UK NCA Chief Alerts on Teen Radicalization into Cybercrime via Online Platforms
Published on: 2026-03-20
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: NCA Boss Warns That Teens Are Being Radicalized Into Cybercrime Online
1. BLUF (Bottom Line Up Front)
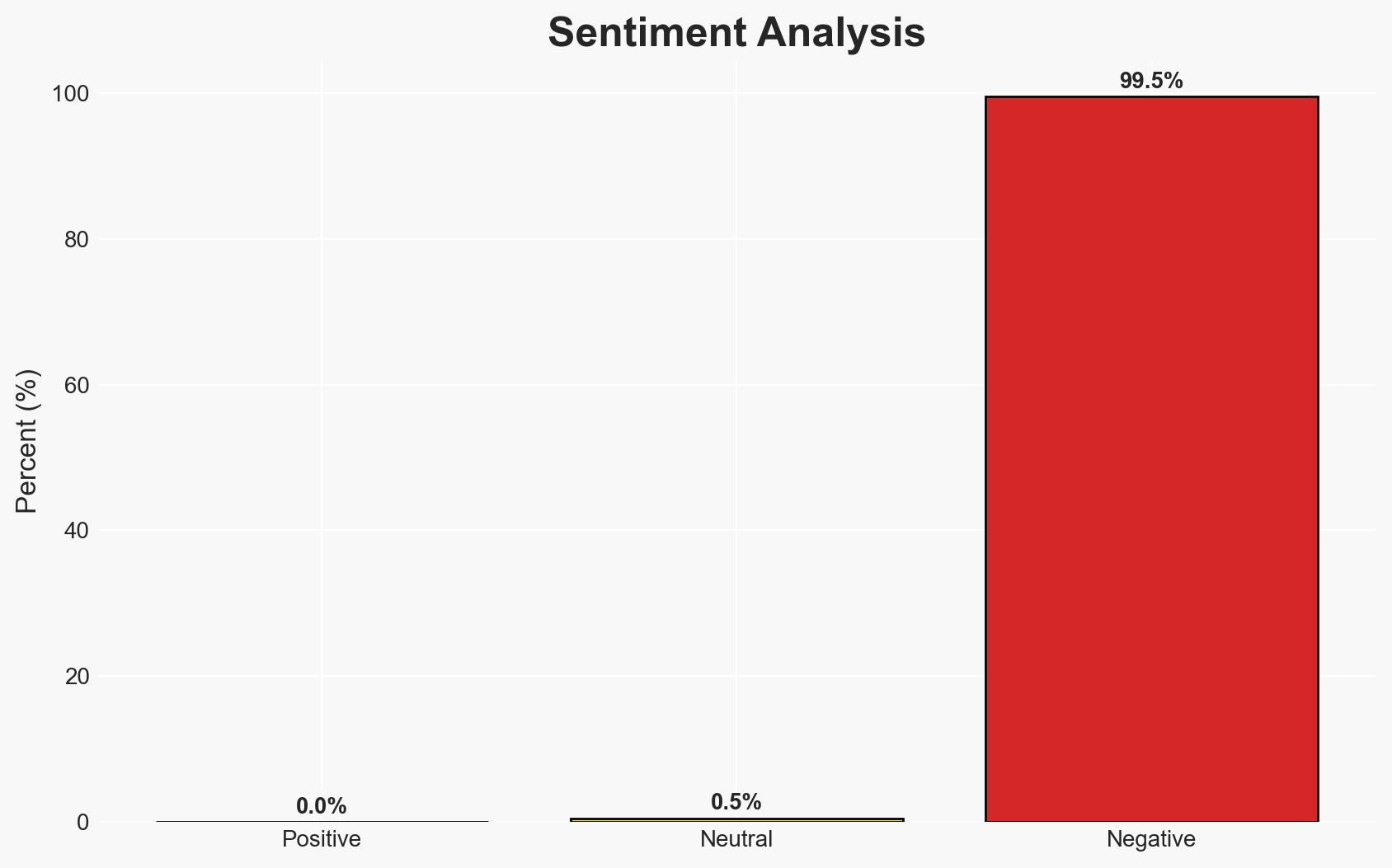
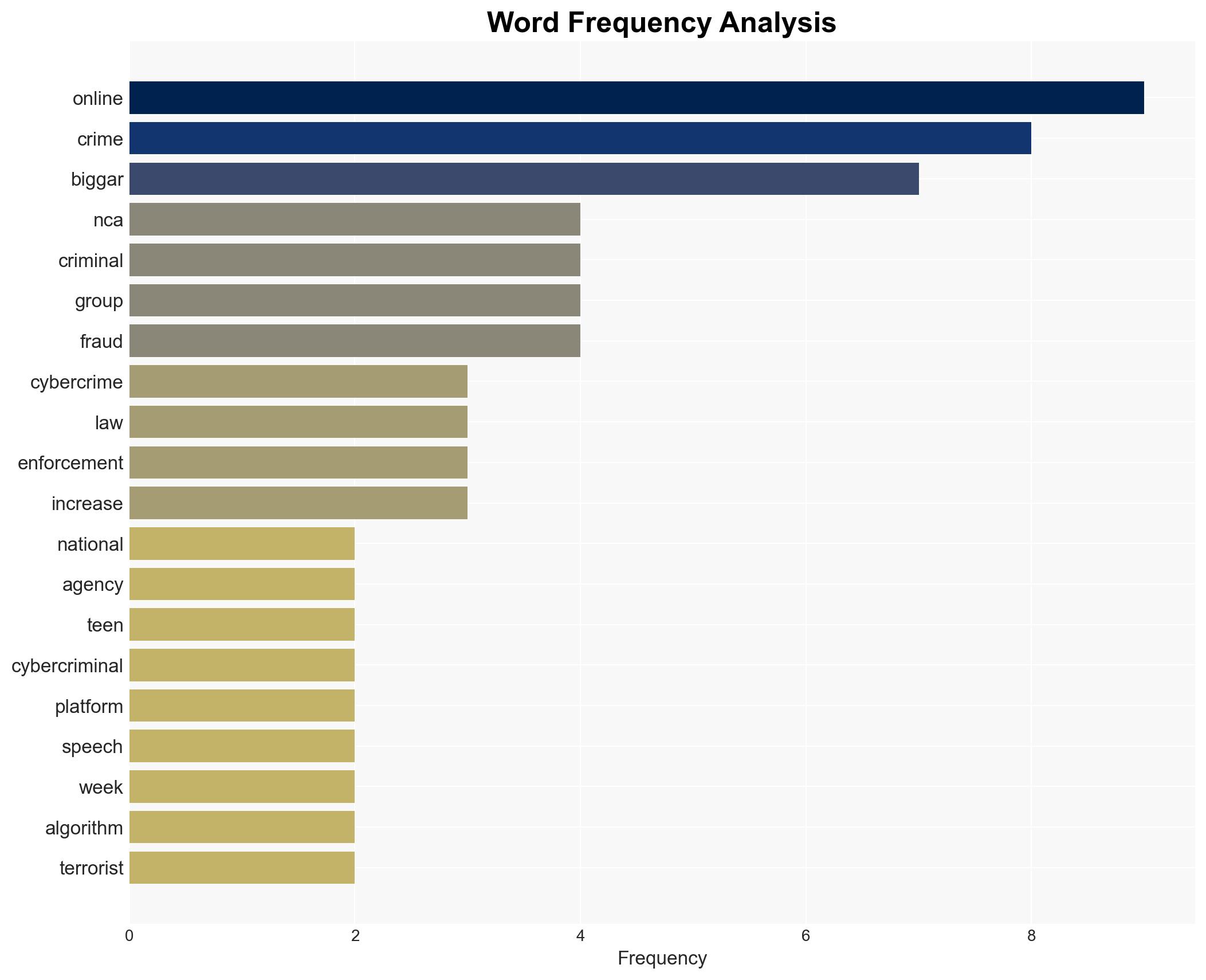
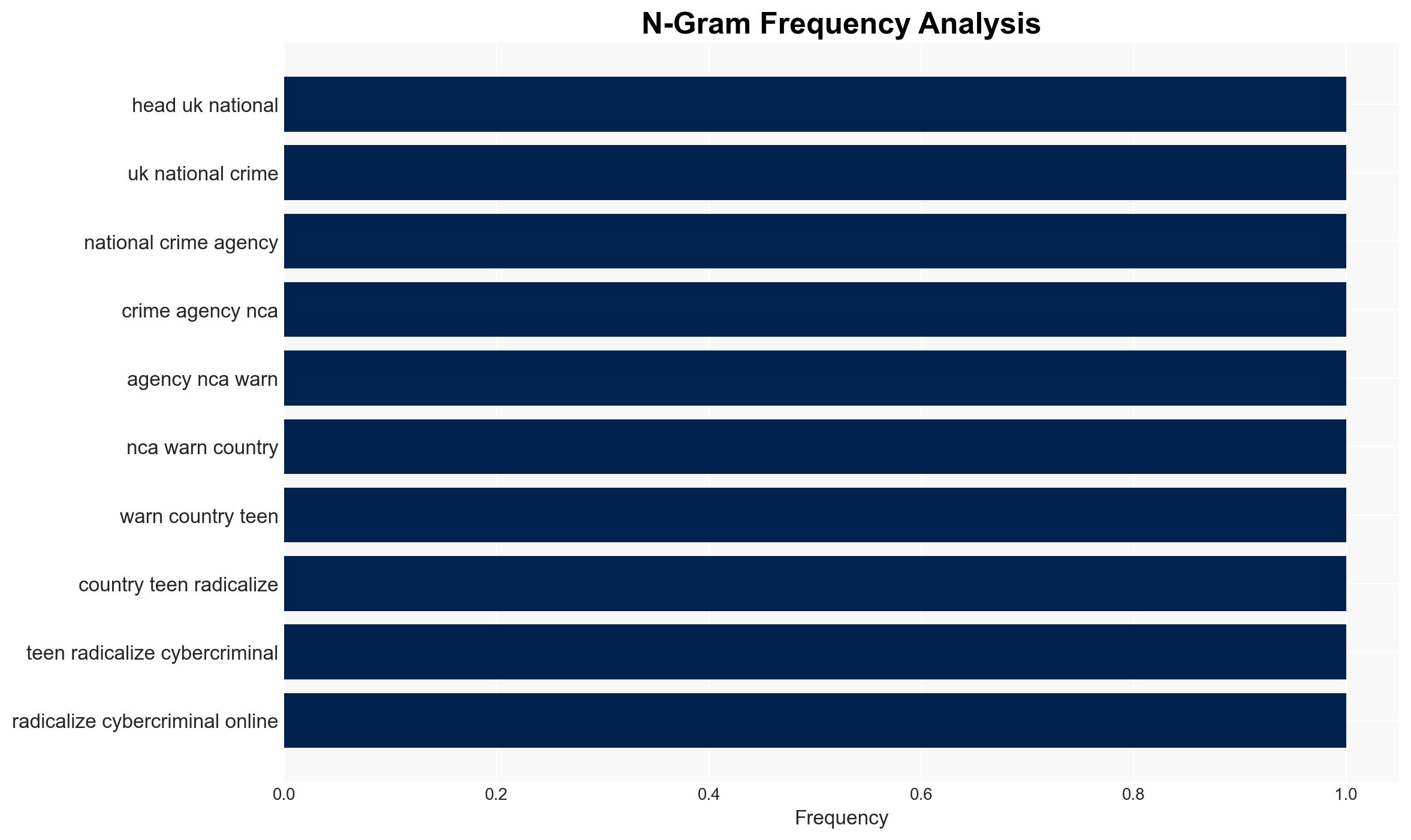
The UK’s National Crime Agency (NCA) has identified a concerning trend of teenagers being radicalized into cybercrime through online platforms. This development is attributed to the influence of toxic online spaces and algorithms. The situation poses a significant threat to national security and requires immediate attention from both law enforcement and technology companies. Overall confidence in this assessment is moderate, given the complexity and evolving nature of online environments.
2. Competing Hypotheses
- Hypothesis A: Teens are being radicalized into cybercrime primarily due to the influence of online platforms and algorithms. Supporting evidence includes the NCA’s observations of toxic online spaces and the blurring of crime types. Key uncertainties involve the scale of influence and specific platforms involved.
- Hypothesis B: The increase in teenage cybercriminal activity is driven more by socio-economic factors and peer influence than by online platforms themselves. This hypothesis is less supported due to the lack of specific evidence addressing these factors in the current context.
- Assessment: Hypothesis A is currently better supported due to direct statements from the NCA and observed trends in online behavior. Indicators that could shift this judgment include new data on socio-economic influences or changes in platform policies.
3. Key Assumptions and Red Flags
- Assumptions: Online platforms significantly influence youth behavior; the NCA’s data accurately reflects current trends; technology companies have the capability to mitigate these influences.
- Information Gaps: Specific platforms and algorithms involved; detailed demographic data on affected teens; effectiveness of current mitigation strategies by tech companies.
- Bias & Deception Risks: Potential bias in NCA’s focus on online platforms; risk of underestimating other contributing factors such as socio-economic conditions.
4. Implications and Strategic Risks
This trend could exacerbate existing cybercrime challenges and strain law enforcement resources. It may also lead to increased regulatory scrutiny of technology companies.
- Political / Geopolitical: Potential for international tensions if foreign platforms are implicated; increased calls for global cooperation on cybercrime.
- Security / Counter-Terrorism: Greater complexity in distinguishing between cybercrime and terrorism; potential for increased recruitment into extremist activities.
- Cyber / Information Space: Heightened risk of sophisticated cyber-attacks; challenges in monitoring and regulating online spaces.
- Economic / Social: Potential economic impact from increased cybercrime; social unrest due to perceived inaction by tech companies.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of online platforms; engage with tech companies to address algorithmic influences; enhance public awareness campaigns.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies for data sharing; invest in youth education programs on cyber ethics; strengthen international cooperation on cybercrime.
- Scenario Outlook:
- Best: Successful collaboration with tech companies reduces radicalization rates.
- Worst: Continued increase in teenage cybercrime leads to significant national security threats.
- Most-Likely: Incremental improvements in mitigation efforts with ongoing challenges.
6. Key Individuals and Entities
- Graeme Biggar, NCA Director General
- The Com, online network
- Scattered Spider, cybercrime group
- ShinyHunters, cybercrime group
- Lapsus$, cybercrime group
- Not clearly identifiable from open sources in this snippet for specific tech companies or platforms
7. Thematic Tags
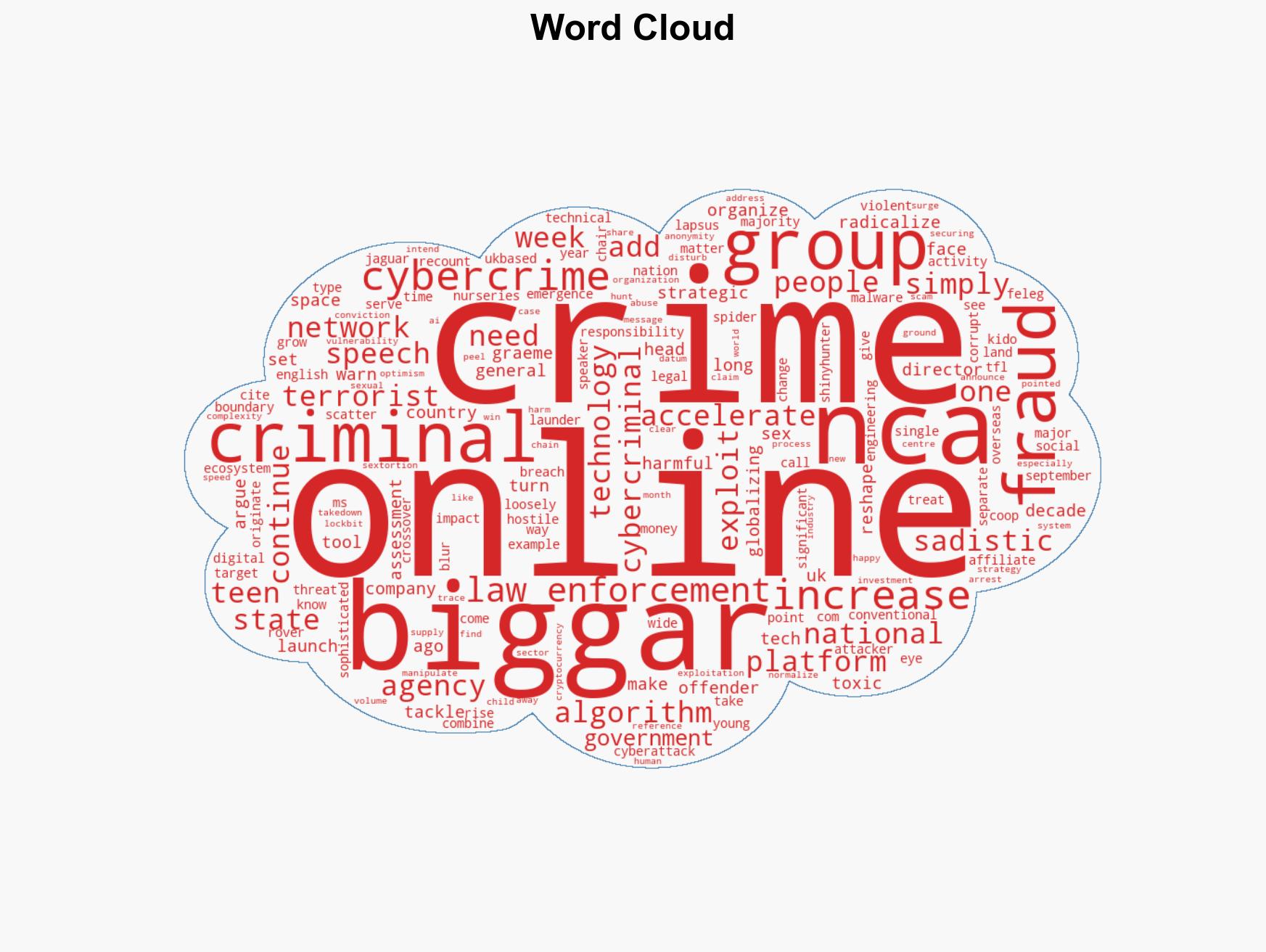
cybersecurity, cybercrime, radicalization, online platforms, national security, law enforcement, technology responsibility, youth engagement
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us