Smart Home Vulnerabilities Persist Despite New Australian Security Standards; Vigilance Required
Published on: 2026-03-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Your smart home can be easily hacked New safety standards will help but stay vigilant
1. BLUF (Bottom Line Up Front)
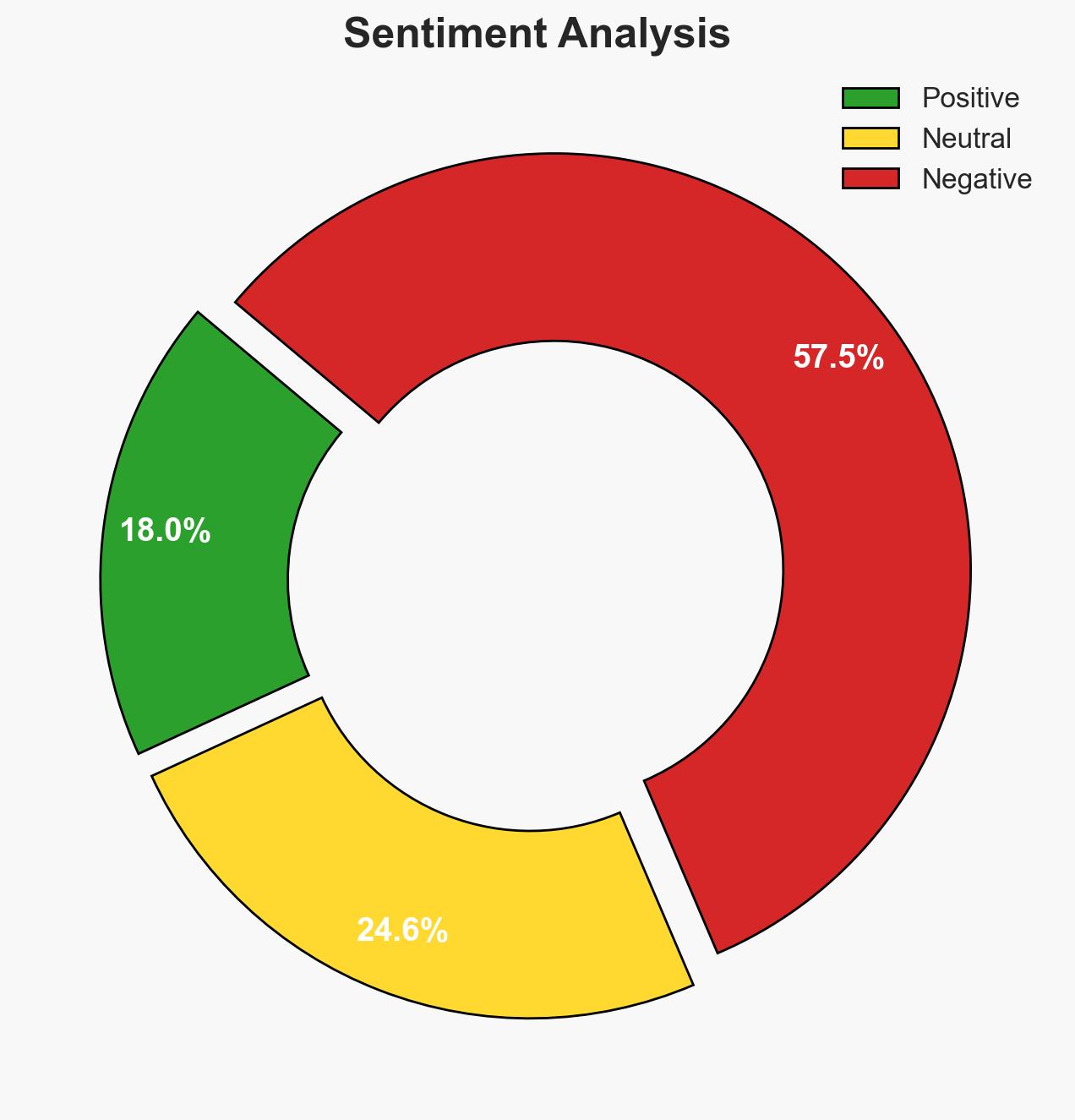
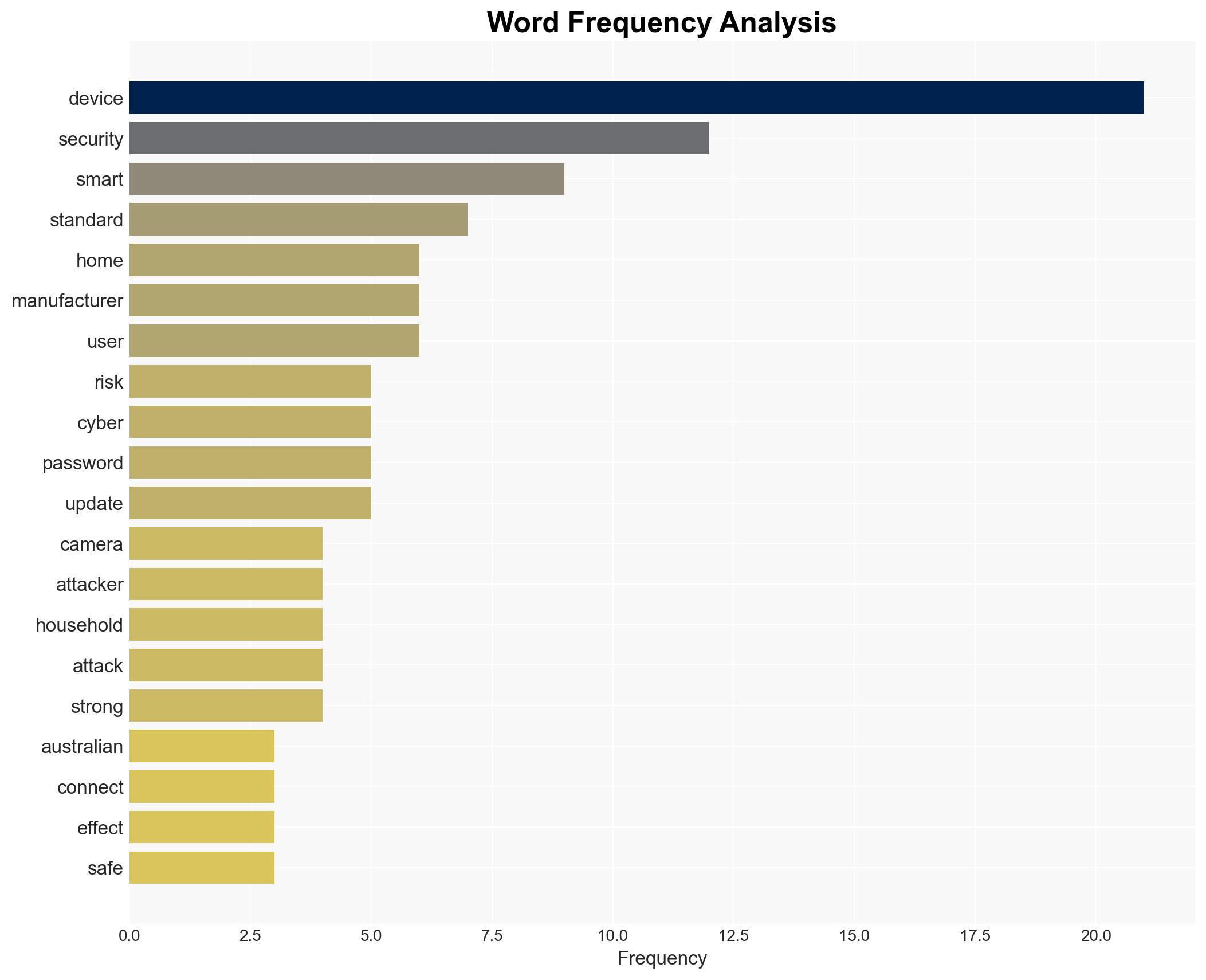
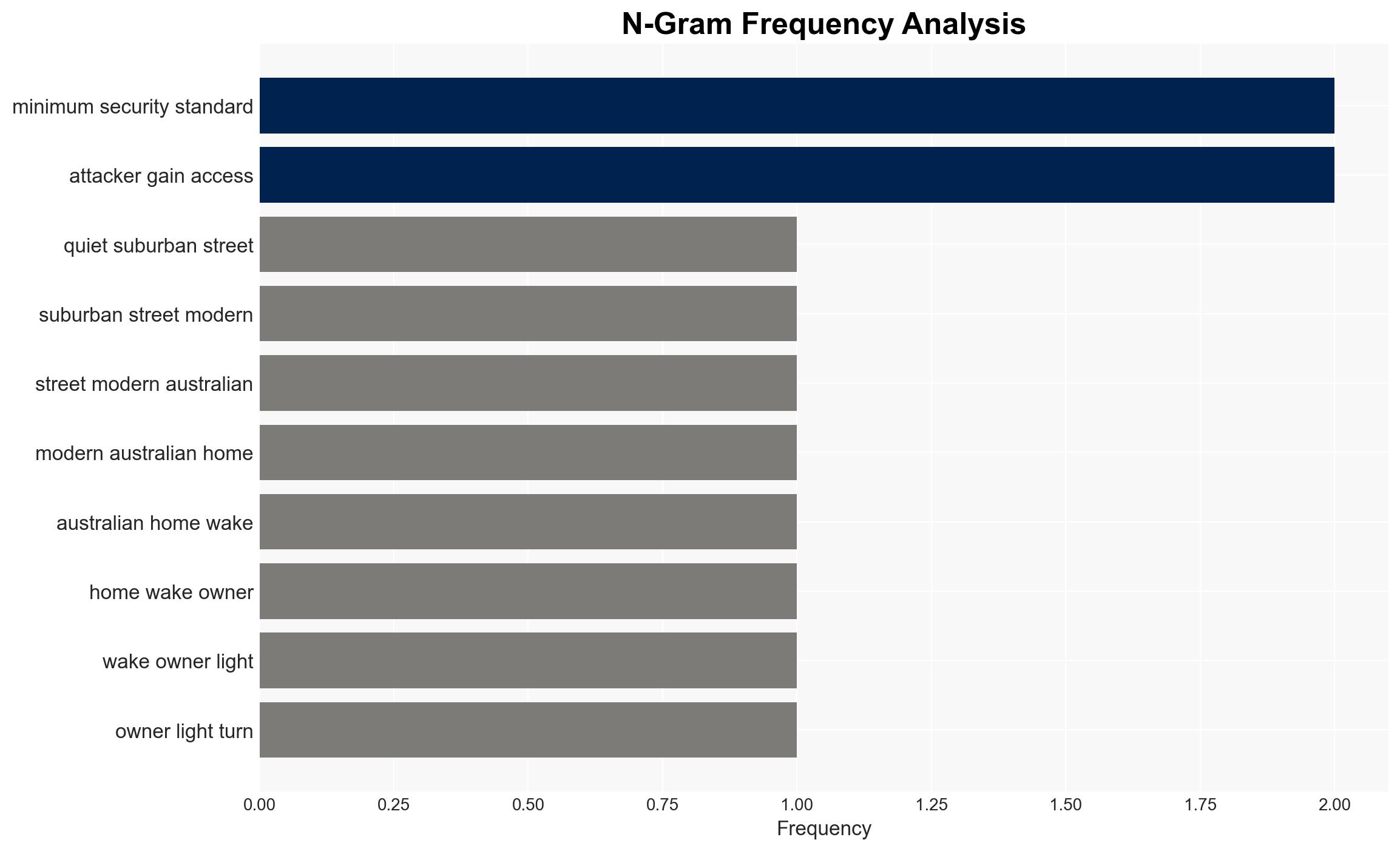
The introduction of minimum security standards for smart devices in Australia aims to mitigate cyber vulnerabilities inherent in smart home technology. However, these measures may not fully address the risks due to manufacturers’ historical neglect of security. The effectiveness of these standards is uncertain, with moderate confidence in their potential to enhance security. The primary affected parties are consumers and manufacturers of smart home devices.
2. Competing Hypotheses
- Hypothesis A: The new security standards will significantly reduce the vulnerability of smart home devices to cyber attacks. This is supported by the government’s proactive stance and the mandatory nature of the standards. However, the lack of details on enforcement and compliance mechanisms introduces uncertainty.
- Hypothesis B: The new standards will have limited impact due to manufacturers’ focus on cost and speed over security, and the persistence of legacy devices without updates. This hypothesis is supported by historical trends and the ongoing existence of weak default security measures.
- Assessment: Hypothesis B is currently better supported due to the entrenched practices of manufacturers and the slow pace of change in consumer behavior regarding device security. Key indicators that could shift this judgment include evidence of widespread compliance with the new standards and a reduction in reported cyber incidents involving smart devices.
3. Key Assumptions and Red Flags
- Assumptions: Manufacturers will comply with the new standards; consumers will adopt better security practices; the standards are comprehensive and enforceable.
- Information Gaps: Specific details on the enforcement mechanisms for the standards and data on compliance rates among manufacturers.
- Bias & Deception Risks: Potential bias in underestimating manufacturers’ willingness to improve security; risk of deceptive compliance reporting by manufacturers.
4. Implications and Strategic Risks
The introduction of security standards could lead to a gradual improvement in the security of smart home devices, but significant risks remain if compliance is not effectively monitored and enforced.
- Political / Geopolitical: Limited direct implications, but potential for increased regulatory scrutiny on tech companies.
- Security / Counter-Terrorism: Enhanced device security could reduce the risk of devices being used in botnet attacks, impacting national security positively.
- Cyber / Information Space: Potential reduction in cyber attack vectors, but attackers may shift focus to other vulnerabilities.
- Economic / Social: Improved consumer confidence in smart home technology could drive market growth, but failure to secure devices could lead to economic losses and privacy concerns.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor compliance with new standards; engage with manufacturers to ensure understanding and implementation of security measures.
- Medium-Term Posture (1–12 months): Develop partnerships with industry stakeholders to promote best practices; invest in consumer education on device security.
- Scenario Outlook:
- Best: High compliance with standards leads to a marked decrease in smart device vulnerabilities.
- Worst: Non-compliance and lack of enforcement result in continued cyber threats and consumer distrust.
- Most-Likely: Gradual improvement in security with ongoing challenges in legacy device vulnerabilities.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
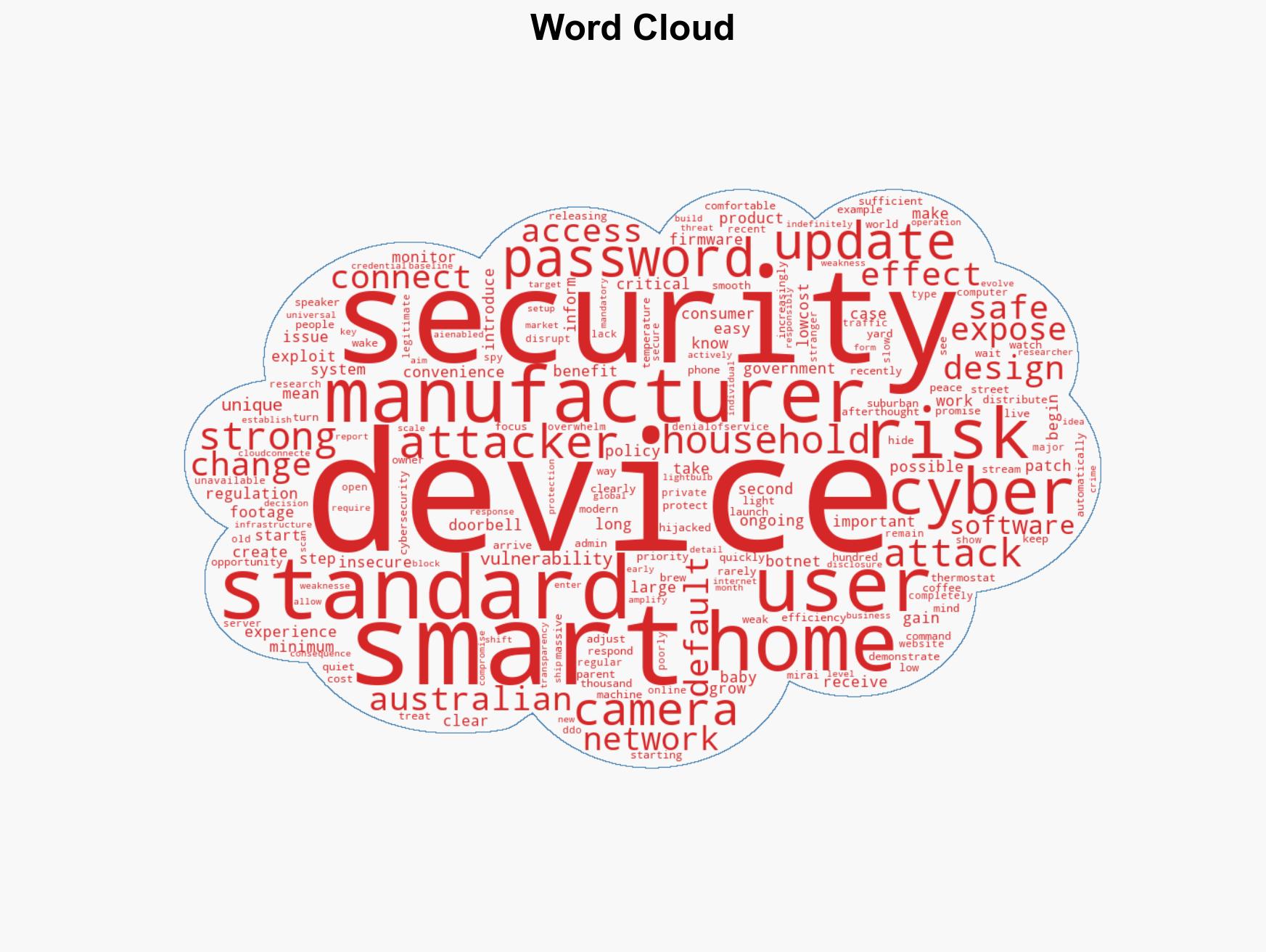
cybersecurity, smart home technology, regulatory standards, consumer protection, cyber threats, device compliance, IoT security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us