Mandiant report reveals attackers now transfer access in just 22 seconds, highlighting evolving tactics.
Published on: 2026-03-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Attackers are handing off access in 22 seconds Mandiant finds
1. BLUF (Bottom Line Up Front)
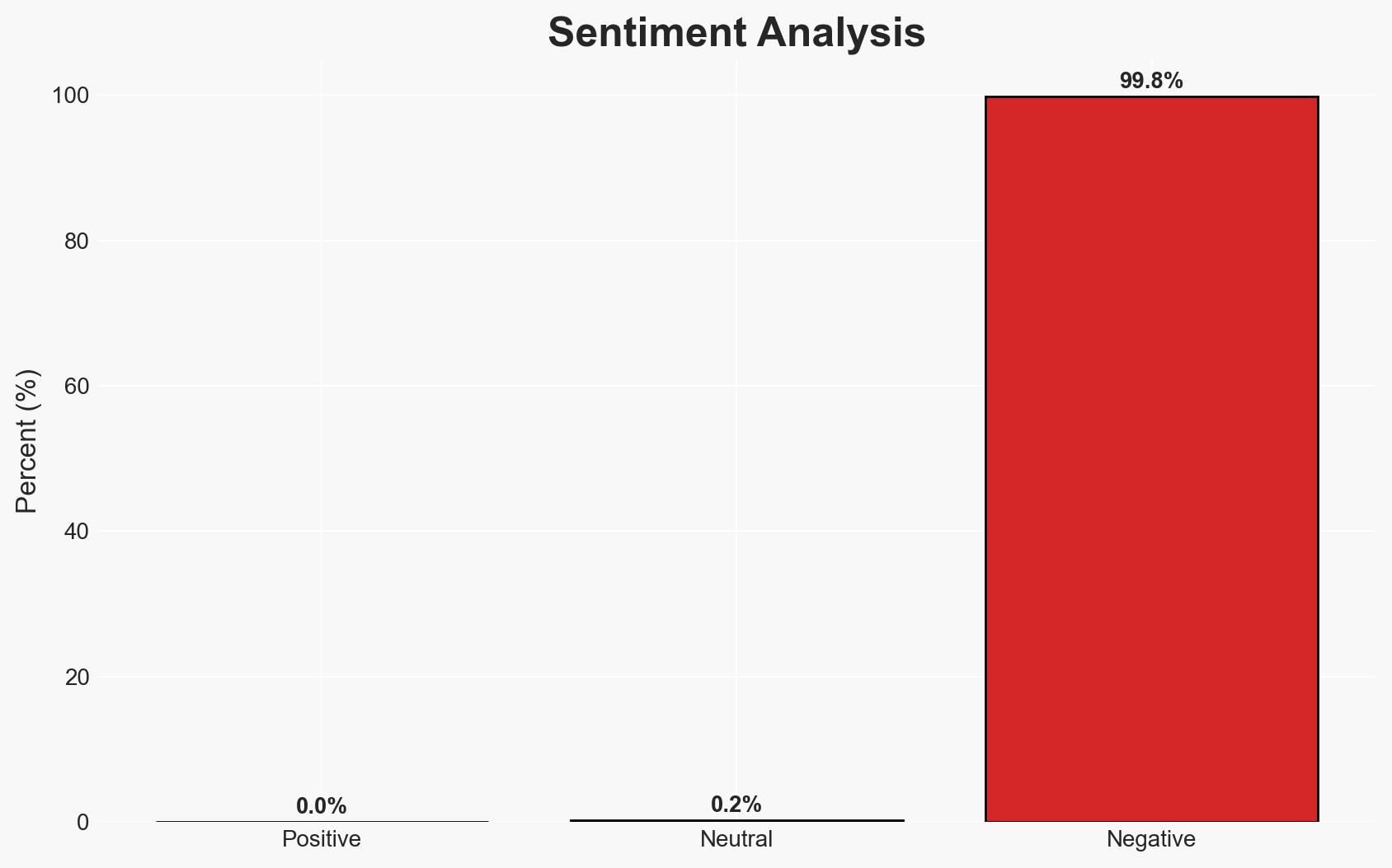
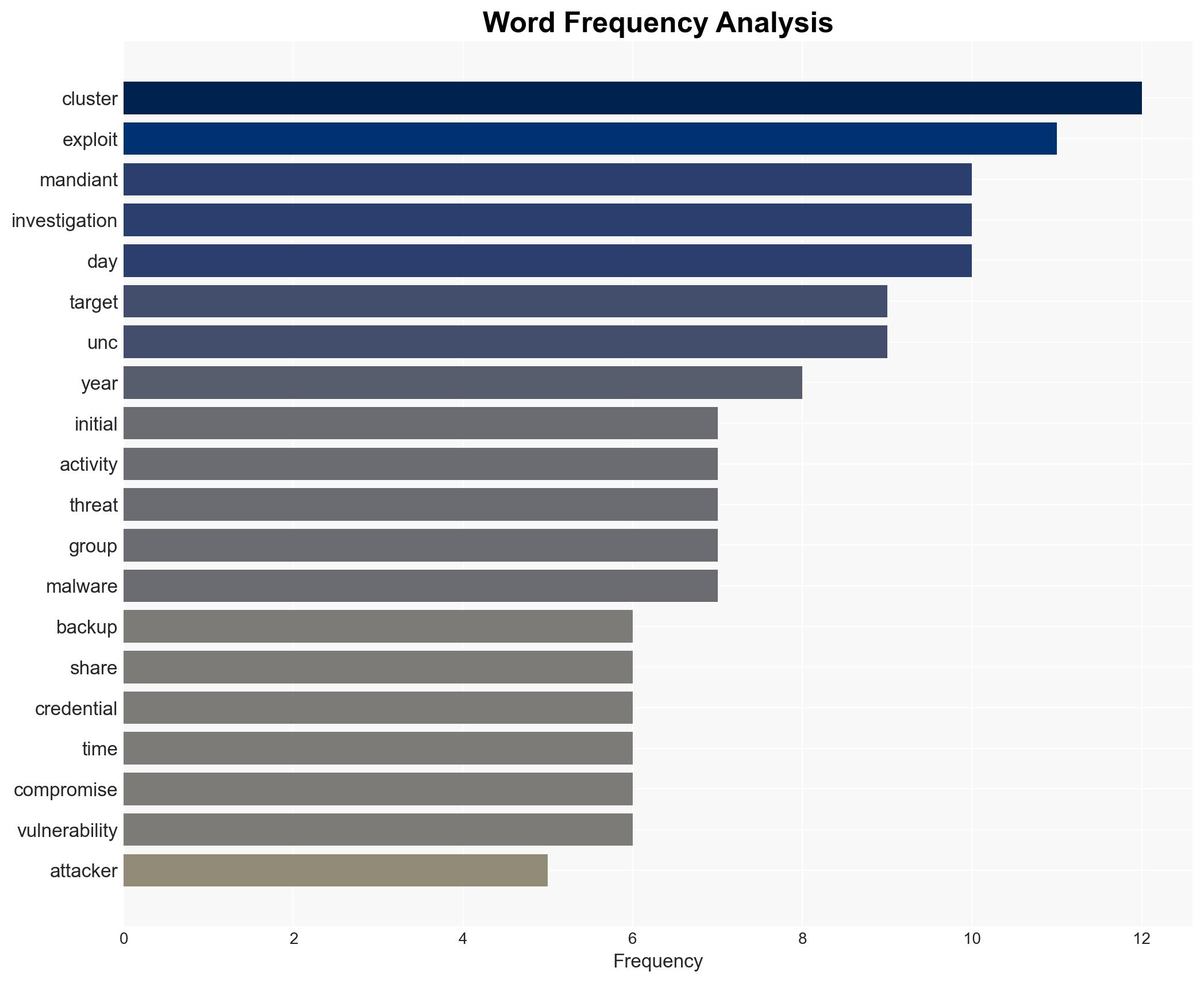
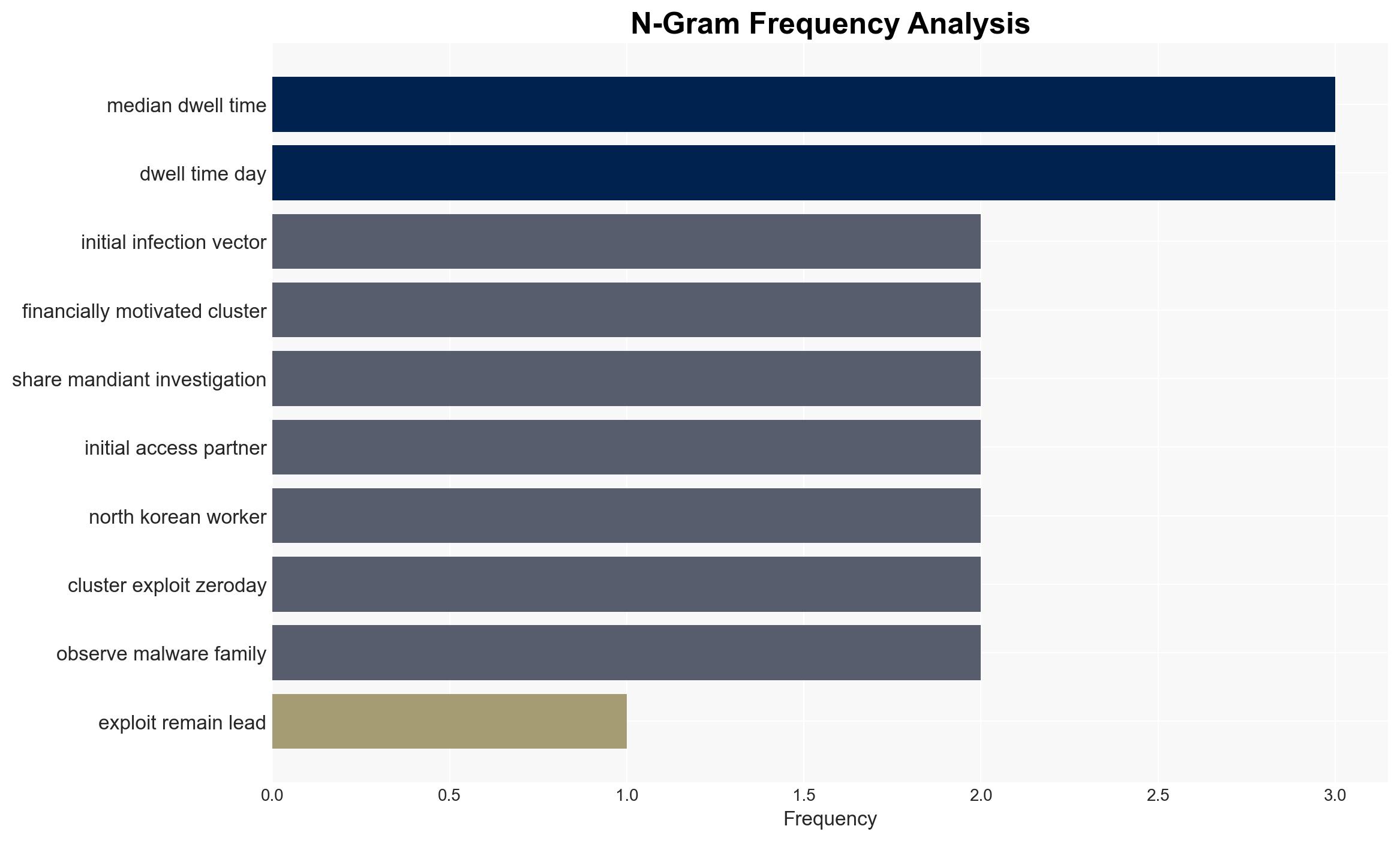
The Mandiant M-Trends 2026 report highlights a significant evolution in cyber threat tactics, with a rapid decrease in the time between initial access and hand-off to secondary threat actors. This shift is primarily affecting organizations’ cybersecurity postures, requiring immediate adaptation in detection and response strategies. The most likely hypothesis is that threat actors are optimizing their operations to evade detection, with moderate confidence in this assessment due to the consistent data trends observed.
2. Competing Hypotheses
- Hypothesis A: Threat actors are increasingly efficient, reducing hand-off times to evade detection and maximize impact. This is supported by the reported decrease in hand-off time from eight hours to 22 seconds and the strategic targeting of infrastructure vulnerabilities. Key uncertainties include the full extent of collaboration between threat groups and their operational capabilities.
- Hypothesis B: The observed rapid hand-offs are a temporary anomaly due to specific high-profile campaigns or advanced threat actors. While this could explain the sudden change, it is contradicted by the consistent trend across multiple investigations and the broader adoption of division-of-labor models.
- Assessment: Hypothesis A is currently better supported due to the consistent pattern of reduced hand-off times and the strategic targeting of critical infrastructure. Indicators such as continued rapid hand-offs and increased targeting of backup systems would further support this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Threat actors prioritize efficiency and stealth; the division-of-labor model is sustainable; current detection methods are insufficient against rapid hand-offs.
- Information Gaps: Detailed methodologies of initial access partners; specific motivations behind the shift in tactics; comprehensive data on the effectiveness of current defensive measures.
- Bias & Deception Risks: Potential over-reliance on Mandiant’s data; confirmation bias towards efficiency-driven threat actor behavior; possible deception in reported threat actor capabilities.
4. Implications and Strategic Risks
The evolution in cyber threat tactics could lead to increased vulnerabilities across sectors, necessitating a reevaluation of cybersecurity strategies. This development may interact with broader geopolitical tensions and influence national security policies.
- Political / Geopolitical: Potential for increased state-sponsored cyber operations leveraging these tactics, escalating international tensions.
- Security / Counter-Terrorism: Enhanced threat landscape with faster operational tempos, challenging existing countermeasures.
- Cyber / Information Space: Increased sophistication in cyber operations, requiring advanced detection and response capabilities.
- Economic / Social: Potential economic disruptions from successful cyber attacks, impacting public trust and social stability.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring for rapid hand-offs, update incident response protocols, and conduct targeted threat intelligence briefings.
- Medium-Term Posture (1–12 months): Develop partnerships for information sharing, invest in advanced detection technologies, and strengthen cybersecurity frameworks.
- Scenario Outlook:
- Best: Organizations adapt quickly, reducing successful attacks.
- Worst: Threat actors exploit the gap, leading to widespread disruptions.
- Most-Likely: Gradual improvement in defenses, with intermittent successful breaches.
6. Key Individuals and Entities
- UNC6040
- UNC3944
- UNC1543
- UNC2165
- ShinyHunters
- Scattered Spider
- Evil Corp
7. Thematic Tags
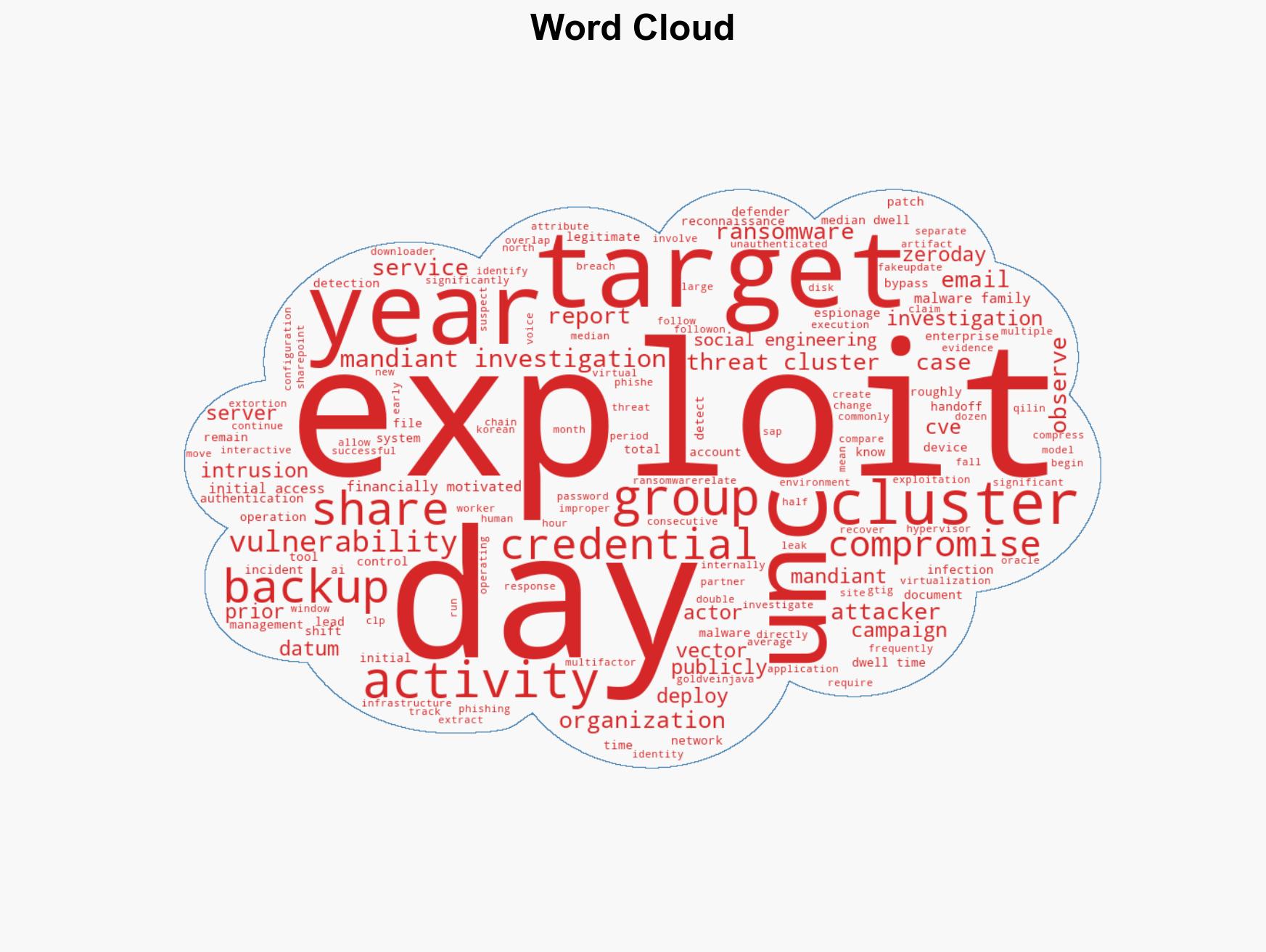
cybersecurity, threat intelligence, cyber operations, division-of-labor, ransomware, incident response, social engineering
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us