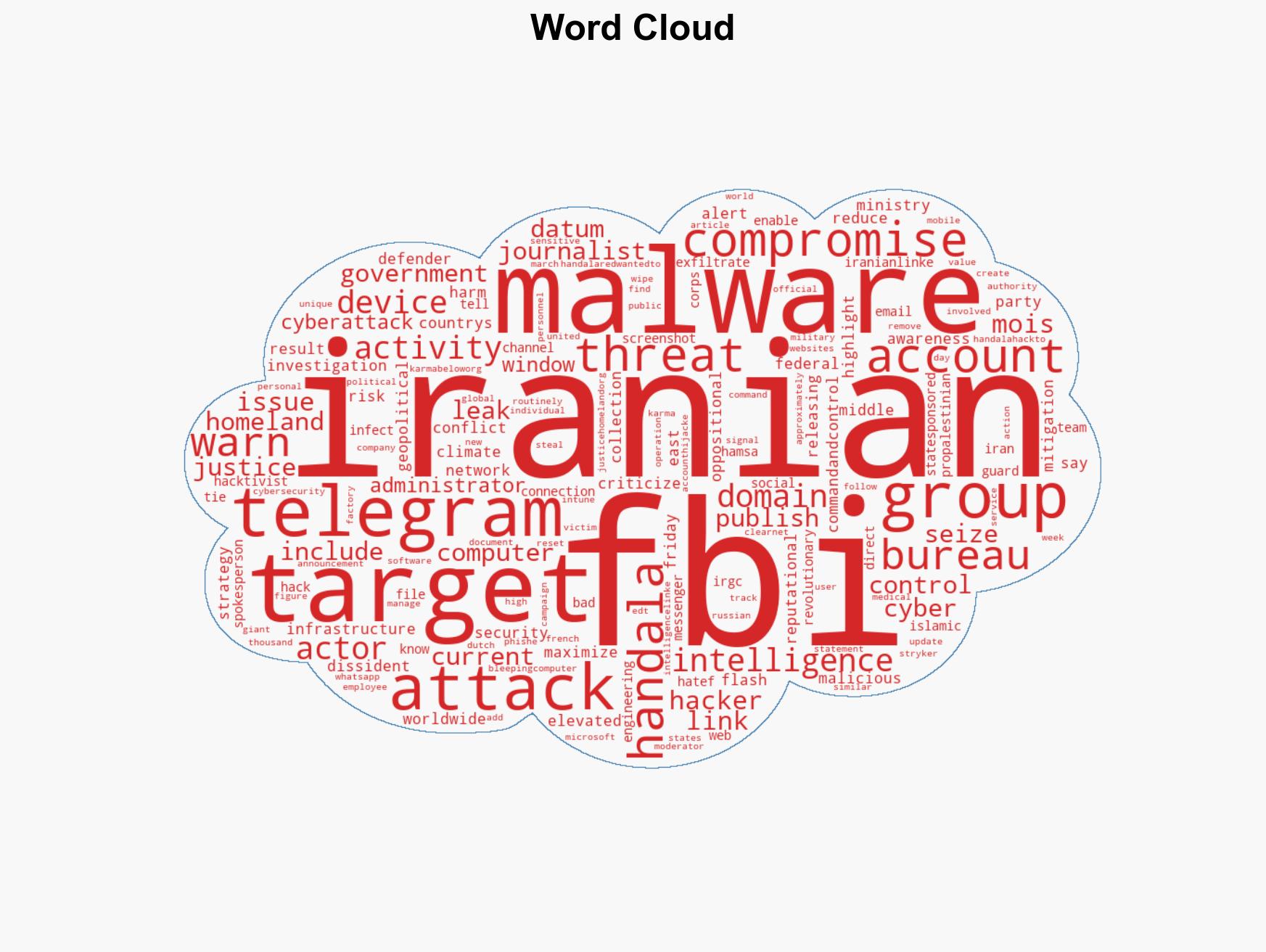
FBI Alerts on Iranian Handala Hackers Exploiting Telegram for Malware Targeting Dissidents and Journalists
Published on: 2026-03-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: FBI warns of Handala hackers using Telegram in malware attacks
1. BLUF (Bottom Line Up Front)
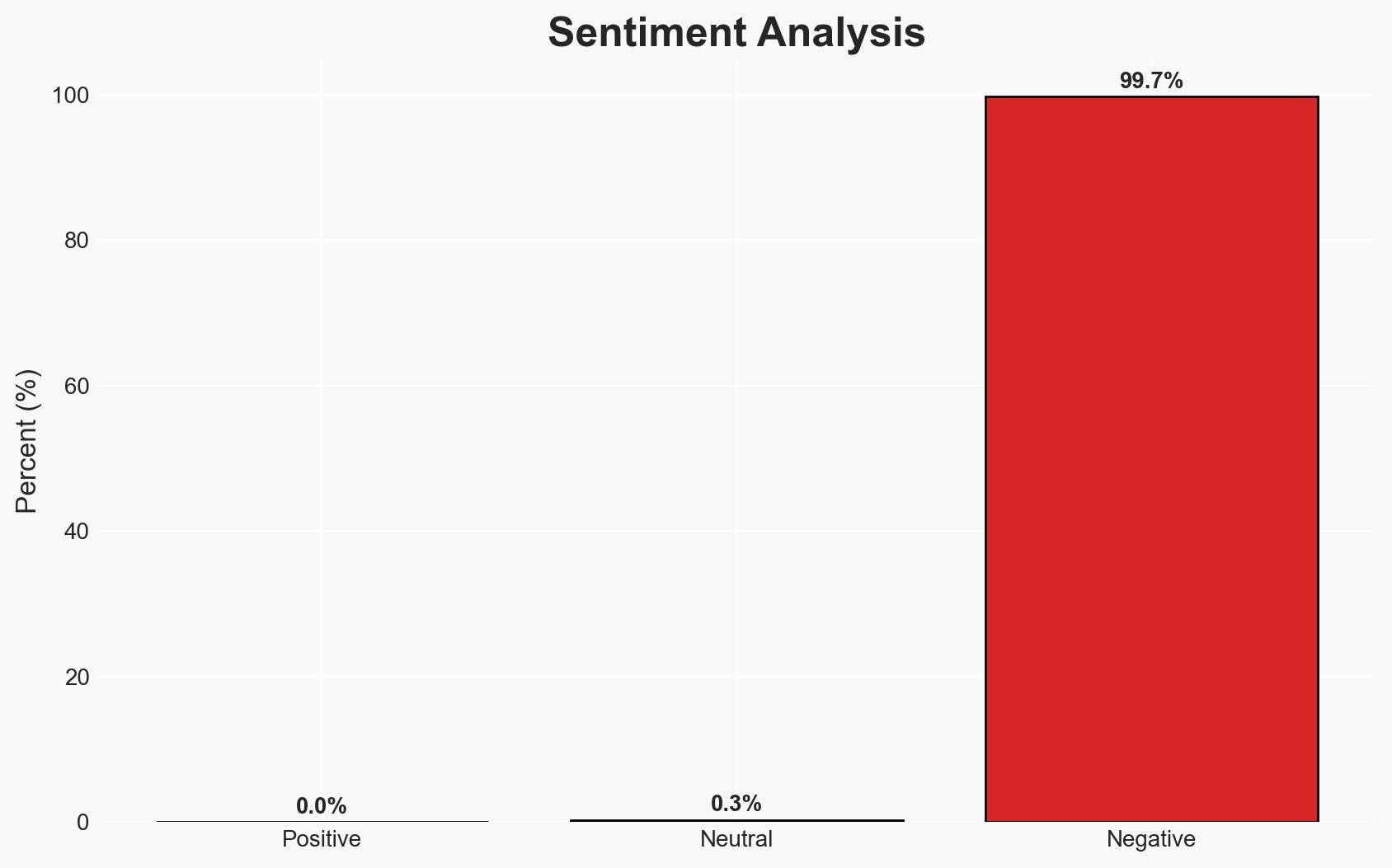
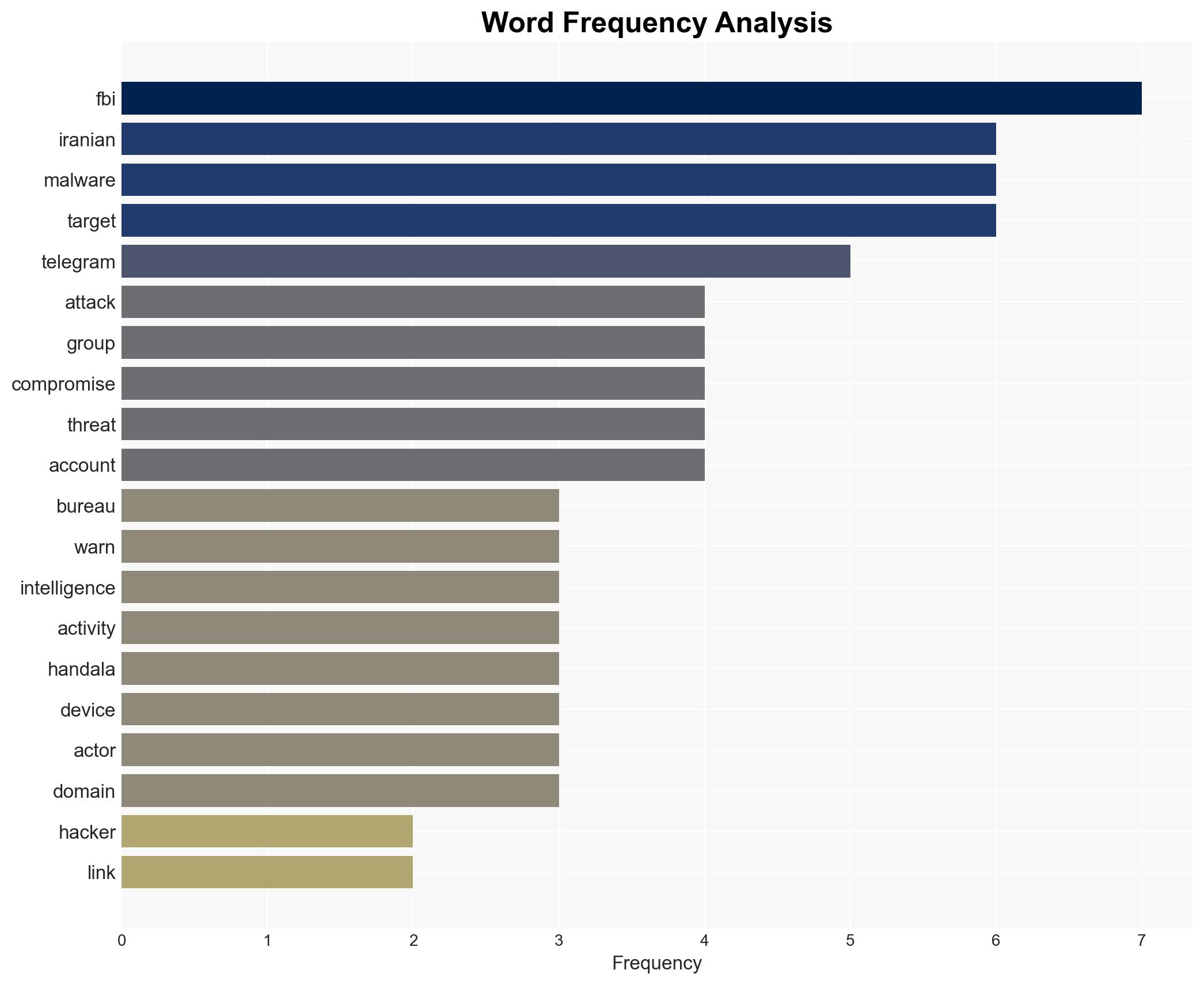
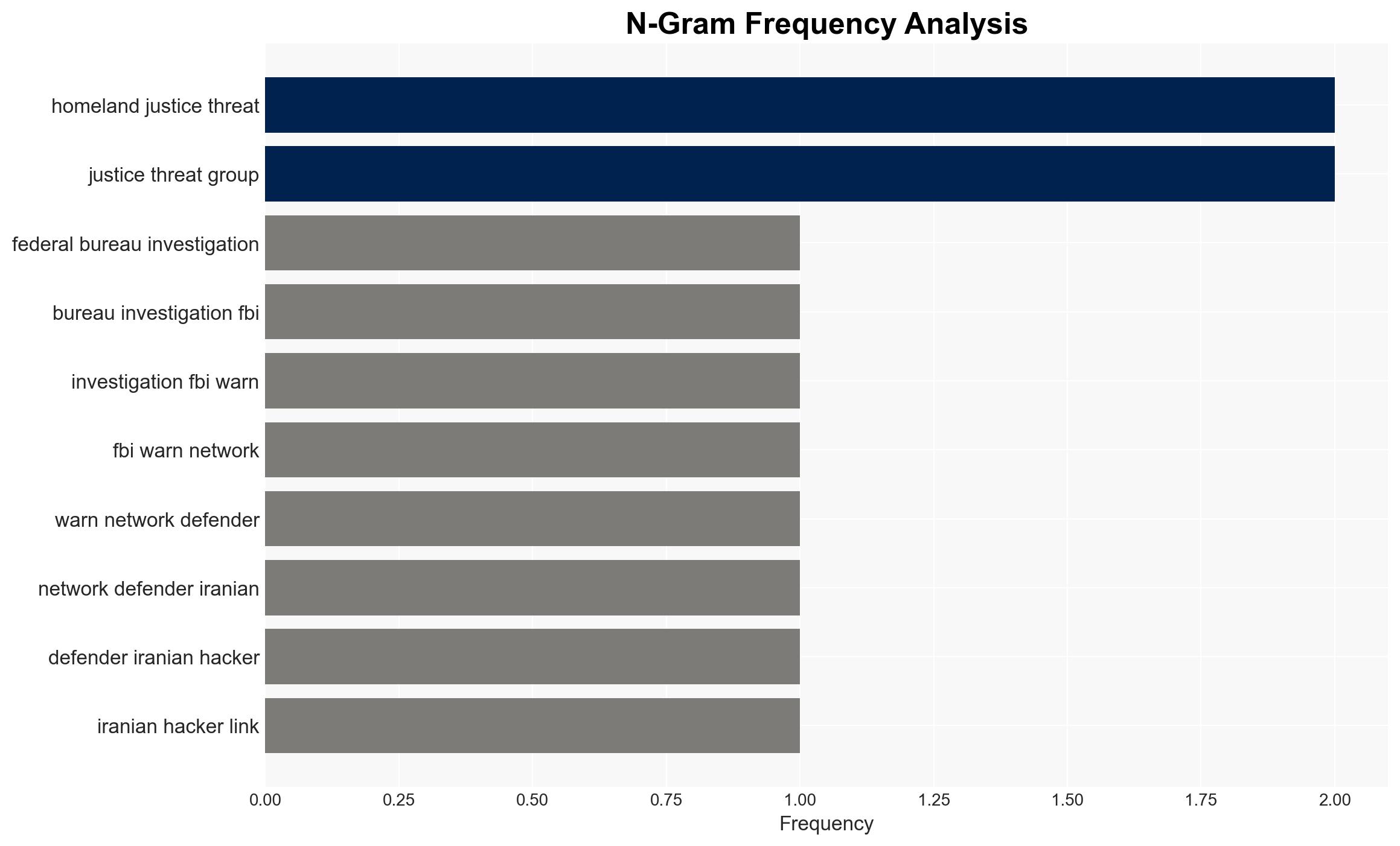
The FBI has identified Iranian MOIS-linked hackers using Telegram as C2 infrastructure for malware targeting dissidents and journalists. This activity, attributed to the Handala and Homeland Justice groups, poses significant risks to information security and geopolitical stability. The overall confidence level in this assessment is moderate due to potential information gaps and the complexity of attribution.
2. Competing Hypotheses
- Hypothesis A: Iranian state-sponsored groups are using Telegram to conduct targeted cyber operations against dissidents and journalists. This is supported by FBI alerts and the seizure of domains linked to these groups. However, the exact scale and scope of operations remain uncertain.
- Hypothesis B: The use of Telegram by these groups is opportunistic and not centrally coordinated by the Iranian state, possibly involving independent hacktivists. This is contradicted by the strategic targeting and alignment with Iranian state interests.
- Assessment: Hypothesis A is currently better supported due to the alignment of activities with known Iranian state objectives and the involvement of MOIS-linked actors. Indicators that could shift this judgment include evidence of decentralized operations or lack of direct state involvement.
3. Key Assumptions and Red Flags
- Assumptions: The Iranian government is directly supporting these cyber operations; Telegram’s infrastructure is being effectively used for C2 purposes; the targeted groups are of strategic interest to Iran.
- Information Gaps: Detailed technical analysis of the malware, confirmation of direct Iranian state orders, and comprehensive mapping of the threat actors’ network.
- Bias & Deception Risks: Potential for confirmation bias in attributing all activities to state actors; risk of deception by threat actors using false flags to mislead attribution.
4. Implications and Strategic Risks
This development could exacerbate tensions in the Middle East and increase cyber threat levels globally. The use of social media platforms for C2 may prompt regulatory and security responses.
- Political / Geopolitical: Potential escalation in cyber conflict between Iran and Western nations, impacting diplomatic relations.
- Security / Counter-Terrorism: Increased risk to individuals and organizations critical of Iran, necessitating enhanced protective measures.
- Cyber / Information Space: Highlighting vulnerabilities in widely used communication platforms, potentially leading to increased scrutiny and regulation.
- Economic / Social: Potential impacts on businesses targeted by cyberattacks, leading to financial losses and reputational damage.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of Telegram and similar platforms for C2 activity, enhance cybersecurity measures for potential targets, and engage in diplomatic channels to address state-sponsored cyber threats.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to improve threat detection, invest in cybersecurity infrastructure, and promote international cooperation on cyber norms.
- Scenario Outlook:
- Best: Effective international collaboration leads to the dismantling of threat networks.
- Worst: Escalation of cyberattacks leading to significant geopolitical conflict.
- Most-Likely: Continued low-level cyber operations with periodic escalations.
6. Key Individuals and Entities
- Handala Hack Team
- Homeland Justice
- Islamic Revolutionary Guard Corps (IRGC)
- Ministry of Intelligence and Security (MOIS)
- Telegram (as a platform)
7. Thematic Tags
cybersecurity, cyber-espionage, state-sponsored hacking, Middle East tensions, information security, geopolitical risk, social media exploitation, counter-terrorism
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us