Data Centers Targeted in Iran’s Unprecedented Military Response to U.S.-Israeli Actions
Published on: 2026-03-20
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Data Centers Are Military Targets Now
1. BLUF (Bottom Line Up Front)
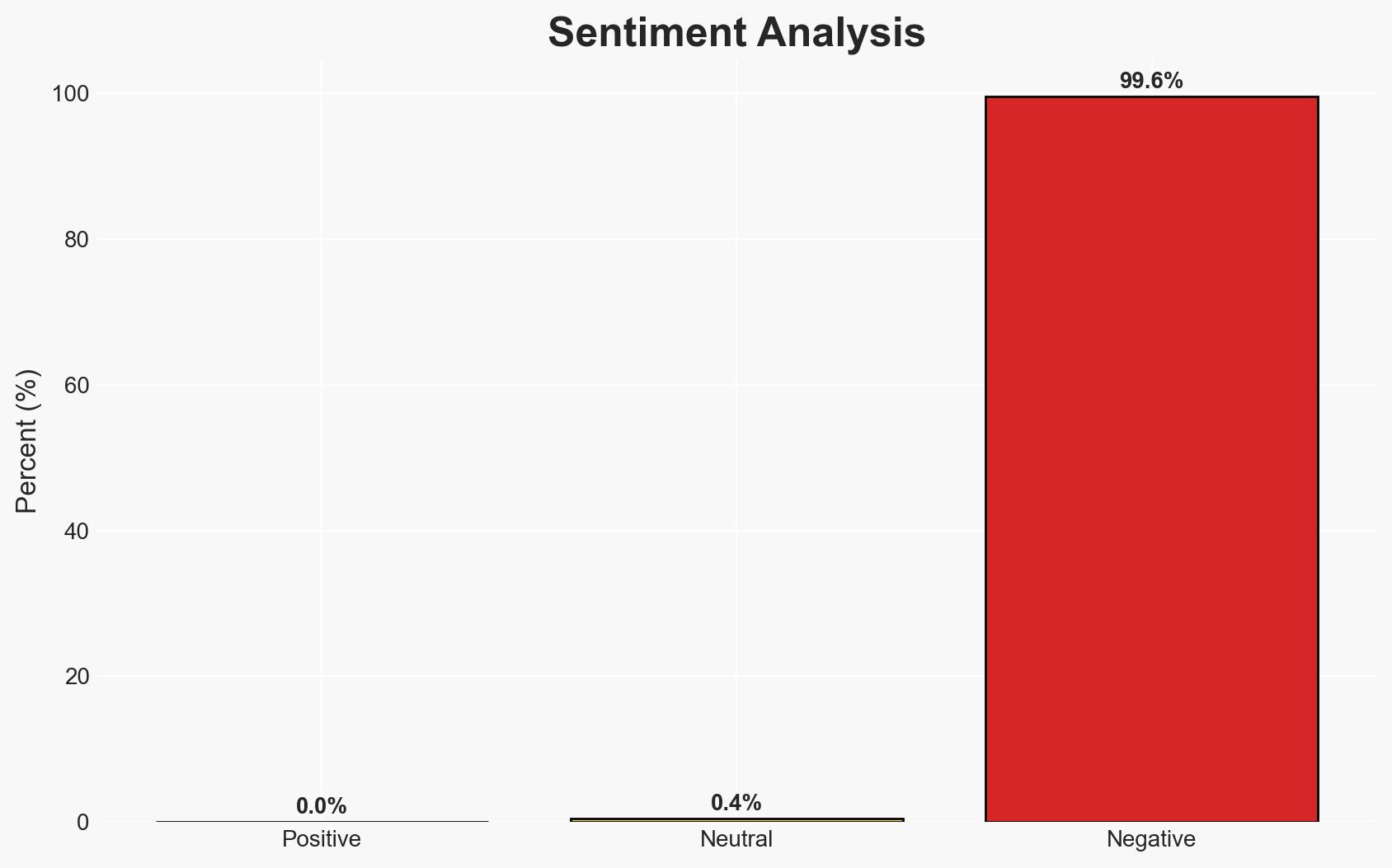
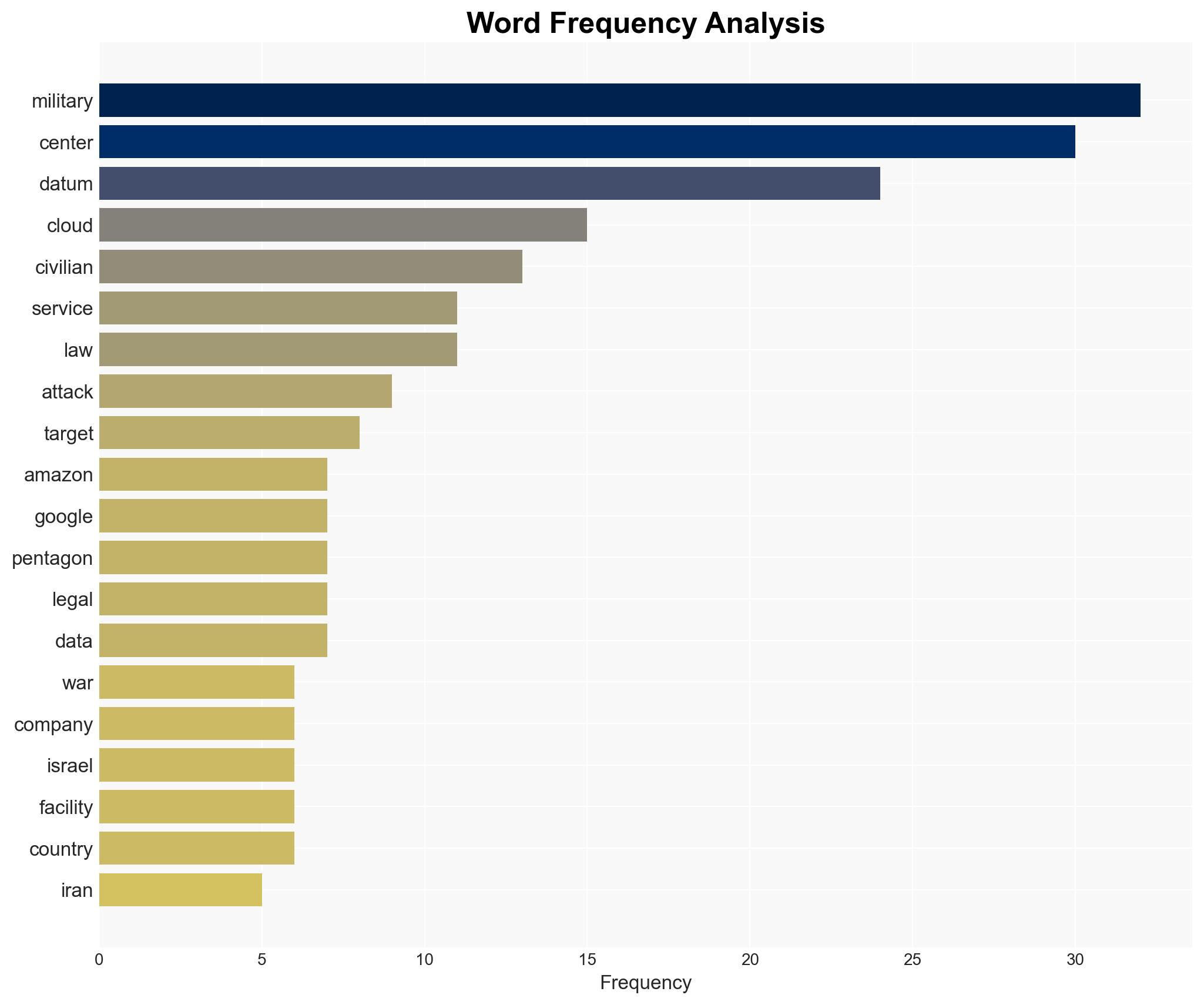
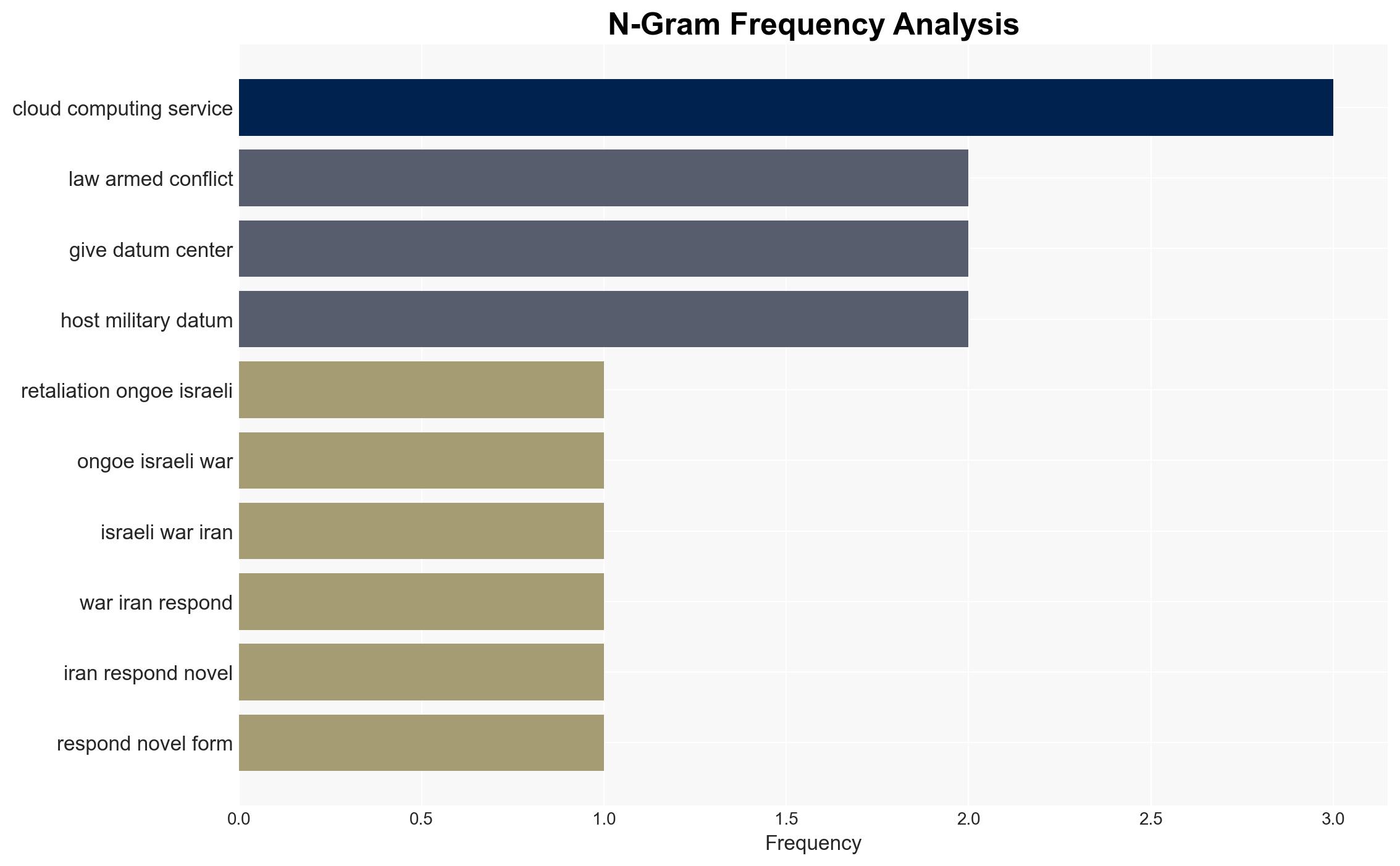
The recent Iranian drone strikes on Amazon-owned data centers in the UAE and Bahrain mark a significant shift in military targeting, highlighting the vulnerability of private sector infrastructure involved in military support. This development could redefine the legal and operational landscape of conflict zones. The most likely hypothesis is that Iran aims to disrupt perceived military support functions of these data centers. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: Iran targeted data centers to directly disrupt military operations supported by cloud services. This is supported by Iran’s stated motive and the involvement of companies known to collaborate with the Pentagon. However, the specific military use of the targeted centers remains unclear.
- Hypothesis B: The attacks were symbolic, aiming to send a political message rather than achieve significant operational disruption. This is supported by the lack of evidence showing direct military impact and the public nature of the announcement.
- Assessment: Hypothesis A is currently better supported due to Iran’s explicit statements regarding the centers’ military roles. Future indicators such as further attacks or evidence of military disruption could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Data centers provide critical support to military operations; Iran has the capability to identify and target such infrastructure; the attacks were intended to disrupt military functions.
- Information Gaps: Specific military applications of the targeted data centers; extent of operational disruption caused by the attacks.
- Bias & Deception Risks: Potential bias in Iranian state media reporting; possible exaggeration of the attacks’ impact by involved parties.
4. Implications and Strategic Risks
This development could lead to an escalation in targeting private sector infrastructure in conflict zones, complicating international legal norms and operational strategies.
- Political / Geopolitical: Potential for increased tensions between Iran and Western allies, and a reevaluation of private sector roles in military conflicts.
- Security / Counter-Terrorism: Increased risk of similar attacks on other critical infrastructure, necessitating enhanced protective measures.
- Cyber / Information Space: Potential for cyber retaliation or increased cyber defense measures by affected companies.
- Economic / Social: Disruption of services could impact regional economies and public perception of corporate involvement in military activities.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of critical infrastructure; engage in diplomatic efforts to de-escalate tensions; assess vulnerabilities in data center operations.
- Medium-Term Posture (1–12 months): Develop resilience measures for critical infrastructure; strengthen public-private partnerships for security; review legal frameworks governing military targeting.
- Scenario Outlook: Best: De-escalation and enhanced security cooperation; Worst: Escalation leading to broader conflict; Most-Likely: Continued low-level targeting with diplomatic tensions.
6. Key Individuals and Entities
- Islamic Revolutionary Guard Corps
- Amazon
- Microsoft
- Tasnim News Agency
- León Castellanos-Jankiewicz, Asser Institute
7. Thematic Tags
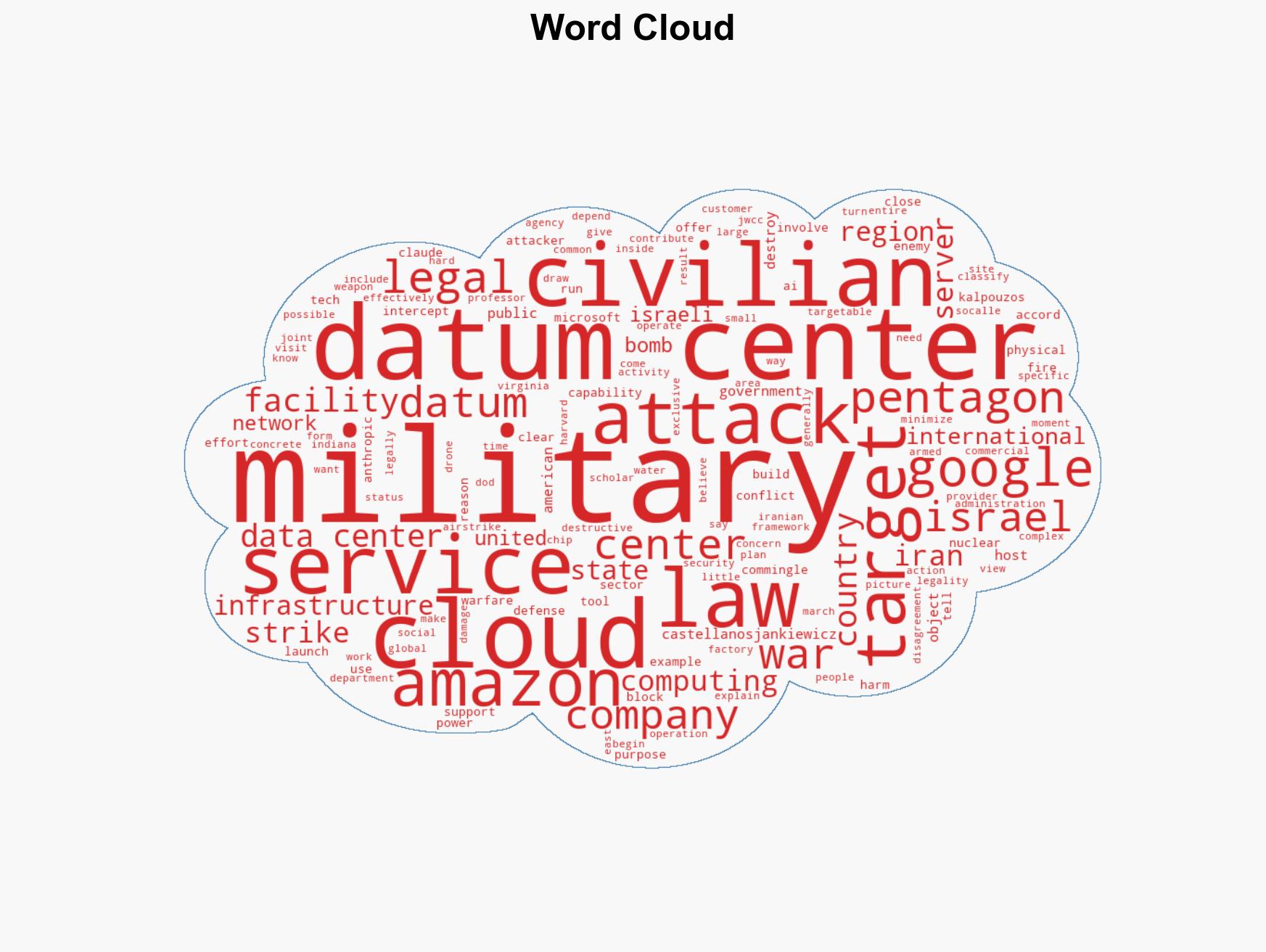
national security threats, military targeting, data centers, Iran, cyber warfare, private sector, international law, geopolitical tensions
Structured Analytic Techniques Applied
- Cognitive Bias Stress Test: Expose and correct potential biases in assessments through red-teaming and structured challenge.
- Bayesian Scenario Modeling: Use probabilistic forecasting for conflict trajectories or escalation likelihood.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
National Security Threats Briefs ·
Daily Summary ·
Support us