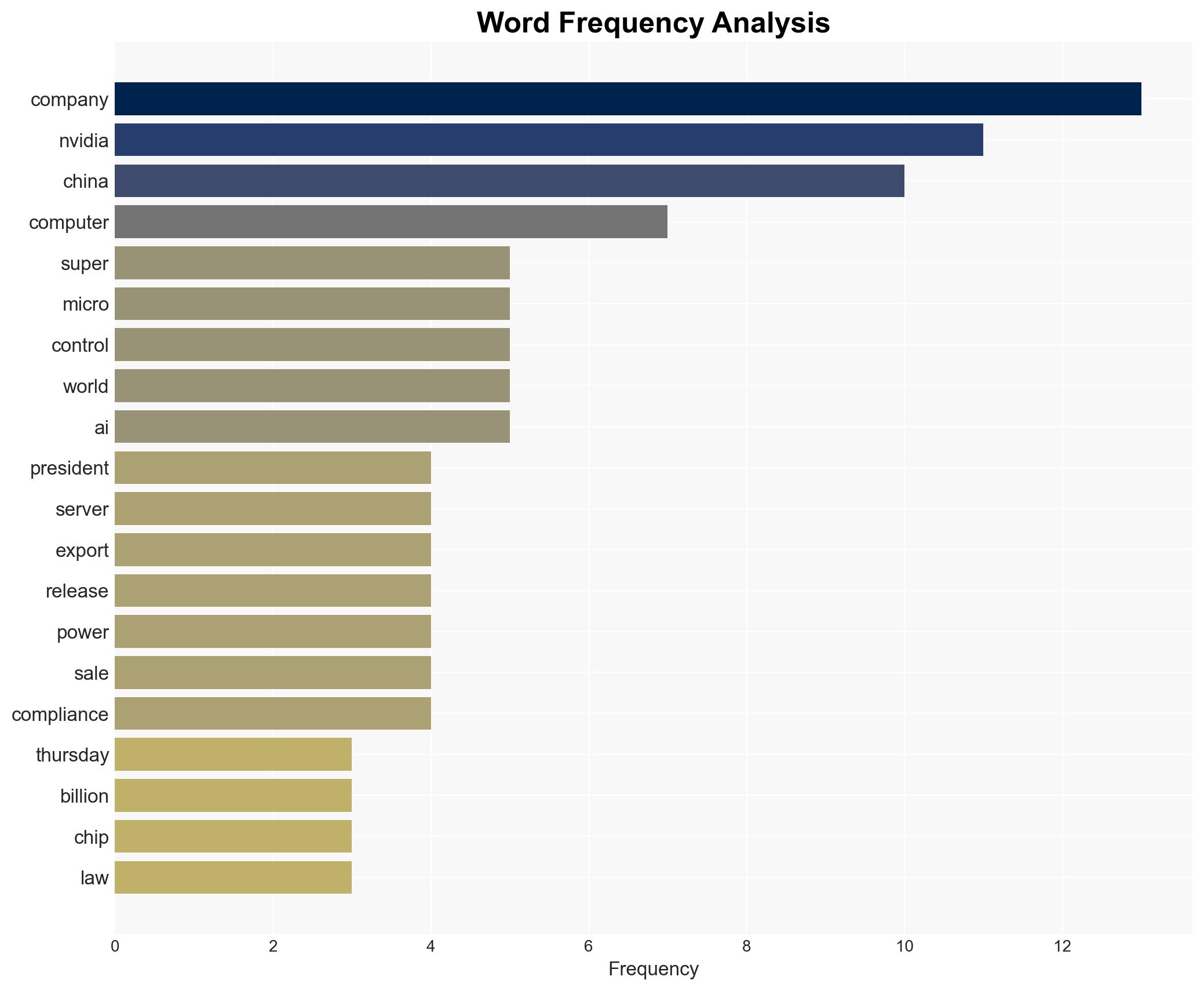
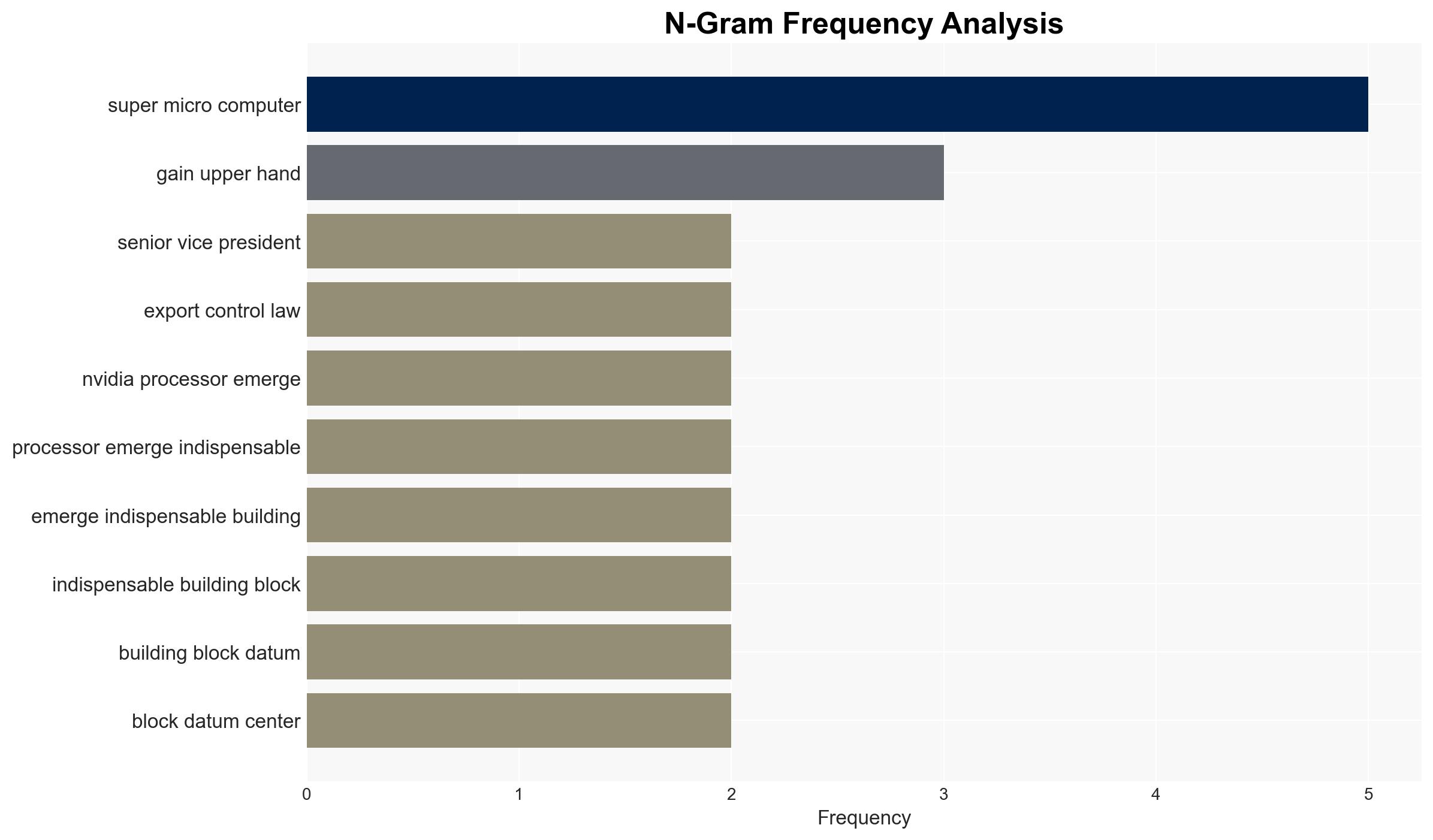
The arrest of three individuals associated with Super Micro Computer Inc. for allegedly conspiring to smuggle AI technology to China highlights significant vulnerabilities in U.S. export control enforcement. This incident underscores the strategic competition between the U.S. and China over AI dominance. The most likely hypothesis is that this was a deliberate attempt to bypass U.S. export restrictions, posing a direct threat to national security. Overall confidence in this assessment is moderate, given the ongoing investigation and potential for new evidence.
2. Competing Hypotheses
- Hypothesis A: The individuals involved intentionally conspired to smuggle AI technology to China to circumvent U.S. export controls. Supporting evidence includes the use of fabricated documents and a pass-through company to conceal activities. However, uncertainties remain about the full extent of the network and potential state involvement.
- Hypothesis B: The actions were part of a rogue operation by individuals seeking personal gain, without broader organizational or state backing. This is less supported due to the scale of the operation and the strategic importance of the technology involved.
- Assessment: Hypothesis A is currently better supported due to the organized nature of the scheme and the strategic implications of the technology involved. Key indicators that could shift this judgment include evidence of state sponsorship or broader corporate complicity.
3. Key Assumptions and Red Flags
- Assumptions: The individuals acted with knowledge of export control laws; the technology in question is critical to AI development; the scheme was primarily motivated by strategic rather than financial goals.
- Information Gaps: Details on the involvement of Chinese entities or government; the full scope of the smuggling network; potential internal company complicity.
- Bias & Deception Risks: Potential bias in interpreting the strategic intent of the individuals; risk of deception in the documents and statements provided by the accused.
4. Implications and Strategic Risks
This development could exacerbate U.S.-China tensions over technology transfer and export controls, potentially leading to stricter regulations and enforcement measures. It may also prompt increased scrutiny of U.S. companies with ties to China.
- Political / Geopolitical: Potential for diplomatic friction and retaliatory measures by China.
- Security / Counter-Terrorism: Increased focus on protecting critical technology sectors from espionage.
- Cyber / Information Space: Heightened risk of cyber operations targeting U.S. tech firms for sensitive data.
- Economic / Social: Possible impact on U.S. tech sector’s global competitiveness and investor confidence.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of export activities, conduct a comprehensive audit of Super Micro Computer Inc., and increase inter-agency collaboration on export control enforcement.
- Medium-Term Posture (1–12 months): Develop resilience measures for critical tech sectors, strengthen partnerships with allies on export controls, and invest in counter-espionage capabilities.
- Scenario Outlook: Best: Strengthened export controls deter future incidents; Worst: Escalation in U.S.-China tech tensions; Most-Likely: Continued enforcement actions with incremental policy adjustments.
6. Key Individuals and Entities
- Yih-Shyan “Wally” Liaw, Senior Vice President, Super Micro Computer Inc.
- Ting-Wei “Willy” Sun, Contractor, Super Micro Computer Inc.
- Ruei-Tsang “Steven” Chang, Sales Manager, Super Micro Computer Inc. (fugitive)
- Super Micro Computer Inc.
7. Thematic Tags
national security threats, export controls, AI technology, U.S.-China relations, corporate espionage, national security, strategic competition, technology smuggling
Structured Analytic Techniques Applied
- Cognitive Bias Stress Test: Expose and correct potential biases in assessments through red-teaming and structured challenge.
- Bayesian Scenario Modeling: Use probabilistic forecasting for conflict trajectories or escalation likelihood.
- Network Influence Mapping: Map relationships between state and non-state actors for impact estimation.
Explore more:
National Security Threats Briefs ·
Daily Summary ·
Support us