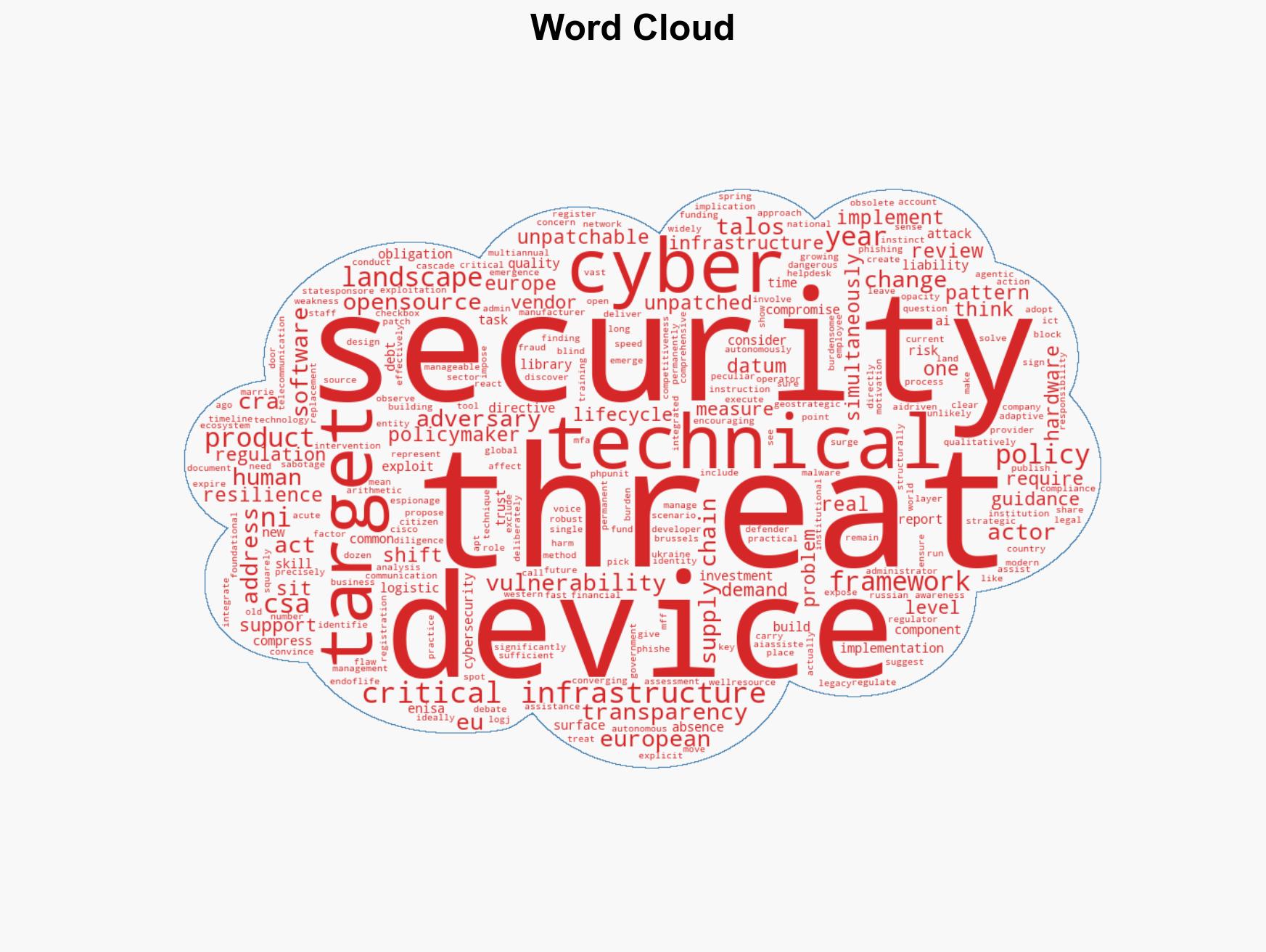
Shifts in Threat Landscape Highlight Critical Gaps in Europe’s Cybersecurity Policies
Published on: 2026-03-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: What the Evolution of the Threat Landscape Tells Us About the Gaps in Europes Cyber Policy
1. BLUF (Bottom Line Up Front)
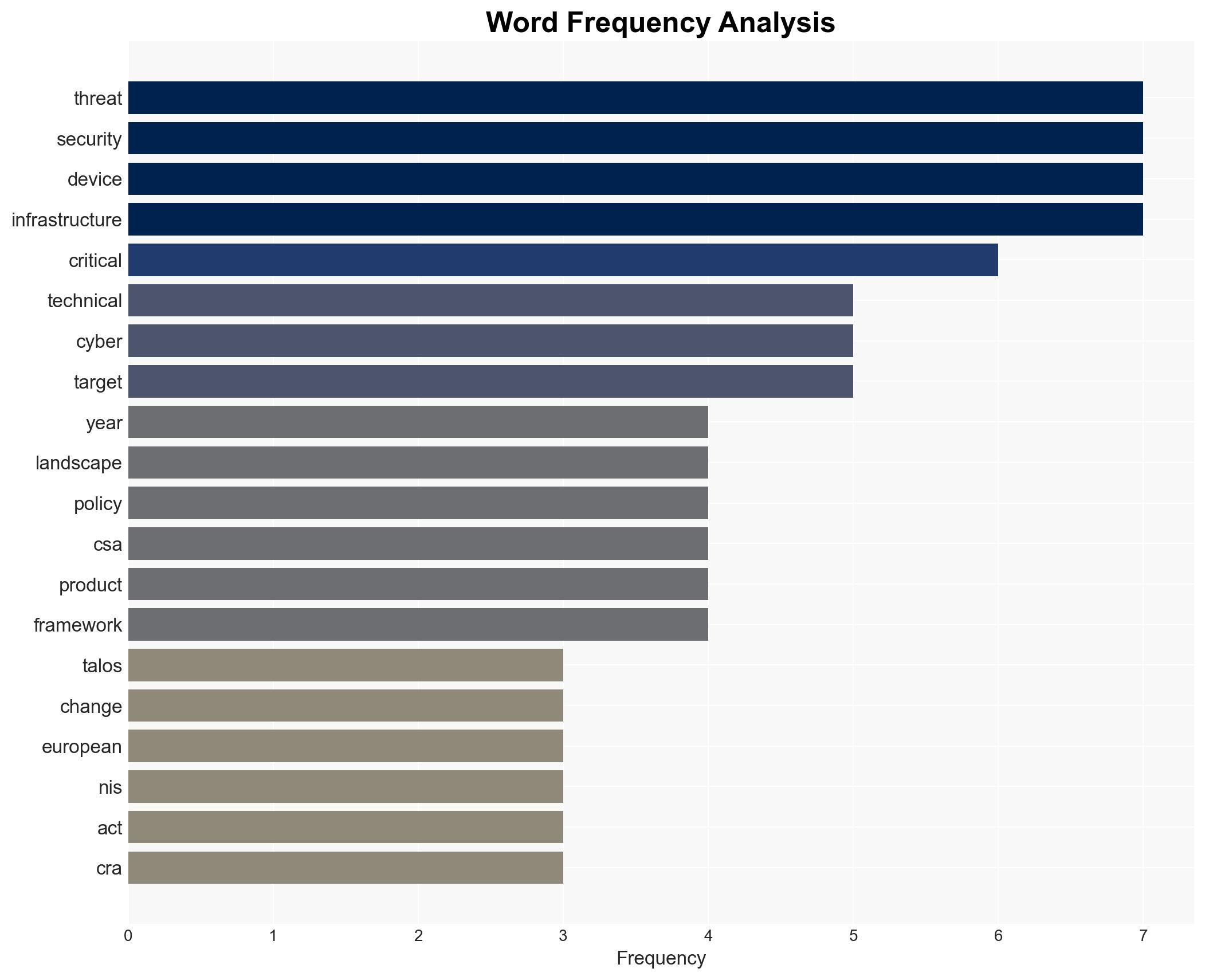
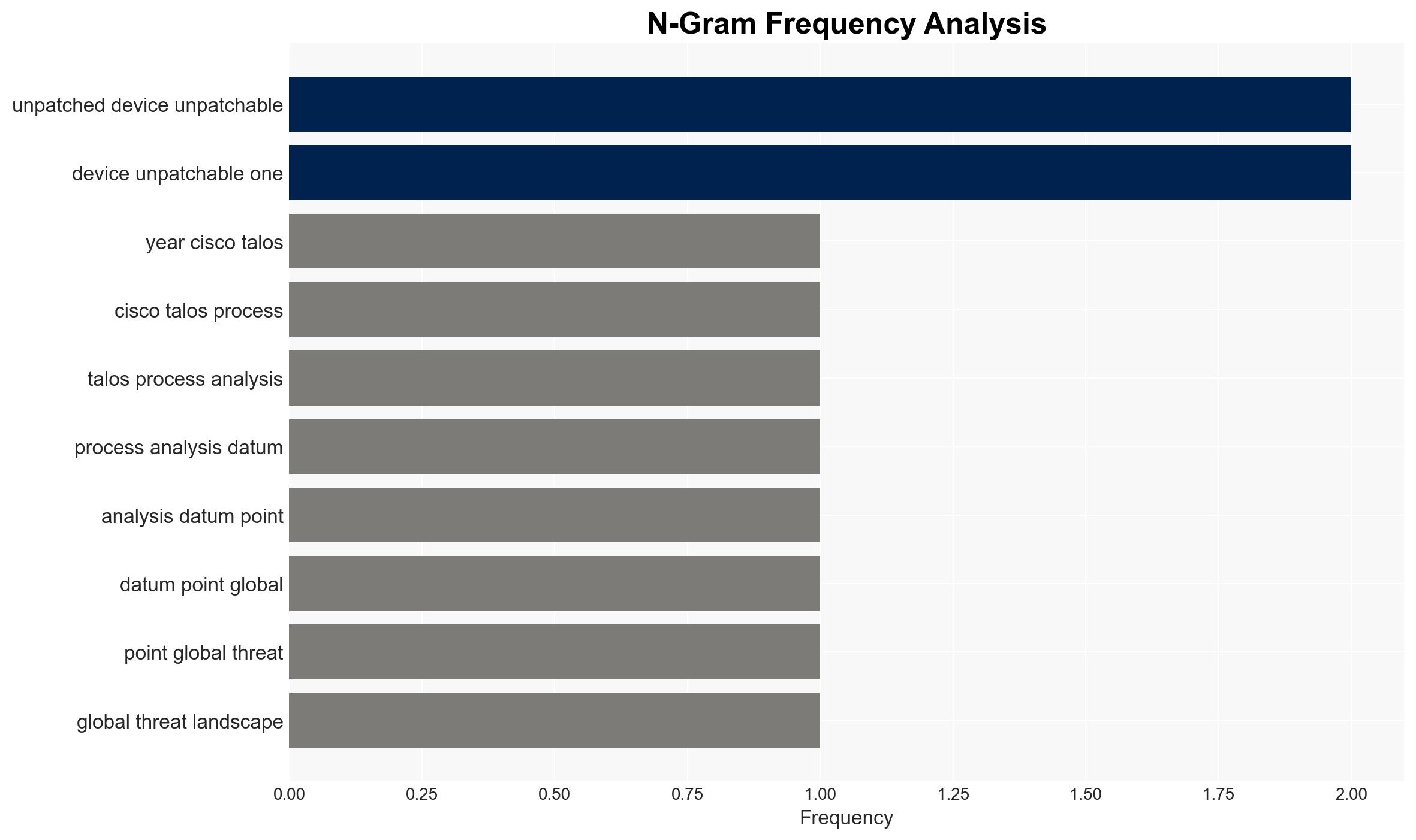
The current European cyber policy framework inadequately addresses the management of unpatchable, end-of-life devices, creating significant vulnerabilities in critical infrastructure. The emergence of autonomous malware further exacerbates these risks, compressing response times for defenders. This situation poses a growing threat to national security and economic stability, with moderate confidence in these assessments.
2. Competing Hypotheses
- Hypothesis A: European cyber policies are sufficient, and the current gaps will be addressed through national-level initiatives and existing frameworks. Evidence includes some countries considering NIS2 implementation to tackle these issues. However, the lack of explicit guidance at the EU level contradicts this.
- Hypothesis B: European cyber policies are insufficient to manage the risks posed by unpatchable devices and autonomous malware. The evidence includes the absence of EU-level guidance on managing obsolete devices and the rapid evolution of autonomous threats. This hypothesis is better supported due to the structural changes in the threat landscape and policy gaps.
- Assessment: Hypothesis B is currently best supported due to the structural inadequacies in EU cyber policies and the rapid evolution of autonomous threats. Key indicators that could shift this judgment include the introduction of comprehensive EU-level policies addressing these gaps.
3. Key Assumptions and Red Flags
- Assumptions: European policymakers will continue to prioritize cyber resilience; the threat landscape will continue to evolve rapidly; national-level initiatives will not fully compensate for EU-level policy gaps; autonomous malware will become more prevalent.
- Information Gaps: Specific national-level initiatives addressing these gaps; detailed data on the prevalence and impact of autonomous malware in Europe.
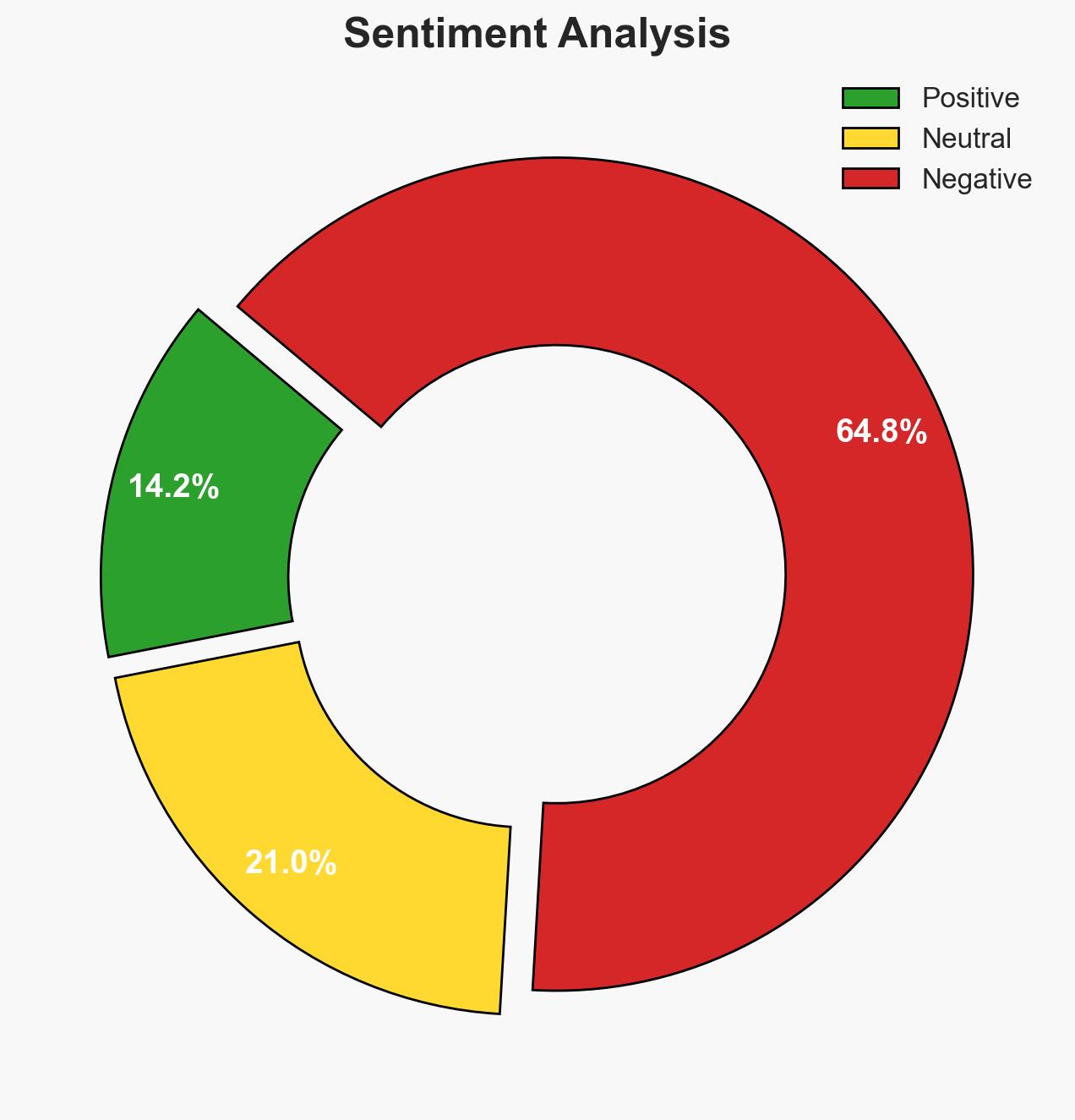
- Bias & Deception Risks: Potential bias in over-reliance on Cisco Talos data; risk of underestimating national-level policy effectiveness; adversarial misinformation campaigns could skew threat perception.
4. Implications and Strategic Risks
The evolving threat landscape could lead to increased cyber incidents affecting critical infrastructure, with potential geopolitical and economic ramifications. Autonomous malware may accelerate the pace and complexity of cyber threats, challenging existing defense mechanisms.
- Political / Geopolitical: Increased cyber incidents could strain international relations and lead to calls for stronger collective defense mechanisms.
- Security / Counter-Terrorism: The operational environment may become more complex, with increased risks of state-sponsored cyber sabotage.
- Cyber / Information Space: The rise of autonomous malware could lead to more sophisticated cyber-attacks, challenging current cybersecurity frameworks.
- Economic / Social: Potential disruptions to critical infrastructure could impact economic stability and public trust in digital systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive review of critical infrastructure vulnerabilities; enhance monitoring for autonomous malware activities; engage with national policymakers to align strategies.
- Medium-Term Posture (1–12 months): Develop EU-level policies for managing obsolete devices; invest in AI-driven cybersecurity solutions; foster international partnerships for threat intelligence sharing.
- Scenario Outlook:
- Best: EU implements comprehensive policies, reducing vulnerabilities (trigger: policy announcements).
- Worst: Increased cyber incidents lead to significant infrastructure disruptions (trigger: multiple high-profile attacks).
- Most-Likely: Gradual policy improvements with ongoing vulnerabilities (trigger: incremental policy updates).
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cybersecurity policy, critical infrastructure, autonomous malware, EU regulations, threat landscape, national security, cyber resilience
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us