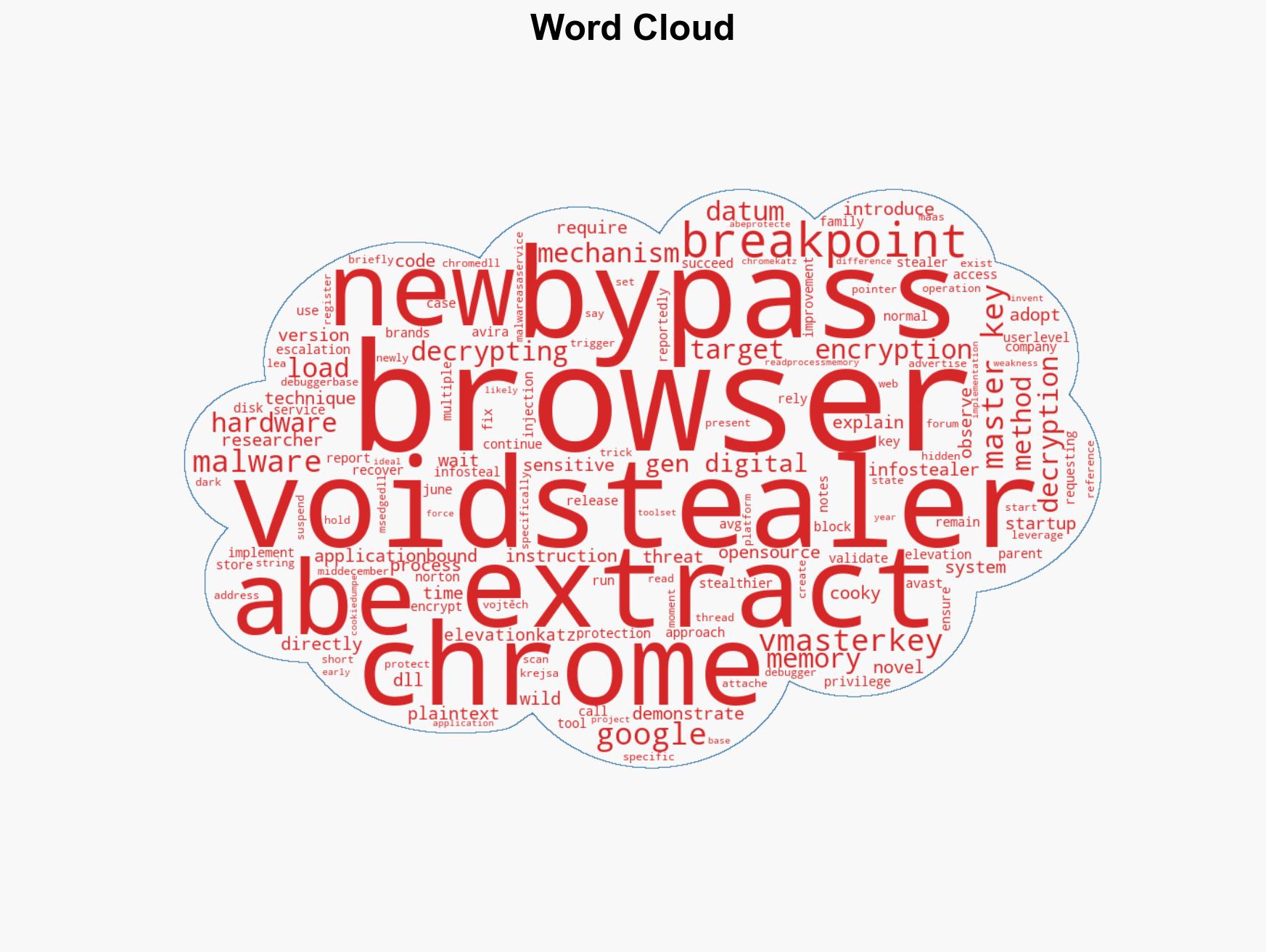
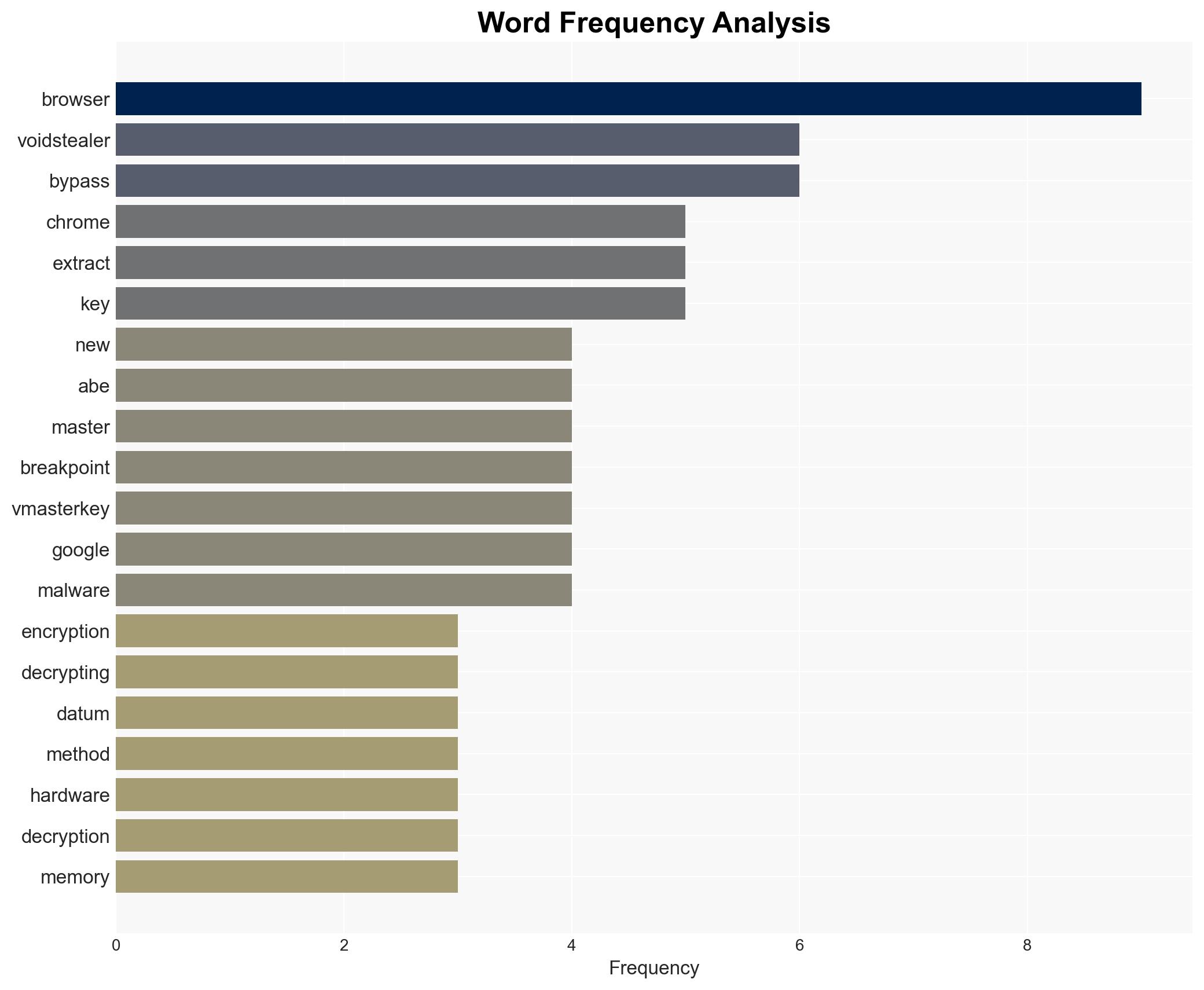
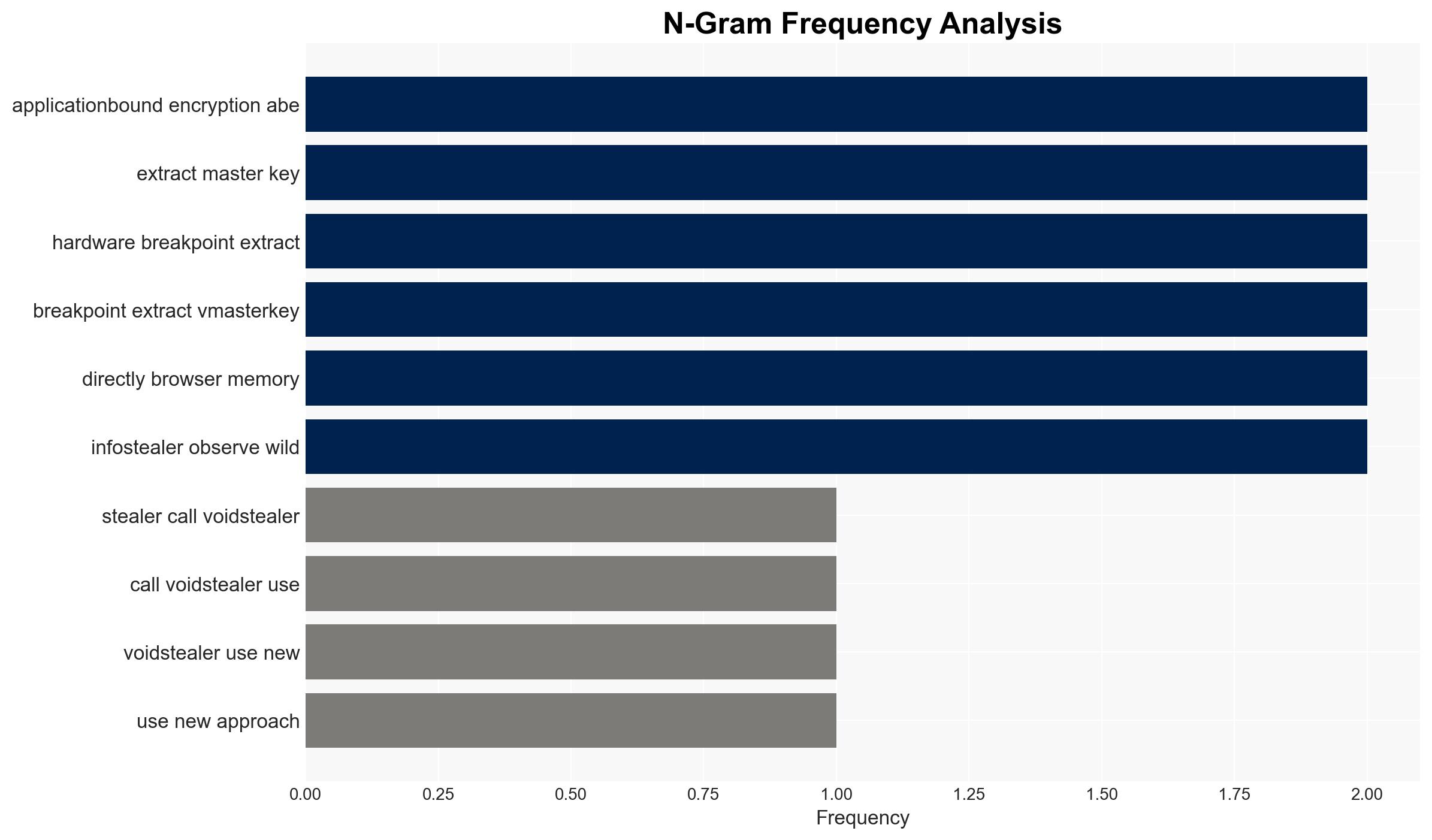
VoidStealer malware circumvents Chrome’s encryption to extract master key using hardware breakpoints
Published on: 2026-03-22
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: VoidStealer malware steals Chrome master key via debugger trick
1. BLUF (Bottom Line Up Front)
VoidStealer, a malware-as-a-service platform, employs a novel technique to bypass Chrome’s Application-Bound Encryption, extracting the master key without privilege escalation. This development poses a significant threat to data security for Chrome users globally. The most likely hypothesis is that this method will proliferate among cybercriminals, increasing the risk of data breaches. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: VoidStealer’s technique will become widely adopted by other malware, leading to a surge in data breaches. This is supported by the novelty and effectiveness of the method, but contradicted by potential countermeasures from Google.
- Hypothesis B: Google will rapidly develop and deploy effective countermeasures, limiting the spread and impact of this technique. This is supported by Google’s history of addressing security vulnerabilities, but contradicted by the persistent success of similar bypasses.
- Assessment: Hypothesis A is currently better supported due to the novelty and stealth of the technique, which may outpace Google’s response. Key indicators that could shift this judgment include announcements of new security updates from Google or reports of widespread adoption of the technique by other malware.
3. Key Assumptions and Red Flags
- Assumptions: The technique will not be immediately countered by Google; cybercriminals will quickly adopt the method; the method’s effectiveness is as reported.
- Information Gaps: Details on Google’s planned countermeasures and the speed of adoption among other malware families.
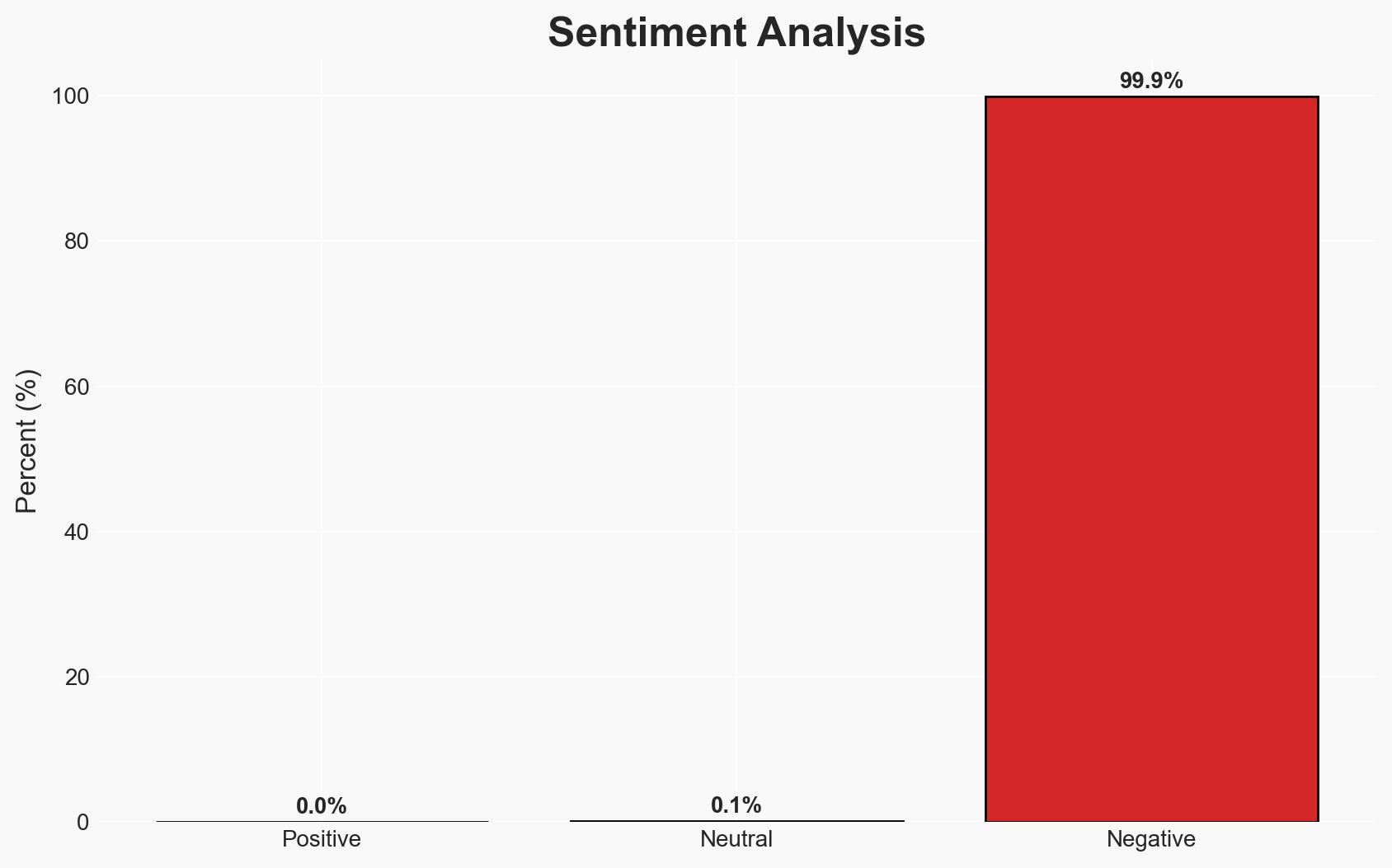
- Bias & Deception Risks: Potential bias in reporting from Gen Digital, as they may have vested interests in highlighting threats; deception risk from cybercriminals exaggerating the technique’s effectiveness.
4. Implications and Strategic Risks
This development could lead to increased cyber threats and data breaches, affecting user trust and security. The technique’s proliferation could challenge existing cybersecurity frameworks and necessitate rapid response measures.
- Political / Geopolitical: Increased tension between tech companies and state actors over cybersecurity responsibilities.
- Security / Counter-Terrorism: Enhanced capabilities for cybercriminals could indirectly support terrorist financing through stolen data.
- Cyber / Information Space: Potential for widespread data breaches and increased demand for cybersecurity solutions.
- Economic / Social: Potential economic impact on businesses reliant on Chrome for secure transactions; erosion of public trust in digital security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor dark web forums for discussions on the technique; collaborate with Google to understand and mitigate the threat.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms to enhance detection capabilities; invest in research for new encryption technologies.
- Scenario Outlook: Best: Google deploys effective countermeasures, limiting impact. Worst: Widespread adoption leads to significant data breaches. Most-Likely: Gradual increase in breaches until effective countermeasures are developed.
6. Key Individuals and Entities
- Vojtěch Krejsa, threat researcher at Gen Digital
- Gen Digital, parent company behind Norton, Avast, AVG, and Avira
- Google, developer of Chrome
- VoidStealer, malware-as-a-service platform
7. Thematic Tags
cybersecurity, malware, data breaches, encryption, cybercrime, information security, digital trust
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us