Israel’s Targeted Strikes on Iranian Leaders: Superior Intelligence and Ground Informants at Play
Published on: 2026-03-20
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: How Israel assassinates its foes Their intelligence is just so much better
1. BLUF (Bottom Line Up Front)
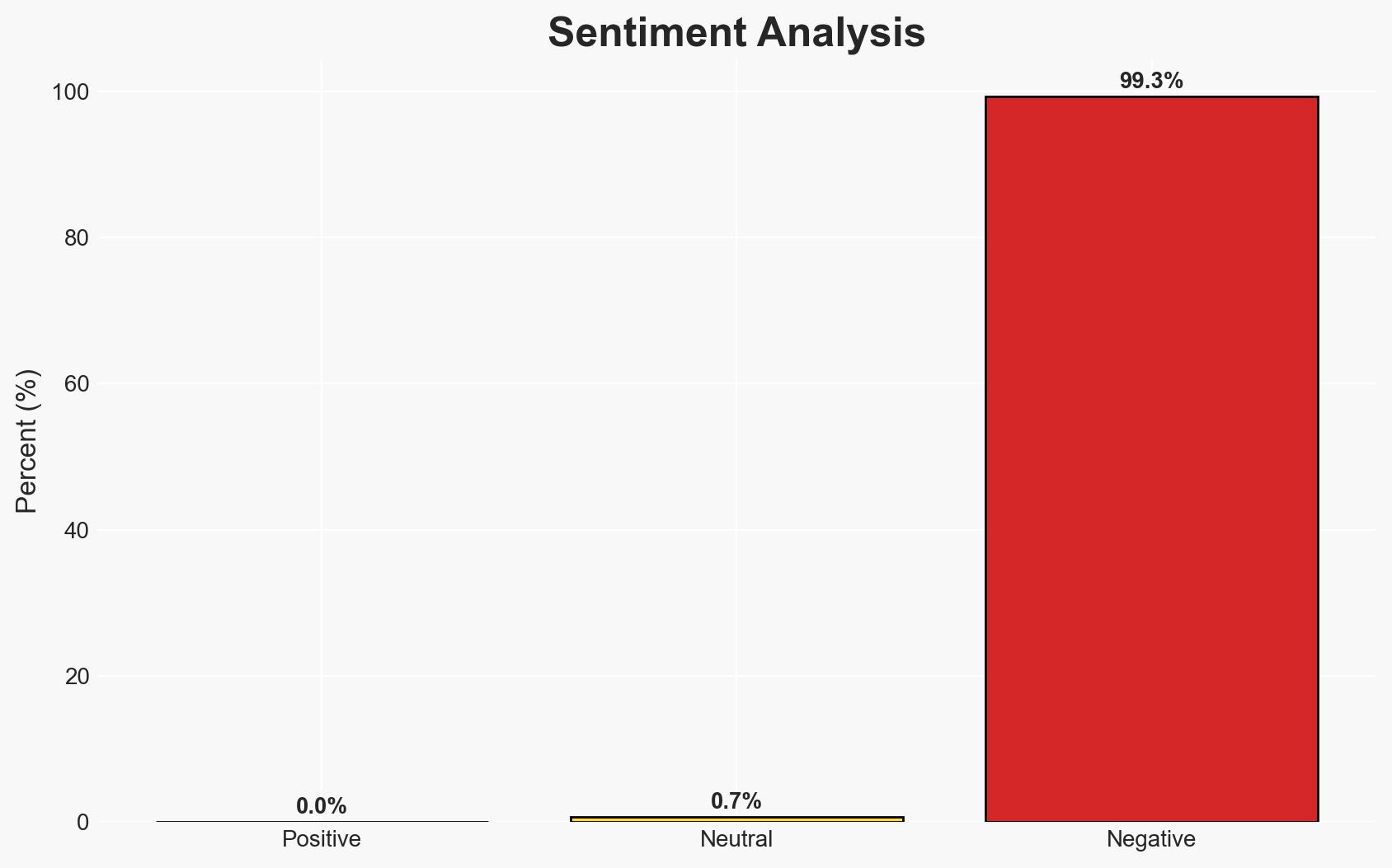
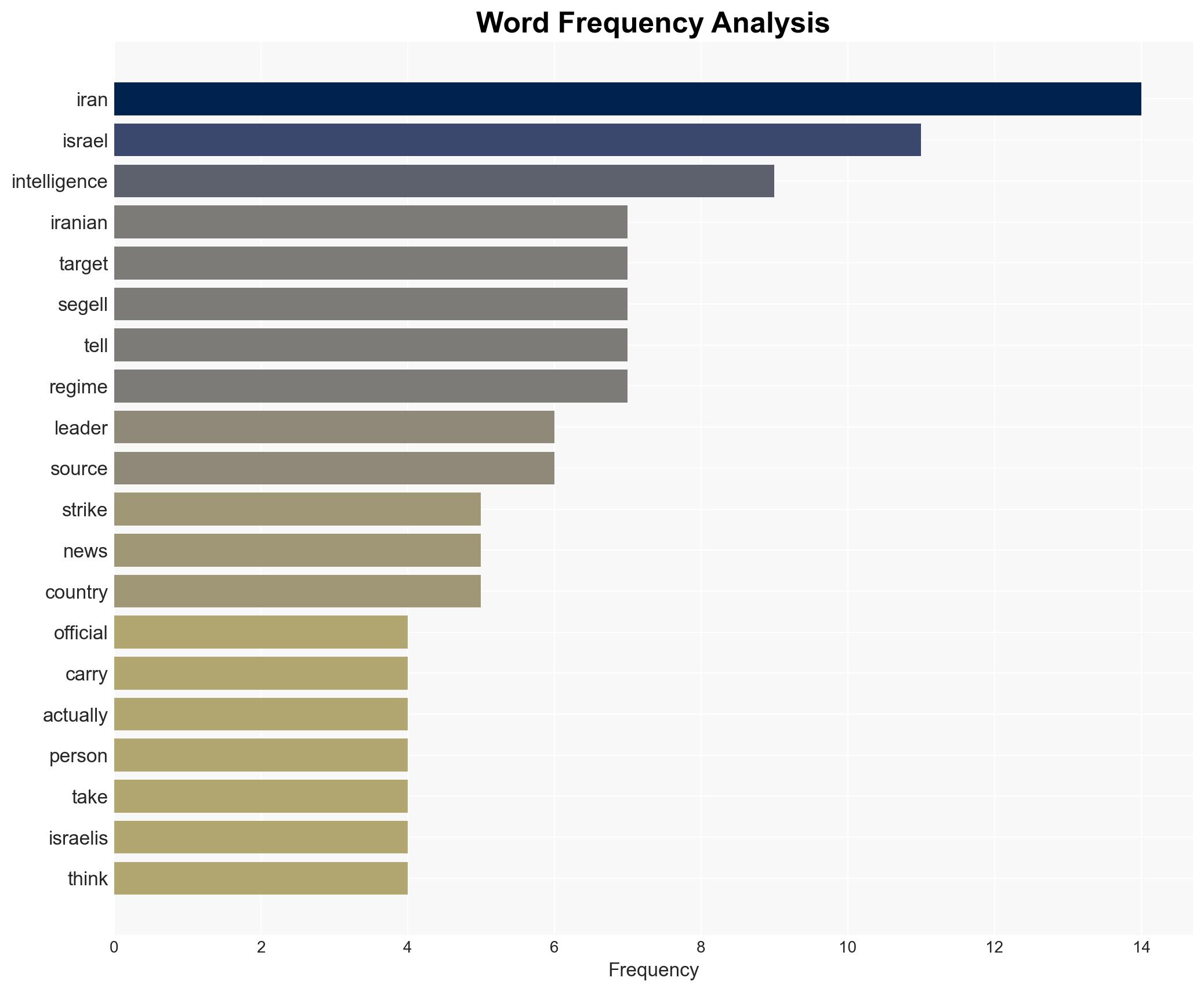
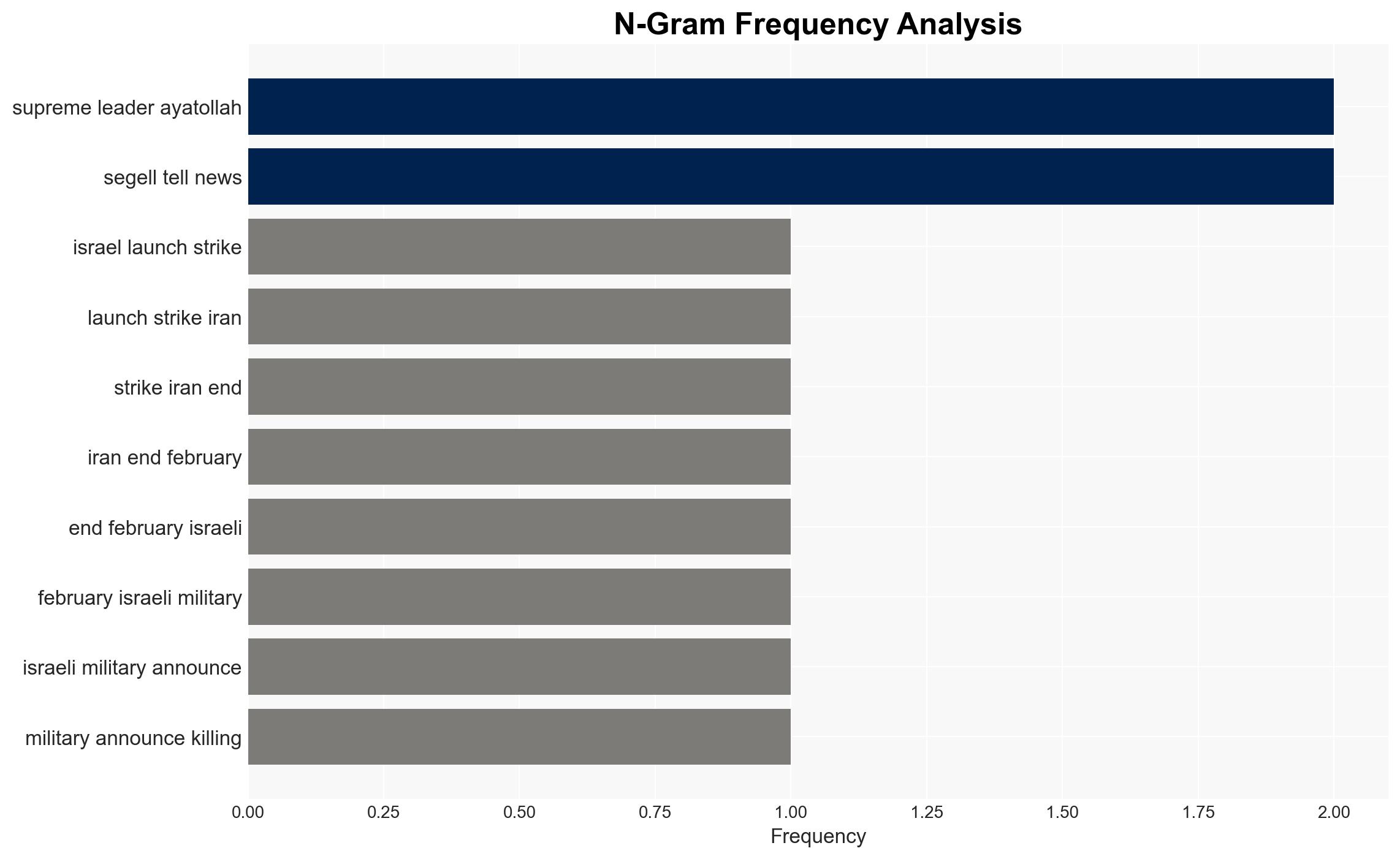
Israel’s targeted assassinations of Iranian officials are primarily driven by superior intelligence capabilities, leveraging both human informants and electronic surveillance. This approach is supported by collaboration with regional partners such as Saudi Arabia and the United States. The most likely hypothesis is that Israel will continue these operations to weaken Iranian influence, with moderate confidence in this assessment due to potential information gaps and deception risks.
2. Competing Hypotheses
- Hypothesis A: Israel’s assassinations of Iranian officials are primarily enabled by a robust network of human informants and electronic surveillance, supported by regional intelligence collaboration. Evidence includes reported use of informants and electronic tracking, but uncertainties remain about the reliability and scope of these sources.
- Hypothesis B: The assassinations are largely a result of opportunistic intelligence gathering and isolated incidents rather than a coordinated strategy. This hypothesis is less supported due to the reported systematic approach and collaboration with multiple intelligence partners.
- Assessment: Hypothesis A is currently best supported due to consistent reports of systematic intelligence operations and regional collaboration. Key indicators that could shift this judgment include evidence of significant operational failures or shifts in regional alliances.
3. Key Assumptions and Red Flags
- Assumptions: Israel has reliable intelligence sources within Iran; regional partners are actively sharing intelligence; electronic surveillance is effectively penetrating Iranian communications.
- Information Gaps: Specific details on the extent of Israel’s human intelligence network within Iran; the exact nature of intelligence-sharing agreements with partners.
- Bias & Deception Risks: Potential over-reliance on informants who may have conflicting agendas; risk of misinformation from adversaries aiming to mislead Israeli operations.
4. Implications and Strategic Risks
The continuation of Israeli targeted assassinations could exacerbate regional tensions and provoke retaliatory actions from Iran, potentially destabilizing the Middle East further.
- Political / Geopolitical: Escalation of hostilities between Israel and Iran, impacting regional alliances and diplomatic relations.
- Security / Counter-Terrorism: Increased threat of retaliatory attacks against Israeli interests globally; potential for heightened security measures.
- Cyber / Information Space: Possible cyber retaliation by Iran targeting Israeli infrastructure; increased propaganda efforts to sway public opinion.
- Economic / Social: Potential disruptions in oil markets due to regional instability; increased social unrest within Iran as a result of internal resistance movements.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Iranian communications and movements; strengthen security protocols for Israeli assets abroad.
- Medium-Term Posture (1–12 months): Develop resilience measures against potential cyber threats; foster intelligence-sharing partnerships with regional allies.
- Scenario Outlook: Best: De-escalation through diplomatic channels; Worst: Full-scale regional conflict; Most-Likely: Continued low-intensity conflict with periodic escalations.
6. Key Individuals and Entities
- Ayatollah Mojtaba Khamenei
- Islamic Revolutionary Guard Corps
- Glen Segell
- Mark Cancian
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
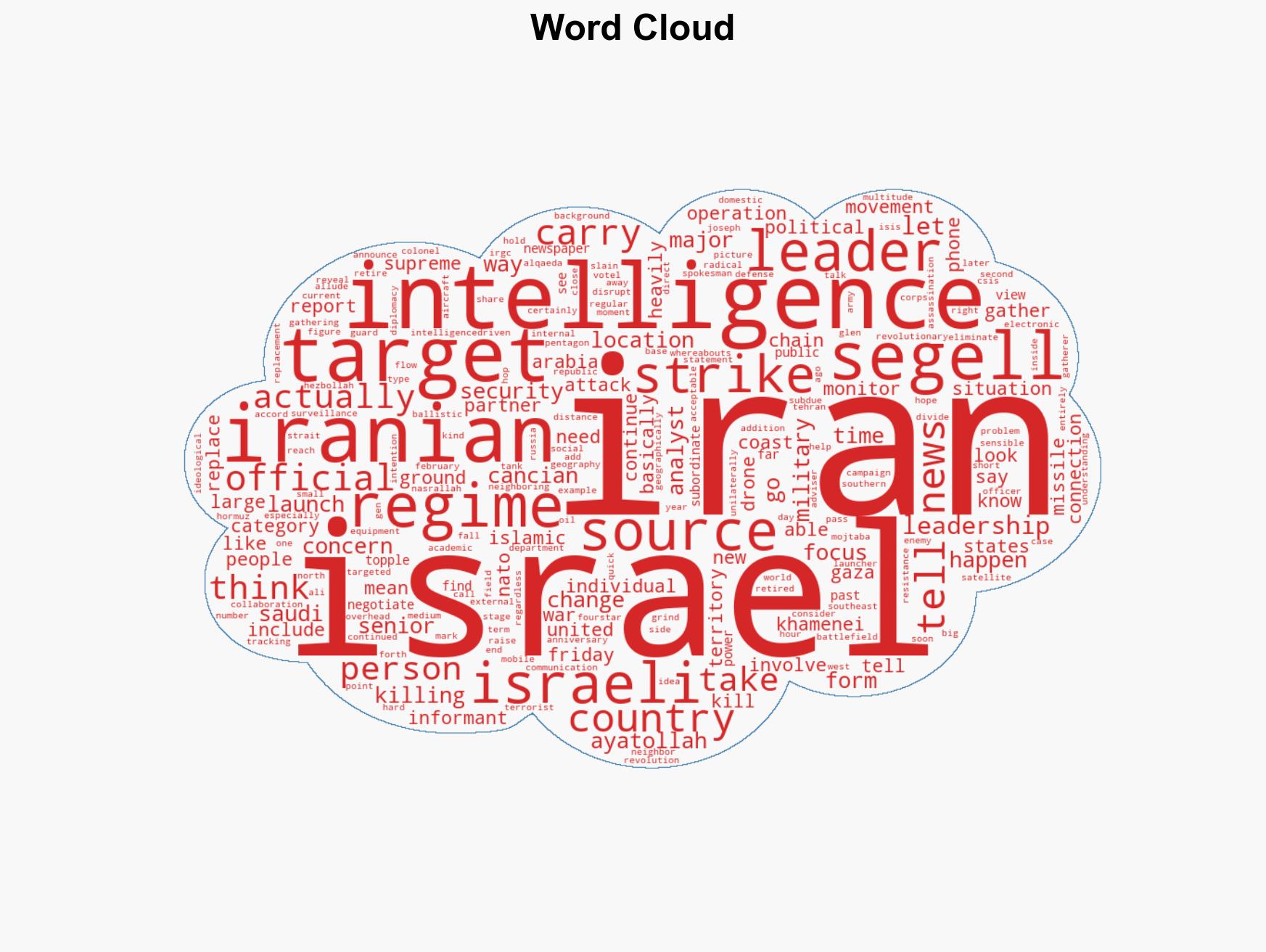
Counter-Terrorism, intelligence operations, regional security, Iran-Israel relations, electronic surveillance, geopolitical tensions, Middle East stability
Structured Analytic Techniques Applied
- ACH 2.0: Reconstruct likely threat actor intentions via hypothesis testing and structured refutation.
- Indicators Development: Track radicalization signals and propaganda patterns to anticipate operational planning.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Counter-Terrorism Briefs ·
Daily Summary ·
Support us