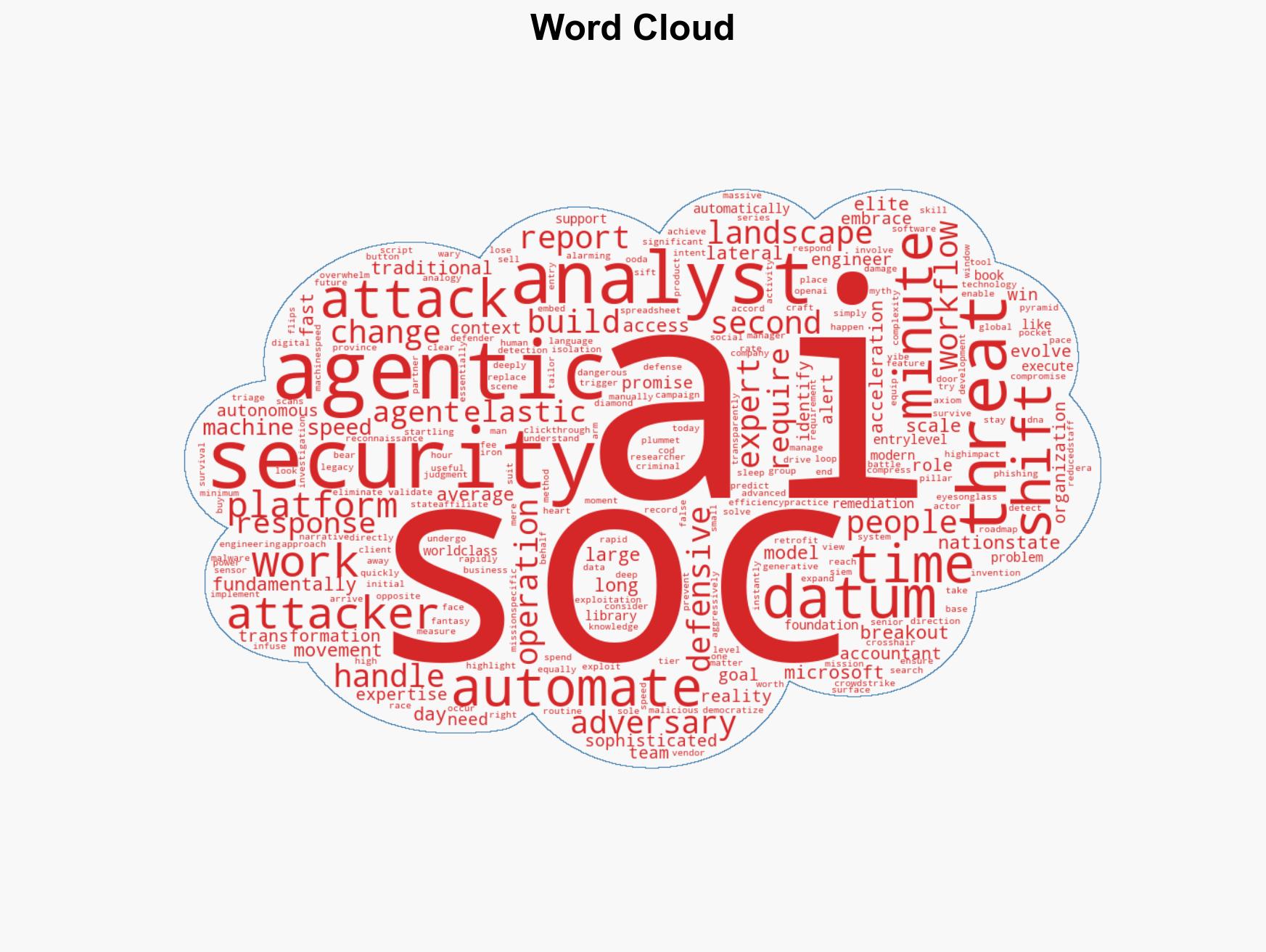
Evolving Cybersecurity: The Urgent Need for SOCs Amid Rapid AI-Driven Threats
Published on: 2026-03-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: The AI arms race in cybersecurity Why your SOC needs to evolve now
1. BLUF (Bottom Line Up Front)
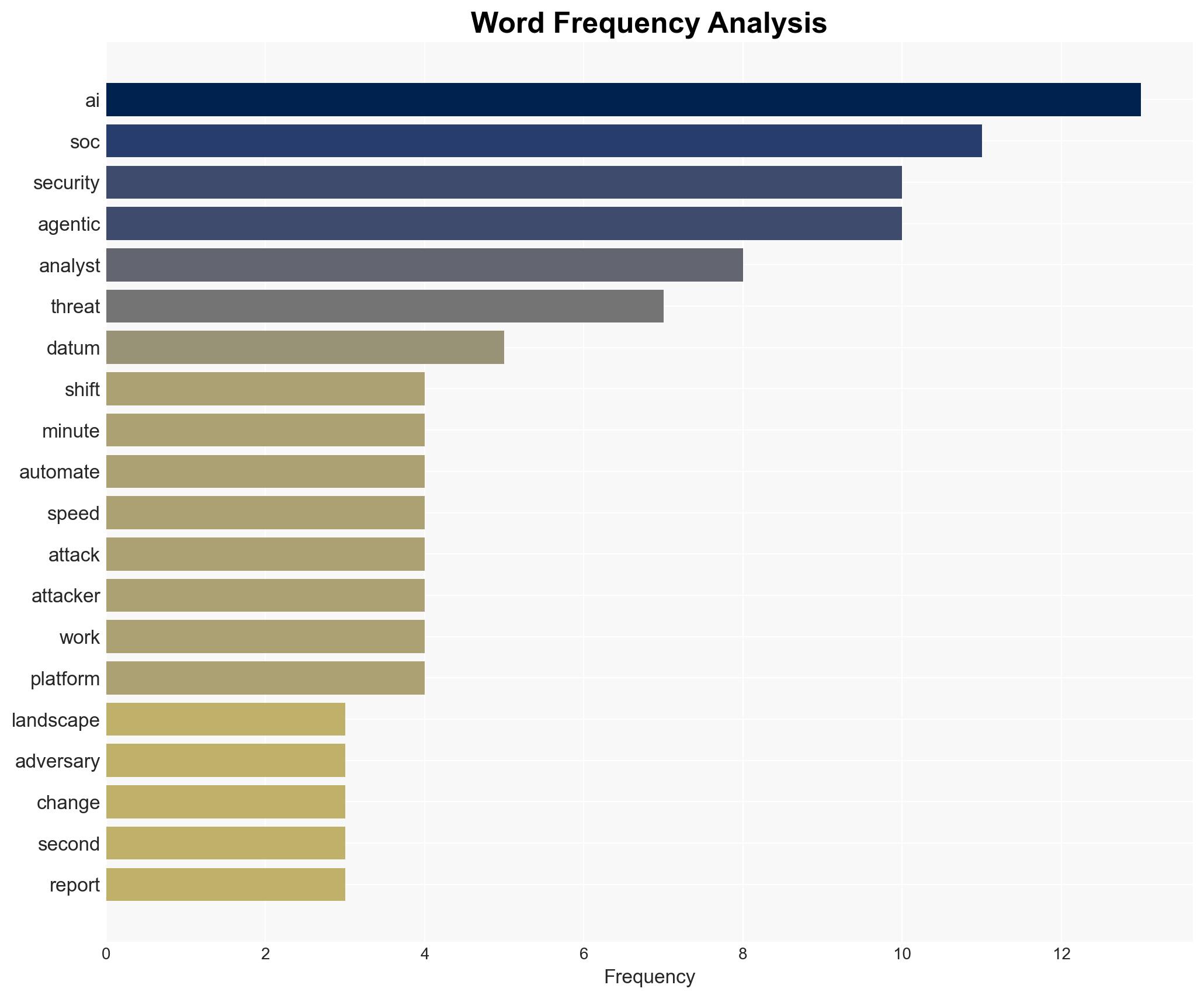
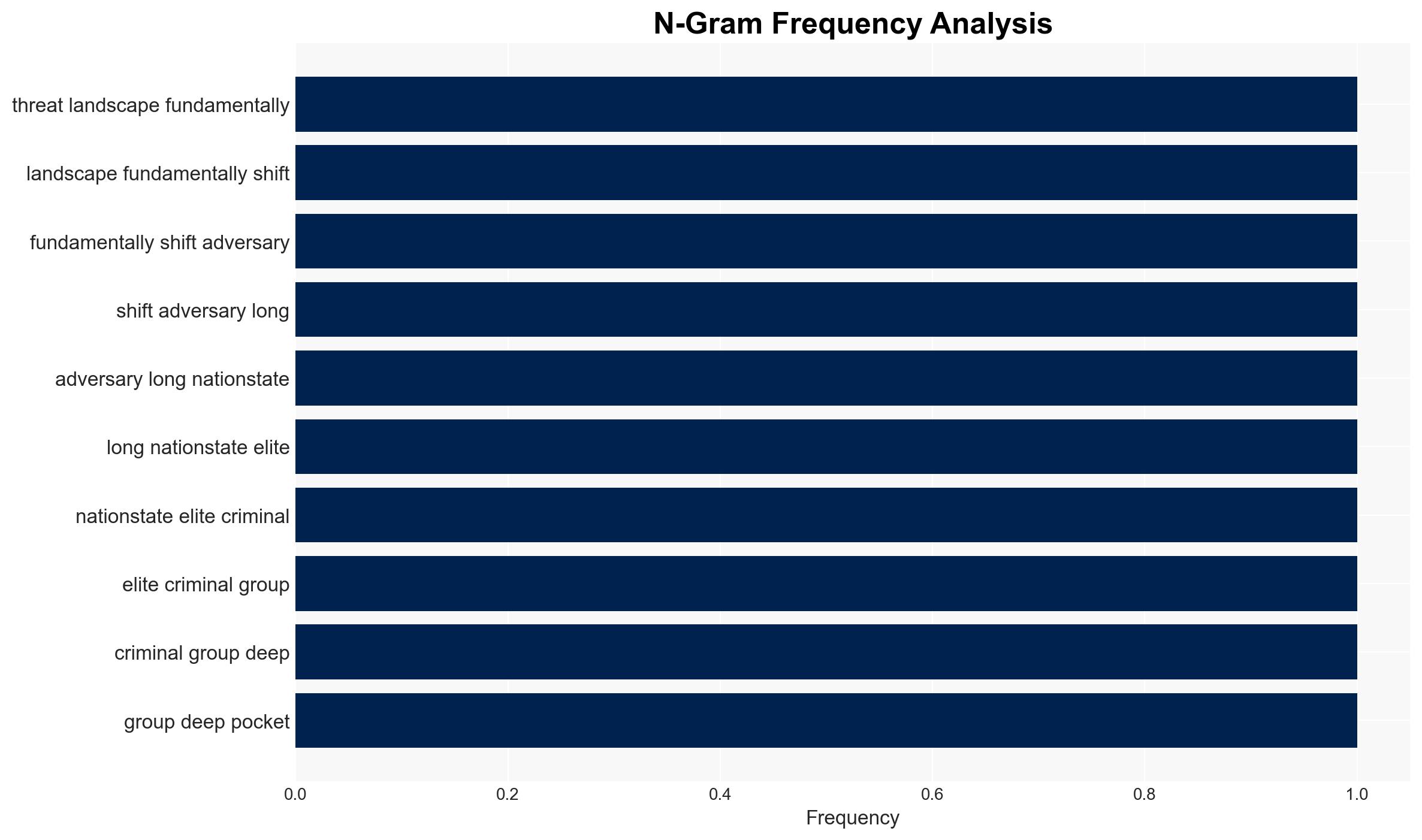
The cybersecurity landscape is rapidly evolving due to the democratization of AI, which is now accessible to a wider range of adversaries beyond nation-states and elite criminal groups. This shift necessitates an evolution in Security Operations Centers (SOCs) to integrate AI tools effectively. The most likely hypothesis is that AI will augment rather than replace SOC analysts, requiring a transformation in their roles. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: AI will replace SOC analysts, leading to reduced staffing needs. This is supported by narratives promoting autonomous SOCs. However, evidence suggests that AI is not a “win button” and requires human expertise for effective deployment. Key uncertainties include the pace of AI development and integration into defensive strategies.
- Hypothesis B: AI will augment SOC analysts, transforming their roles rather than replacing them. This is supported by the analogy of accountants adapting to spreadsheet software and the need for business context and security expertise. The rapid pace of AI adoption by adversaries further supports this hypothesis.
- Assessment: Hypothesis B is currently better supported due to the need for human expertise in interpreting AI-generated data and the limitations of AI in understanding complex security contexts. Indicators that could shift this judgment include breakthroughs in AI autonomy or significant changes in adversary tactics.
3. Key Assumptions and Red Flags
- Assumptions: AI technology will continue to advance rapidly; SOC analysts can effectively integrate AI tools; adversaries will increasingly use AI in attacks; AI will not achieve full autonomy in the near term.
- Information Gaps: Detailed data on AI adoption rates among different adversary groups; effectiveness metrics of AI-augmented SOCs; long-term impacts of AI on SOC staffing and operations.
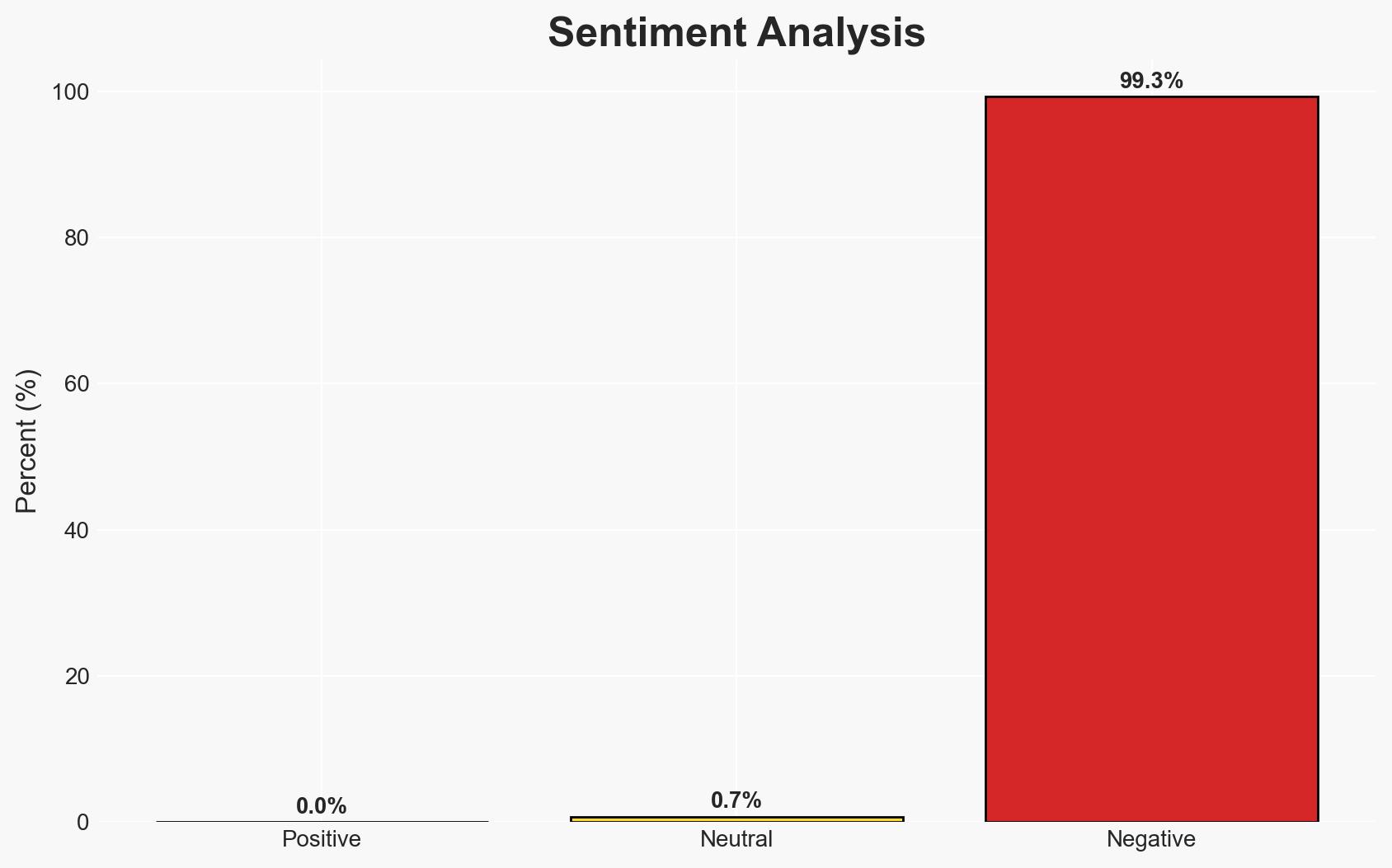
- Bias & Deception Risks: Potential overreliance on AI-generated data; source bias from technology vendors promoting AI solutions; adversaries using misinformation to exaggerate AI capabilities.
4. Implications and Strategic Risks
The integration of AI into cybersecurity operations could significantly alter threat dynamics and defensive strategies. Over time, this may lead to increased sophistication in both attacks and defenses, impacting various domains.
- Political / Geopolitical: Potential escalation in cyber warfare capabilities among state and non-state actors.
- Security / Counter-Terrorism: Increased threat from non-traditional actors leveraging AI for cyber-attacks.
- Cyber / Information Space: Enhanced capabilities for both offensive and defensive cyber operations; potential for misinformation campaigns using AI.
- Economic / Social: Potential economic impacts from increased cyber threats; societal reliance on AI for security could lead to vulnerabilities.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive review of current SOC capabilities; initiate AI training programs for analysts; enhance monitoring of AI-related threat intelligence.
- Medium-Term Posture (1–12 months): Develop partnerships with AI technology providers; invest in AI research and development; implement AI-driven threat detection and response systems.
- Scenario Outlook:
- Best: Effective integration of AI leads to enhanced security and reduced threat impact.
- Worst: Overreliance on AI results in vulnerabilities and increased successful attacks.
- Most-Likely: Gradual augmentation of SOC capabilities with AI, leading to a balanced approach in threat management.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, AI integration, SOC evolution, threat landscape, cyber defense, AI augmentation, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us