Over 14,000 Devices Compromised in Major Cyberattack Linked to New KadNap Malware
Published on: 2026-03-22
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: 14000 Devices Were Hijacked To Create An Unprecedented Cyberattack
1. BLUF (Bottom Line Up Front)
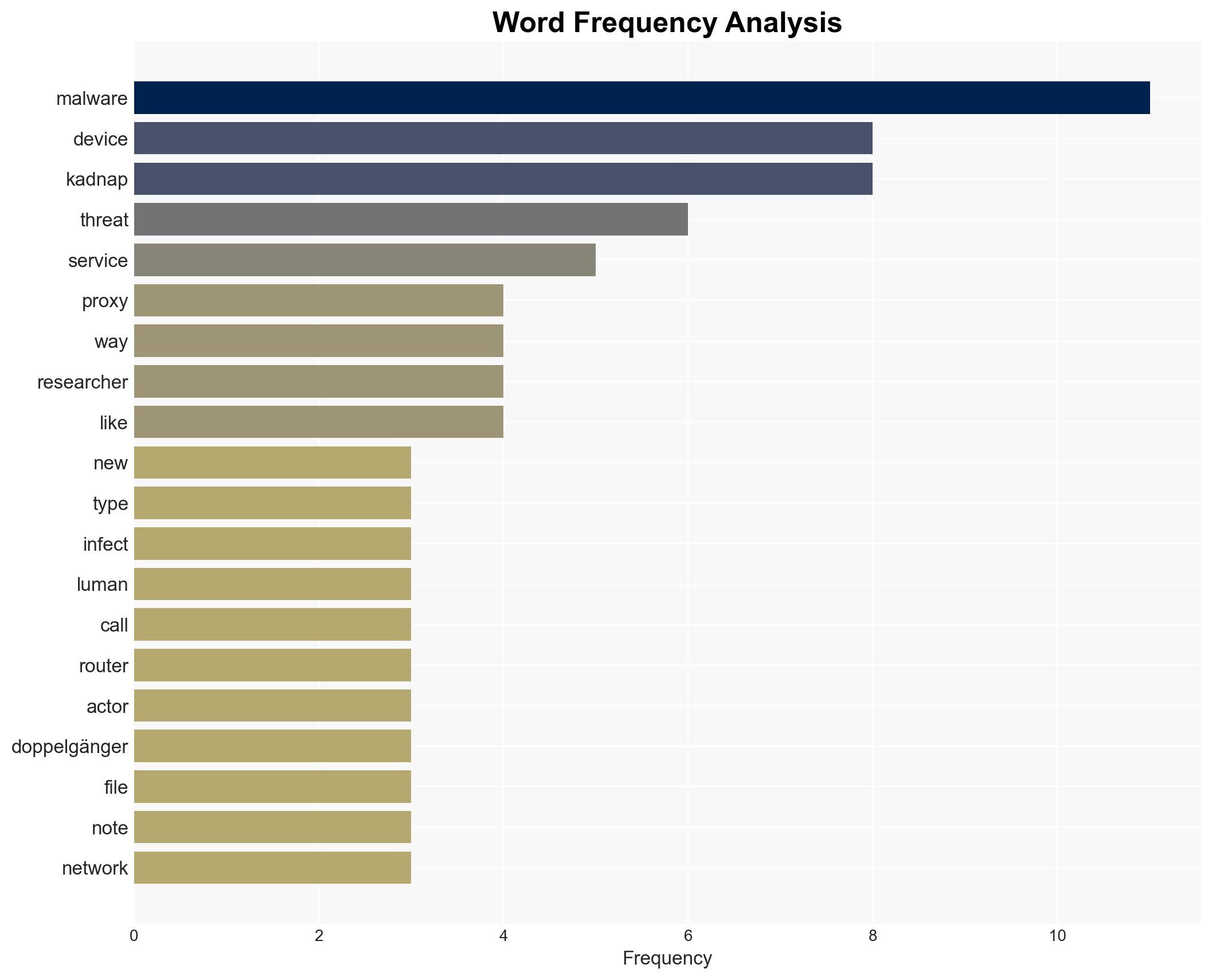
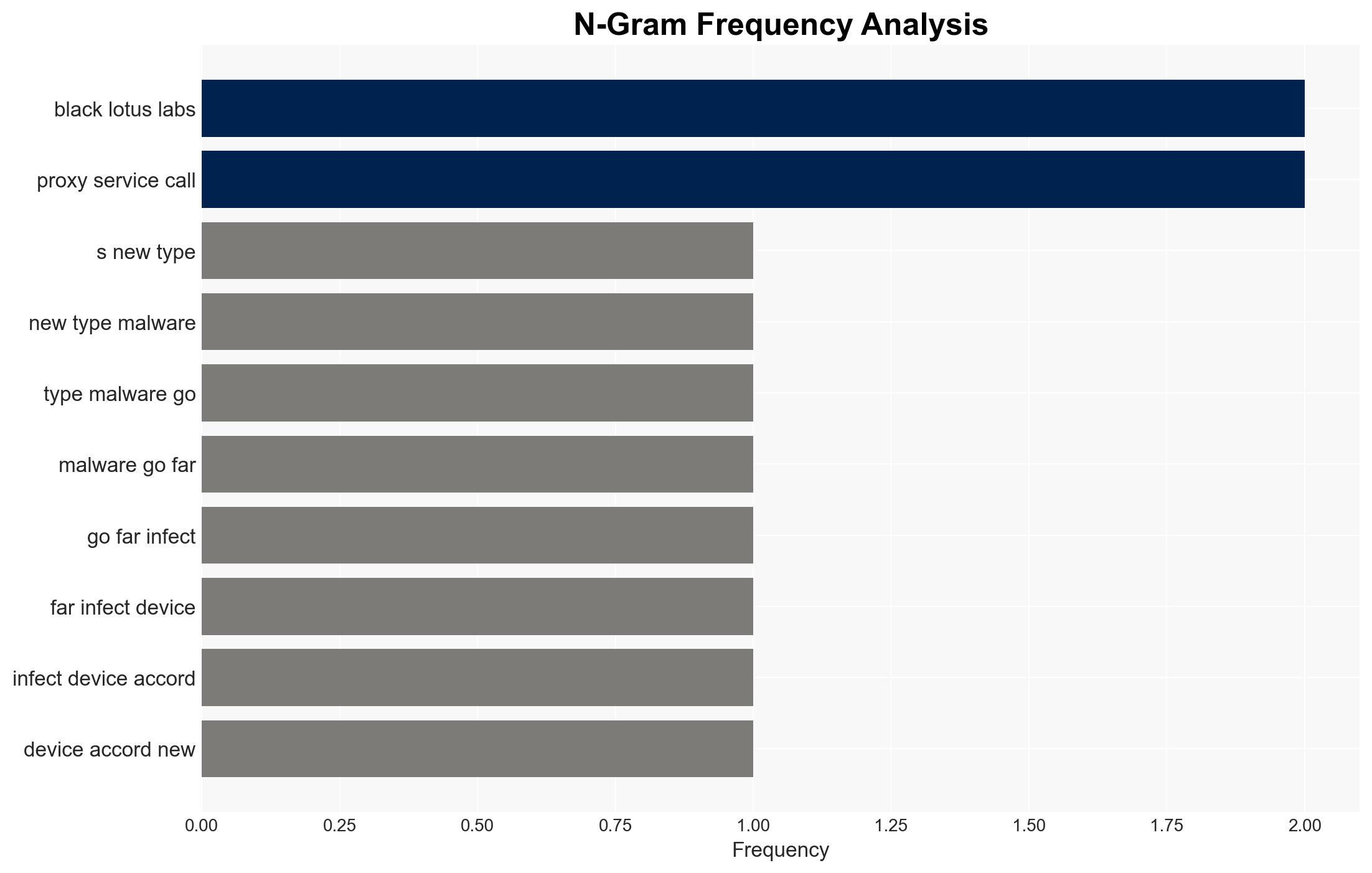
The KadNap malware has compromised over 14,000 devices, primarily targeting Asus routers, with significant impact in the United States. This malware facilitates anonymous DDoS attacks via a proxy service called Doppelgänger, posing a growing threat as IoT adoption increases. Moderate confidence is placed in the assessment that the malware’s primary goal is to expand its botnet for cybercriminal activities.
2. Competing Hypotheses
- Hypothesis A: KadNap is primarily designed to expand a botnet for conducting large-scale DDoS attacks. This is supported by the malware’s integration into the Doppelgänger proxy service and its targeting of edge devices like routers, which are ideal for such operations. However, the exact scale and coordination of these attacks remain uncertain.
- Hypothesis B: KadNap is a tool for broader cyber-espionage activities, using DDoS attacks as a cover. While the malware’s capabilities could support espionage, there is limited direct evidence linking it to such operations, and its current use aligns more with DDoS facilitation.
- Assessment: Hypothesis A is currently better supported due to the malware’s design and deployment patterns. Indicators such as increased targeting of IoT devices or shifts in attack patterns could suggest a pivot towards espionage.
3. Key Assumptions and Red Flags
- Assumptions: The malware’s primary function is to facilitate DDoS attacks; the infection vector is predominantly through Asus routers; the threat actors aim to remain undetected.
- Information Gaps: Specific identities of the threat actors; detailed technical analysis of the malware’s full capabilities; comprehensive geographic distribution of infected devices.
- Bias & Deception Risks: Potential bias in focusing on Asus routers due to initial detection; deception risk from threat actors using false flags to mislead attribution efforts.
4. Implications and Strategic Risks
The proliferation of KadNap could lead to increased cyber instability, particularly affecting nations with high IoT adoption. The malware’s evolution may influence global cybersecurity policies and practices.
- Political / Geopolitical: Potential for increased tensions between affected nations, particularly if state-sponsored activity is suspected.
- Security / Counter-Terrorism: Enhanced threat landscape requiring updated defense measures and international cooperation.
- Cyber / Information Space: Escalation in cyber-attacks, necessitating improved detection and response capabilities.
- Economic / Social: Potential economic disruptions from DDoS attacks on critical infrastructure; increased public concern over IoT security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of Asus routers and similar edge devices; disseminate threat intelligence to relevant stakeholders; enhance public awareness on IoT security practices.
- Medium-Term Posture (1–12 months): Develop partnerships for information sharing; invest in research for advanced malware detection; strengthen cybersecurity frameworks and regulations.
- Scenario Outlook:
- Best: Rapid containment and neutralization of KadNap, leading to improved IoT security practices.
- Worst: Expansion of the botnet leading to widespread DDoS attacks on critical infrastructure.
- Most-Likely: Continued use of KadNap for DDoS attacks with gradual improvements in detection and mitigation strategies.
6. Key Individuals and Entities
- Black Lotus Labs (Lumen)
- Asus (Device Manufacturer)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
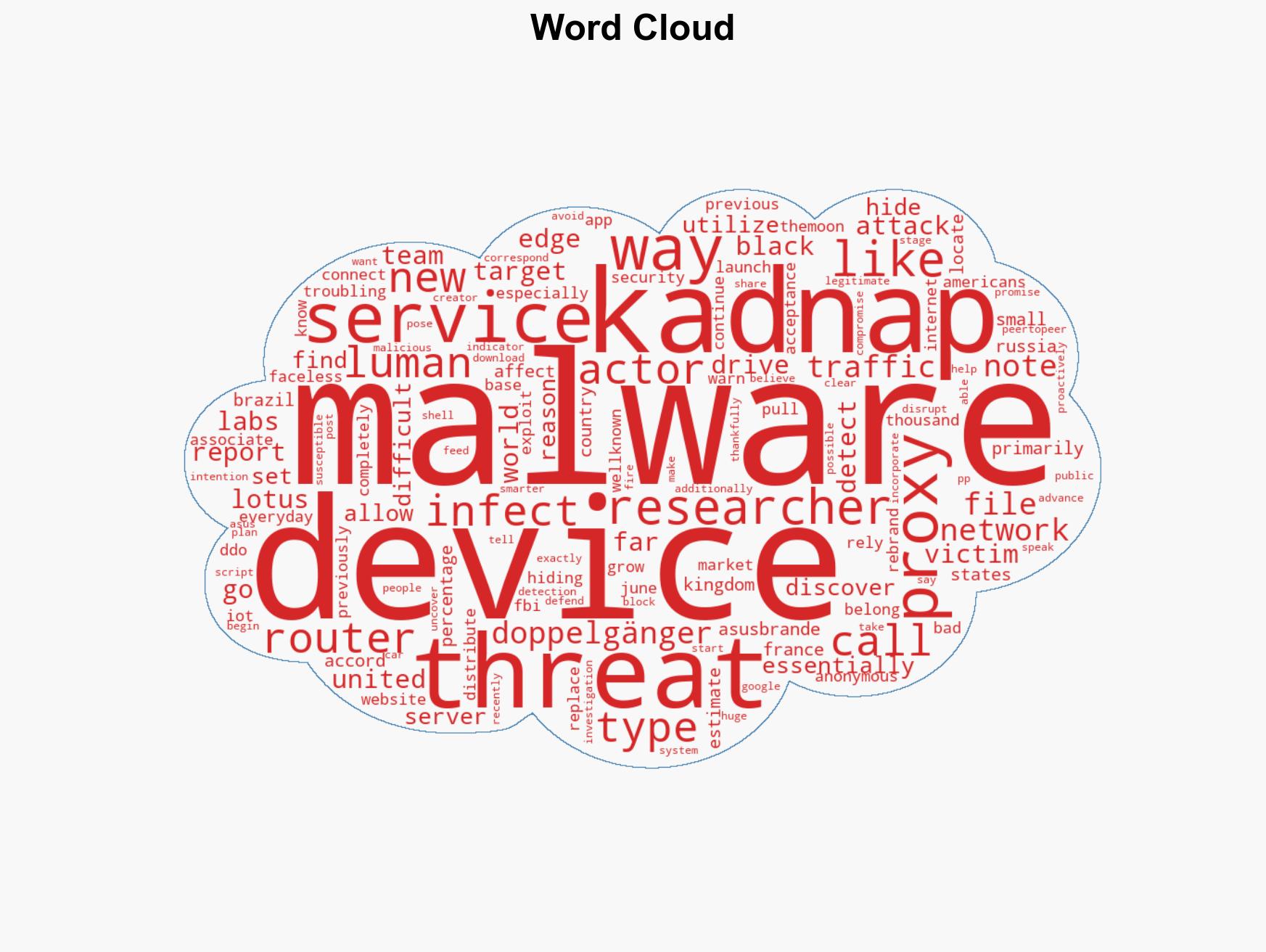
cybersecurity, malware, DDoS attacks, IoT security, cybercrime, network security, threat intelligence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us