Young Australian warns peers after being hacked and held for ransom, highlighting rising cybercrime risks.
Published on: 2026-03-21
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Ash was hacked She wants you to know ‘you could be next’
1. BLUF (Bottom Line Up Front)
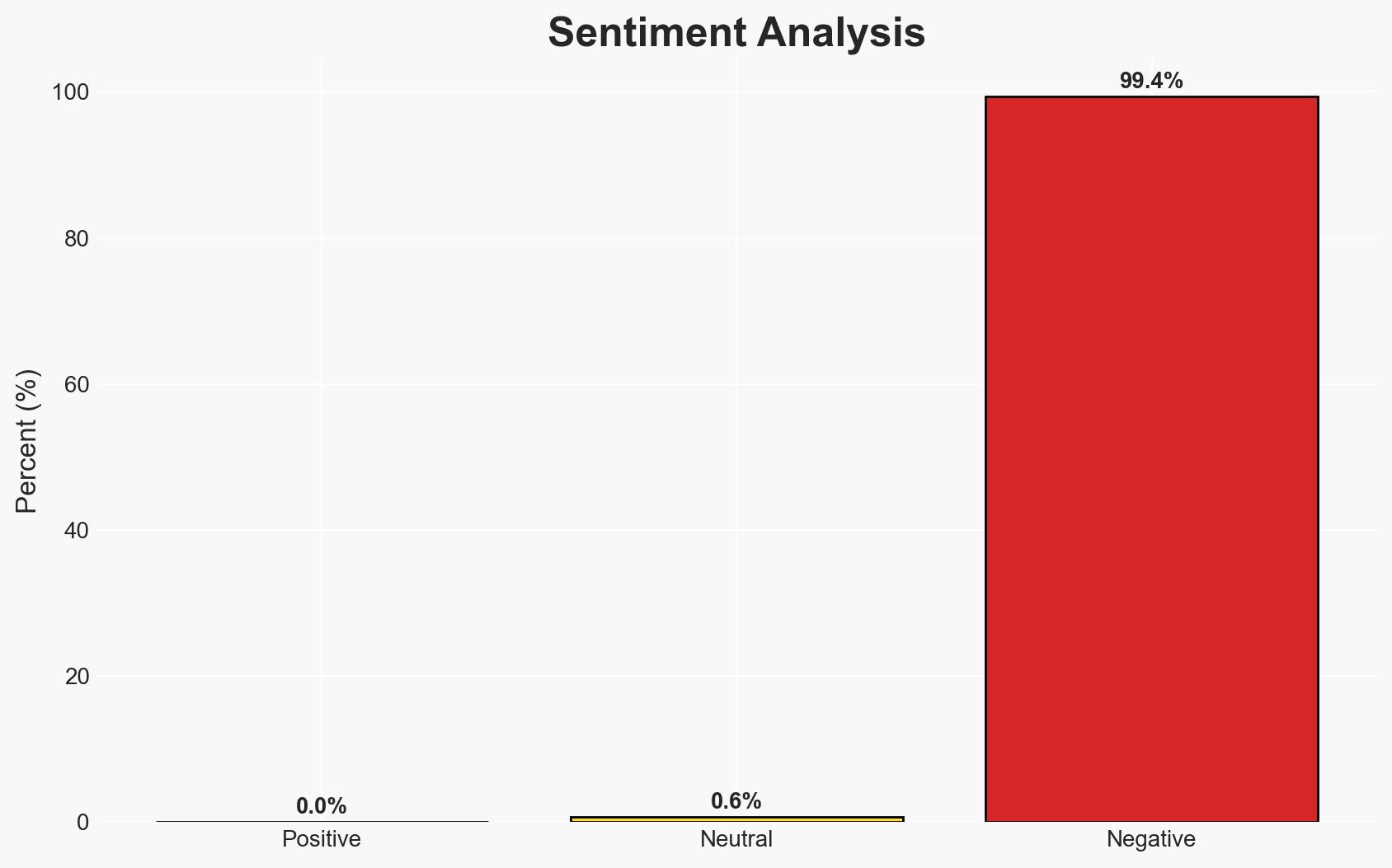
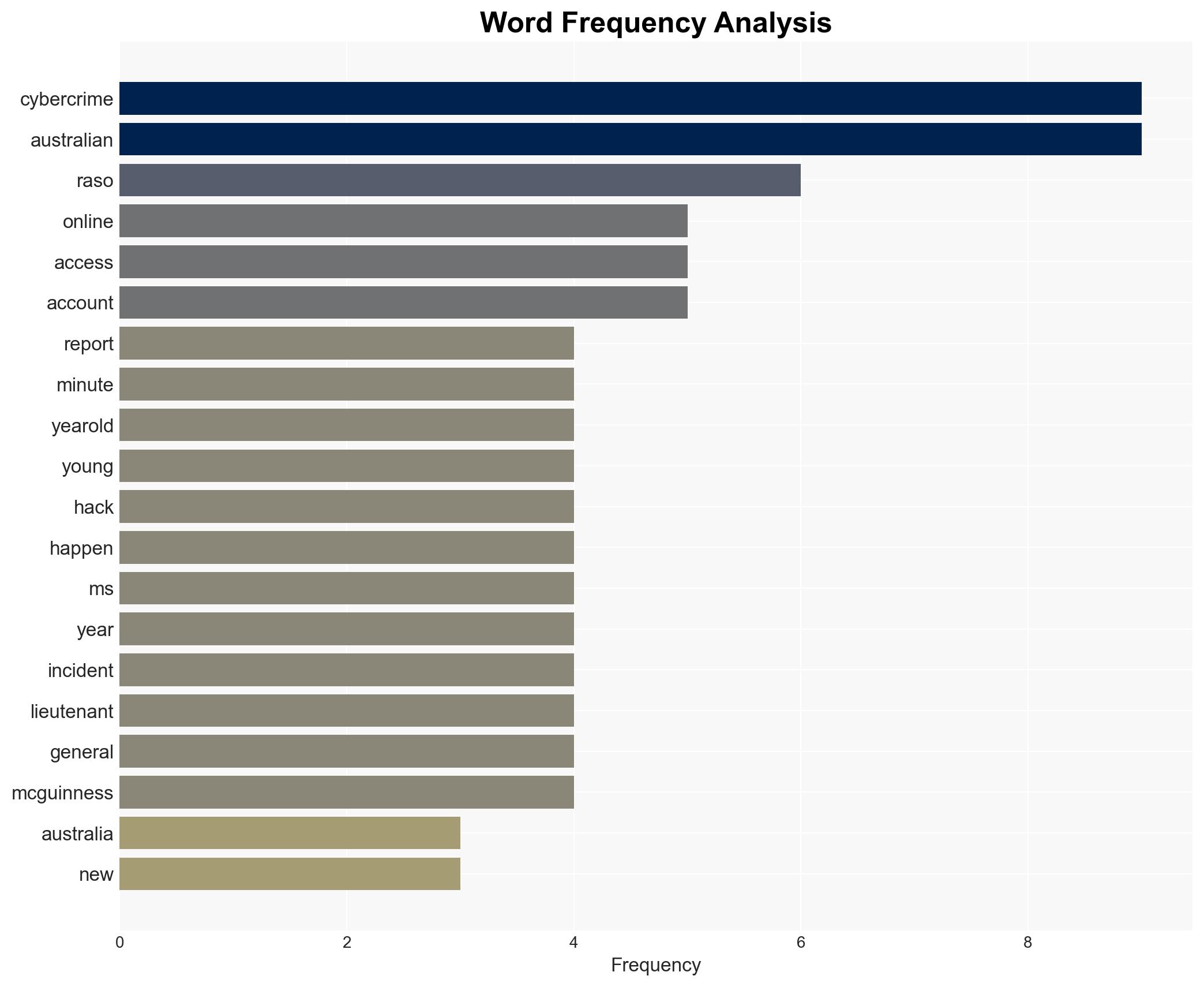
The increasing frequency of cybercrime in Australia, particularly targeting younger demographics, highlights a significant vulnerability in online security practices. The case of Ash Raso exemplifies the personal and financial risks involved. The most likely hypothesis is that inadequate cybersecurity measures among young Australians are contributing to the rise in incidents. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
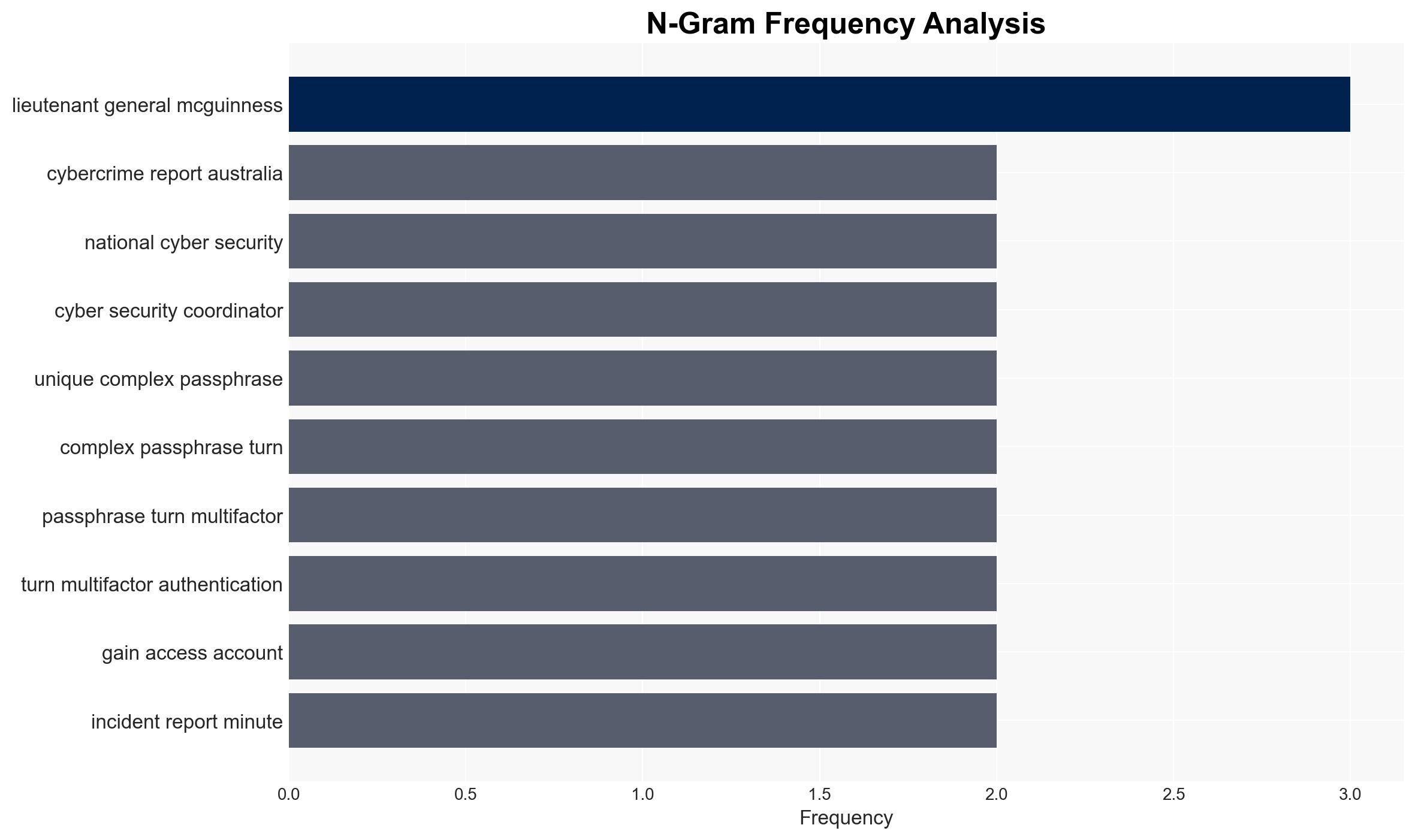
- Hypothesis A: The rise in cybercrime incidents is primarily due to inadequate cybersecurity practices among younger Australians, as evidenced by their tendency to reuse passwords and use weak security measures. This is supported by the reported data and expert opinions. Key uncertainties include the actual scale of unreported incidents and the effectiveness of current educational campaigns.
- Hypothesis B: The increase in cybercrime is driven by more sophisticated cybercriminal tactics rather than user negligence. This hypothesis is less supported due to the lack of specific evidence of advanced tactics in the provided data. However, it cannot be entirely dismissed without further technical analysis of the attacks.
- Assessment: Hypothesis A is currently better supported due to the explicit mention of poor security practices among young Australians. Indicators that could shift this judgment include new evidence of advanced cybercriminal methods or changes in reporting trends.
3. Key Assumptions and Red Flags
- Assumptions: Young Australians’ cybersecurity practices are representative of broader trends; reported cybercrime statistics accurately reflect the situation; educational efforts are not sufficiently impacting behavior.
- Information Gaps: Detailed breakdown of attack vectors used in these incidents; comprehensive data on unreported cybercrimes; effectiveness of current cybersecurity education programs.
- Bias & Deception Risks: Potential bias in self-reported data on password practices; media sensationalism affecting perception of threat levels; possible underreporting or misreporting of incidents.
4. Implications and Strategic Risks
The ongoing trend of increasing cybercrime incidents could lead to heightened public concern and demand for stronger cybersecurity measures. This may influence policy decisions and resource allocation.
- Political / Geopolitical: Increased pressure on government to enhance national cybersecurity infrastructure and international cooperation.
- Security / Counter-Terrorism: Potential for cybercriminal tactics to be adopted by terrorist groups, increasing complexity of threat landscape.
- Cyber / Information Space: Escalation in cybercrime could lead to more aggressive cybersecurity policies and potential overreach in surveillance.
- Economic / Social: Economic impact from cybercrime losses could affect consumer confidence and business operations, particularly in digital sectors.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase public awareness campaigns focusing on cybersecurity best practices; enhance monitoring of cybercrime trends and patterns.
- Medium-Term Posture (1–12 months): Develop partnerships with technology firms to improve cybersecurity tools; invest in educational programs targeting vulnerable demographics.
- Scenario Outlook:
- Best: Successful reduction in cybercrime incidents through improved public awareness and security practices.
- Worst: Continued rise in incidents leading to significant economic and social disruption.
- Most-Likely: Gradual improvement in security practices with ongoing challenges due to evolving cyber threats.
6. Key Individuals and Entities
- Lieutenant General Michelle McGuinness – Australia’s National Cyber Security Coordinator
- Ash Raso – Cybercrime victim
- Not clearly identifiable from open sources in this snippet for other entities.
7. Thematic Tags
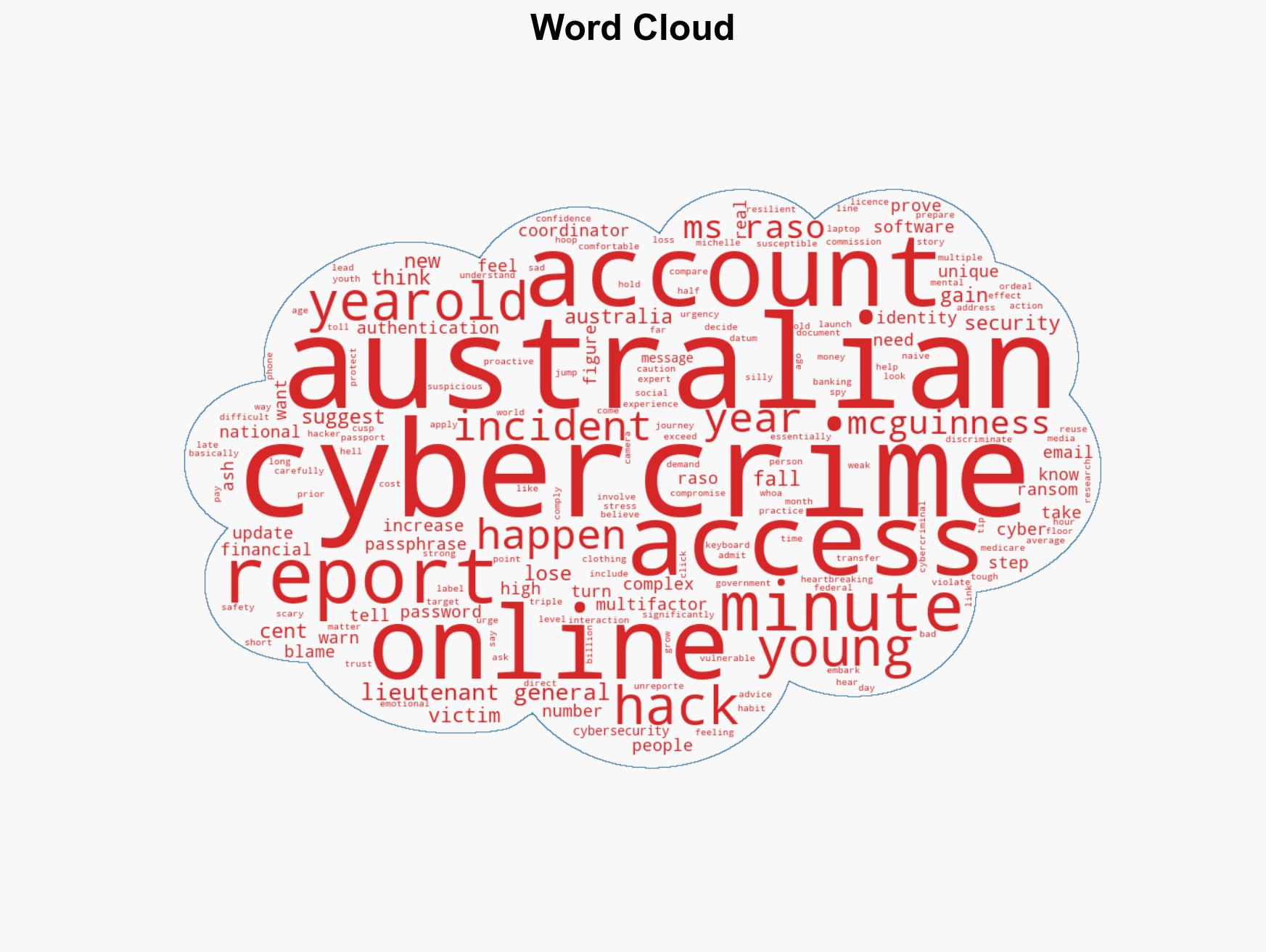
cybersecurity, cybercrime, online safety, digital vulnerability, public awareness, youth cybersecurity, economic impact
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us