CISA directs federal agencies to address iOS vulnerabilities exploited by DarkSword in cyberattacks
Published on: 2026-03-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: CISA orders feds to patch DarkSword iOS flaws exploited attacks
1. BLUF (Bottom Line Up Front)
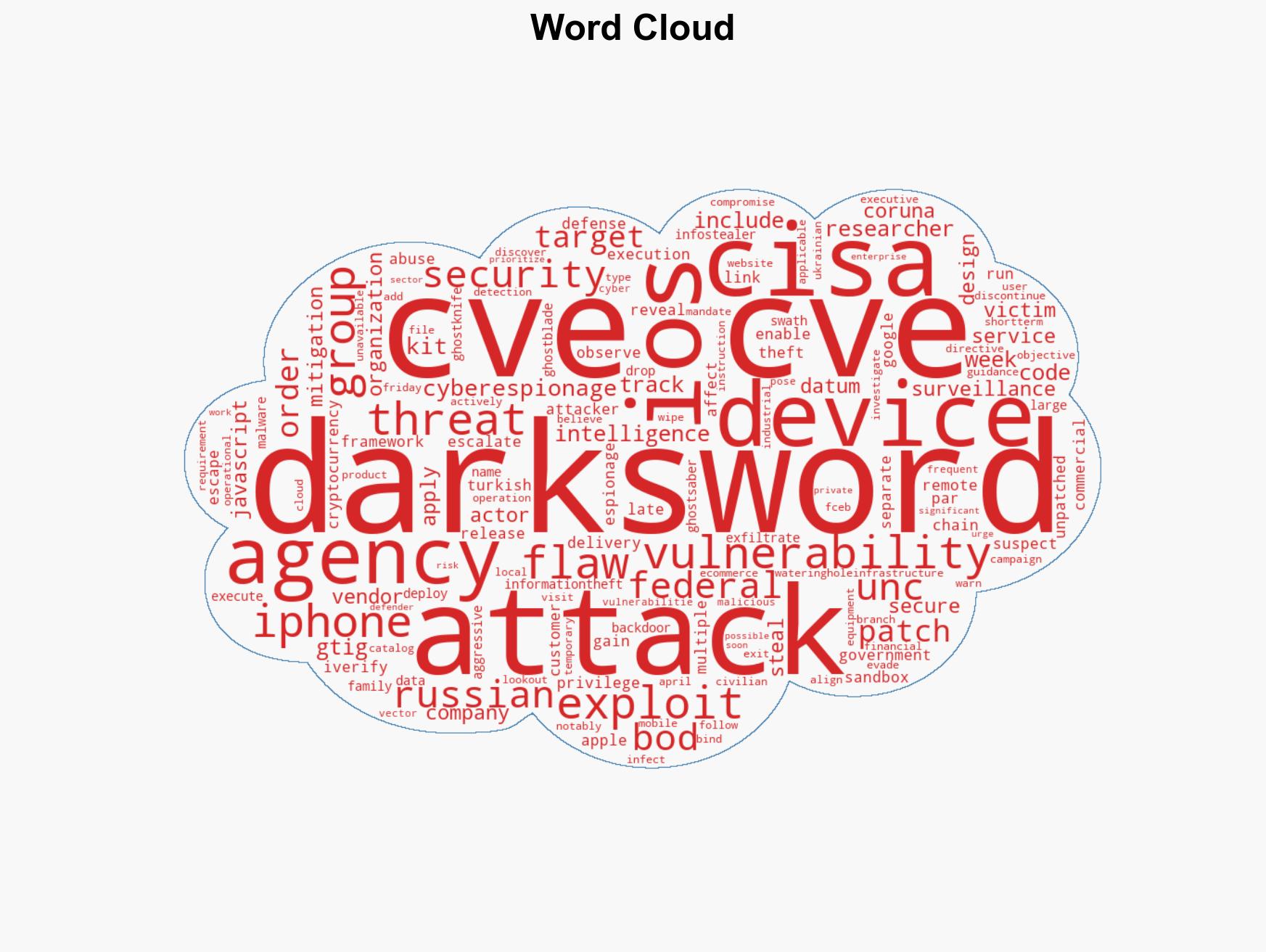
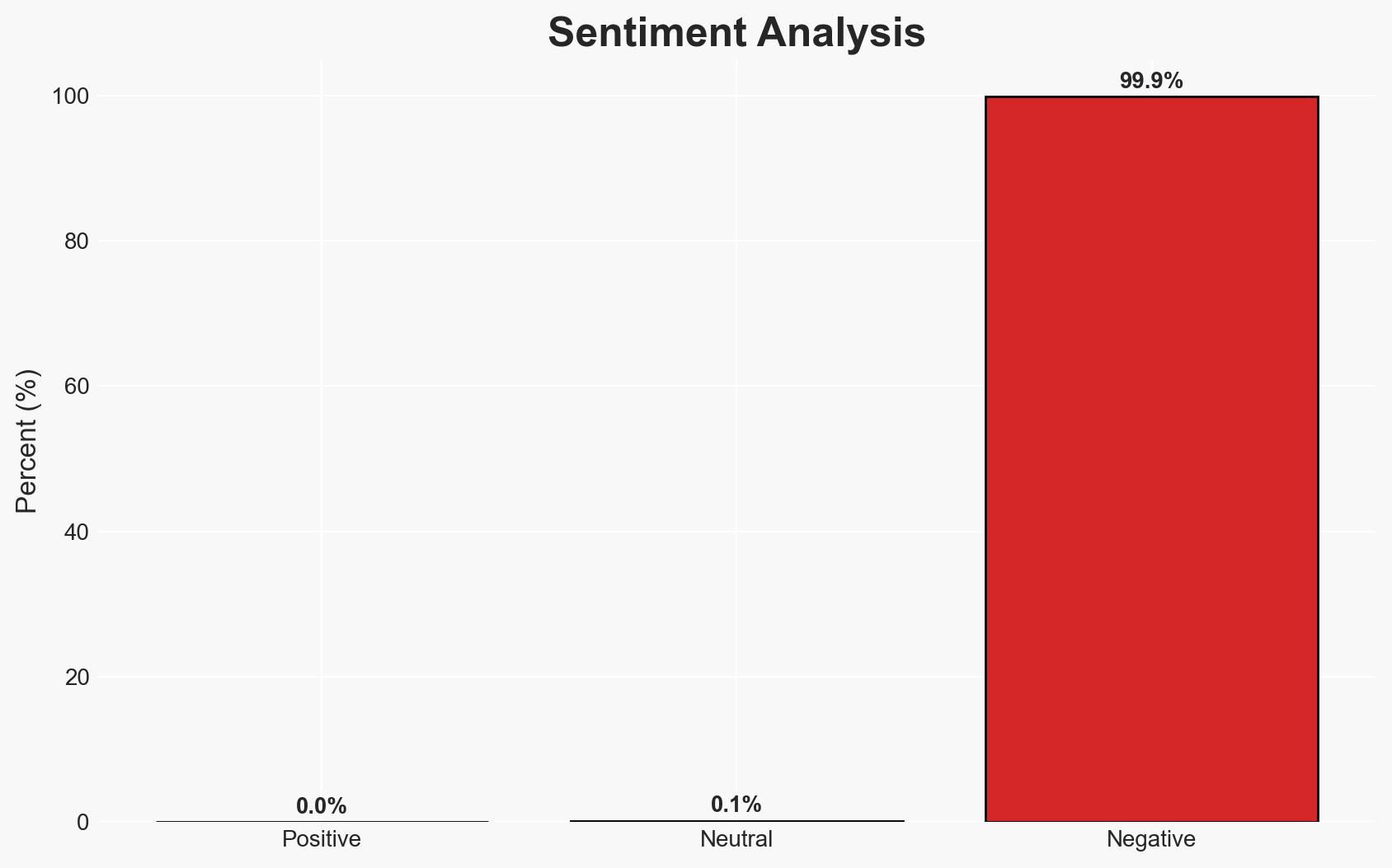
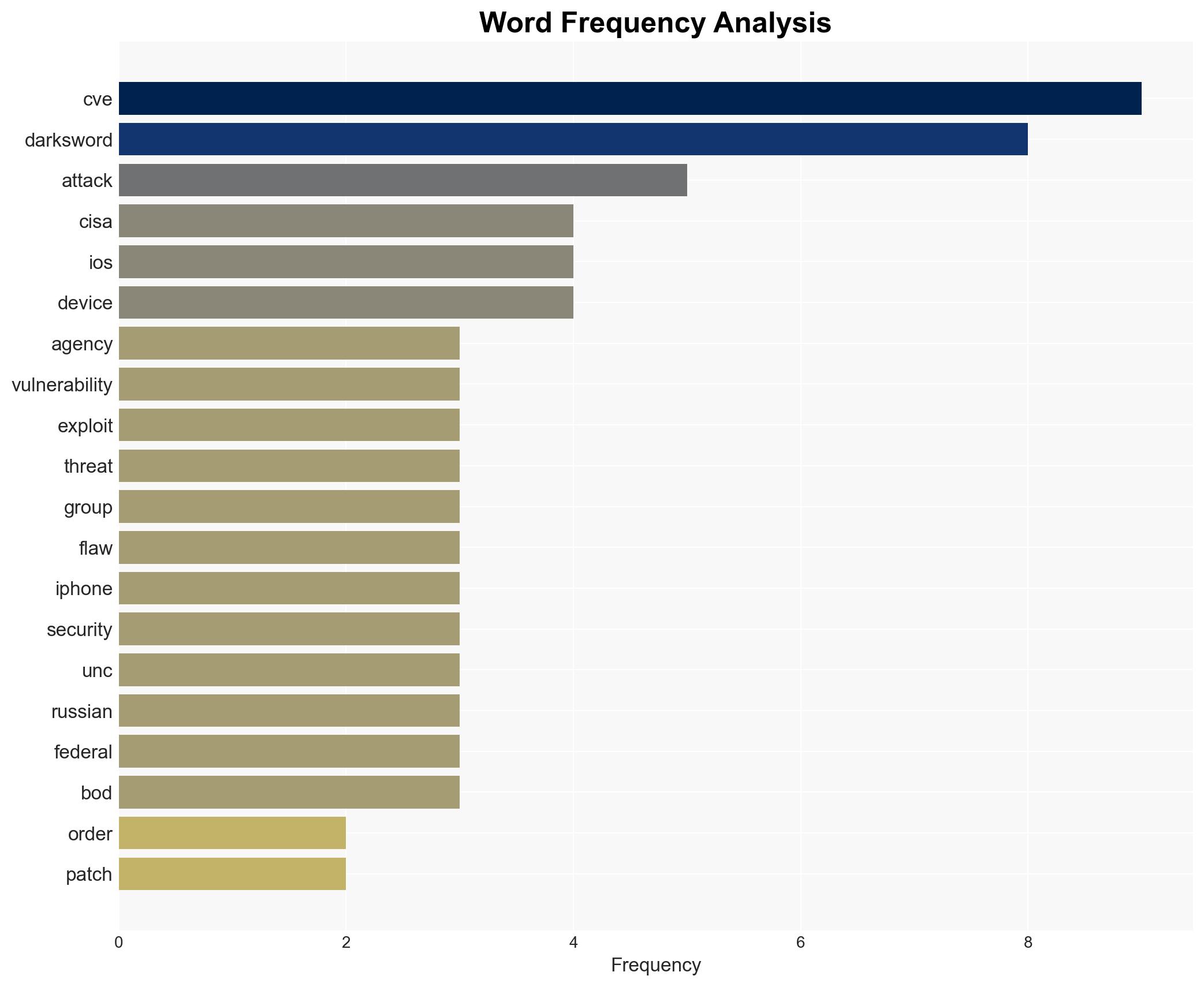
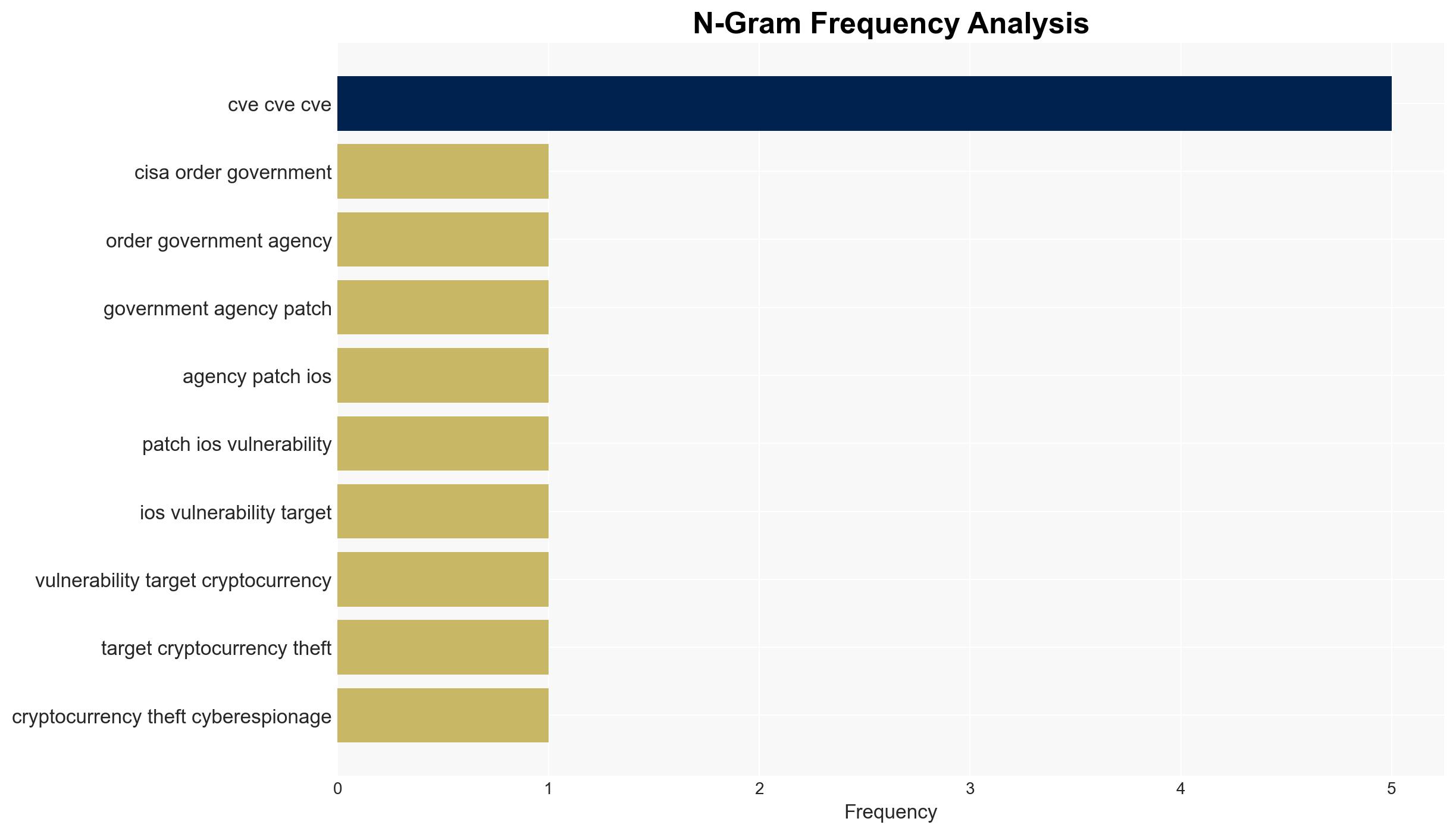
The Cybersecurity and Infrastructure Security Agency (CISA) has mandated U.S. federal agencies to patch critical iOS vulnerabilities exploited by the DarkSword exploit kit, linked to cyberespionage and cryptocurrency theft. This directive aims to mitigate significant risks posed by these vulnerabilities to federal systems. The most likely hypothesis is that these vulnerabilities are being actively exploited by state-sponsored actors, particularly Russian entities, for espionage purposes. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The DarkSword exploit kit is primarily used by Russian state-sponsored actors for cyberespionage targeting U.S. interests. Supporting evidence includes the linkage to a suspected Russian espionage group and alignment with Russian intelligence requirements. However, the exact scope and scale of operations remain uncertain.
- Hypothesis B: The DarkSword exploit kit is being used by multiple threat actors, including non-state actors, for financial gain through cryptocurrency theft. This hypothesis is supported by the involvement of a Turkish commercial surveillance vendor and the financial objectives of some actors. Contradicting evidence includes the sophisticated nature of the attacks, which suggests state-level involvement.
- Assessment: Hypothesis A is currently better supported due to the strategic alignment with Russian intelligence objectives and the complexity of the attacks, which are indicative of state-sponsored capabilities. Indicators such as increased targeting of geopolitical adversaries could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The vulnerabilities are primarily exploited by state-sponsored actors; the patches will effectively mitigate the threat; federal agencies will comply with CISA’s directive in a timely manner.
- Information Gaps: Detailed attribution of the threat actors involved; the full extent of compromised devices; the effectiveness of the patches in real-world scenarios.
- Bias & Deception Risks: Potential bias in attributing attacks to state actors without conclusive evidence; reliance on open-source intelligence that may be incomplete or manipulated.
4. Implications and Strategic Risks
This development could lead to heightened tensions between the U.S. and Russia, particularly if further evidence of state-sponsored involvement emerges. It may also prompt increased cybersecurity measures across both public and private sectors.
- Political / Geopolitical: Potential diplomatic confrontations or sanctions against Russia if state-sponsored involvement is confirmed.
- Security / Counter-Terrorism: Enhanced threat environment for federal agencies, necessitating improved cybersecurity protocols.
- Cyber / Information Space: Increased focus on securing mobile devices and mitigating vulnerabilities in widely used operating systems.
- Economic / Social: Potential economic impacts from disrupted operations or data breaches, particularly in sectors reliant on mobile technology.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Ensure all federal agencies apply the necessary patches; increase monitoring for signs of exploitation; engage with international partners to share threat intelligence.
- Medium-Term Posture (1–12 months): Develop resilience measures, including regular updates and training; strengthen partnerships with private sector cybersecurity firms.
- Scenario Outlook:
- Best Case: Successful patching mitigates the threat with minimal disruption.
- Worst Case: Continued exploitation leads to significant data breaches and geopolitical tensions.
- Most-Likely: Partial mitigation with ongoing low-level exploitation and increased cybersecurity awareness.
6. Key Individuals and Entities
- UNC6748 – Linked to Turkish commercial surveillance vendor PARS Defense
- UNC6353 – Suspected Russian espionage group
- Google Threat Intelligence Group (GTIG)
- Lookout – Mobile security company
- CISA – Cybersecurity and Infrastructure Security Agency
- Apple – Technology company responsible for iOS patches
7. Thematic Tags
cybersecurity, cyber-espionage, state-sponsored attacks, iOS vulnerabilities, CISA directives, mobile security, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us