Interlock ransomware exploited Cisco FMC vulnerability CVE-2026-20131 weeks before public patch release
Published on: 2026-03-20
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Cisco FMC flaw was exploited by Interlock weeks before patch CVE-2026-20131
1. BLUF (Bottom Line Up Front)
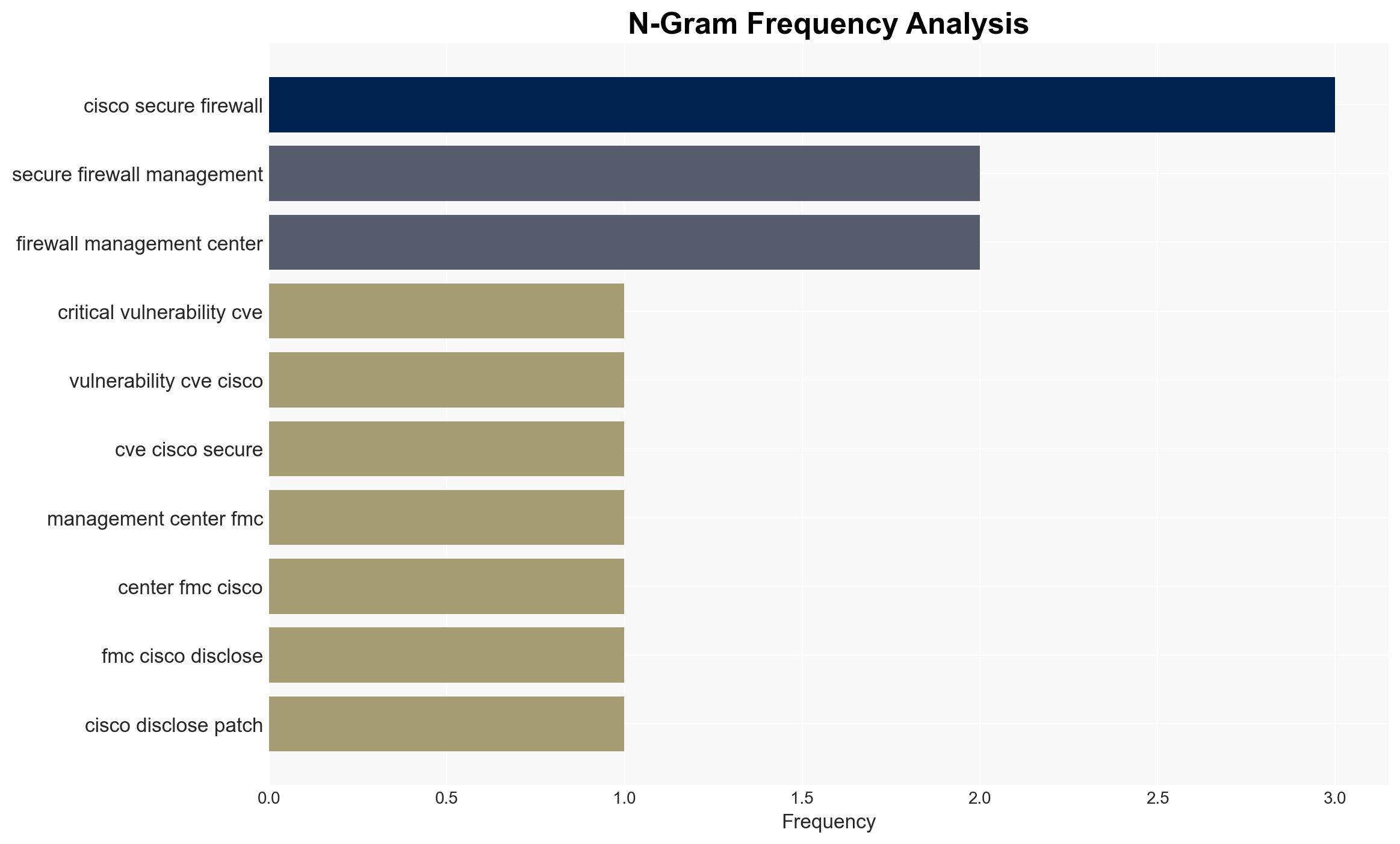
The Interlock ransomware gang exploited a critical vulnerability in Cisco Secure Firewall Management Center (CVE-2026-20131) weeks before its disclosure and patching, potentially compromising numerous organizations. This exploitation highlights significant risks in cybersecurity defenses and the need for proactive threat intelligence. Overall confidence in this assessment is moderate, given the limited scope of available data.
2. Competing Hypotheses
- Hypothesis A: Interlock independently discovered and exploited CVE-2026-20131 before Cisco’s internal discovery. Supporting evidence includes the timeline of exploitation predating Cisco’s disclosure. Key uncertainties involve how Interlock discovered the vulnerability.
- Hypothesis B: Interlock obtained knowledge of the vulnerability through insider access or information leakage from Cisco or its partners. This hypothesis lacks direct supporting evidence but is plausible given the sophistication of the attack.
- Assessment: Hypothesis A is currently better supported due to the observed timeline and lack of evidence for insider involvement. Indicators such as insider threat reports or leaks could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Interlock has the technical capability to discover zero-day vulnerabilities independently; Cisco’s internal processes did not leak vulnerability information; the timeline of exploitation is accurately reported.
- Information Gaps: Details on how Interlock discovered the vulnerability; comprehensive data on affected organizations; potential insider threat vectors.
- Bias & Deception Risks: Potential bias in attributing the attack solely to Interlock without considering other actors; deception risks in the attackers’ use of anonymization techniques.
4. Implications and Strategic Risks
This development underscores the persistent threat posed by ransomware groups exploiting zero-day vulnerabilities, potentially leading to increased scrutiny on cybersecurity practices and vendor disclosure processes.
- Political / Geopolitical: Potential for increased regulatory pressure on technology vendors to improve vulnerability management.
- Security / Counter-Terrorism: Heightened threat environment for organizations using Cisco products, necessitating enhanced monitoring and response capabilities.
- Cyber / Information Space: Likely increase in cyber defense measures and information sharing among affected industries.
- Economic / Social: Potential financial losses and reputational damage for affected organizations, impacting market stability and trust in cybersecurity solutions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Organizations should apply the Cisco patch immediately, enhance monitoring for signs of exploitation, and review access logs for anomalous activity.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing, invest in employee training on cybersecurity awareness, and conduct regular vulnerability assessments.
- Scenario Outlook: Best: Rapid patch adoption mitigates further exploitation. Worst: Continued exploitation leads to significant data breaches. Most-Likely: Mixed patch adoption results in sporadic incidents, prompting increased cybersecurity measures.
6. Key Individuals and Entities
- Interlock ransomware gang
- Cisco Systems, Inc.
- Amazon CISO and VP of Security Engineering CJ Moses
- Not clearly identifiable from open sources in this snippet.
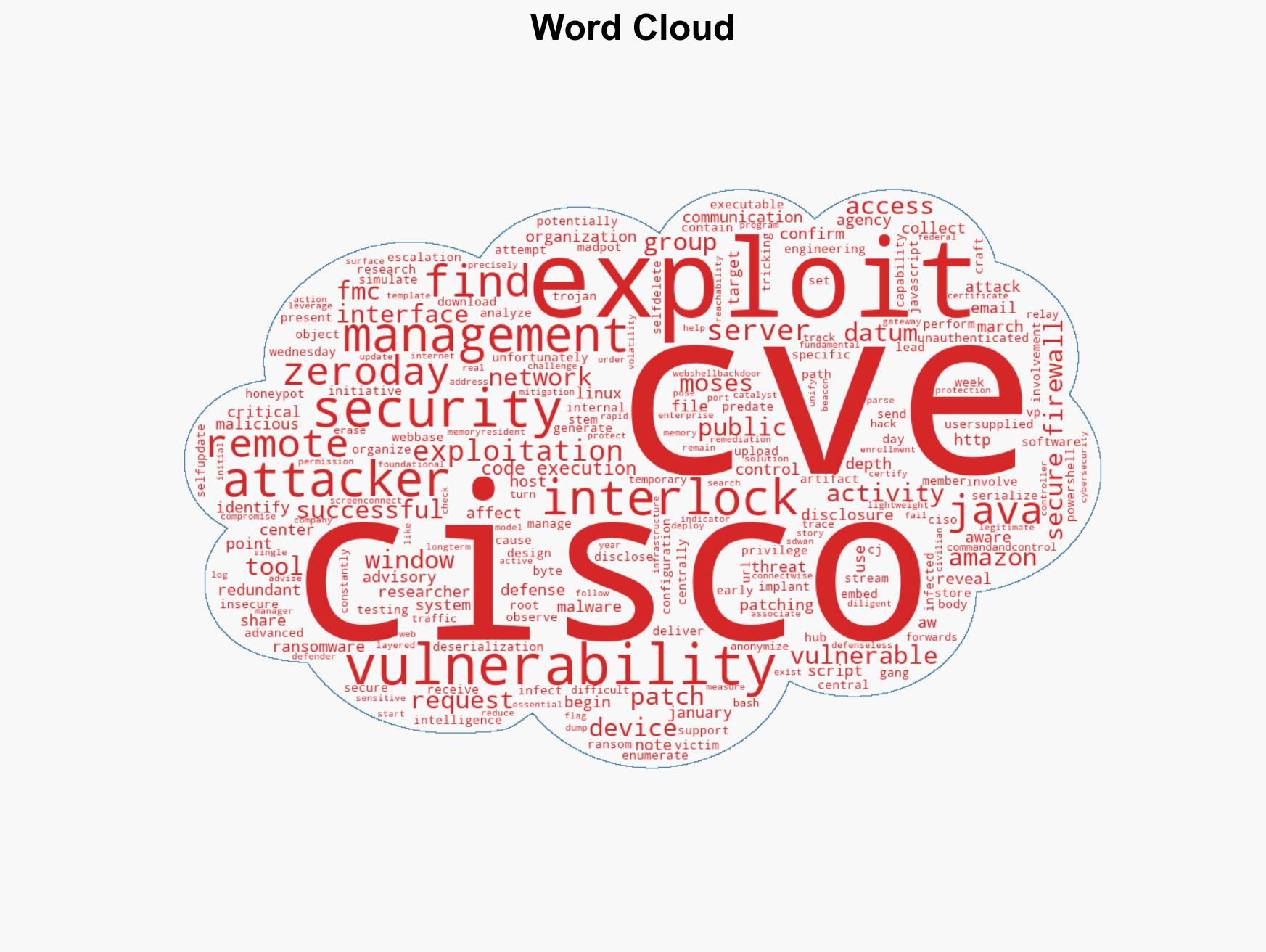
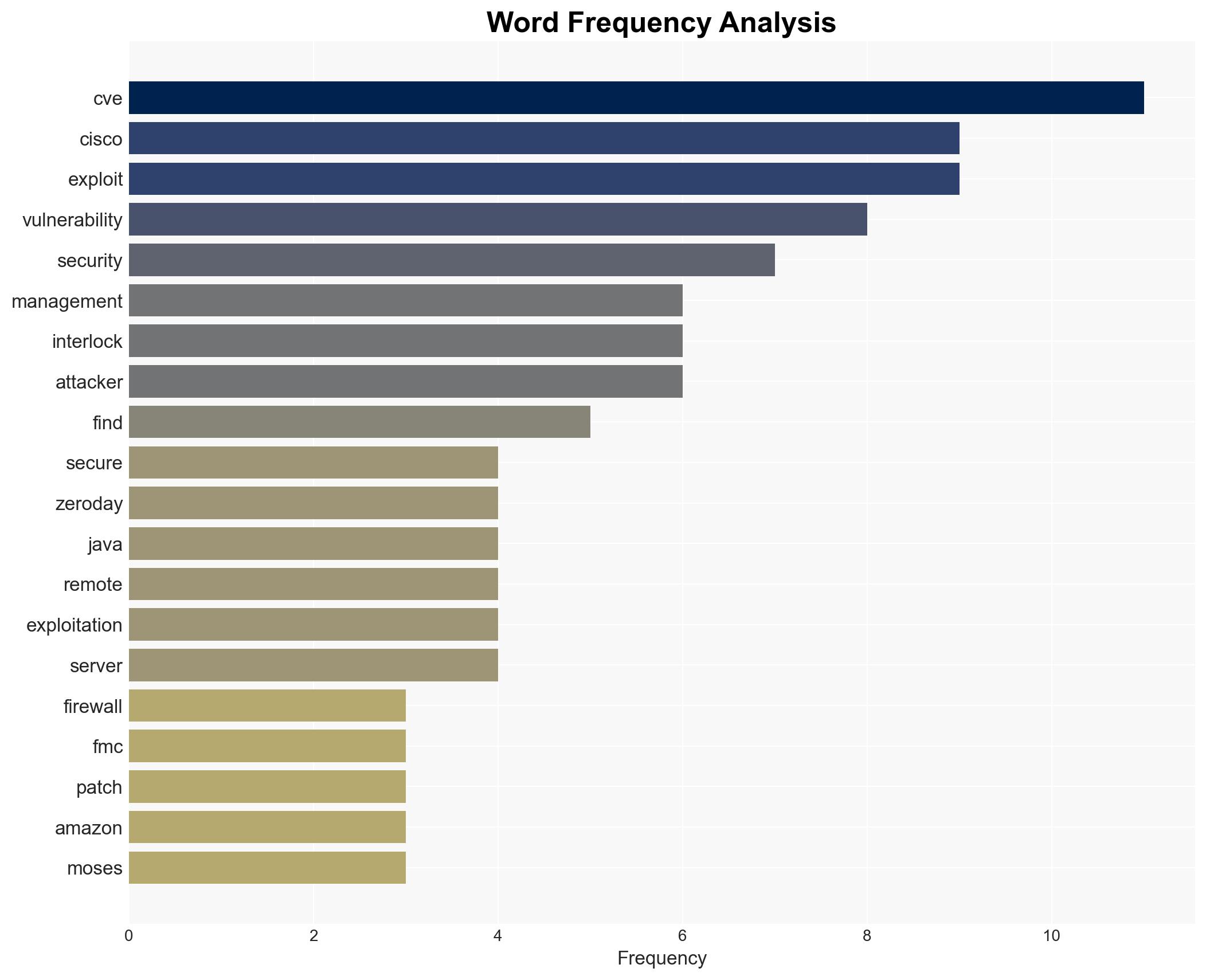
7. Thematic Tags
cybersecurity, ransomware, zero-day vulnerability, threat intelligence, Cisco
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us