A third of the most exploited vulnerabilities have persisted for over ten years.
Published on: 2026-03-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: 32 of top-exploited vulnerabilities are over a decade old
1. BLUF (Bottom Line Up Front)
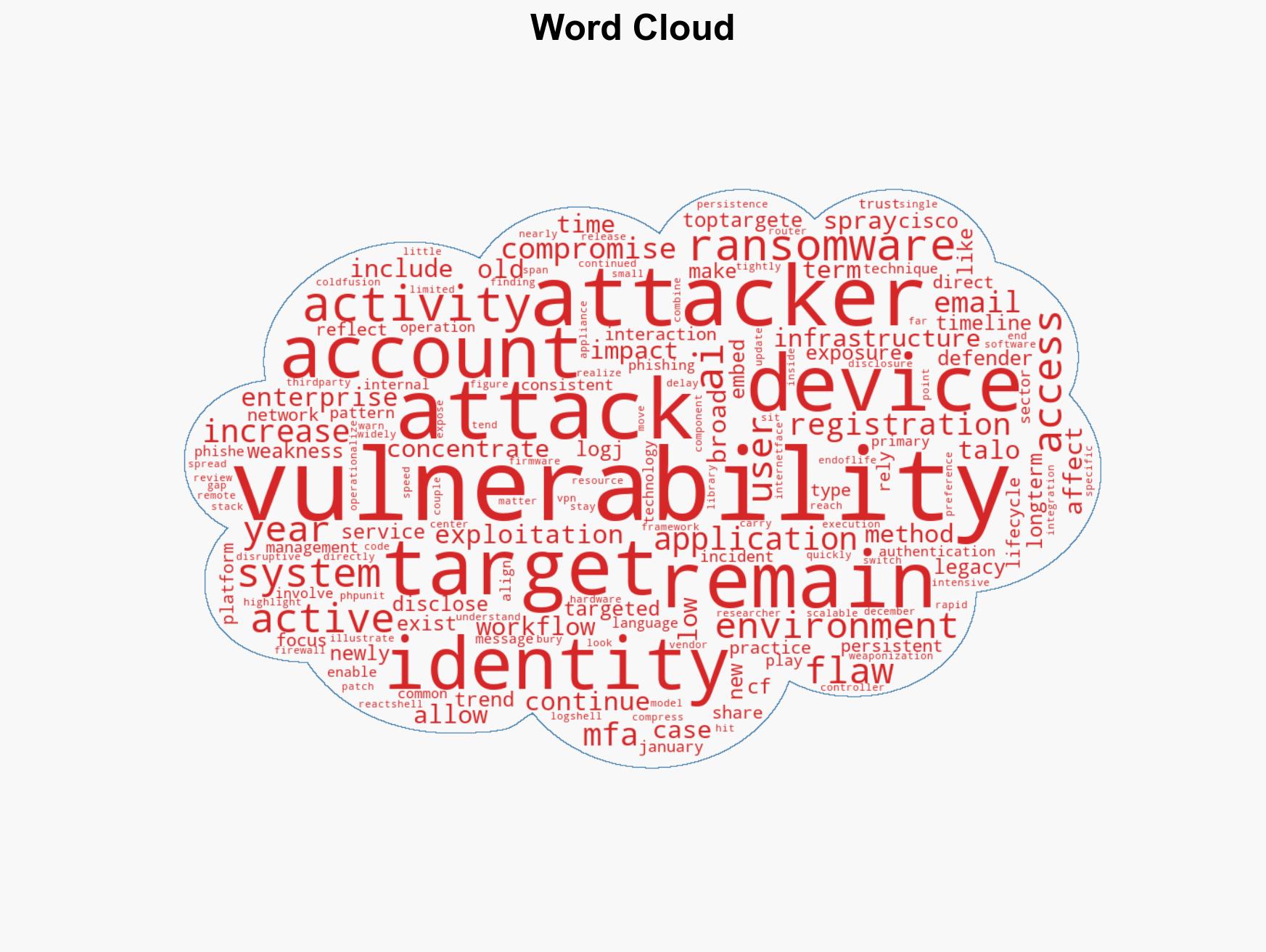
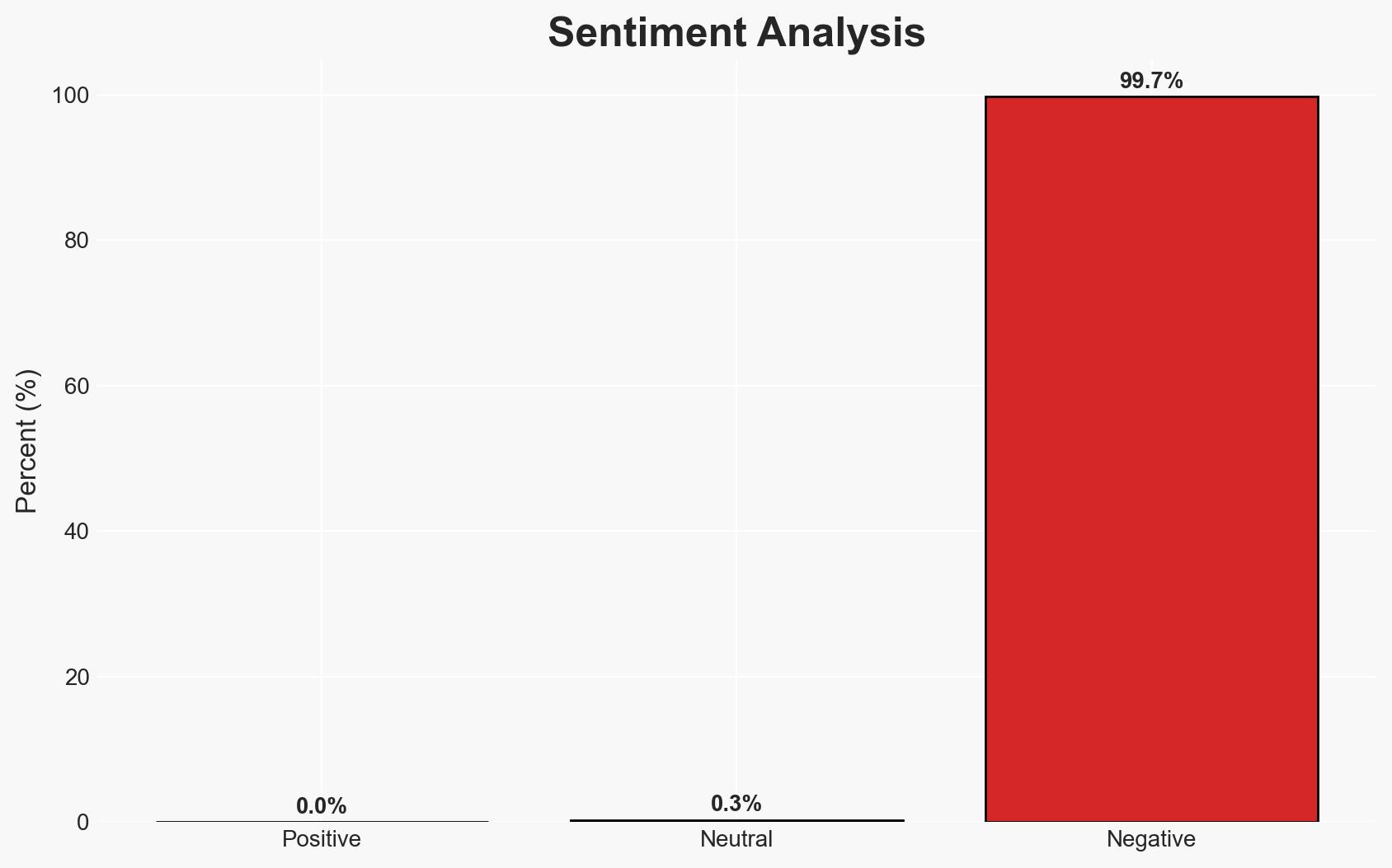
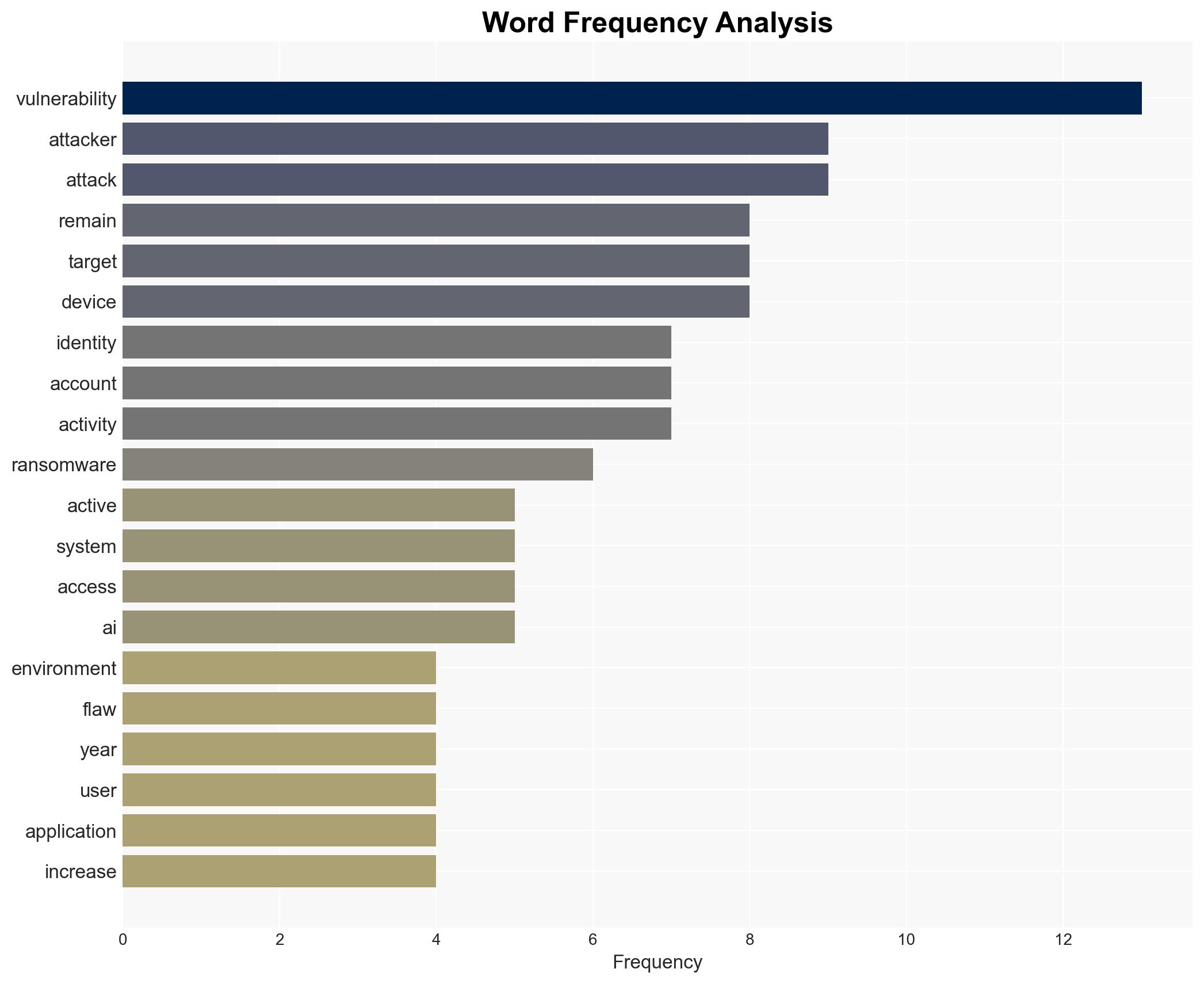
The persistence of decade-old vulnerabilities in enterprise systems poses a significant security risk, with attackers rapidly exploiting both new and old flaws. This trend highlights a critical gap in patch management and system updates, affecting a wide range of sectors, particularly those with legacy systems. Overall confidence in this assessment is moderate, given the consistent patterns observed in exploitation timelines.
2. Competing Hypotheses
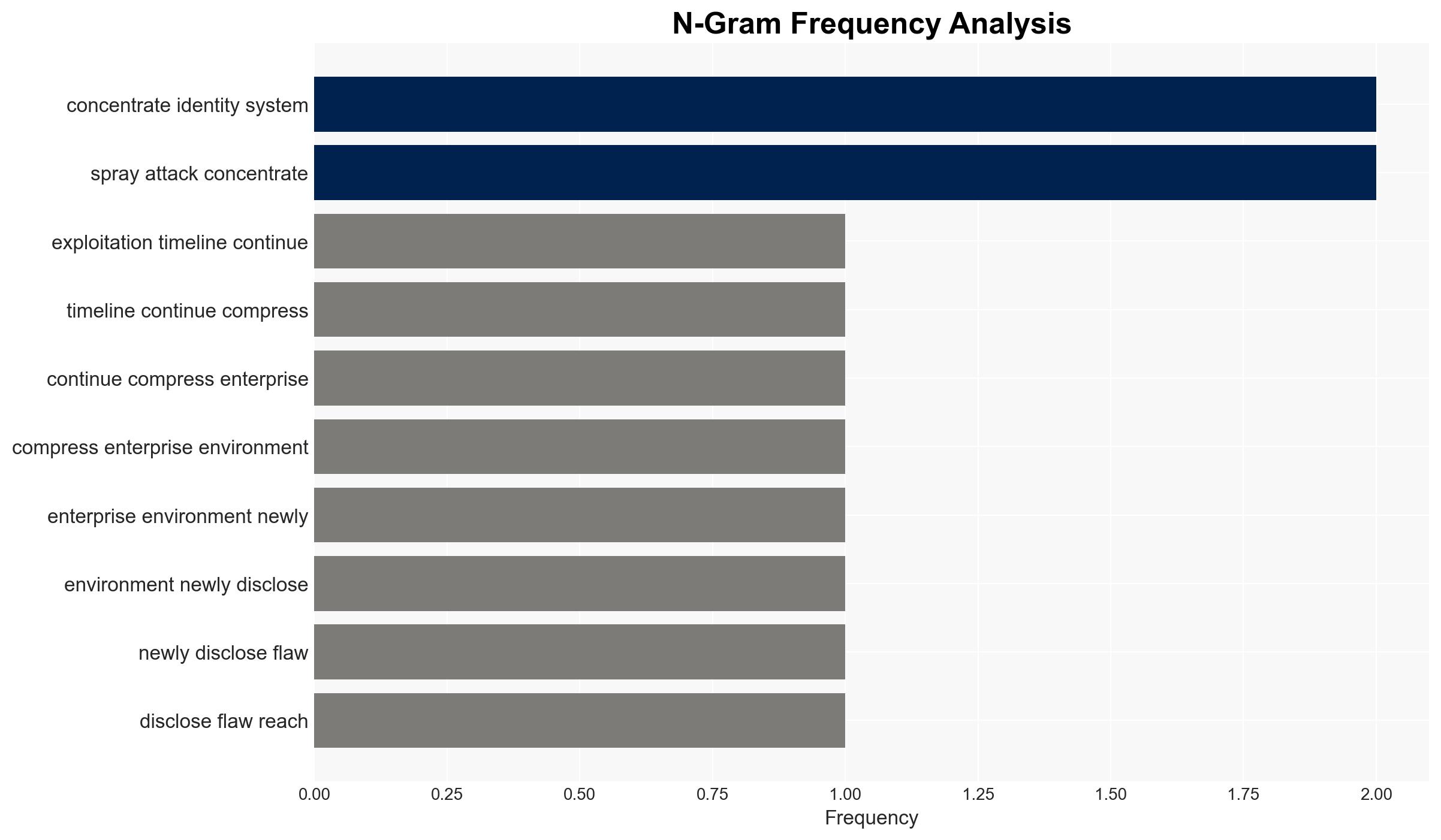
- Hypothesis A: Attackers prioritize older vulnerabilities because they are deeply embedded in legacy systems, making them difficult to patch and thus more attractive targets. This is supported by the continued exploitation of vulnerabilities like Log4Shell and the high percentage of end-of-life devices affected. However, the rapid exploitation of new vulnerabilities suggests attackers are opportunistic rather than solely reliant on older flaws.
- Hypothesis B: The rapid weaponization of new vulnerabilities indicates that attackers are primarily focused on exploiting the latest flaws to maximize impact before patches are widely applied. The quick targeting of React2Shell supports this view, though it does not fully explain the sustained focus on older vulnerabilities.
- Assessment: Hypothesis A is currently better supported due to the documented persistence of older vulnerabilities in critical systems and the challenges associated with patching legacy infrastructure. Indicators such as increased patching efficiency or a shift in attacker focus could alter this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Enterprises have significant legacy systems that are difficult to update; attackers have the capability to exploit both new and old vulnerabilities; patching practices are inconsistent across industries.
- Information Gaps: Detailed data on specific industries’ patching timelines and practices; comprehensive analysis of the economic impact of these vulnerabilities.
- Bias & Deception Risks: Potential bias in reporting from cybersecurity firms with vested interests; attackers may intentionally mislead about their methods and targets to obfuscate true capabilities.
4. Implications and Strategic Risks
The ongoing exploitation of both new and old vulnerabilities could lead to increased cyber incidents, affecting national security and economic stability. The persistence of these vulnerabilities suggests systemic issues in cybersecurity practices that could be exploited by state and non-state actors.
- Political / Geopolitical: Potential for increased cyber tensions between states as vulnerabilities are exploited for espionage or sabotage.
- Security / Counter-Terrorism: Enhanced risk of cyber-attacks on critical infrastructure, which could be leveraged by terrorist organizations.
- Cyber / Information Space: Increased activity in cybercrime and espionage, with potential for misinformation campaigns exploiting these vulnerabilities.
- Economic / Social: Potential disruptions in industries reliant on legacy systems, leading to economic losses and social unrest if critical services are impacted.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive audit of systems to identify and prioritize patching of known vulnerabilities; enhance monitoring for signs of exploitation.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms to improve threat intelligence sharing; invest in upgrading legacy systems and improving patch management processes.
- Scenario Outlook:
- Best: Improved patch management reduces exploitation rates, with increased collaboration leading to better threat mitigation.
- Worst: Continued exploitation of vulnerabilities leads to significant cyber incidents affecting critical infrastructure and economic stability.
- Most-Likely: A mixed scenario where some vulnerabilities are addressed, but others persist due to resource constraints and systemic challenges.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, vulnerabilities, patch management, legacy systems, cyber exploitation, threat intelligence, ransomware
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us