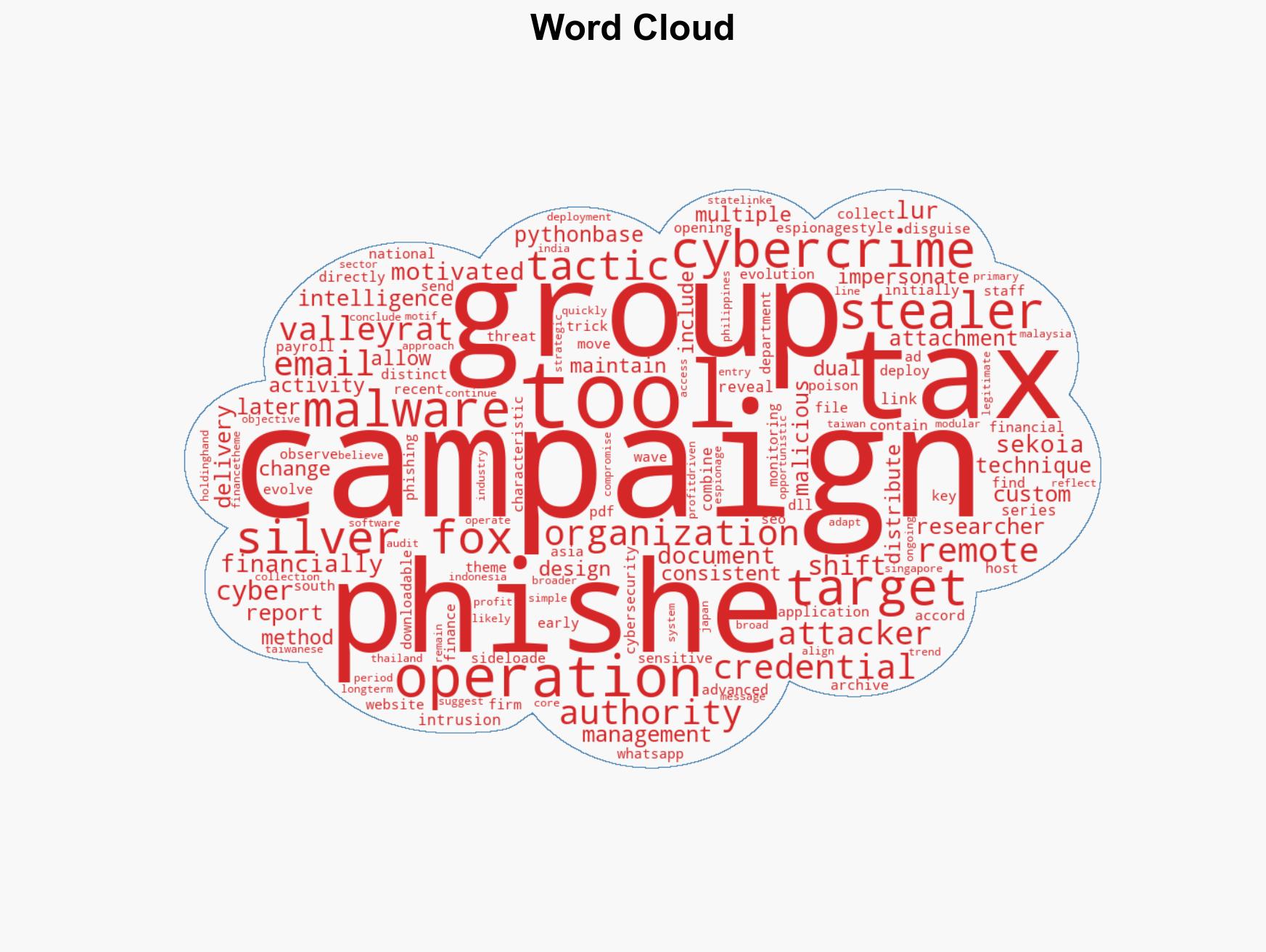
Silver Fox Cyber Operations Evolve to Combine Espionage and Financial Cybercrime Tactics
Published on: 2026-03-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Silver Fox Cyber Campaigns Show Shift Toward Dual Espionage
1. BLUF (Bottom Line Up Front)
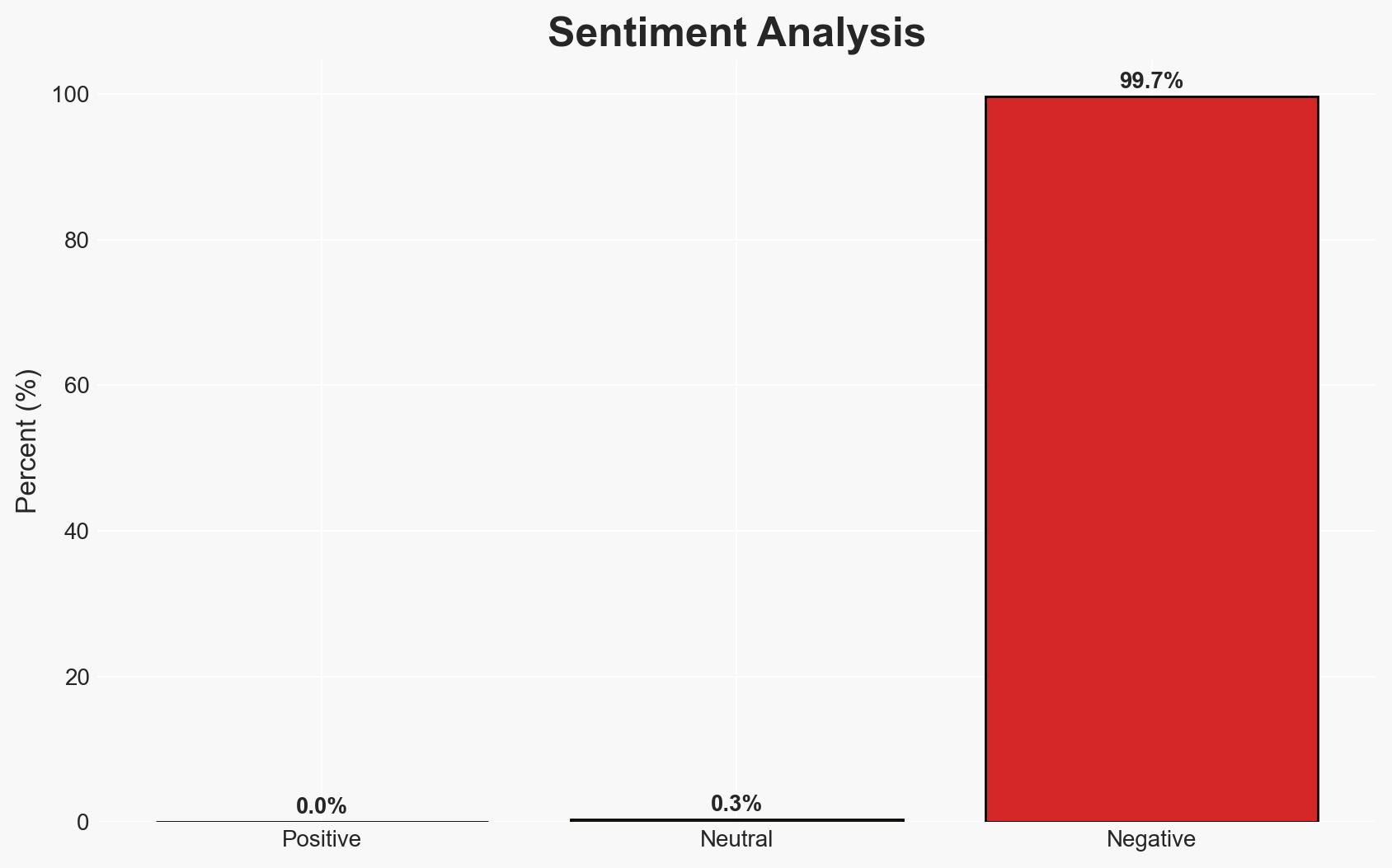
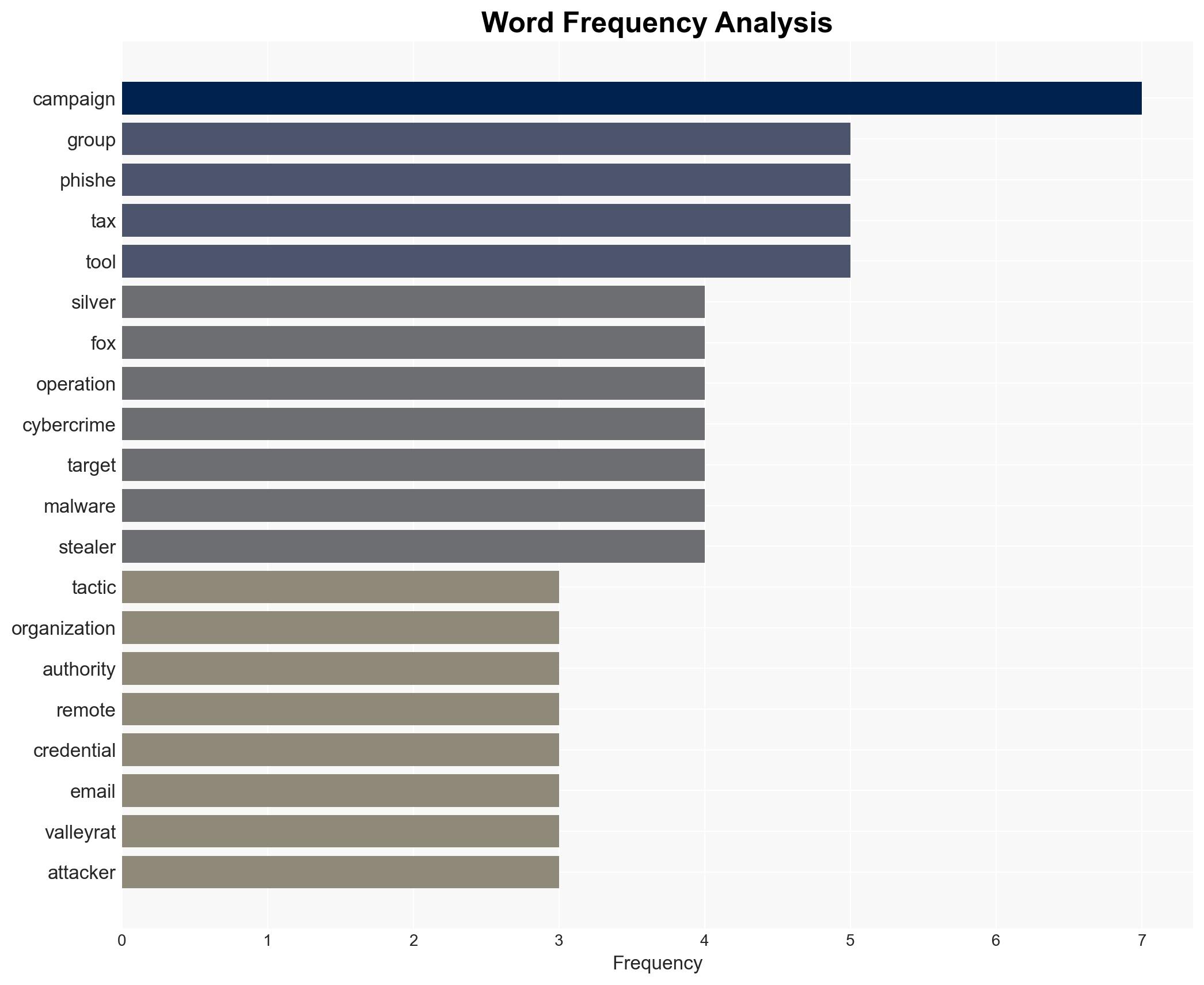
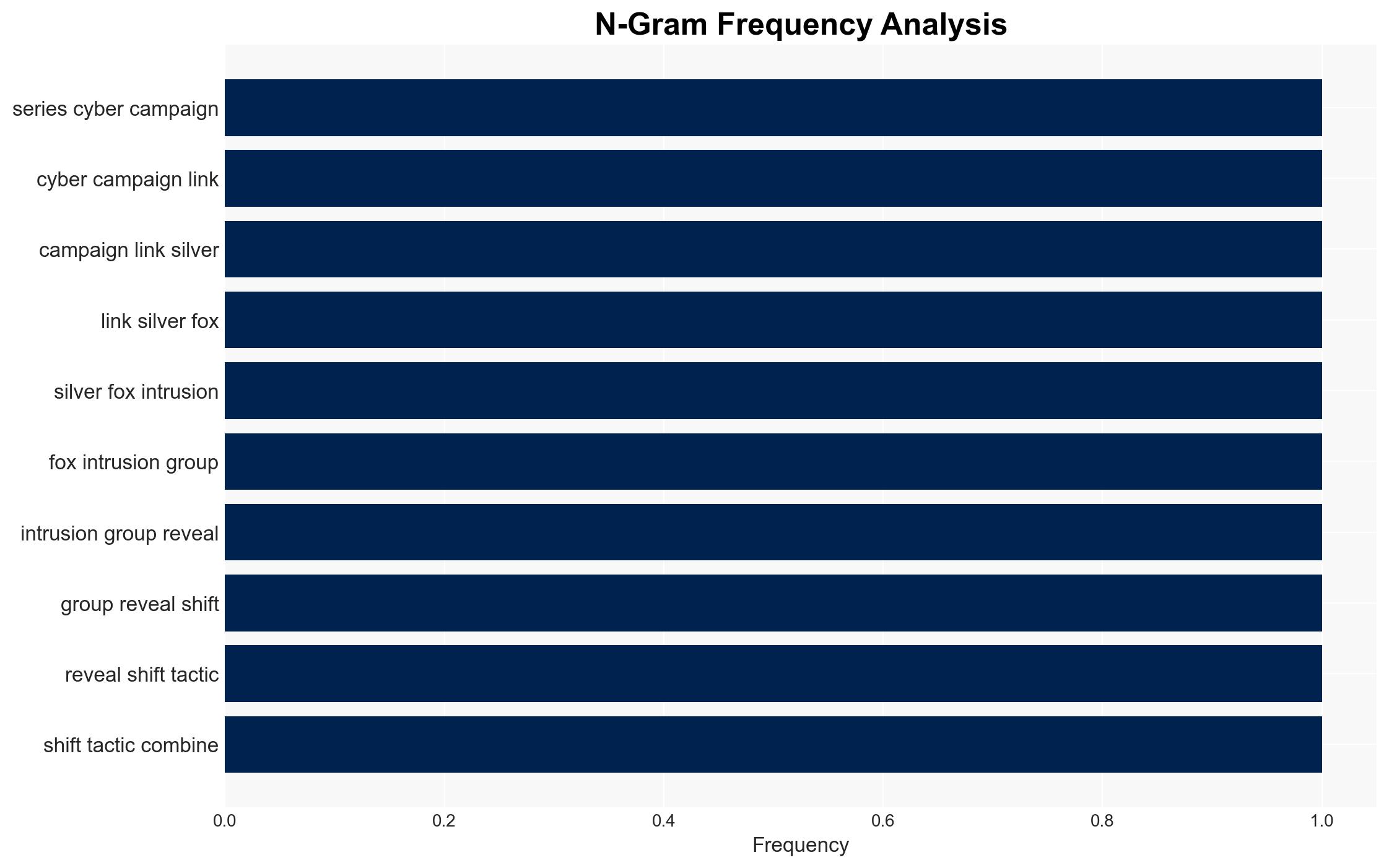
The Silver Fox intrusion group has shifted its cyber tactics between 2025 and 2026, blending espionage with financially motivated cybercrime, targeting organizations across South Asia. This dual approach complicates attribution and response strategies, affecting regional security and economic stability. Overall, there is moderate confidence in this assessment due to observed patterns and tool usage.
2. Competing Hypotheses
- Hypothesis A: Silver Fox is primarily a state-sponsored group using cybercrime to fund espionage activities. This is supported by the strategic targeting of Taiwanese organizations during tax audits, suggesting intelligence collection motives. However, the financial crime aspect could be a cover or secondary objective.
- Hypothesis B: Silver Fox is an independent cybercrime group that opportunistically engages in espionage when it aligns with financial objectives. The use of simple credential stealers and legitimate remote management tools supports a profit-driven motive, but the targeted nature of some campaigns suggests a more complex agenda.
- Assessment: Hypothesis A is currently better supported due to the alignment of certain campaigns with geopolitical interests, particularly in Taiwan. Key indicators that could shift this judgment include evidence of direct state sponsorship or a shift in targeting patterns.
3. Key Assumptions and Red Flags
- Assumptions: Silver Fox has the capability to conduct both espionage and cybercrime; the group has access to resources for developing custom malware; regional geopolitical tensions influence cyber activities.
- Information Gaps: Lack of direct attribution to a specific state actor; insufficient data on the group’s internal structure and decision-making processes.
- Bias & Deception Risks: Potential bias in source reporting due to reliance on cybersecurity firm analysis; risk of deception through false-flag operations by Silver Fox to obscure true motives.
4. Implications and Strategic Risks
The evolution of Silver Fox’s tactics could lead to increased regional instability and complicate international cyber norms. The blending of espionage and cybercrime blurs traditional response frameworks.
- Political / Geopolitical: Escalation of cyber tensions in South Asia, particularly affecting Taiwan’s geopolitical stance.
- Security / Counter-Terrorism: Increased threat to national security infrastructures and potential for cross-border cyber incidents.
- Cyber / Information Space: Enhanced sophistication in cyber operations may lead to more widespread adoption of similar tactics by other groups.
- Economic / Social: Potential disruption to financial sectors and erosion of trust in digital communications and transactions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of phishing campaigns and enhance cybersecurity awareness in targeted sectors; collaborate with regional partners for intelligence sharing.
- Medium-Term Posture (1–12 months): Develop resilience measures against dual-purpose cyber threats; strengthen public-private partnerships to improve threat detection and response.
- Scenario Outlook:
- Best: Successful international cooperation mitigates threats, reducing Silver Fox’s operational impact.
- Worst: Escalation of cyber activities leads to significant geopolitical conflict and economic disruption.
- Most-Likely: Continued dual-purpose operations with periodic spikes in activity aligned with geopolitical events.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cyber-espionage, cybercrime, South Asia, dual-use operations, geopolitical tensions, threat intelligence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us