Flashpoint launches advanced threat intelligence suite to connect cyber threats with business implications
Published on: 2026-03-23
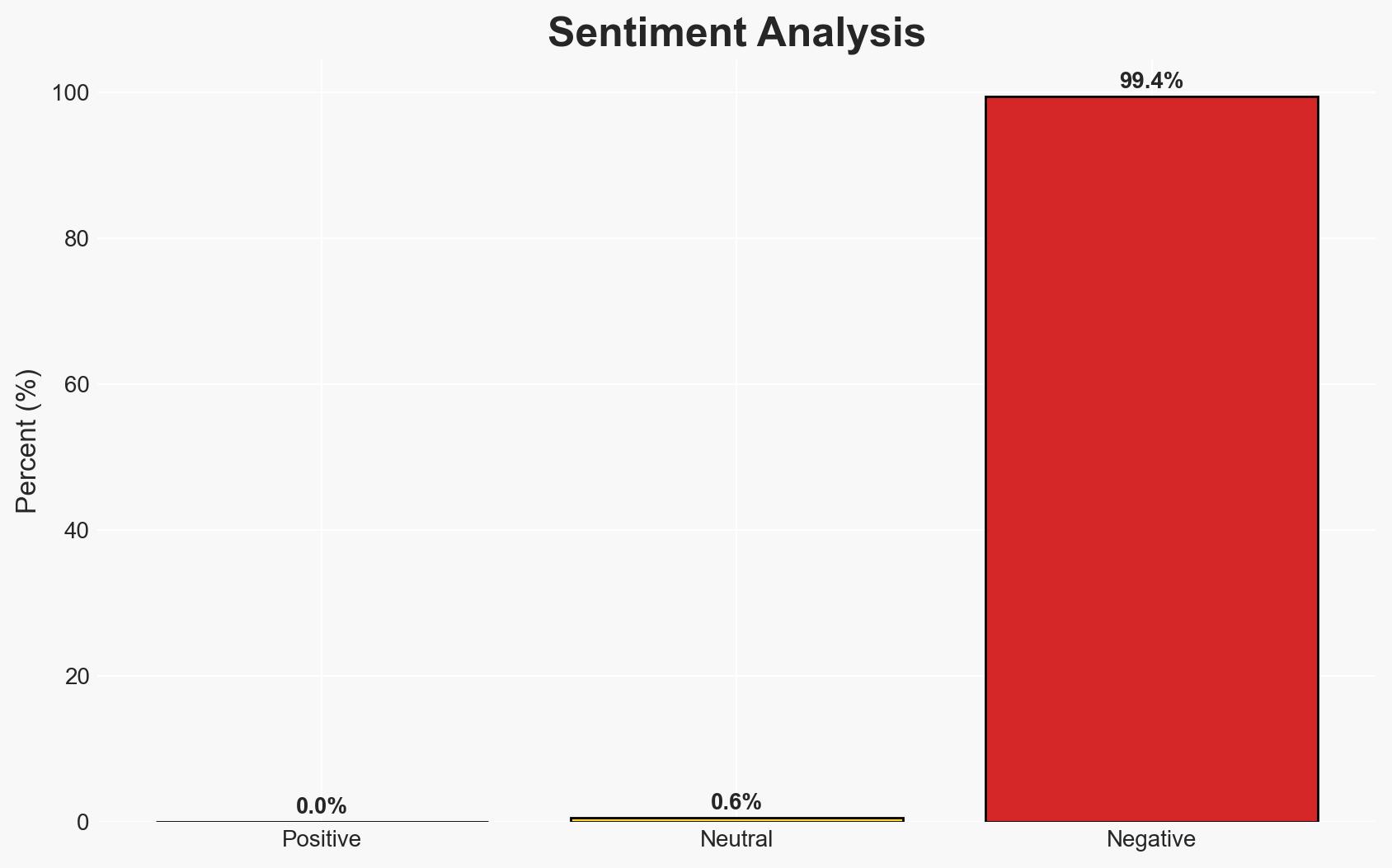
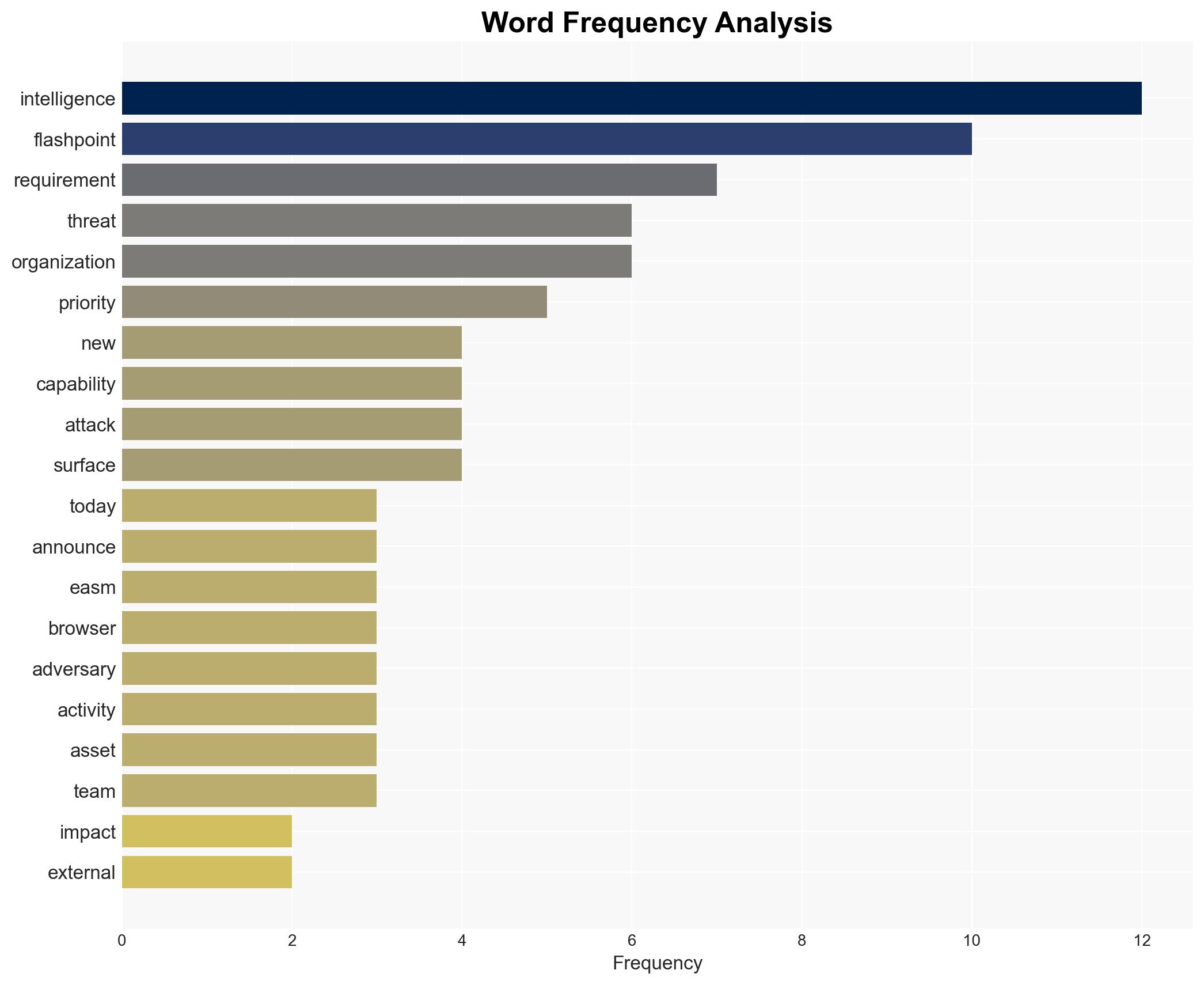
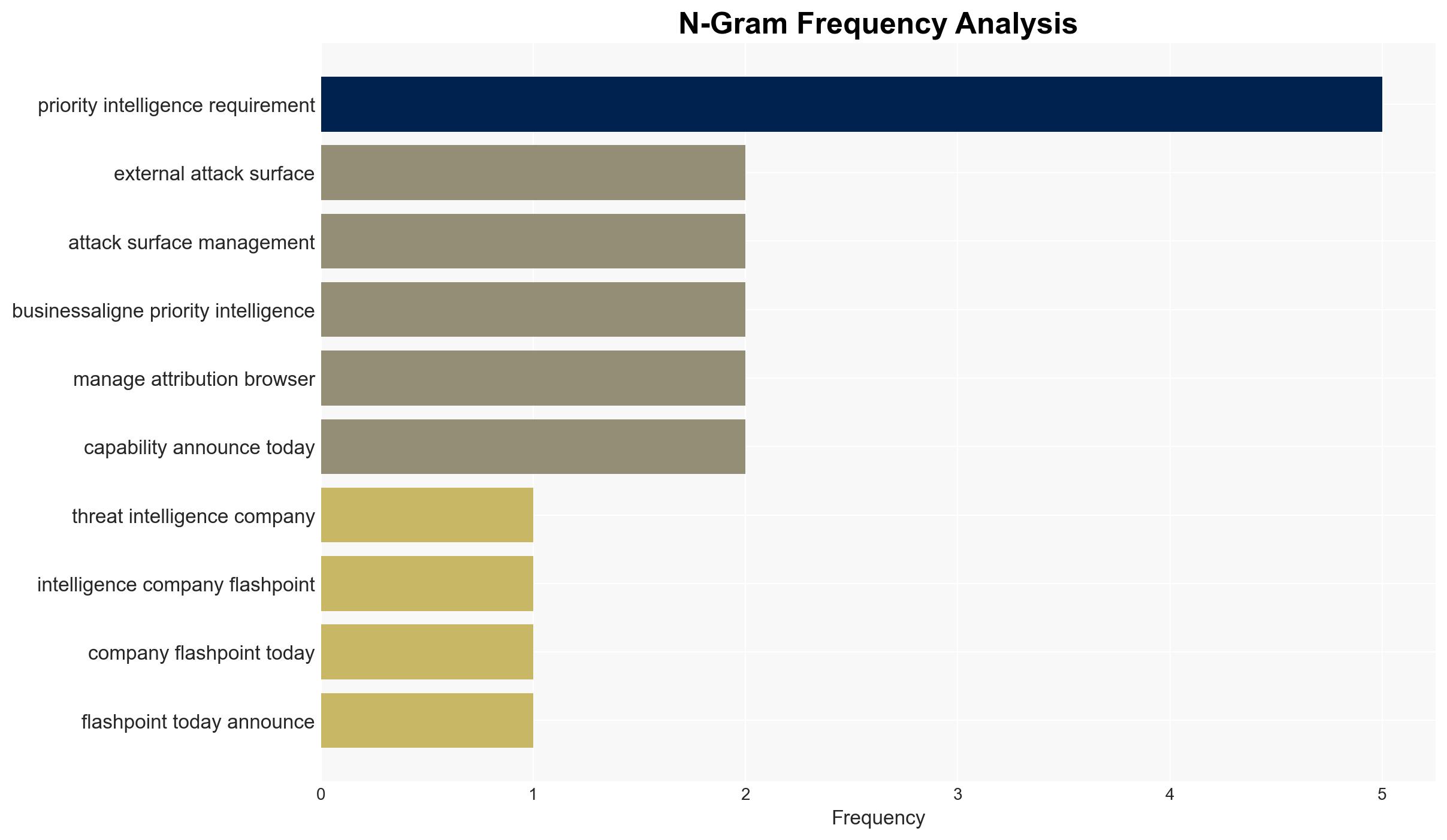
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Flashpoint unveils new threat intelligence suite to link cyber risks to business impact
1. BLUF (Bottom Line Up Front)
Flashpoint has introduced a new threat intelligence suite aimed at enhancing the linkage between cyber risks and business impact, potentially improving organizational security posture. The suite includes capabilities like External Attack Surface Management and business-aligned Priority Intelligence Requirements. This development is likely to affect cybersecurity teams and decision-makers within enterprises. Overall, there is moderate confidence in the positive impact of these tools on organizational threat intelligence operations.
2. Competing Hypotheses
- Hypothesis A: Flashpoint’s new suite will significantly enhance organizations’ ability to prioritize and respond to cyber threats by providing clearer connections between threat data and business impact. Supporting evidence includes the introduction of threat-informed EASM and Priority Intelligence Requirements. However, the effectiveness of these tools in diverse organizational contexts remains uncertain.
- Hypothesis B: The new suite may not substantially change current threat intelligence practices due to potential integration challenges and the need for organizational adaptation. While the tools offer advanced capabilities, their success depends on proper implementation and user training, which may not be uniformly achievable across all organizations.
- Assessment: Hypothesis A is currently better supported due to the innovative nature of the tools and their alignment with identified gaps in existing threat intelligence processes. Indicators such as widespread adoption and positive feedback from early adopters could further support this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Organizations have the necessary infrastructure to integrate these new tools; Flashpoint’s data sources are comprehensive and reliable; cybersecurity teams are adequately trained to utilize the new capabilities.
- Information Gaps: Specific metrics on the effectiveness of the new suite in reducing cyber incidents; user feedback from early adopters; compatibility with existing security systems.
- Bias & Deception Risks: Potential bias in Flashpoint’s promotional materials; over-reliance on vendor-provided data without independent validation; possible exaggeration of tool capabilities.
4. Implications and Strategic Risks
This development could lead to a more proactive cybersecurity posture among organizations, potentially reducing the impact of cyber threats. However, the success of these tools depends on their integration and user adoption.
- Political / Geopolitical: Minimal direct impact, but improved cybersecurity could enhance national resilience against state-sponsored cyber threats.
- Security / Counter-Terrorism: Enhanced threat intelligence could improve detection and response times, reducing the risk of successful cyber-attacks.
- Cyber / Information Space: The suite could set a new standard in threat intelligence, prompting competitors to innovate similarly.
- Economic / Social: Improved cybersecurity could lead to increased trust in digital services, potentially boosting economic activity.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Evaluate the compatibility of Flashpoint’s suite with existing systems; conduct pilot testing with a focus on integration and user training.
- Medium-Term Posture (1–12 months): Develop partnerships with Flashpoint for ongoing support and updates; invest in training programs to maximize tool efficacy.
- Scenario Outlook:
- Best: Widespread adoption leads to significant reductions in cyber incidents.
- Worst: Integration challenges limit the suite’s effectiveness, resulting in minimal impact.
- Most-Likely: Gradual improvement in threat intelligence capabilities as organizations adapt to the new tools.
6. Key Individuals and Entities
- Flashpoint (Threat Intelligence Company)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, threat intelligence, business impact, risk management, cyber threats, organizational security, enterprise security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us