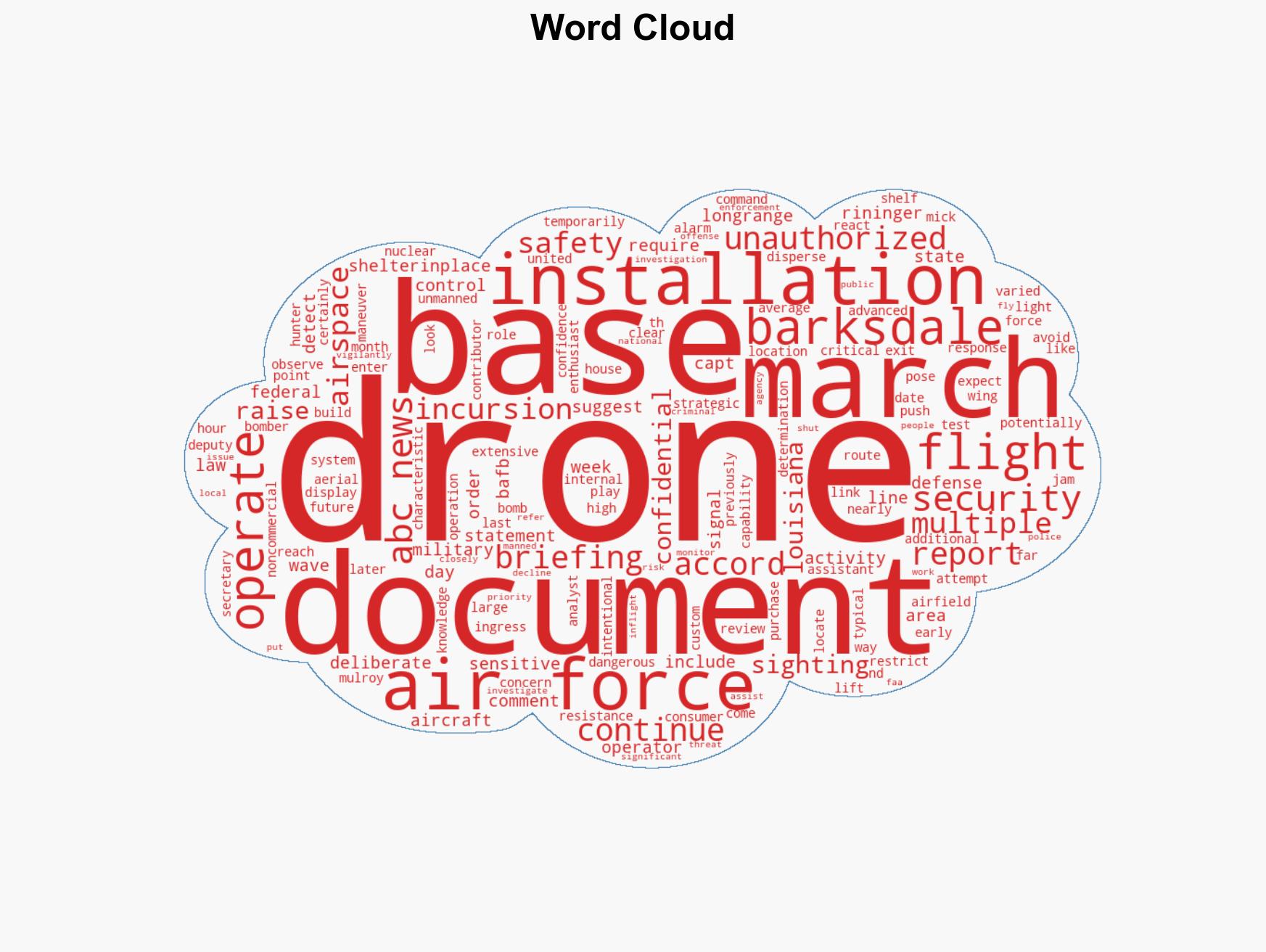
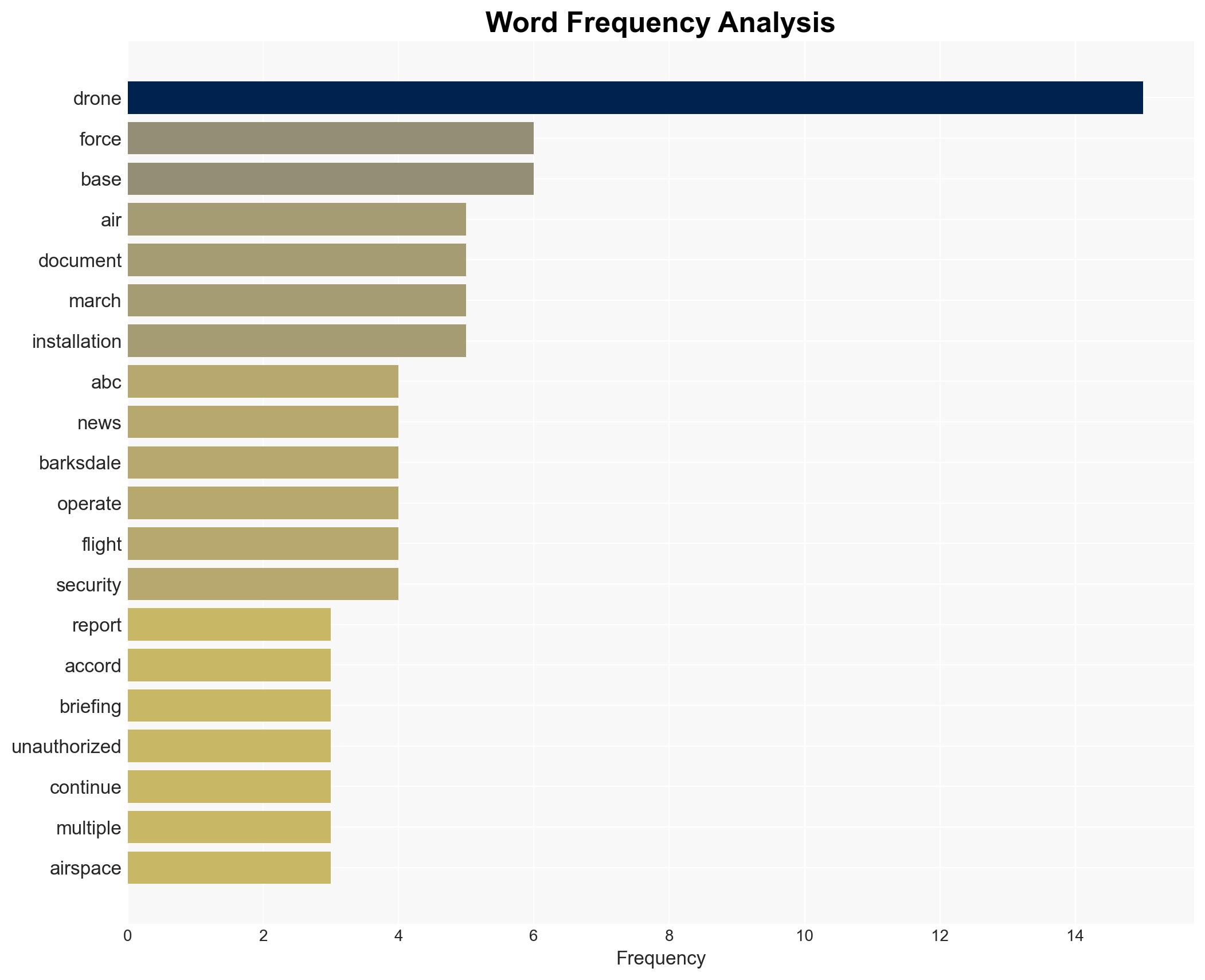
Unauthorized drone incursions detected in waves over critical US Air Force base, raising security concerns
Published on: 2026-03-20
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: ‘Multiple waves’ of unauthorized drones spotted over strategic US Air Force base
1. BLUF (Bottom Line Up Front)
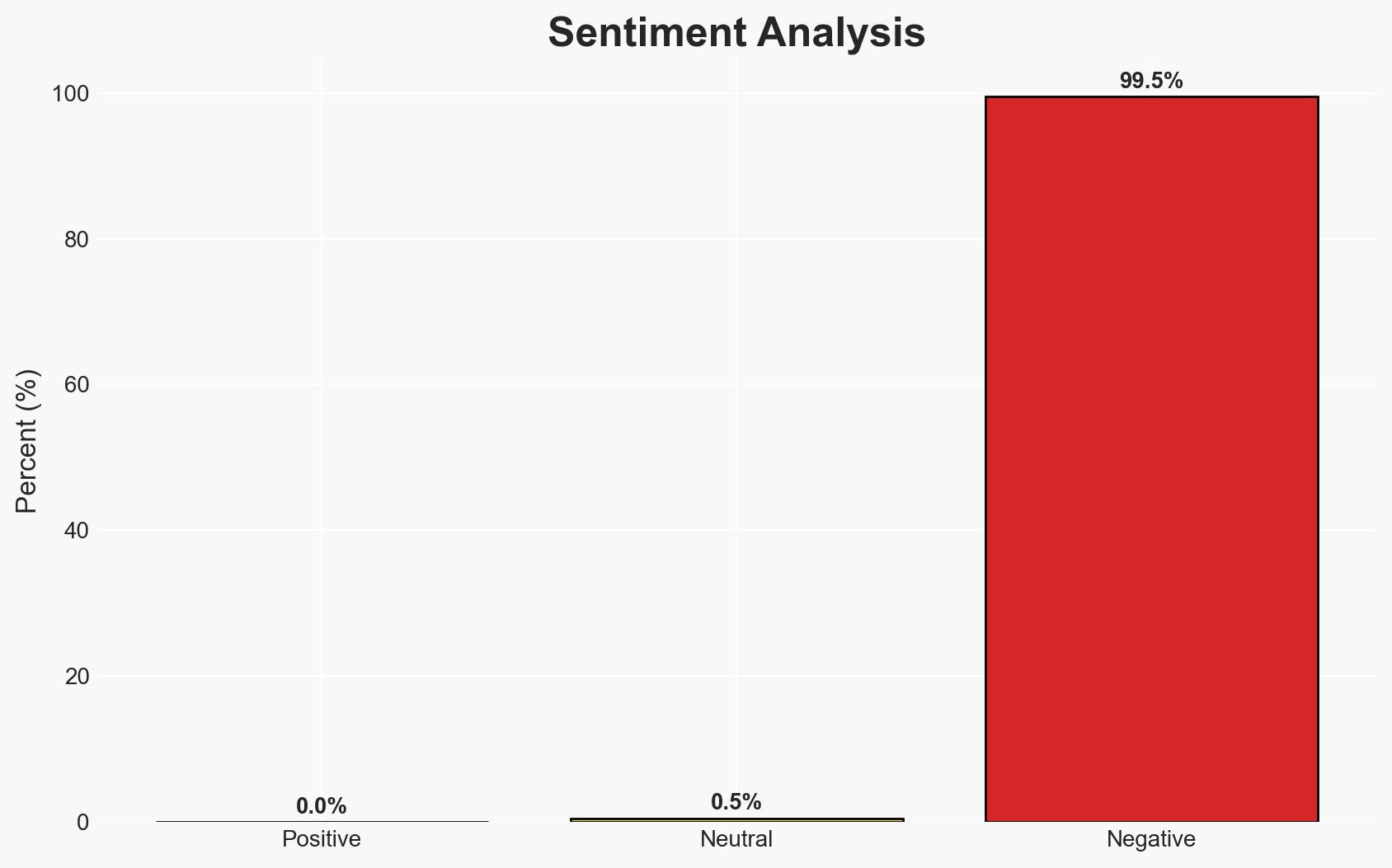
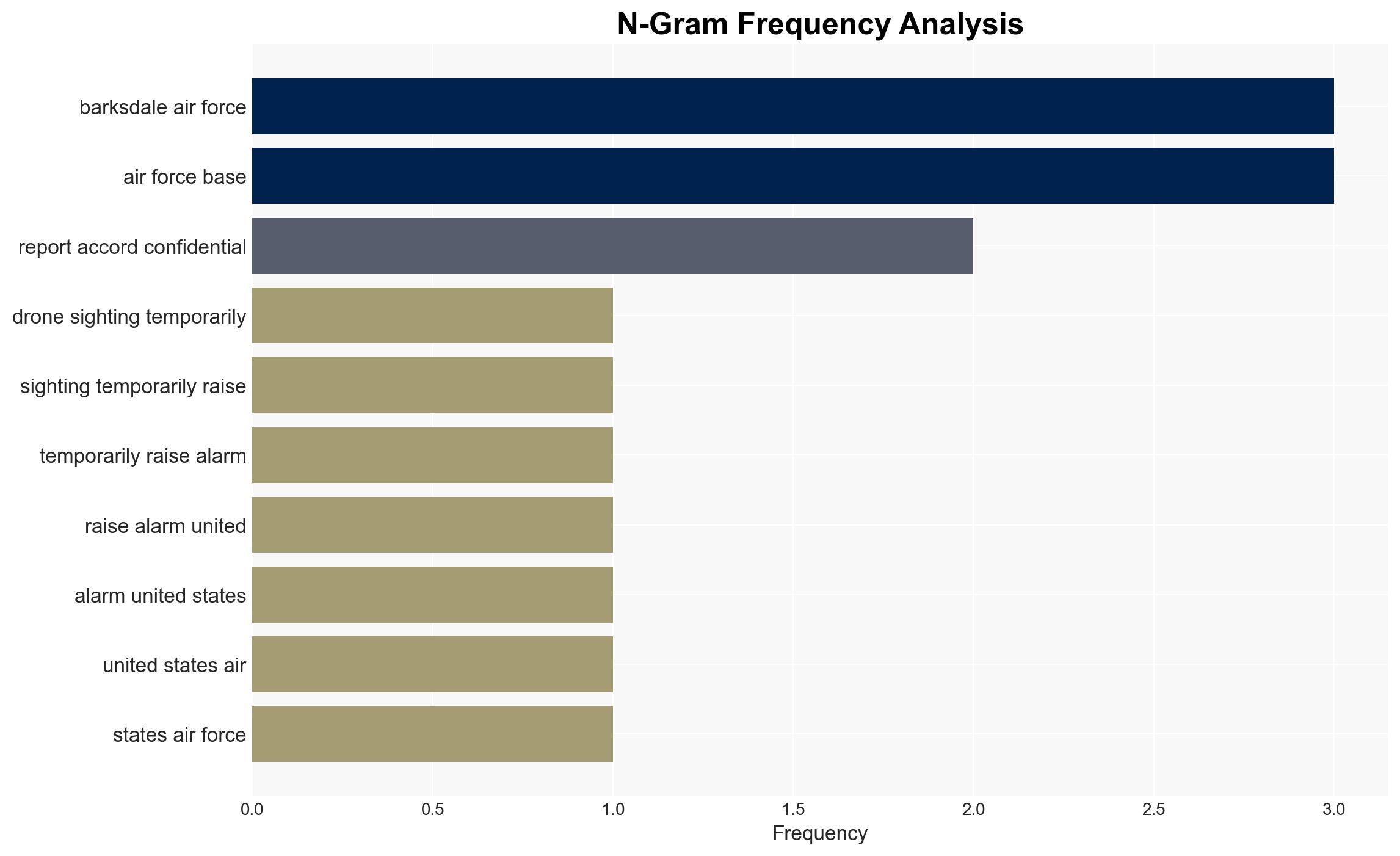
Unauthorized drone activity at Barksdale Air Force Base, a critical site for U.S. nuclear capabilities, suggests a deliberate attempt to probe security responses. The drones’ characteristics indicate a sophisticated operation, likely beyond the capabilities of amateur enthusiasts. This poses a significant national security threat, with moderate confidence in the assessment that further incursions are probable.
2. Competing Hypotheses
- Hypothesis A: The drone activity is a state-sponsored operation aimed at testing U.S. military base defenses. Supporting evidence includes the drones’ advanced capabilities and strategic targeting of a nuclear command site. However, the lack of direct attribution to a specific state actor remains a key uncertainty.
- Hypothesis B: The incursions are conducted by a non-state actor, possibly a sophisticated criminal or terrorist group, seeking to exploit vulnerabilities for future attacks or intelligence gathering. This hypothesis is supported by the deliberate evasion tactics and custom-built drones, but lacks clear motive or known group involvement.
- Assessment: Hypothesis A is currently better supported due to the strategic nature of the target and the advanced technology involved, which aligns with state-level capabilities. Indicators such as intercepted communications or further technical analysis could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The drones were operated with intent to test security; the technology used is not commercially available; the operators have advanced technical skills.
- Information Gaps: The identity of the operators; the origin of the drones; specific objectives of the incursions.
- Bias & Deception Risks: Potential confirmation bias in attributing state sponsorship; risk of misdirection by the operators to obscure true intent or affiliation.
4. Implications and Strategic Risks
This development could lead to increased tensions and a reevaluation of base security protocols, potentially prompting broader military and diplomatic responses.
- Political / Geopolitical: Potential escalation with foreign states if attribution is confirmed; increased scrutiny on U.S. military vulnerabilities.
- Security / Counter-Terrorism: Heightened alert status at military installations; potential for copycat incidents.
- Cyber / Information Space: Risk of cyber operations accompanying physical incursions; misinformation campaigns exploiting the incident.
- Economic / Social: Limited immediate economic impact; potential public concern over military security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance surveillance and detection capabilities at Barksdale; conduct a comprehensive review of airspace security protocols.
- Medium-Term Posture (1–12 months): Develop partnerships for drone threat intelligence sharing; invest in counter-drone technologies.
- Scenario Outlook:
- Best: Identification and neutralization of the threat with no further incidents.
- Worst: Successful breach leading to compromised security or intelligence loss.
- Most-Likely: Continued probing with sporadic incidents, prompting ongoing security enhancements.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
national security threats, drone incursions, national security, military base security, unauthorized surveillance, counter-drone operations, airspace security, state-sponsored threats
Structured Analytic Techniques Applied
- Cognitive Bias Stress Test: Expose and correct potential biases in assessments through red-teaming and structured challenge.
- Bayesian Scenario Modeling: Use probabilistic forecasting for conflict trajectories or escalation likelihood.
- Network Influence Mapping: Map relationships between state and non-state actors for impact estimation.
Explore more:
National Security Threats Briefs ·
Daily Summary ·
Support us