CTI-REALM: Microsoft Launches Open-Source Benchmark for AI-Driven Cyber Threat Detection Engineering
Published on: 2026-03-20
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
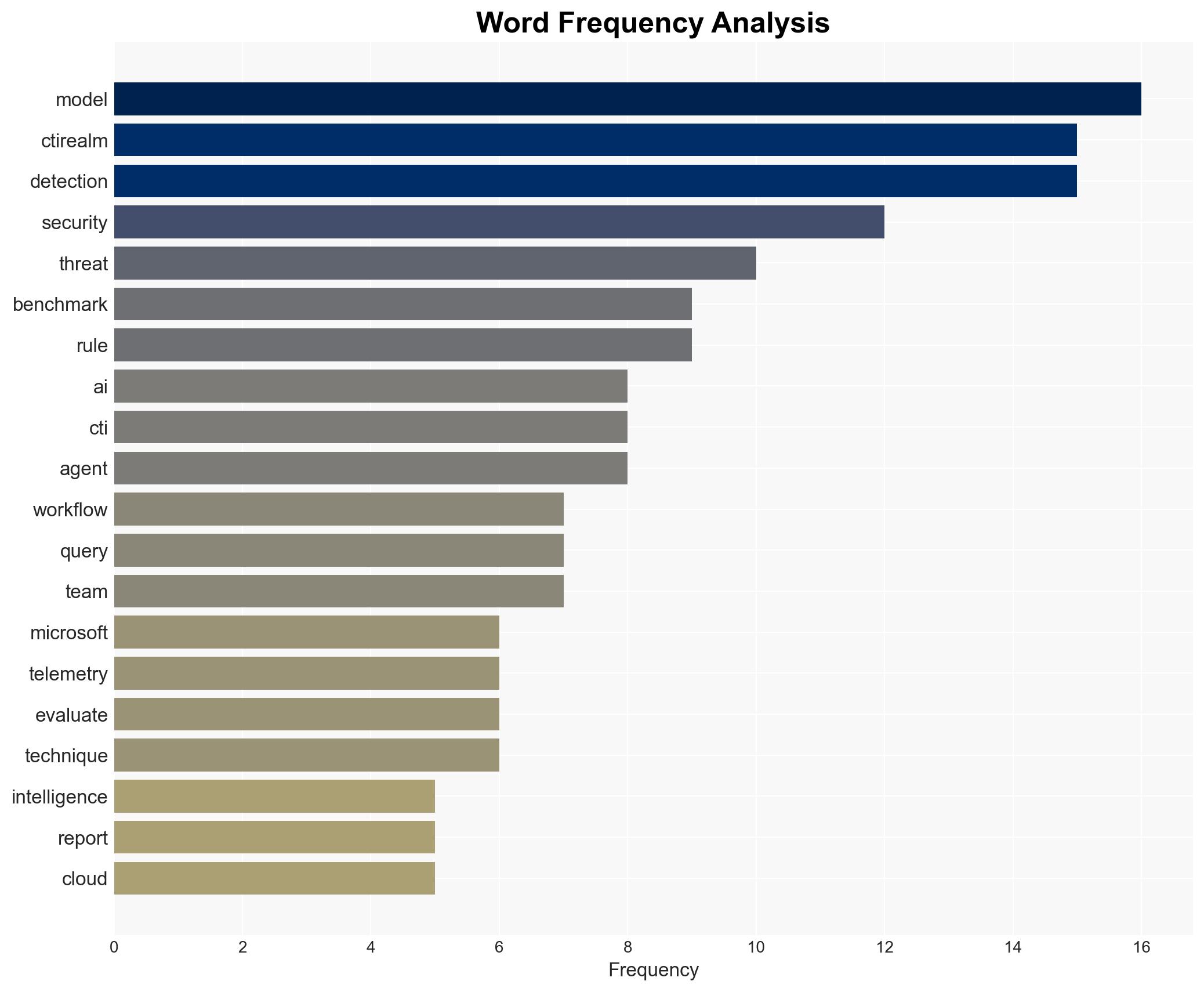
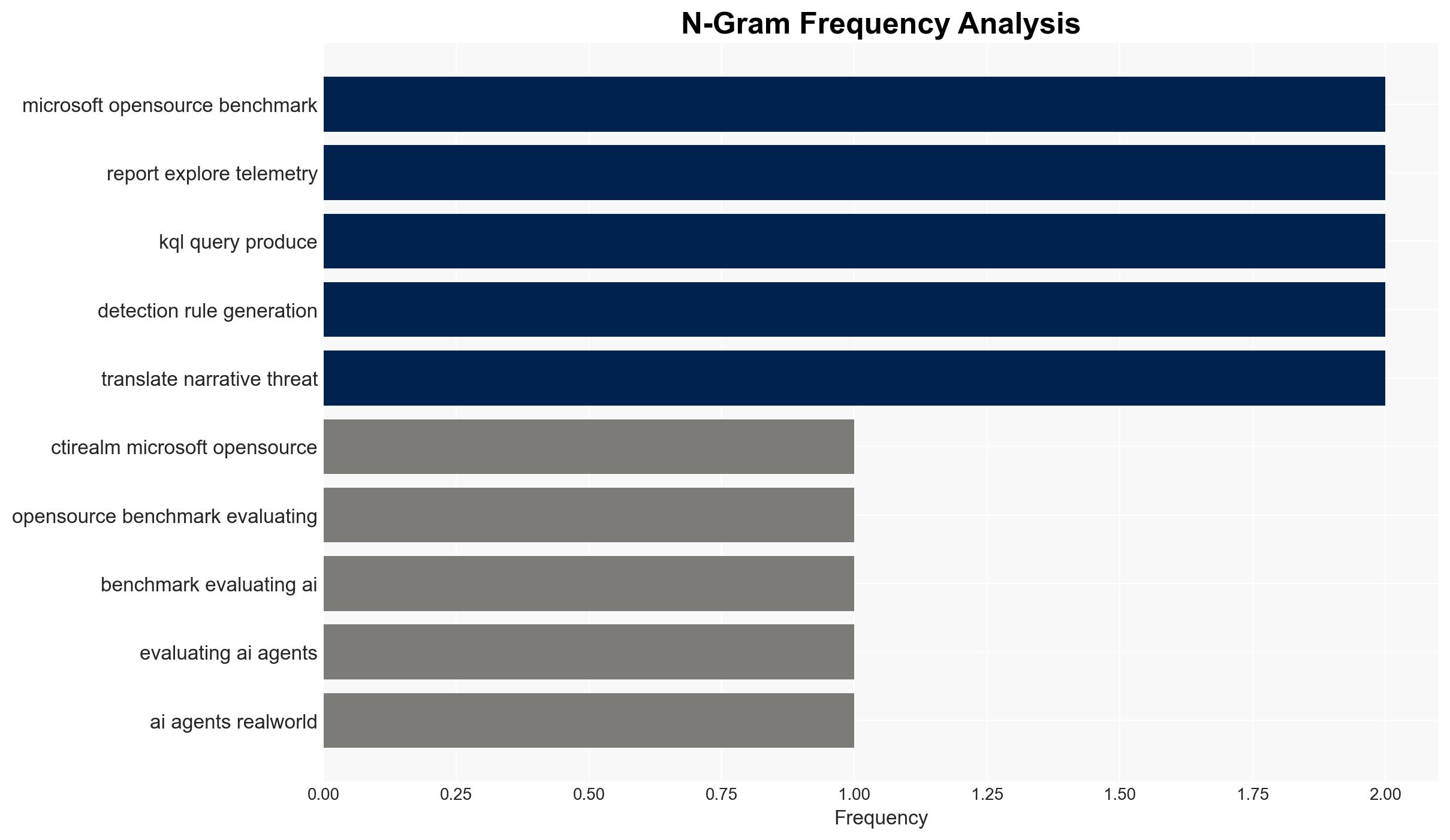
Intelligence Report: CTI-REALM A new benchmark for end-to-end detection rule generation with AI agents
1. BLUF (Bottom Line Up Front)
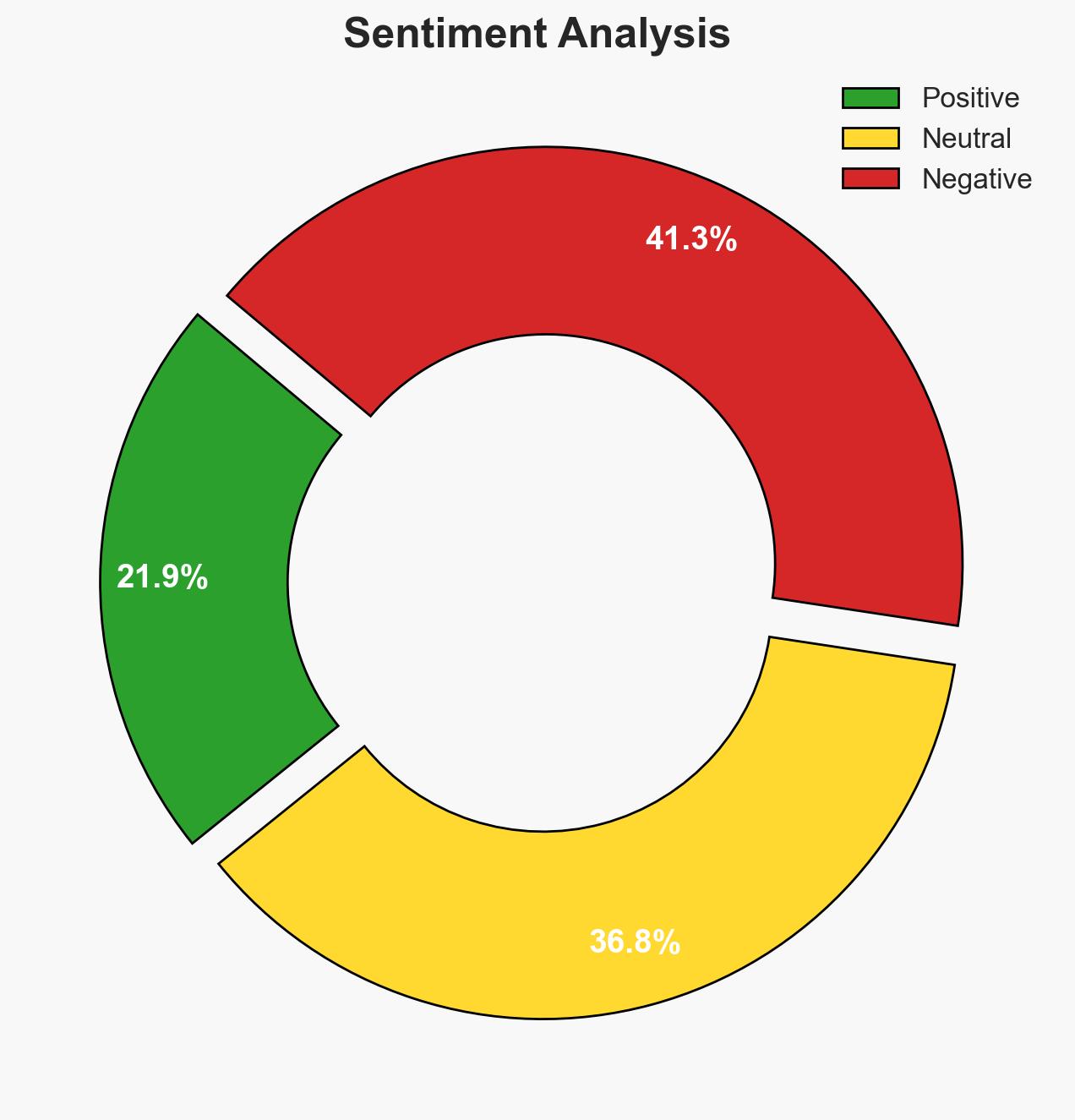
CTI-REALM represents a significant advancement in cybersecurity benchmarks by focusing on the operationalization of threat intelligence into actionable detection logic. This development primarily affects cybersecurity professionals and organizations utilizing AI for threat detection. The most likely hypothesis is that CTI-REALM will enhance the effectiveness of AI-driven cybersecurity measures. Overall confidence in this judgment is moderate, given the current lack of comprehensive real-world validation data.
2. Competing Hypotheses
- Hypothesis A: CTI-REALM will significantly improve AI-driven detection capabilities by providing a comprehensive benchmark that tests the full detection workflow. Supporting evidence includes the benchmark’s focus on real-world scenarios and its open-source nature, which encourages widespread adoption and improvement. Key uncertainties involve the actual adoption rate and integration challenges within existing systems.
- Hypothesis B: CTI-REALM may have limited impact due to potential integration challenges and the complexity of adapting existing AI models to new benchmarks. Contradicting evidence includes the potential for resistance from organizations with established detection systems and the need for substantial resource investment to adapt to the new benchmark.
- Assessment: Hypothesis A is currently better supported due to Microsoft’s established influence in the cybersecurity domain and the benchmark’s alignment with industry needs for comprehensive detection capabilities. Indicators that could shift this judgment include reports of integration difficulties or lack of measurable improvements in detection efficacy.
3. Key Assumptions and Red Flags
- Assumptions: AI models can effectively translate CTI into detection logic; organizations have the resources to adopt new benchmarks; CTI-REALM will be regularly updated to reflect evolving threats.
- Information Gaps: Lack of data on real-world performance improvements post-adoption; unclear how quickly organizations can integrate CTI-REALM into existing workflows.
- Bias & Deception Risks: Potential cognitive bias towards overestimating AI capabilities; source bias due to Microsoft’s vested interest in promoting its own benchmark.
4. Implications and Strategic Risks
CTI-REALM’s introduction could reshape how organizations approach AI-driven threat detection, potentially leading to more robust cybersecurity postures. However, the transition may also expose gaps in current systems and require significant resource allocation.
- Political / Geopolitical: Increased reliance on AI in cybersecurity could influence national security policies and international cyber norms.
- Security / Counter-Terrorism: Enhanced detection capabilities may deter cyber threats but could also drive adversaries to develop more sophisticated attack methods.
- Cyber / Information Space: The benchmark could lead to improved information sharing and collaboration across the cybersecurity community.
- Economic / Social: Organizations may face increased costs associated with adopting and integrating new AI benchmarks, impacting budget allocations and potentially leading to workforce adjustments.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor industry feedback on CTI-REALM adoption; assess organizational readiness for integration; initiate pilot programs to test the benchmark’s applicability.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms to enhance AI capabilities; invest in training for staff on new detection workflows; evaluate the benchmark’s impact on detection efficacy.
- Scenario Outlook:
- Best: Widespread adoption leads to significant improvements in threat detection and reduced cyber incidents.
- Worst: Integration challenges and high costs limit adoption, resulting in minimal impact on overall cybersecurity posture.
- Most-Likely: Gradual adoption with measurable improvements in detection capabilities as organizations adapt to the new benchmark.
6. Key Individuals and Entities
- Microsoft
- Datadog Security Labs
- Palo Alto Networks
- Splunk
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
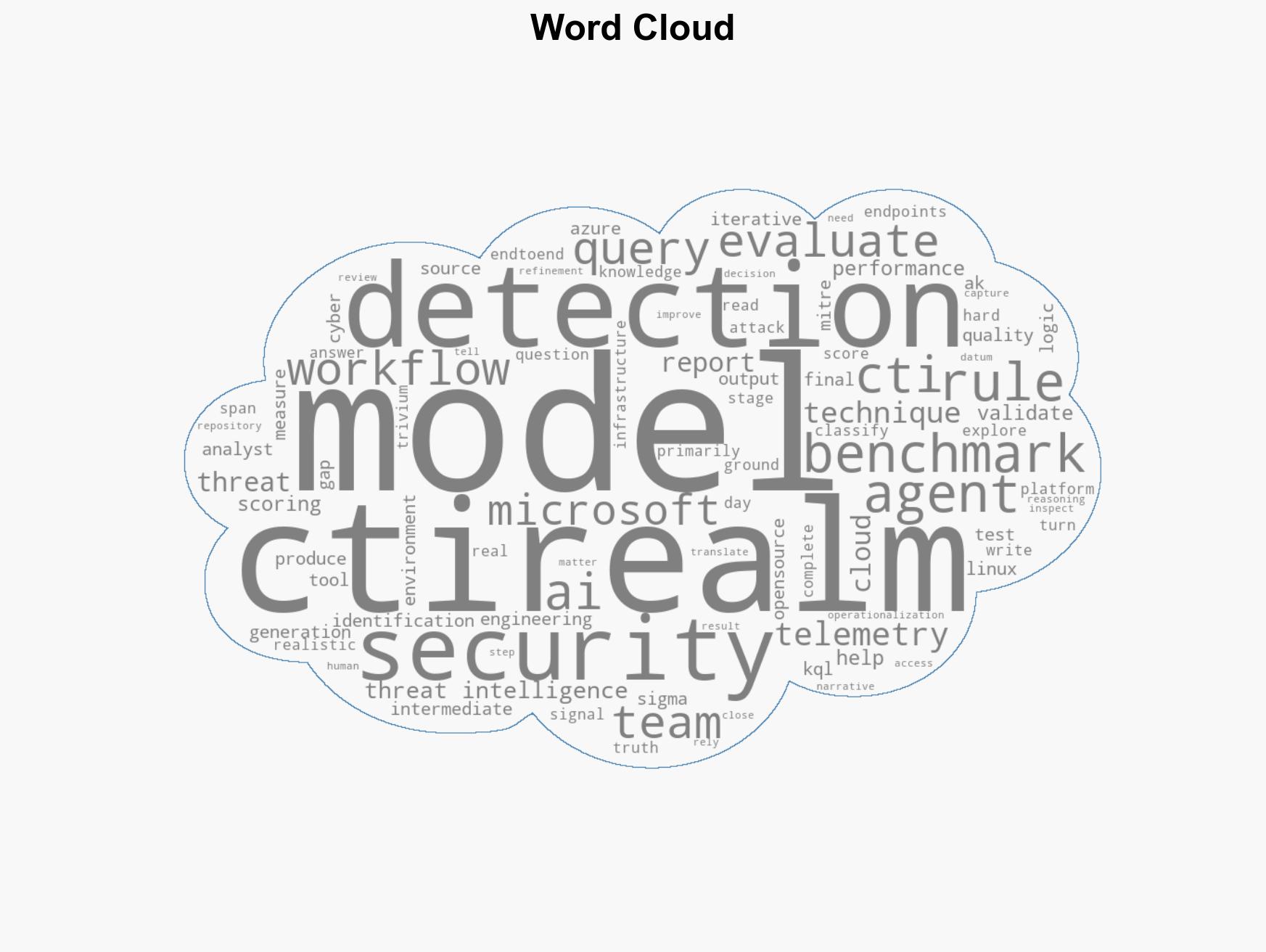
cybersecurity, AI-driven detection, threat intelligence, Microsoft, open-source benchmarks, detection logic, cybersecurity collaboration
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us