Trio-Tech’s Singapore unit suffers ransomware attack; compromised data appears online after initial containme…
Published on: 2026-03-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Trio-Techs Singapore subsidiary hit by ransomware attack stolen data published online
1. BLUF (Bottom Line Up Front)
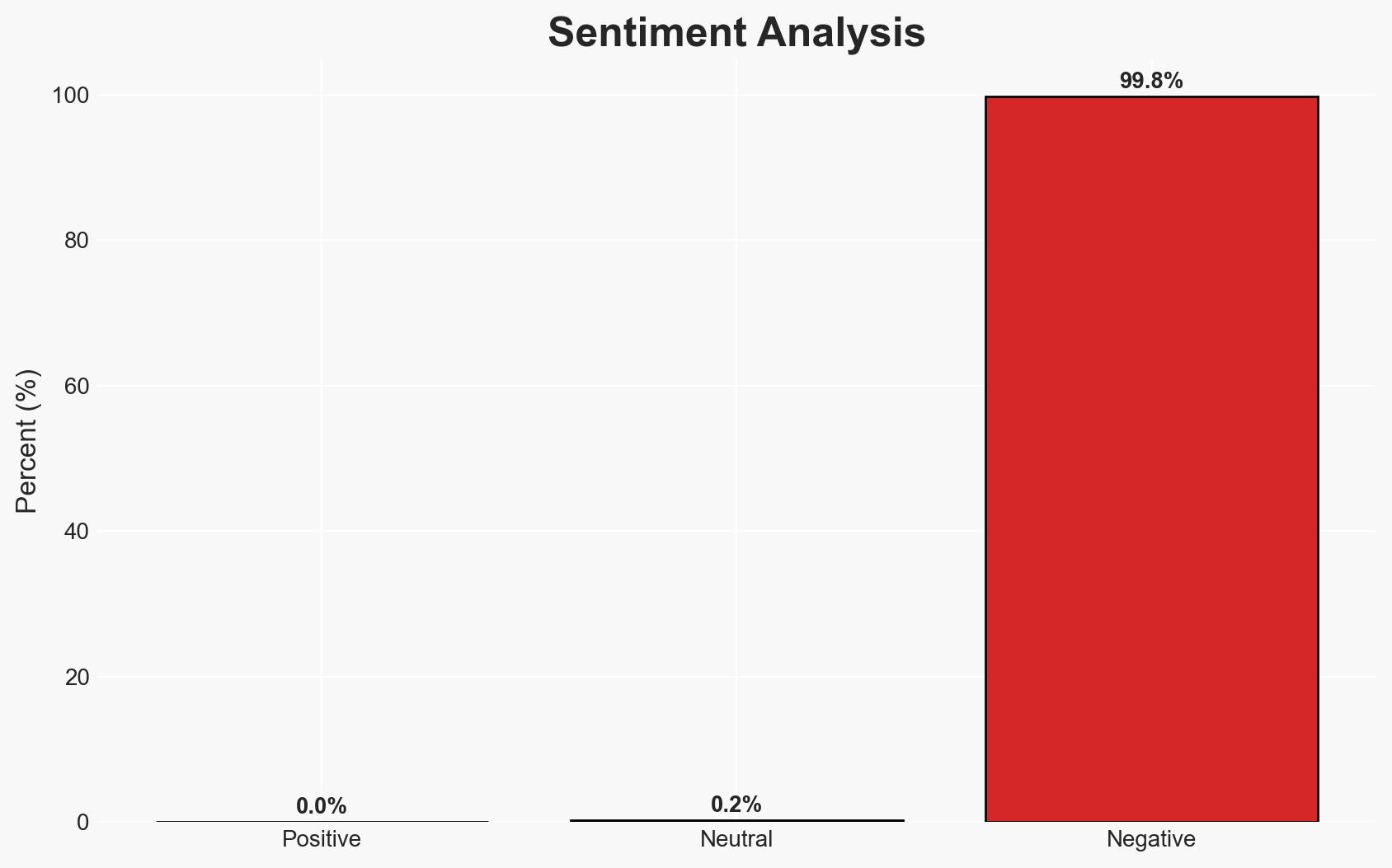
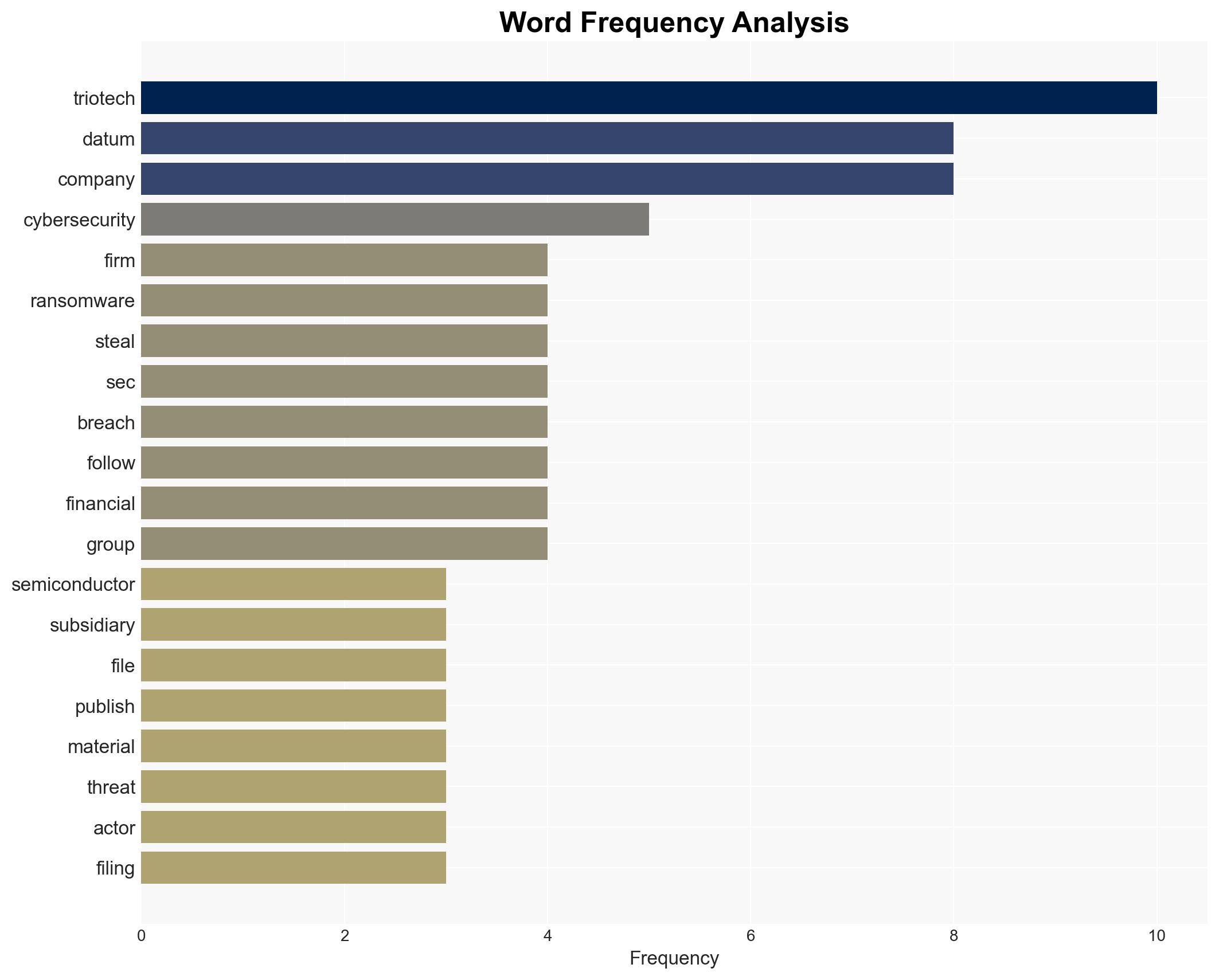
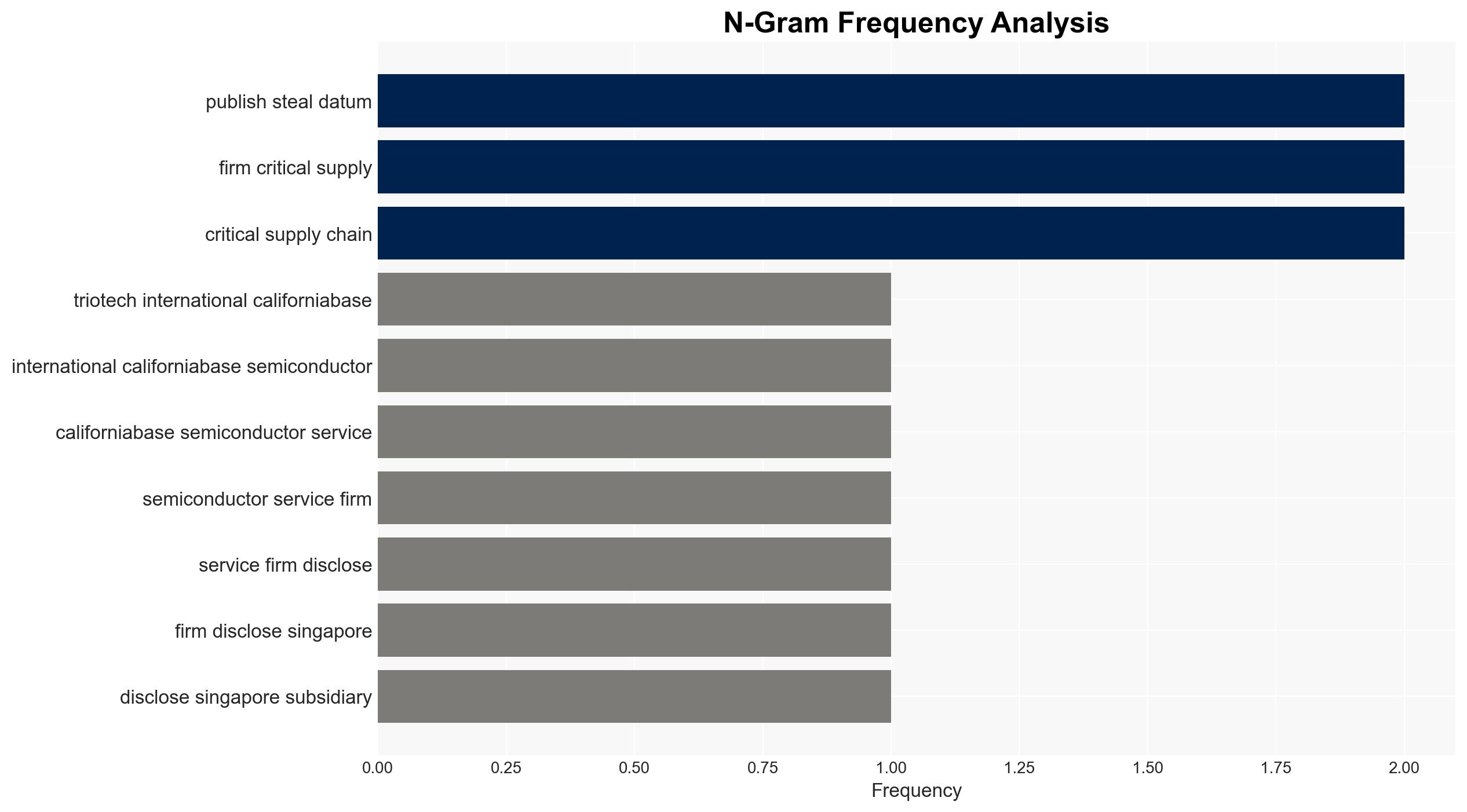
The ransomware attack on Trio-Tech’s Singapore subsidiary, attributed to the Gunra group, has resulted in the publication of stolen data online, significantly impacting the company’s operational security. The incident, initially deemed non-material, has evolved into a potentially significant cybersecurity event. This assessment is made with moderate confidence, given the ongoing investigation and incomplete data on the breach’s full scope.
2. Competing Hypotheses
- Hypothesis A: The ransomware attack was opportunistic, targeting Trio-Tech due to vulnerabilities in their cybersecurity infrastructure. This is supported by the rapid encryption and data publication, but contradicted by the lack of specific targeting information.
- Hypothesis B: The attack was strategically targeted, aiming to exploit Trio-Tech’s role in the semiconductor industry. This is supported by the attackers’ use of a double extortion tactic, but contradicted by the company’s relatively small market presence.
- Assessment: Hypothesis A is currently better supported due to the absence of evidence indicating a strategic targeting of Trio-Tech specifically. Indicators such as further attacks on similar companies or explicit statements from the attackers could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The attack was not state-sponsored; Gunra operates independently; the data published is sensitive enough to impact Trio-Tech’s operations.
- Information Gaps: Full extent of data compromised, specific vulnerabilities exploited, and the identity of affected parties.
- Bias & Deception Risks: Potential underestimation of the attack’s impact by Trio-Tech; possible misinformation from threat actors regarding their capabilities or intentions.
4. Implications and Strategic Risks
This development could lead to increased scrutiny on cybersecurity practices within the semiconductor industry, potentially influencing regulatory policies. The attack may also embolden similar threat actors to target small-cap companies perceived as vulnerable.
- Political / Geopolitical: Potential for increased regulatory oversight in the tech sector, especially concerning cybersecurity standards.
- Security / Counter-Terrorism: Heightened threat environment for semiconductor companies, necessitating improved cybersecurity measures.
- Cyber / Information Space: Increased activity in ransomware forums and potential for copycat attacks leveraging similar tactics.
- Economic / Social: Financial strain on Trio-Tech and similar companies, potentially affecting market stability and investor confidence.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of dark web activity related to Trio-Tech, strengthen cybersecurity protocols, and engage with law enforcement for threat actor identification.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing, and invest in employee cybersecurity training and infrastructure upgrades.
- Scenario Outlook:
- Best Case: Rapid containment and remediation with minimal operational impact; improved cybersecurity posture.
- Worst Case: Prolonged data exposure leading to significant financial losses and reputational damage.
- Most-Likely: Gradual recovery with increased cybersecurity investments and minor regulatory impacts.
6. Key Individuals and Entities
- Trio-Tech International
- Gunra ransomware group
- SEC (Securities and Exchange Commission)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
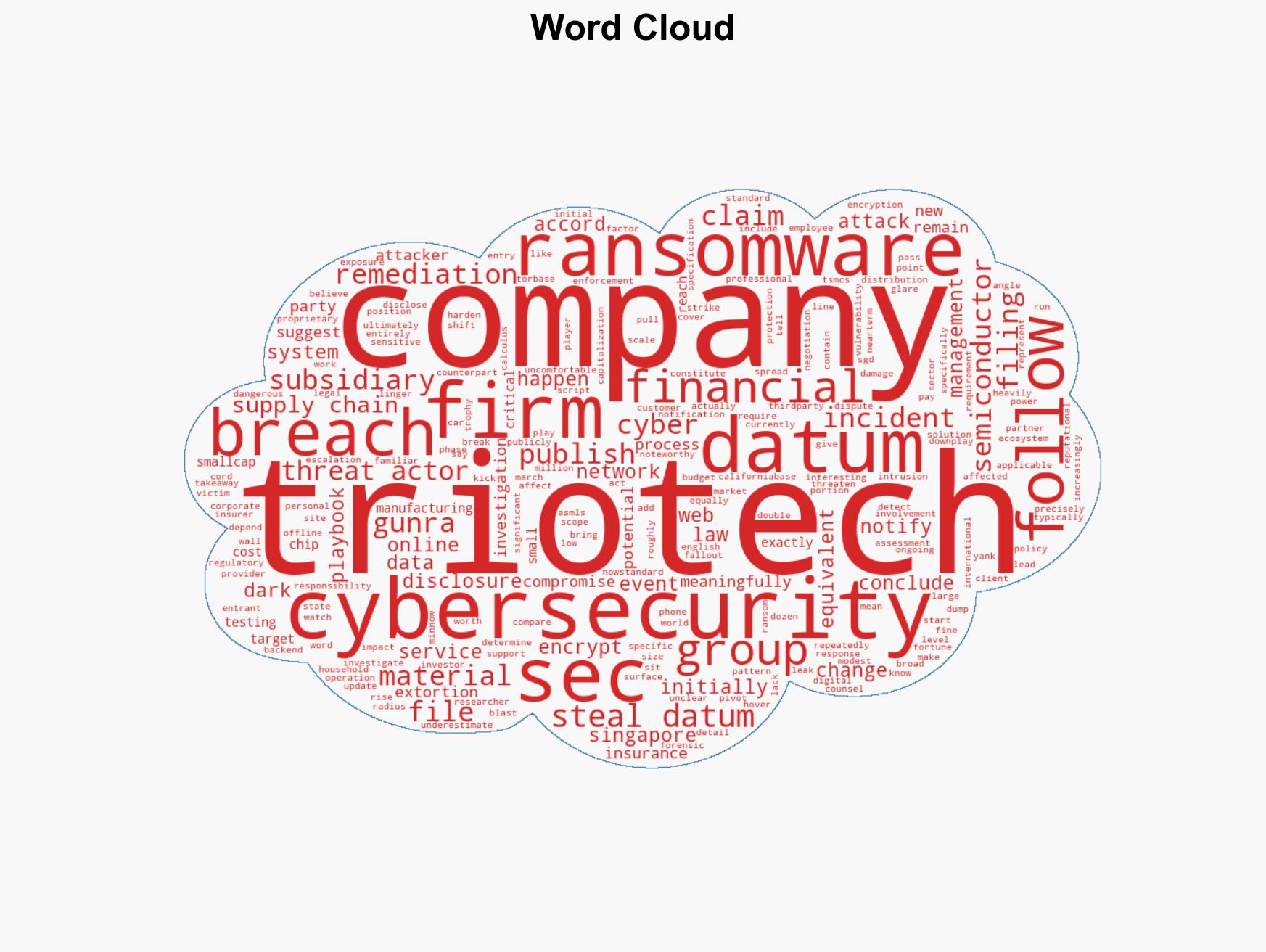
cybersecurity, ransomware, semiconductor industry, data breach, cyber extortion, regulatory impact, threat intelligence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us