Cybercriminals Rapidly Exploit Langflow’s Critical RCE Vulnerability Within 20 Hours of Discovery
Published on: 2026-03-20
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Hackers Exploit Critical Langflow Bug in Just 20 Hours
1. BLUF (Bottom Line Up Front)
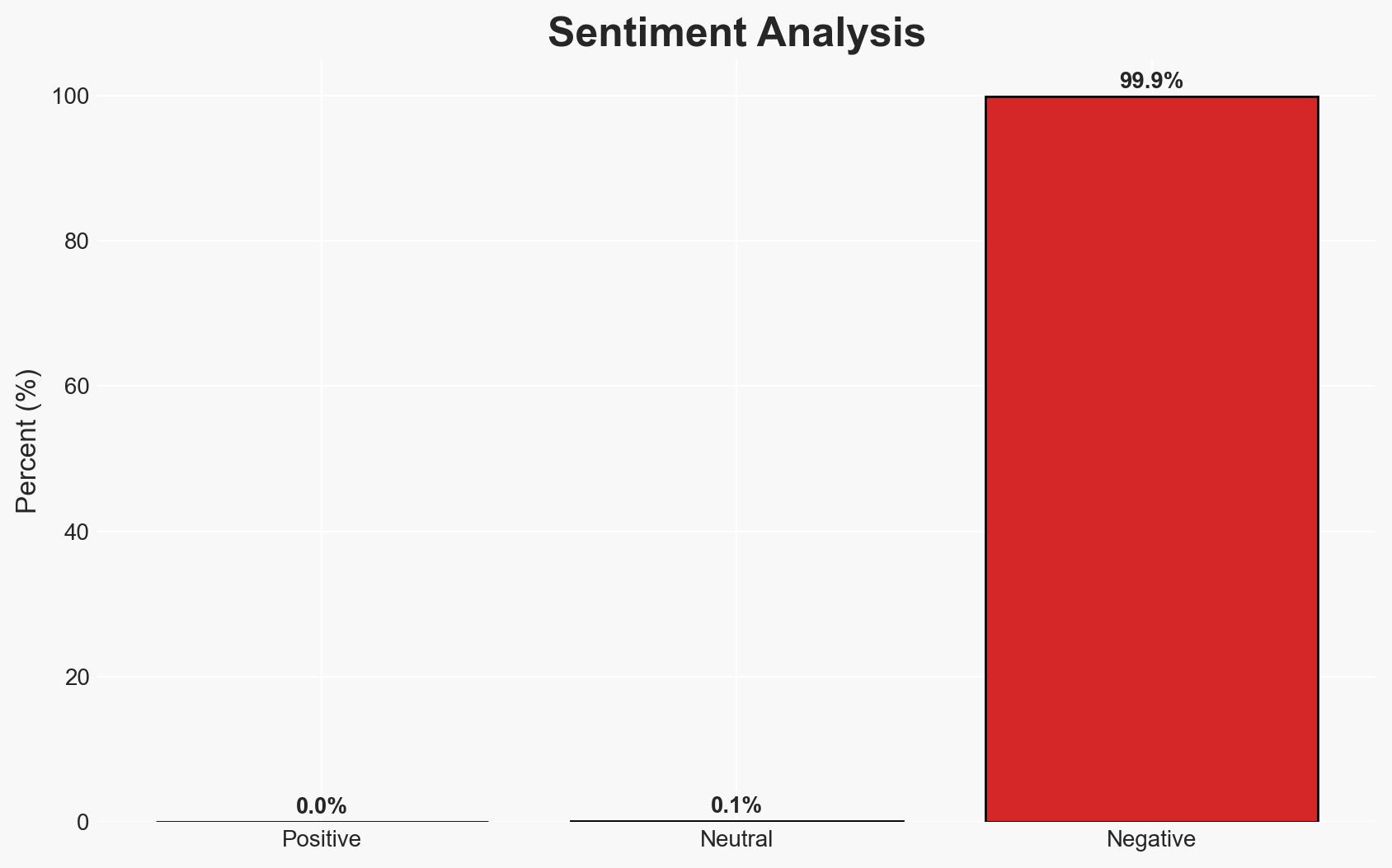
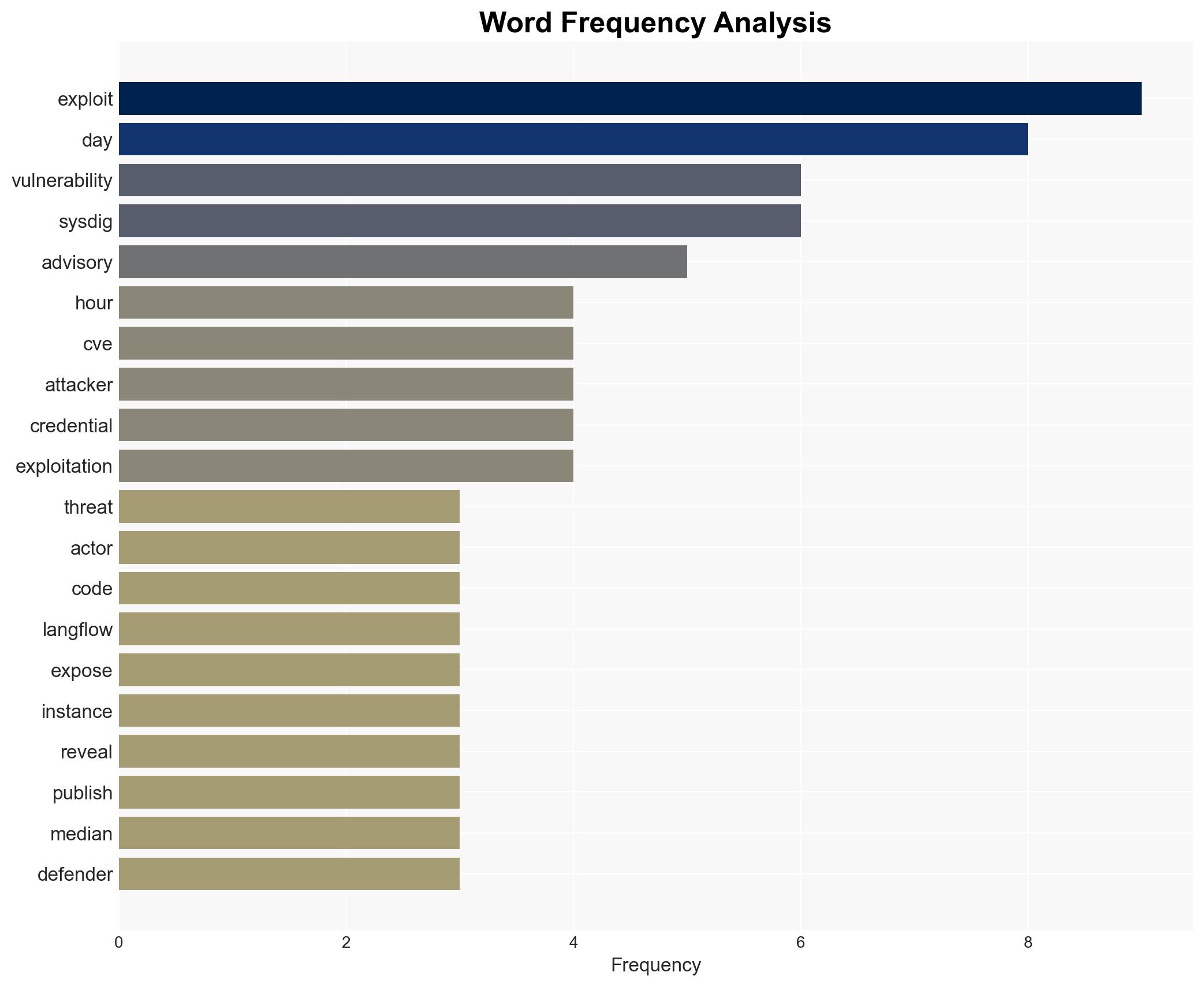
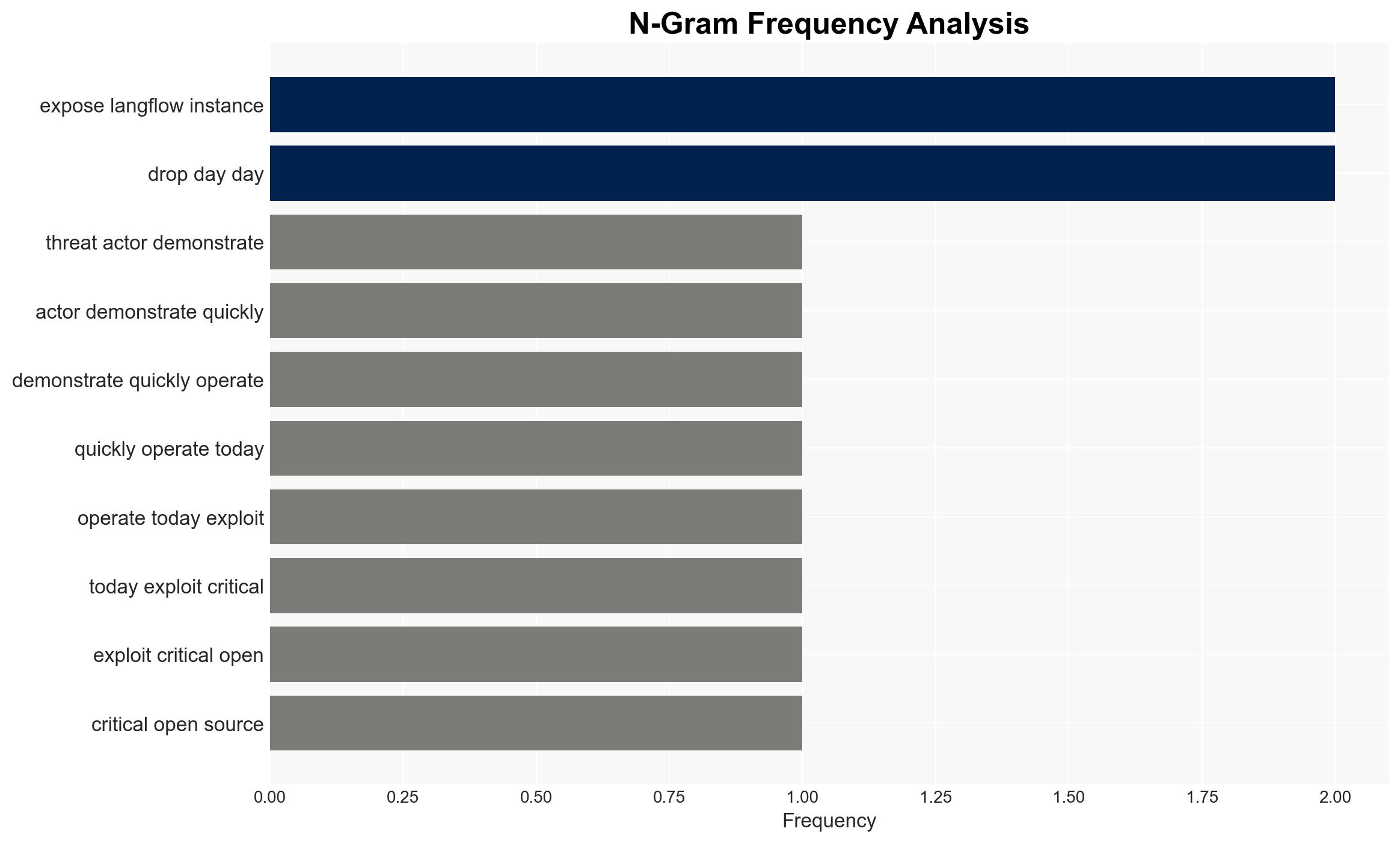
Threat actors rapidly exploited a critical vulnerability in Langflow, an open-source AI framework, within 20 hours of disclosure, highlighting significant challenges in vulnerability management. This incident underscores the need for accelerated patch deployment and proactive threat monitoring. The most likely hypothesis is that organized cybercriminal groups are leveraging advanced capabilities to exploit vulnerabilities quickly. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The rapid exploitation of the Langflow vulnerability was conducted by a well-organized cybercriminal group with advanced capabilities. Supporting evidence includes the speed of exploitation and the use of automated scanning and custom exploit scripts. However, the specific identity and motivations of the attackers remain uncertain.
- Hypothesis B: The exploitation was carried out by opportunistic individual hackers or smaller groups leveraging publicly available information. This is supported by the lack of a public proof-of-concept (PoC) and the use of a single HTTP request for exploitation, suggesting a low barrier to entry. Contradicting this is the coordinated nature of the attack.
- Assessment: Hypothesis A is currently better supported due to the coordinated and sophisticated nature of the attack, which suggests organized cybercriminal involvement. Key indicators that could shift this judgment include identification of the attackers or evidence of similar tactics used by known groups.
3. Key Assumptions and Red Flags
- Assumptions: The attackers had prior experience with similar vulnerabilities; Langflow instances were inadequately secured; the advisory provided sufficient detail for exploitation.
- Information Gaps: Specific identity and motivations of the attackers; the full scope of compromised systems and data; potential connections to other cyber incidents.
- Bias & Deception Risks: Potential confirmation bias in attributing the attack to organized groups; reliance on Sysdig as a primary source may introduce bias if their data is incomplete or skewed.
4. Implications and Strategic Risks
This development could lead to increased targeting of open-source frameworks, necessitating enhanced security measures and faster patch cycles. The incident may also prompt regulatory scrutiny on software supply chain security.
- Political / Geopolitical: Potential for increased tensions between states over cyber capabilities and responsibilities.
- Security / Counter-Terrorism: Heightened risk of similar attacks on critical infrastructure, requiring enhanced defensive postures.
- Cyber / Information Space: Accelerated arms race in vulnerability exploitation; potential for increased misinformation campaigns leveraging compromised systems.
- Economic / Social: Possible economic impacts due to compromised business operations and loss of consumer trust in digital services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Implement immediate patching protocols for Langflow; enhance monitoring for signs of exploitation; engage with cybersecurity firms for threat intelligence sharing.
- Medium-Term Posture (1–12 months): Develop partnerships with open-source communities to improve security practices; invest in automated patch management systems; conduct regular security audits.
- Scenario Outlook:
- Best: Rapid patching and collaboration reduce future exploitation risks.
- Worst: Continued exploitation leads to significant data breaches and economic damage.
- Most-Likely: Incremental improvements in security posture mitigate some risks, but challenges persist.
6. Key Individuals and Entities
- Sysdig (Cybersecurity firm reporting the exploitation)
- Zero Day Clock initiative (Source of vulnerability exploitation data)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
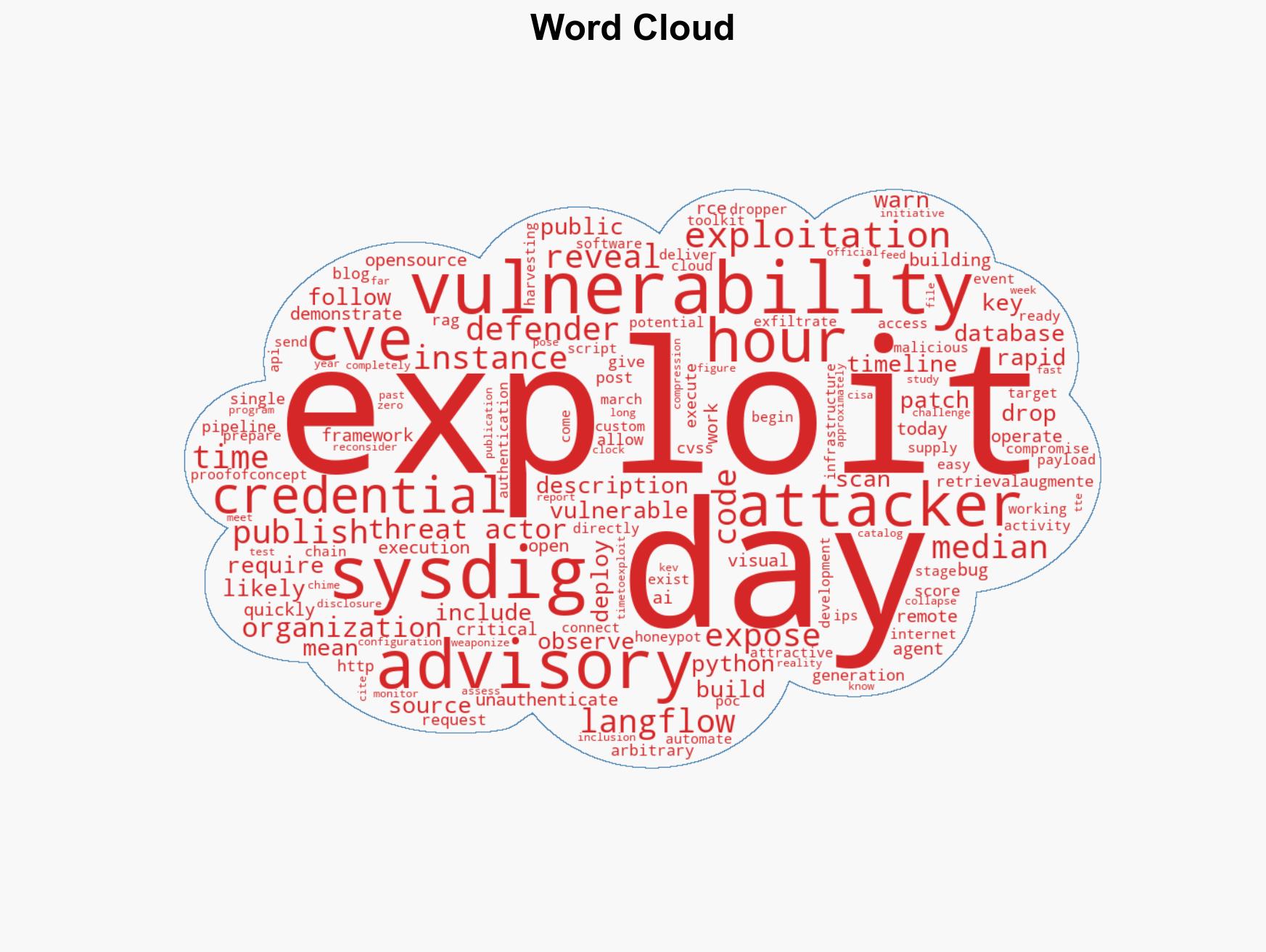
cybersecurity, vulnerability management, open-source software, cybercrime, threat intelligence, remote code execution, software supply chain
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us