Dell Enhances Cybersecurity with Quantum-Resilient Solutions and AI-Driven Threat Detection Capabilities
Published on: 2026-03-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Dell expands security stack with quantum-ready protections and AI threat detection
1. BLUF (Bottom Line Up Front)
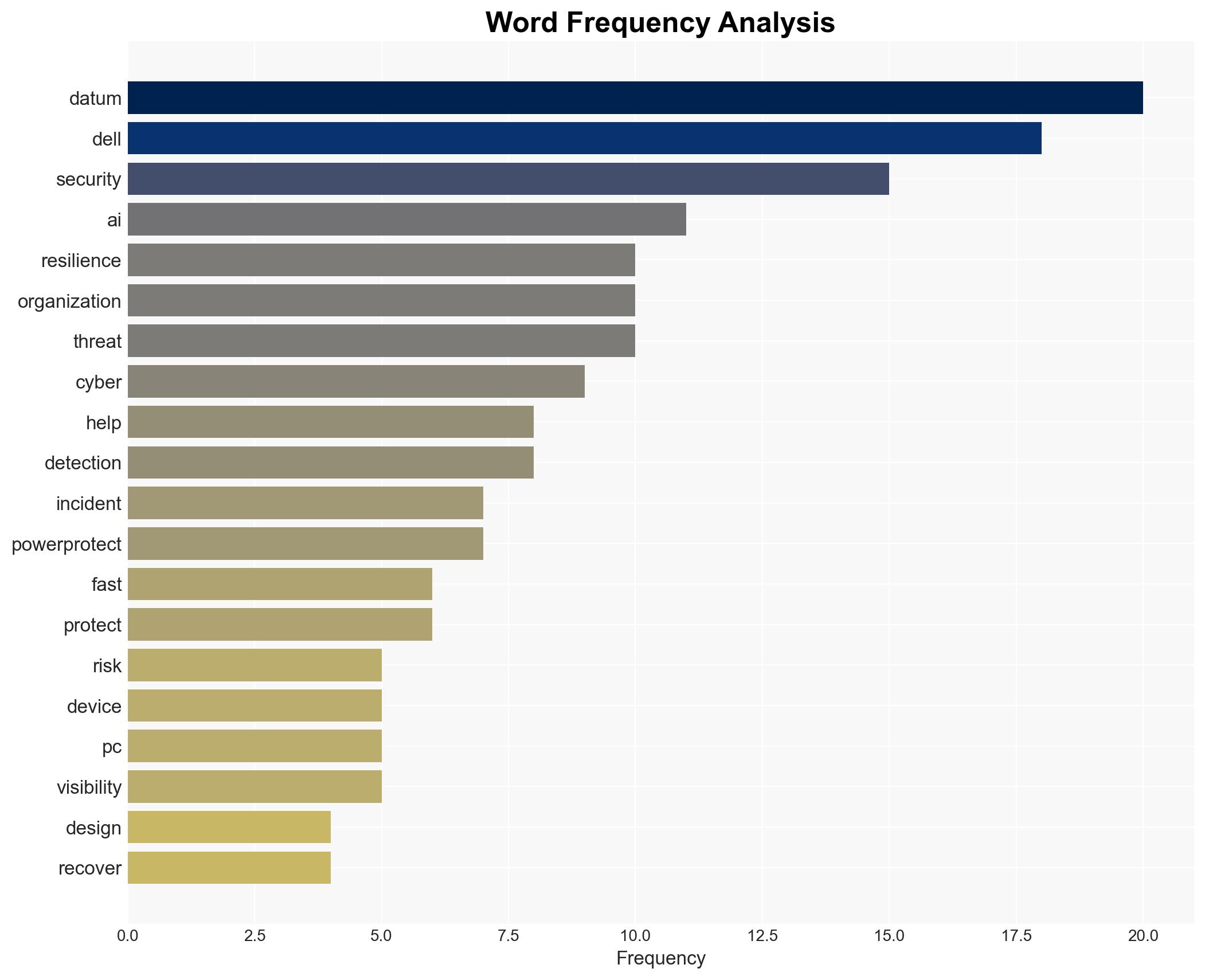
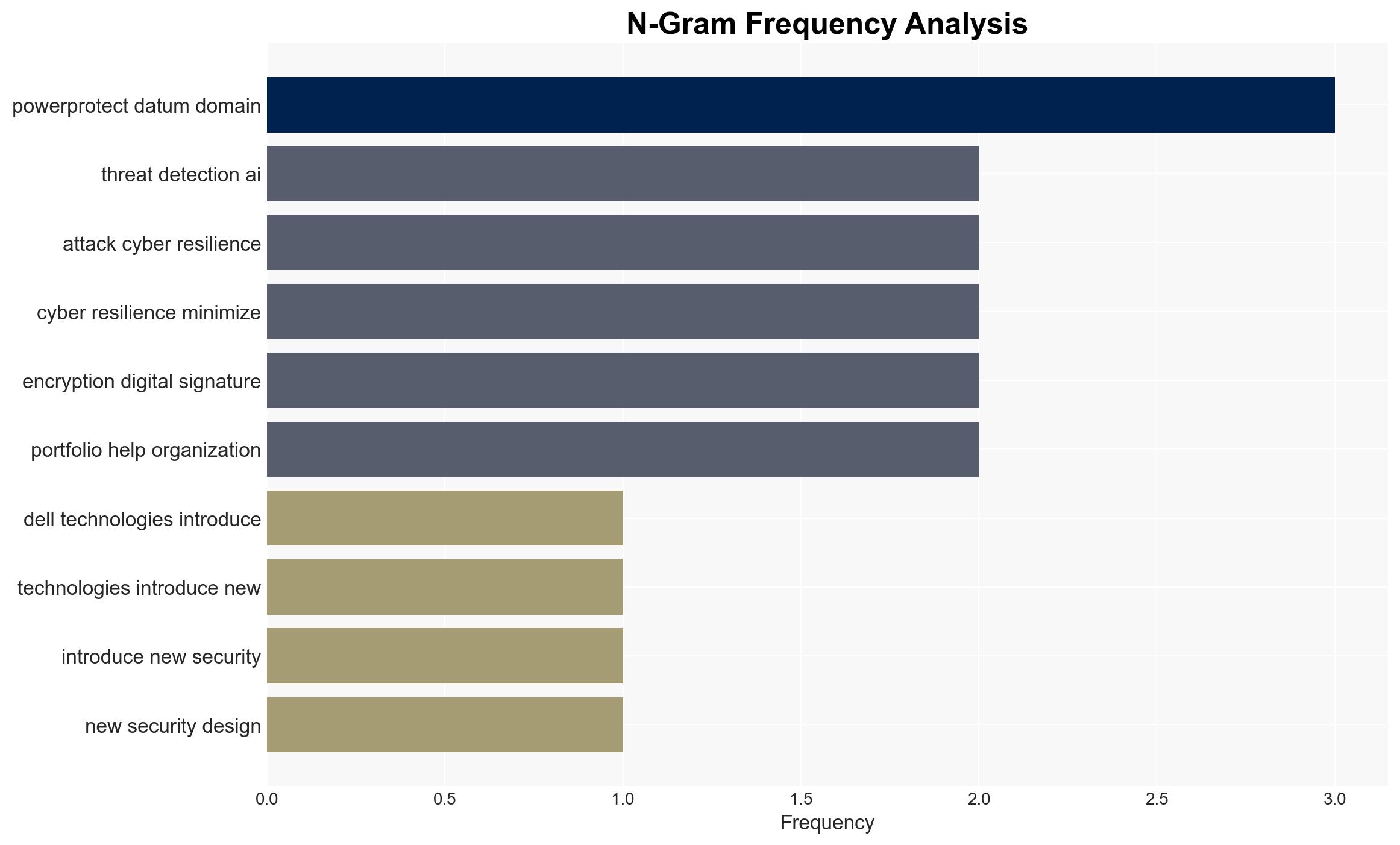
Dell Technologies is enhancing its security offerings to address emerging threats from quantum computing and AI, focusing on hardening device foundations and improving cyber resilience. This development primarily affects organizations reliant on Dell’s technology stack, with moderate confidence in the effectiveness of these measures given the evolving nature of the threats. The initiative is likely to influence the broader cybersecurity landscape by setting new standards for quantum-ready protections.
2. Competing Hypotheses
- Hypothesis A: Dell’s enhancements will significantly improve organizational defenses against quantum and AI-driven threats. Supporting evidence includes the introduction of quantum-ready security features and AI-powered threat detection. However, the effectiveness of these measures against future, unknown threats remains uncertain.
- Hypothesis B: Dell’s enhancements may not substantially alter the threat landscape due to the rapid evolution of quantum and AI technologies potentially outpacing current defenses. The lack of real-world testing against advanced quantum threats contradicts the anticipated effectiveness.
- Assessment: Hypothesis A is currently better supported due to Dell’s proactive approach and alignment with post-quantum standards. However, ongoing advancements in quantum computing could shift this judgment if Dell’s measures prove insufficient against emerging threats.
3. Key Assumptions and Red Flags
- Assumptions: Dell’s security features are assumed to be effective against anticipated quantum threats; AI threat detection will enhance incident response; organizations will adopt these technologies promptly.
- Information Gaps: Lack of detailed performance data on Dell’s new security features against advanced quantum attacks; unclear adoption rates among key industry sectors.
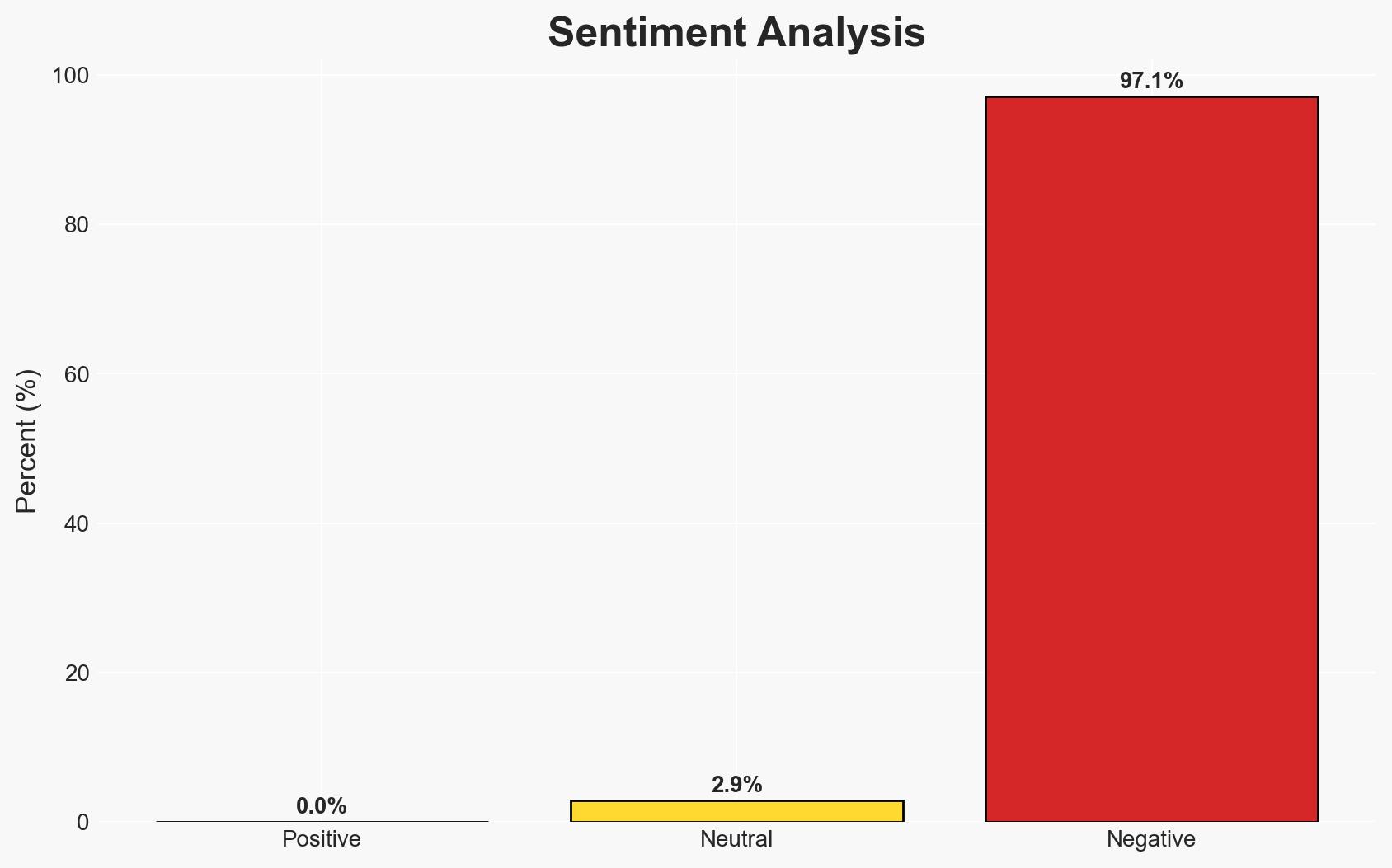
- Bias & Deception Risks: Potential over-reliance on vendor-provided data; marketing bias in portraying the effectiveness of new security measures without independent verification.
4. Implications and Strategic Risks
The introduction of quantum-ready protections by Dell could set a precedent in the cybersecurity industry, influencing competitors and regulatory standards. However, the rapid evolution of quantum computing poses a strategic risk if defenses do not keep pace.
- Political / Geopolitical: Potential for increased regulatory scrutiny on quantum computing standards; influence on international cybersecurity norms.
- Security / Counter-Terrorism: Enhanced defenses could reduce vulnerabilities to state-sponsored cyber operations and terrorism-related cyber threats.
- Cyber / Information Space: Shift towards quantum-resistant encryption may alter cyber defense strategies globally; increased focus on AI-driven threat detection.
- Economic / Social: Organizations may face increased costs for upgrading to quantum-ready technologies, impacting budget allocations and strategic planning.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor adoption rates of Dell’s new security features; engage with industry partners to assess the effectiveness of quantum-ready protections.
- Medium-Term Posture (1–12 months): Develop partnerships for independent testing of quantum-resistant technologies; enhance organizational cyber resilience frameworks in line with emerging standards.
- Scenario Outlook:
- Best: Widespread adoption of quantum-ready protections significantly reduces cyber threats.
- Worst: Quantum threats evolve faster than defenses, leading to increased vulnerabilities.
- Most-Likely: Gradual improvement in defenses with ongoing adjustments to counter evolving threats.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
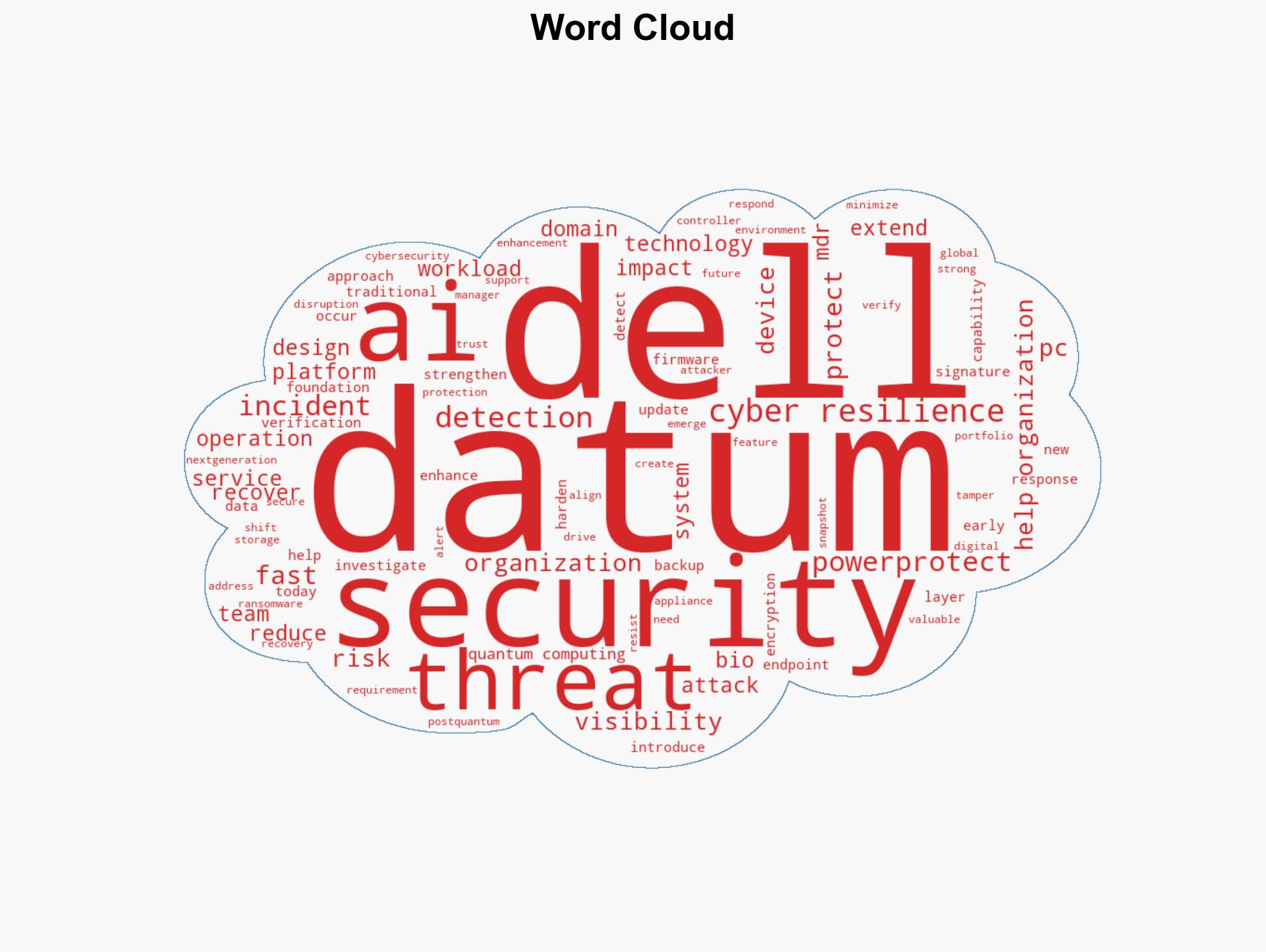
cybersecurity, quantum computing, AI threat detection, cyber resilience, encryption, technology adoption, cyber defense
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us