Half of cybersecurity leaders feel unprepared for AI-driven attacks; four key steps to enhance defenses now.
Published on: 2026-03-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: 1 in 2 security leaders say they’re not ready for AI attacks – 4 actions to take now
1. BLUF (Bottom Line Up Front)
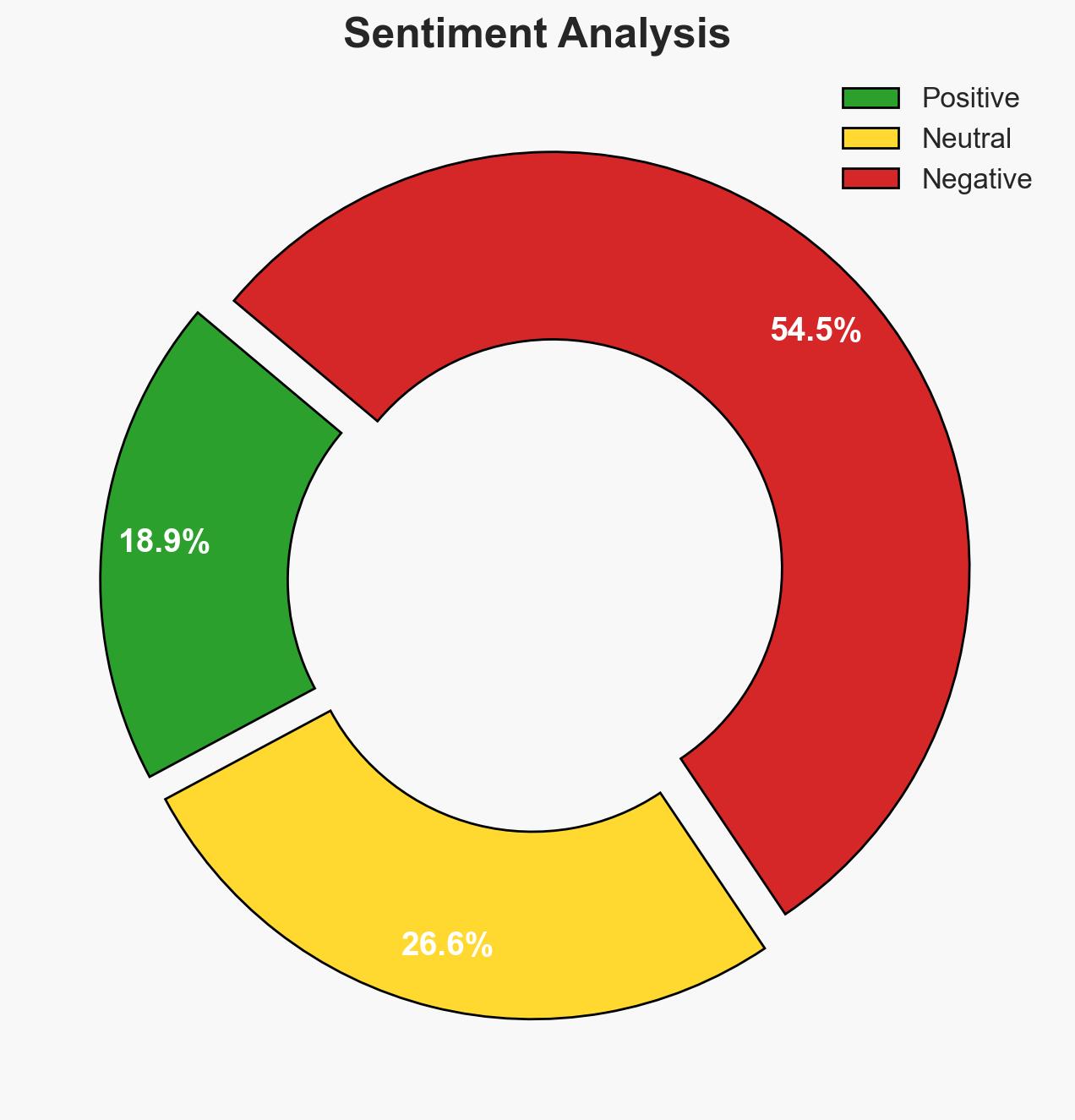
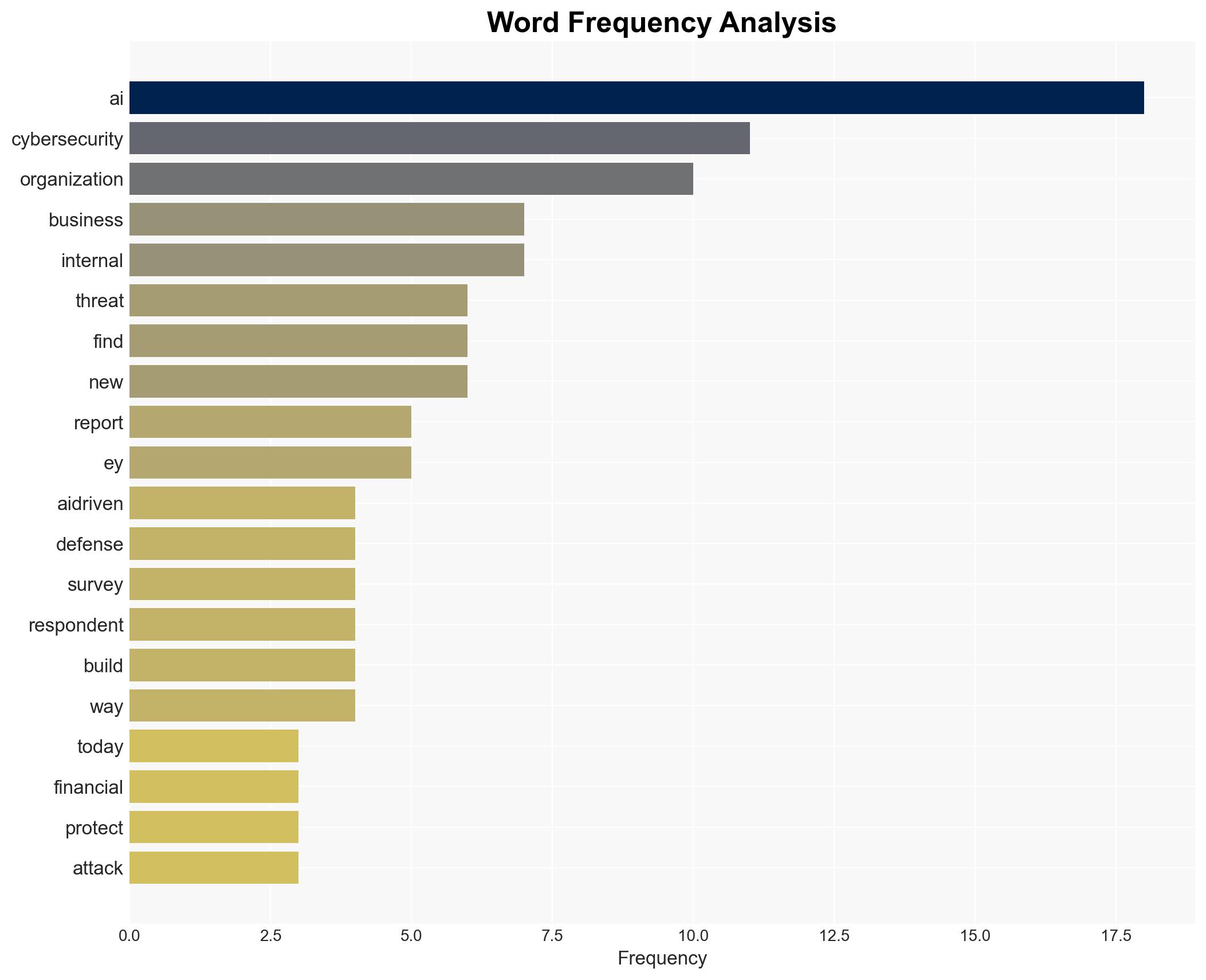
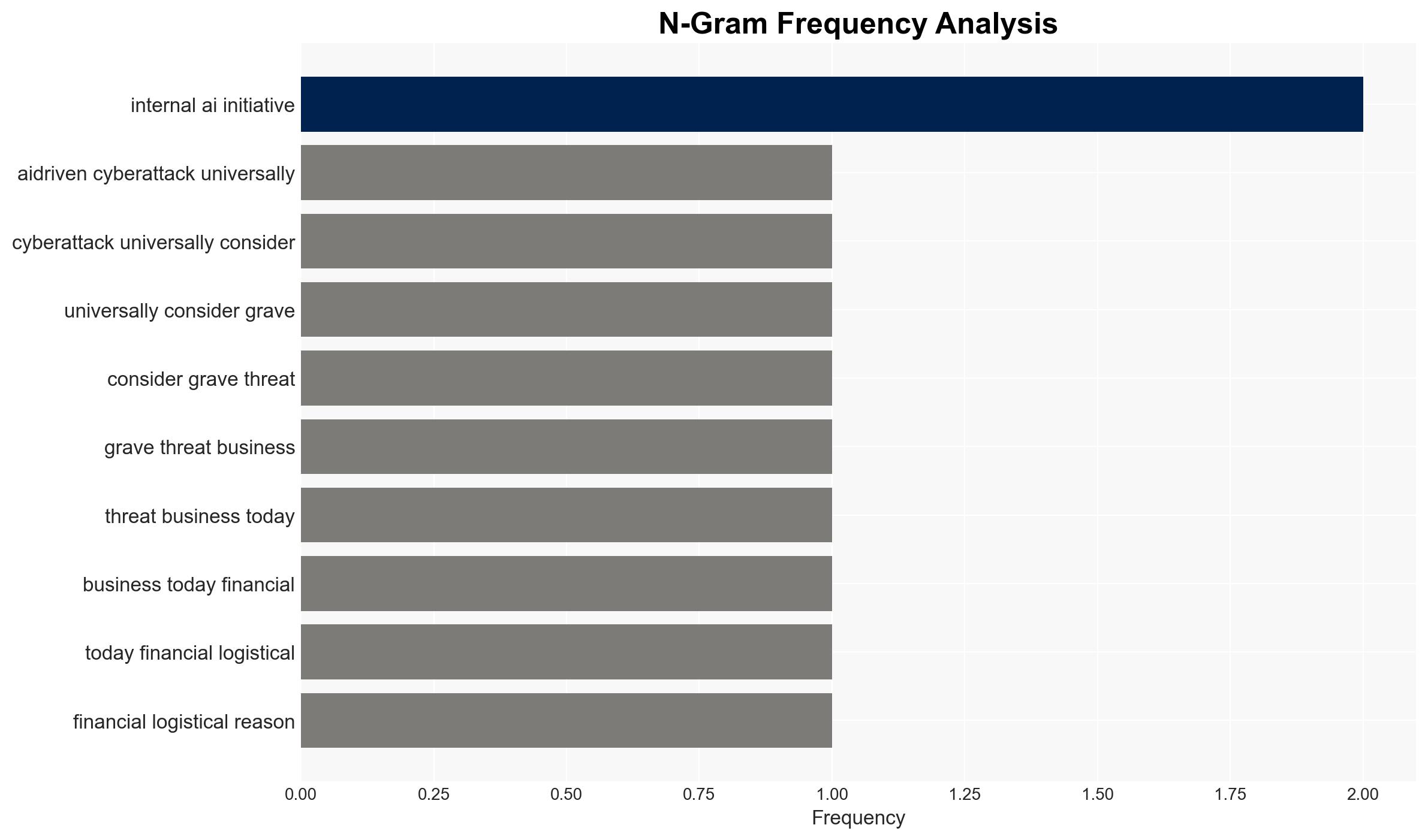
The majority of organizations recognize AI-driven cyberattacks as a significant threat but lack preparedness and a clear strategy to counteract them. This gap in readiness poses a substantial risk to business operations and security. The most likely hypothesis is that organizations will continue to struggle with AI integration in cybersecurity, leading to increased vulnerability. Overall confidence in this judgment is moderate.
2. Competing Hypotheses
- Hypothesis A: Organizations will rapidly develop and implement effective AI-driven cybersecurity strategies. This is supported by the high awareness of AI threats among security leaders. However, the lack of confidence and current pilot status of many initiatives contradicts this hypothesis.
- Hypothesis B: Organizations will continue to face challenges in deploying AI effectively for cybersecurity, leading to persistent vulnerabilities. This is supported by the low confidence levels and the failure of many AI initiatives to deliver ROI. The ongoing struggle to integrate AI into business processes further supports this hypothesis.
- Assessment: Hypothesis B is currently better supported due to the widespread acknowledgment of AI threats without corresponding confidence in defense capabilities. Indicators that could shift this judgment include significant investments in AI training and infrastructure or successful pilot programs transitioning to full implementation.
3. Key Assumptions and Red Flags
- Assumptions: Organizations have the necessary resources to invest in AI-driven cybersecurity; AI threats will continue to evolve; current AI technologies can be effectively adapted for cybersecurity purposes.
- Information Gaps: Detailed data on specific AI-driven attacks organizations have faced; insights into successful AI integration strategies in cybersecurity.
- Bias & Deception Risks: Overreliance on self-reported confidence levels; potential underreporting of successful AI-driven attacks due to reputational concerns.
4. Implications and Strategic Risks
The development of AI-driven cyber threats could significantly alter the cybersecurity landscape, affecting multiple domains.
- Political / Geopolitical: Increased cyber tensions between states as AI capabilities are weaponized.
- Security / Counter-Terrorism: Enhanced capabilities for non-state actors to conduct sophisticated cyber operations.
- Cyber / Information Space: Proliferation of AI tools among cybercriminals, leading to more frequent and complex attacks.
- Economic / Social: Potential economic disruptions from successful cyberattacks; increased pressure on workforce to upskill in AI technologies.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct comprehensive risk assessments; initiate AI training programs for cybersecurity teams; enhance monitoring of AI-driven threat vectors.
- Medium-Term Posture (1–12 months): Develop partnerships with AI research institutions; invest in AI infrastructure; establish a clear AI integration roadmap for cybersecurity.
- Scenario Outlook:
- Best Case: Organizations successfully integrate AI, reducing vulnerabilities (trigger: significant AI investment).
- Worst Case: AI-driven attacks outpace defensive measures, leading to major breaches (trigger: continued failure in AI deployment).
- Most Likely: Gradual improvement in AI integration with ongoing challenges (trigger: incremental advancements in AI training and infrastructure).
6. Key Individuals and Entities
- Ganesh Devarajan, cyber risk lead at EY Americas
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, AI integration, cyber threats, organizational readiness, AI-driven attacks, risk management, digital transformation
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us