Strategies for CISOs to Navigate the Rise of Geopolitical Cyber Threats and Wiper Attacks
Published on: 2026-03-20
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: How CISOs Can Survive the Era of Geopolitical Cyberattacks
1. BLUF (Bottom Line Up Front)
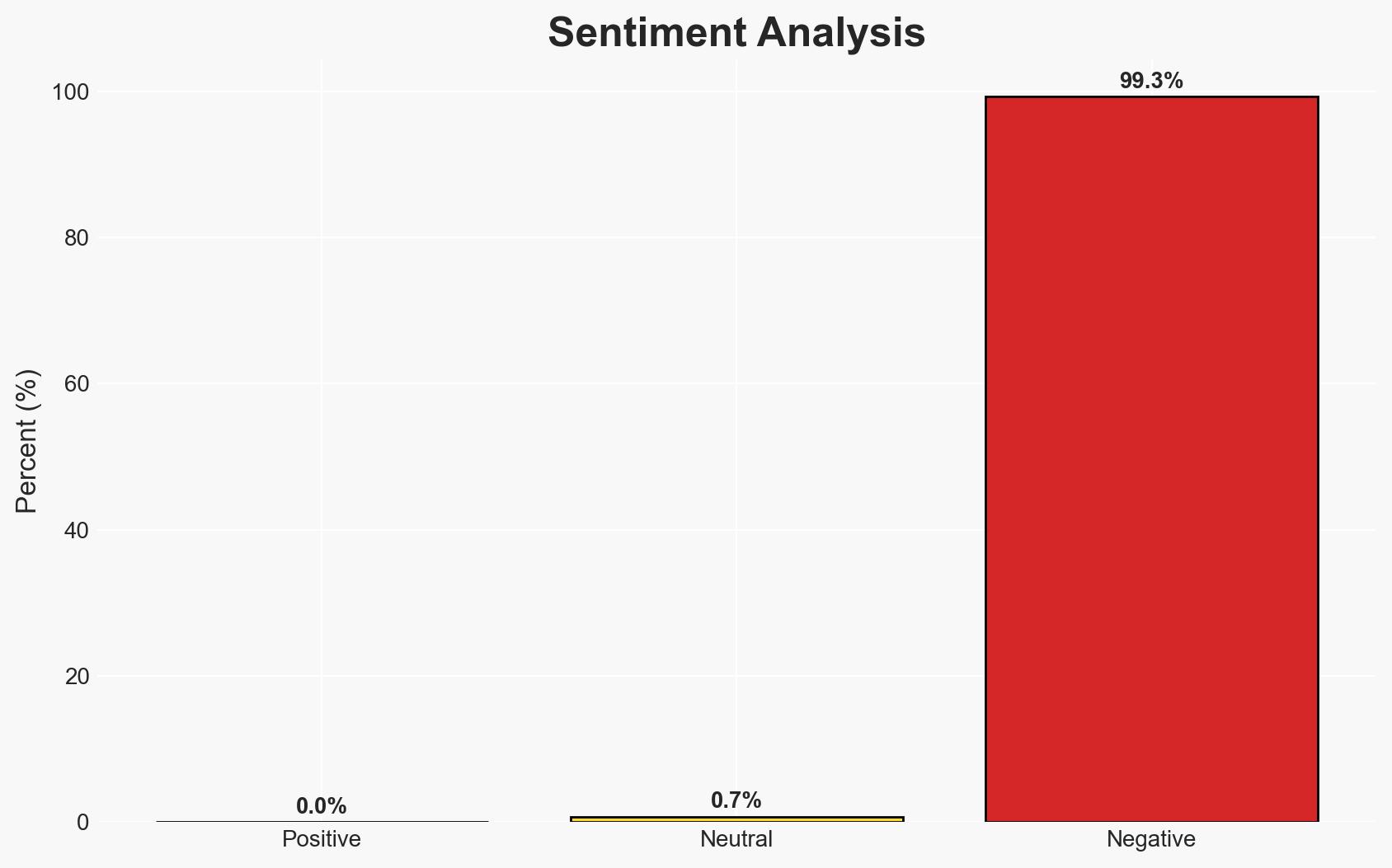
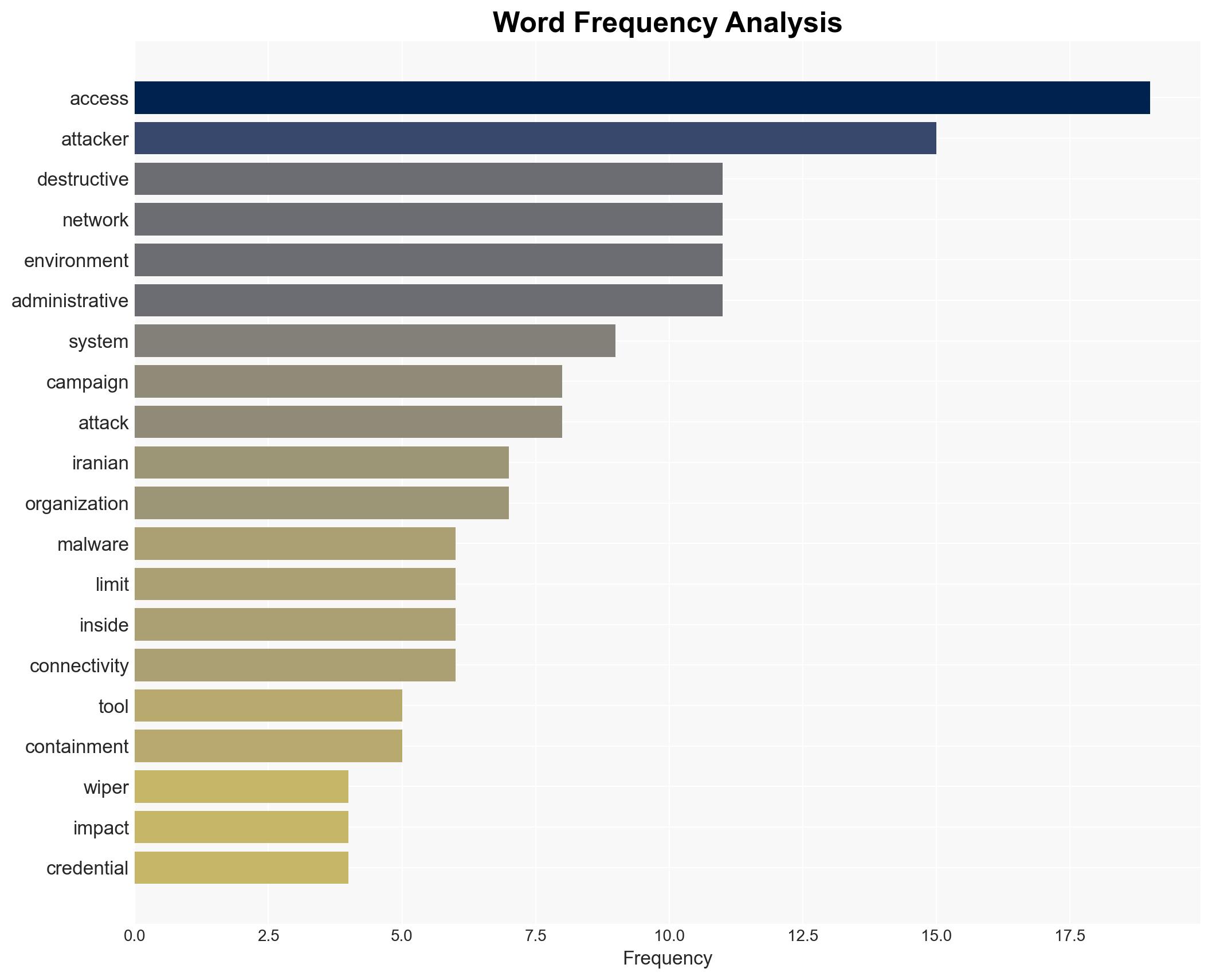
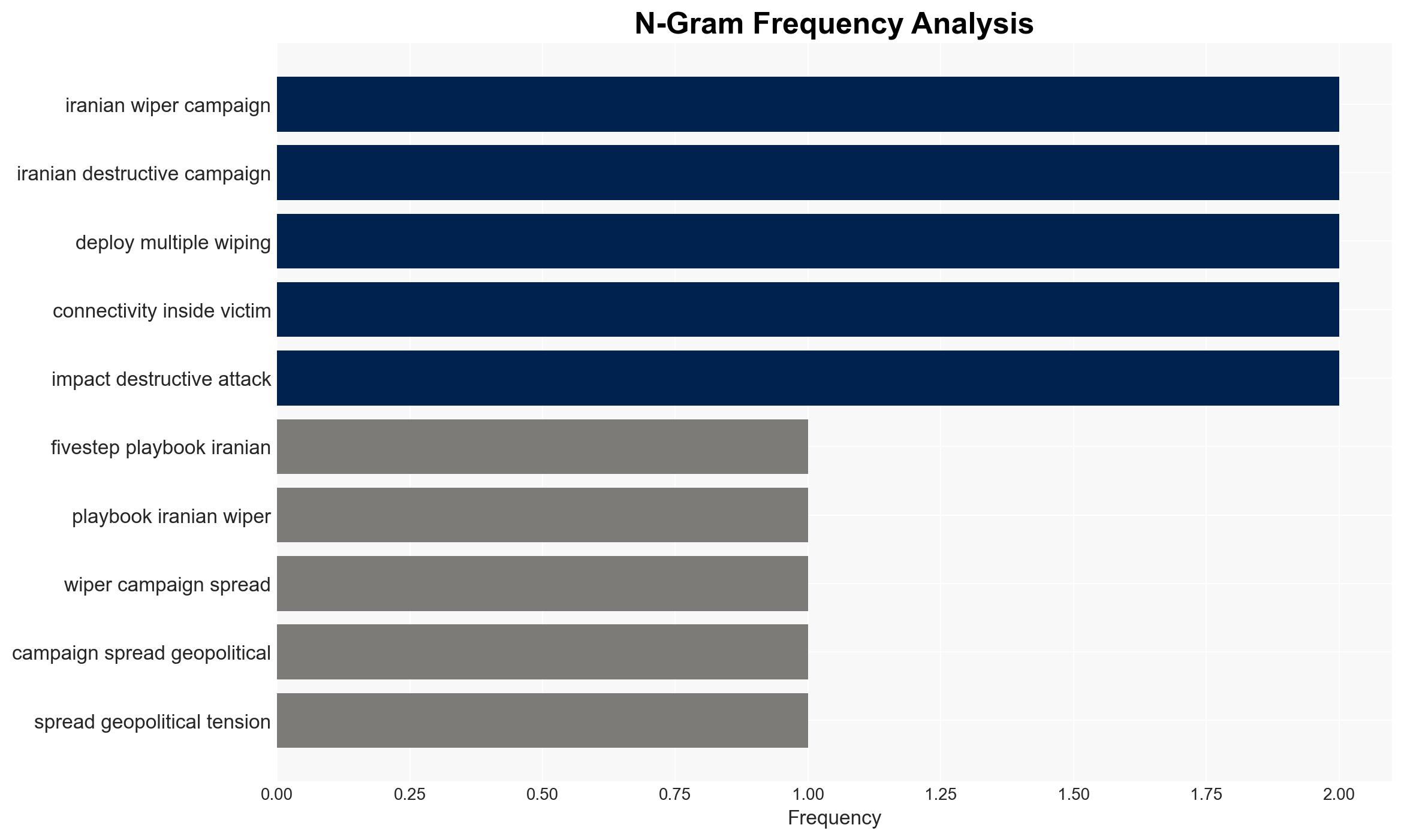
Iranian wiper campaigns represent a significant shift in cyber threats, focusing on operational disruption rather than financial gain. These attacks target critical infrastructure and supply chains, posing a substantial risk to global operations. The most likely hypothesis is that these campaigns will continue to evolve, necessitating a focus on containment and internal controls. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: Iranian wiper campaigns are primarily motivated by geopolitical objectives, aiming to disrupt critical infrastructure as a form of asymmetric warfare. This is supported by the targeting of supply chains and healthcare systems. However, the specific strategic goals remain unclear.
- Hypothesis B: These campaigns are opportunistic, exploiting vulnerabilities in global networks to demonstrate cyber capabilities and exert political pressure. While the scale of attacks suggests strategic intent, the lack of sophisticated malware indicates a focus on exploiting existing network weaknesses.
- Assessment: Hypothesis A is currently better supported due to the targeted nature of the attacks on critical infrastructure, which aligns with known geopolitical tensions involving Iran. Key indicators that could shift this judgment include changes in target selection or the emergence of more sophisticated malware.
3. Key Assumptions and Red Flags
- Assumptions: The primary actors are state-sponsored or politically aligned groups; critical infrastructure remains a key target; current defensive measures are insufficient against manual operations.
- Information Gaps: Detailed motivations behind specific target selections; the extent of state sponsorship or independent operation of groups like Handala.
- Bias & Deception Risks: Potential over-reliance on known patterns of Iranian cyber operations; risk of misattribution due to shared tactics among different actors.
4. Implications and Strategic Risks
The evolution of Iranian wiper campaigns could lead to increased geopolitical tensions and a reevaluation of cyber defense strategies globally. These developments may influence international relations and cybersecurity policies.
- Political / Geopolitical: Potential escalation in cyber conflict between Iran and affected nations, possibly leading to diplomatic strains or sanctions.
- Security / Counter-Terrorism: Increased focus on protecting critical infrastructure from cyber threats, requiring enhanced coordination among security agencies.
- Cyber / Information Space: Greater emphasis on internal network security and the development of advanced detection and response capabilities.
- Economic / Social: Disruptions in supply chains and healthcare could lead to economic instability and public unrest in affected regions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of critical infrastructure networks; conduct comprehensive security audits focusing on internal controls.
- Medium-Term Posture (1–12 months): Develop partnerships with international cybersecurity agencies; invest in training for incident response teams.
- Scenario Outlook:
- Best Case: Improved defenses mitigate the impact of future attacks, leading to reduced geopolitical tensions.
- Worst Case: Escalation of cyber conflicts results in widespread infrastructure disruptions and economic instability.
- Most Likely: Continued sporadic attacks with incremental improvements in defense strategies and international cooperation.
6. Key Individuals and Entities
- Handala (Iran-linked group)
- Stryker (Fortune 500 manufacturer)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
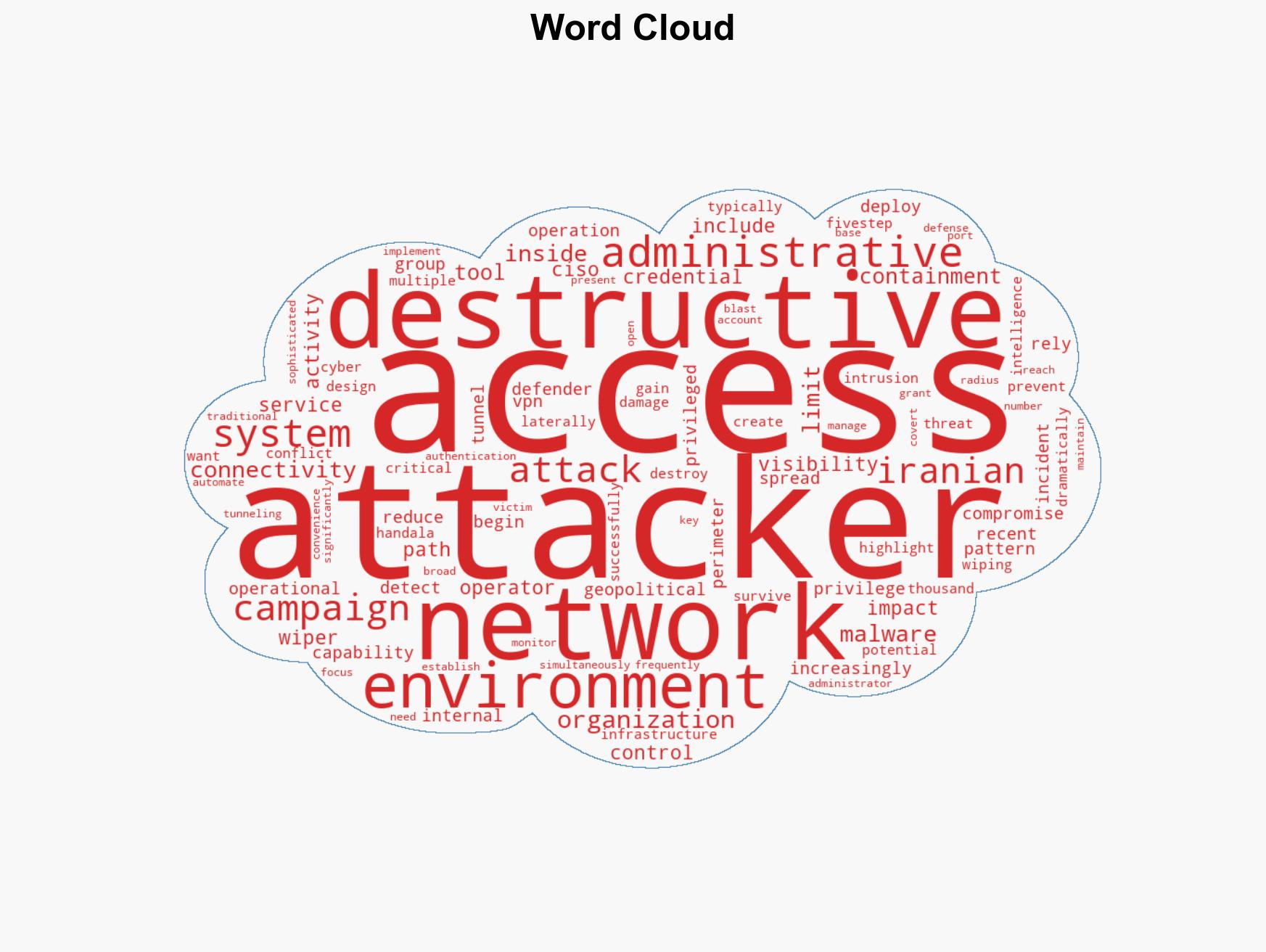
cybersecurity, geopolitical cyberattacks, critical infrastructure, Iranian wiper campaigns, cybersecurity strategy, cyber defense, supply chain security, asymmetric warfare
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us