Justice Department closes four websites linked to Iranian groups threatening dissidents and claiming hacks
Published on: 2026-03-20
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: DOJ says it shut down websites that threatened dissidents and took credit for hacks
1. BLUF (Bottom Line Up Front)
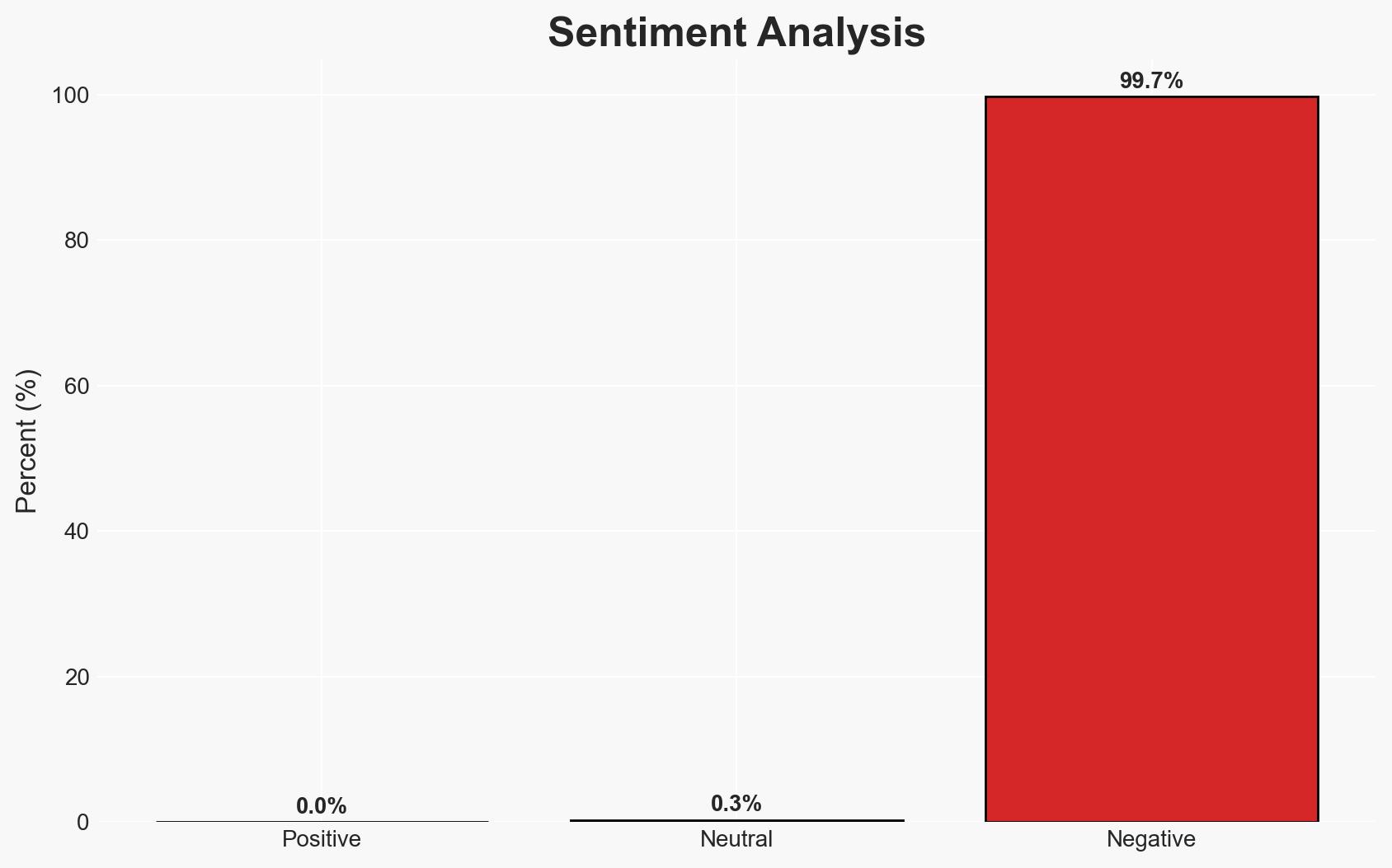
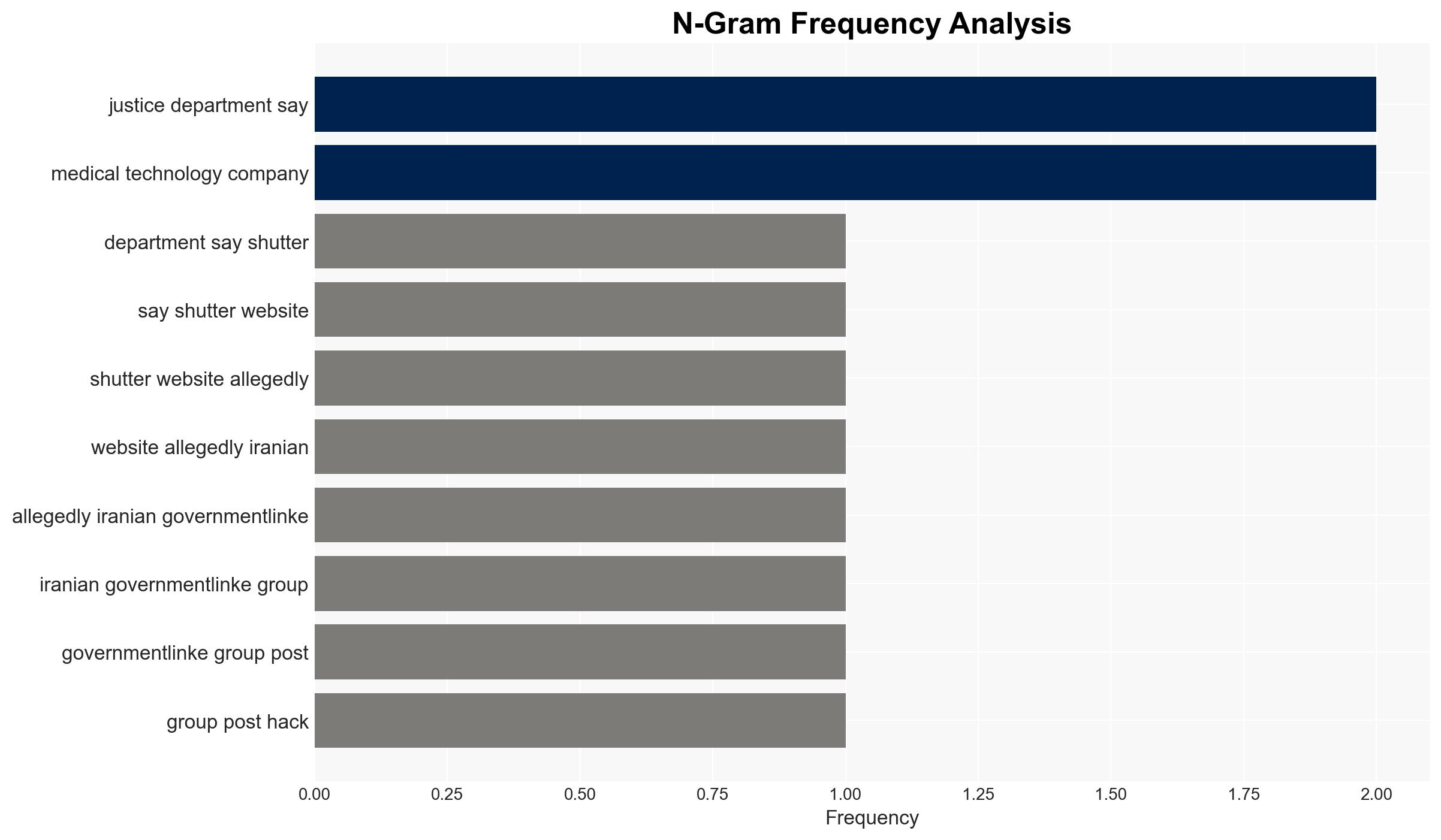
The U.S. Department of Justice has dismantled four websites allegedly used by Iranian government-linked groups for cyberattacks and psychological operations against regime critics. This action highlights ongoing cyber threats from Iran, potentially escalating tensions in the cyber domain. The most likely hypothesis is that these activities are state-sponsored efforts to intimidate dissidents and retaliate against perceived adversaries. Overall confidence in this judgment is moderate.
2. Competing Hypotheses
- Hypothesis A: The websites were part of a coordinated Iranian state-sponsored campaign to conduct cyber operations against dissidents and foreign adversaries. Supporting evidence includes the DOJ’s linking of these sites to Iranian intelligence and the use of similar tactics across multiple groups. However, the specific attribution to state actors remains partially circumstantial.
- Hypothesis B: The websites were operated by independent hacktivist groups with ideological alignment to Iranian state interests but without direct government control. This hypothesis is less supported due to the DOJ’s assertion of direct links to Iran’s Ministry of Intelligence and Security, although the possibility of proxy use cannot be entirely dismissed.
- Assessment: Hypothesis A is currently better supported due to the DOJ’s findings and the sophistication of the operations, which suggest state-level resources. Indicators that could shift this judgment include evidence of financial or operational independence of the groups from Iranian state structures.
3. Key Assumptions and Red Flags
- Assumptions: The Iranian government has the capability and intent to conduct cyber operations against foreign entities; the DOJ’s intelligence is accurate and comprehensive; the websites were primarily used for state-directed activities.
- Information Gaps: Specific details on the operational control and funding of the groups; comprehensive technical analysis of the malware used; clarity on the extent of damage caused by the cyberattacks.
- Bias & Deception Risks: Potential confirmation bias in attributing all activities to state actors; risk of Iranian disinformation campaigns to obfuscate true operators; reliance on potentially biased open-source reporting.
4. Implications and Strategic Risks
This development could lead to increased cyber hostilities between Iran and its adversaries, potentially spilling over into other domains.
- Political / Geopolitical: Potential for heightened tensions between the U.S. and Iran, impacting diplomatic relations and regional stability.
- Security / Counter-Terrorism: Increased threat to U.S. and allied infrastructure, necessitating enhanced cybersecurity measures and intelligence sharing.
- Cyber / Information Space: Likely escalation in cyber operations, with potential retaliatory attacks on U.S. entities and allies.
- Economic / Social: Potential disruptions in sectors targeted by cyberattacks, affecting economic stability and public trust in digital infrastructure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of Iranian cyber activities, enhance defensive cybersecurity measures, and engage in diplomatic efforts to de-escalate tensions.
- Medium-Term Posture (1–12 months): Develop resilience through public-private partnerships, invest in cybersecurity infrastructure, and strengthen alliances for coordinated cyber defense.
- Scenario Outlook:
- Best Case: Diplomatic engagement reduces cyber hostilities, leading to a decrease in attacks.
- Worst Case: Escalation leads to significant cyberattacks on critical infrastructure, causing widespread disruption.
- Most Likely: Continued low-level cyber skirmishes with periodic escalations, requiring sustained vigilance.
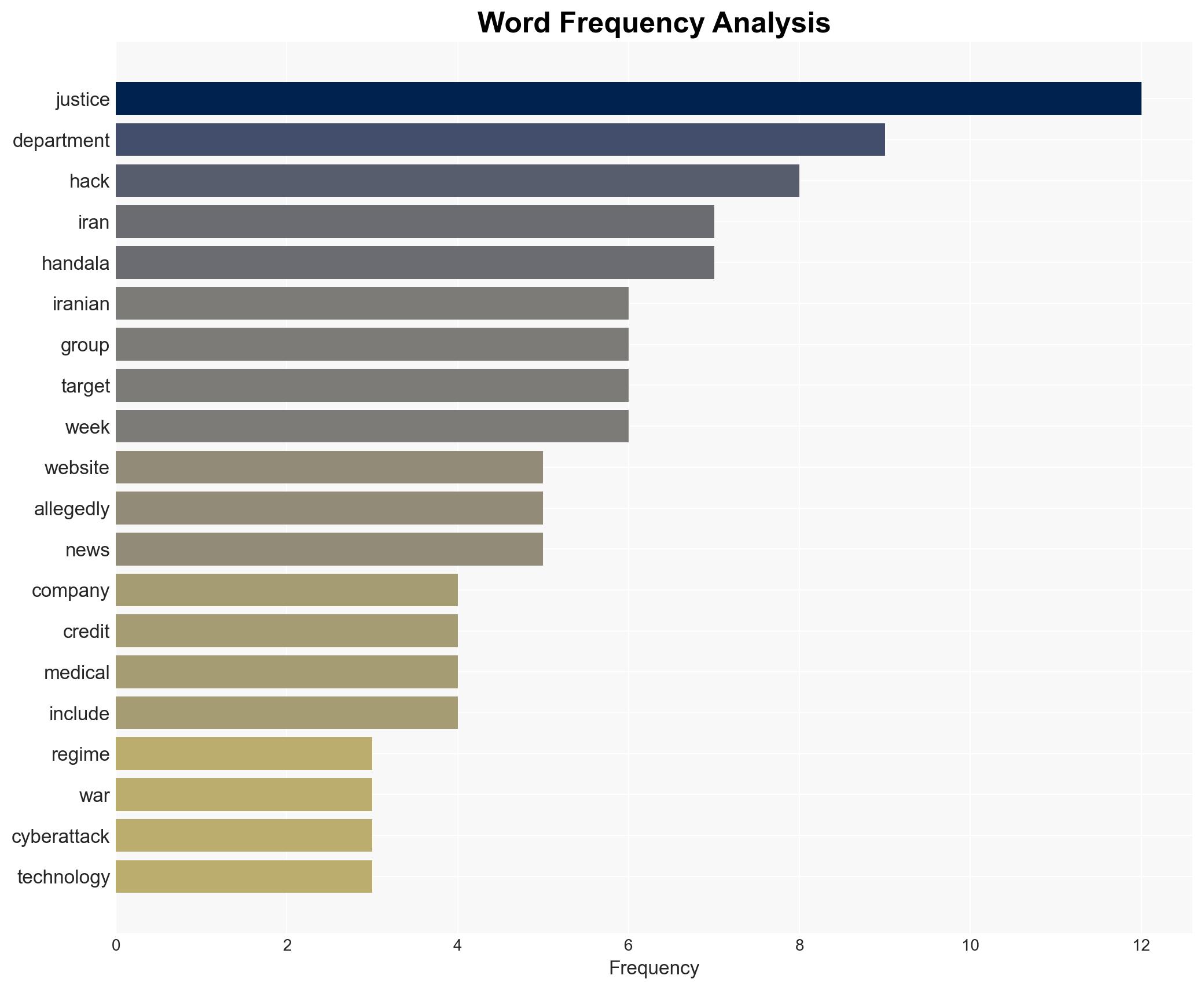
6. Key Individuals and Entities
- Handala
- Homeland Justice
- Karma Below
- Iran’s Ministry of Intelligence and Security
- Stryker (U.S.-based multinational medical technologies firm)
- Jalisco New Generation Cartel (alleged partner)
7. Thematic Tags
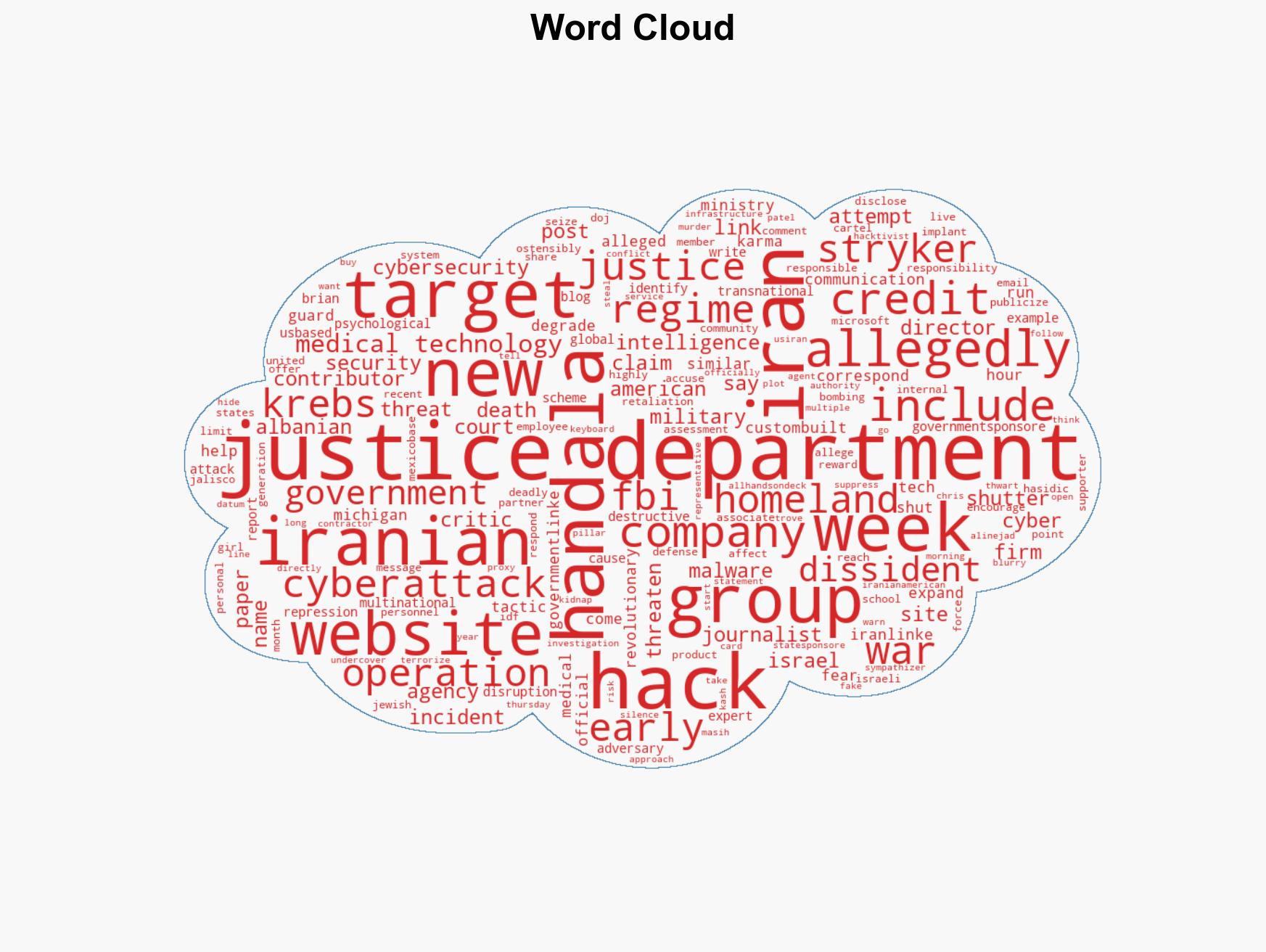
cybersecurity, state-sponsored hacking, Iran, transnational repression, cyber warfare, intelligence operations, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us