Poland’s cyberattacks surged in 2025, highlighted by a significant strike on its energy infrastructure
Published on: 2026-03-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
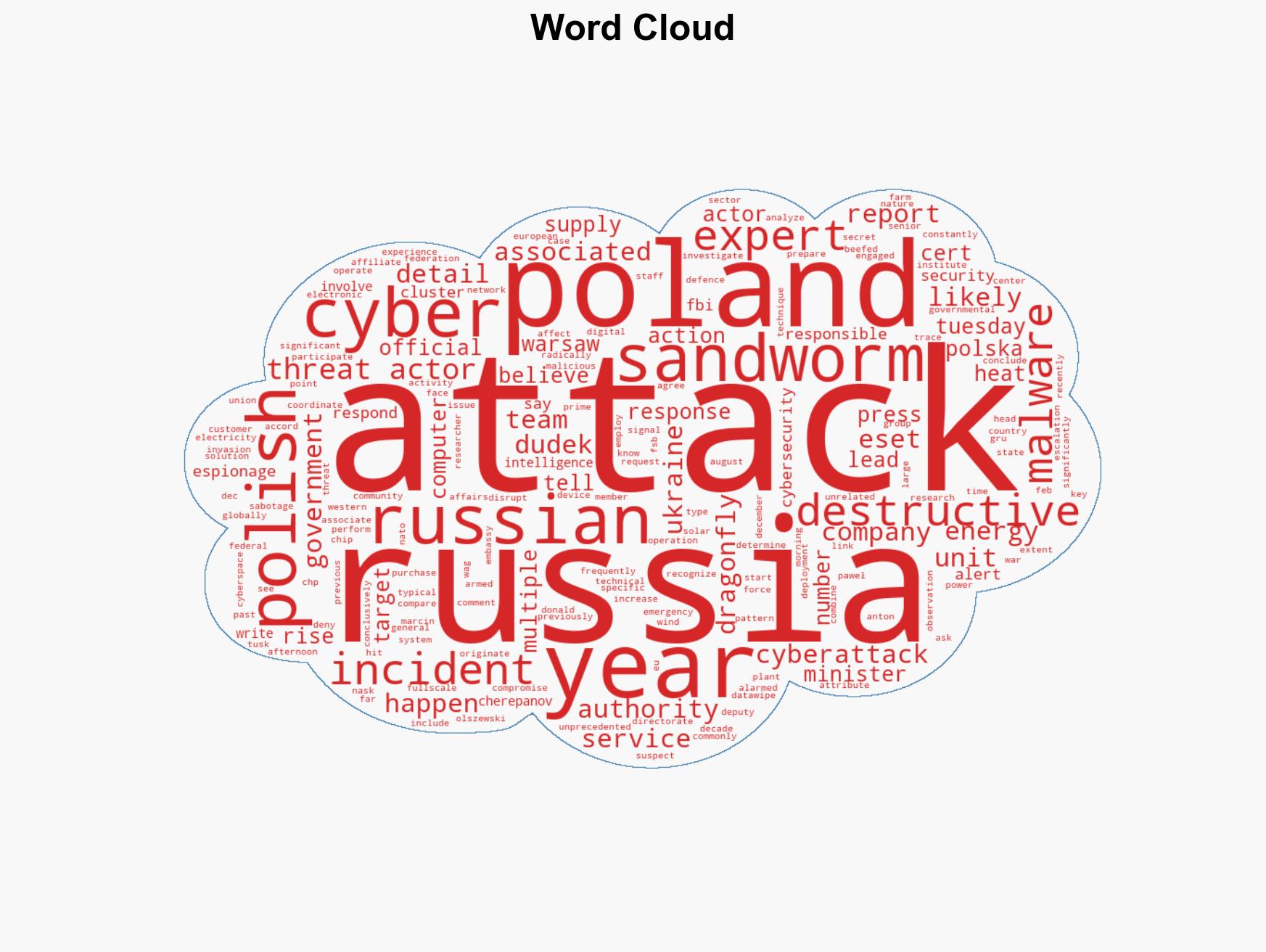
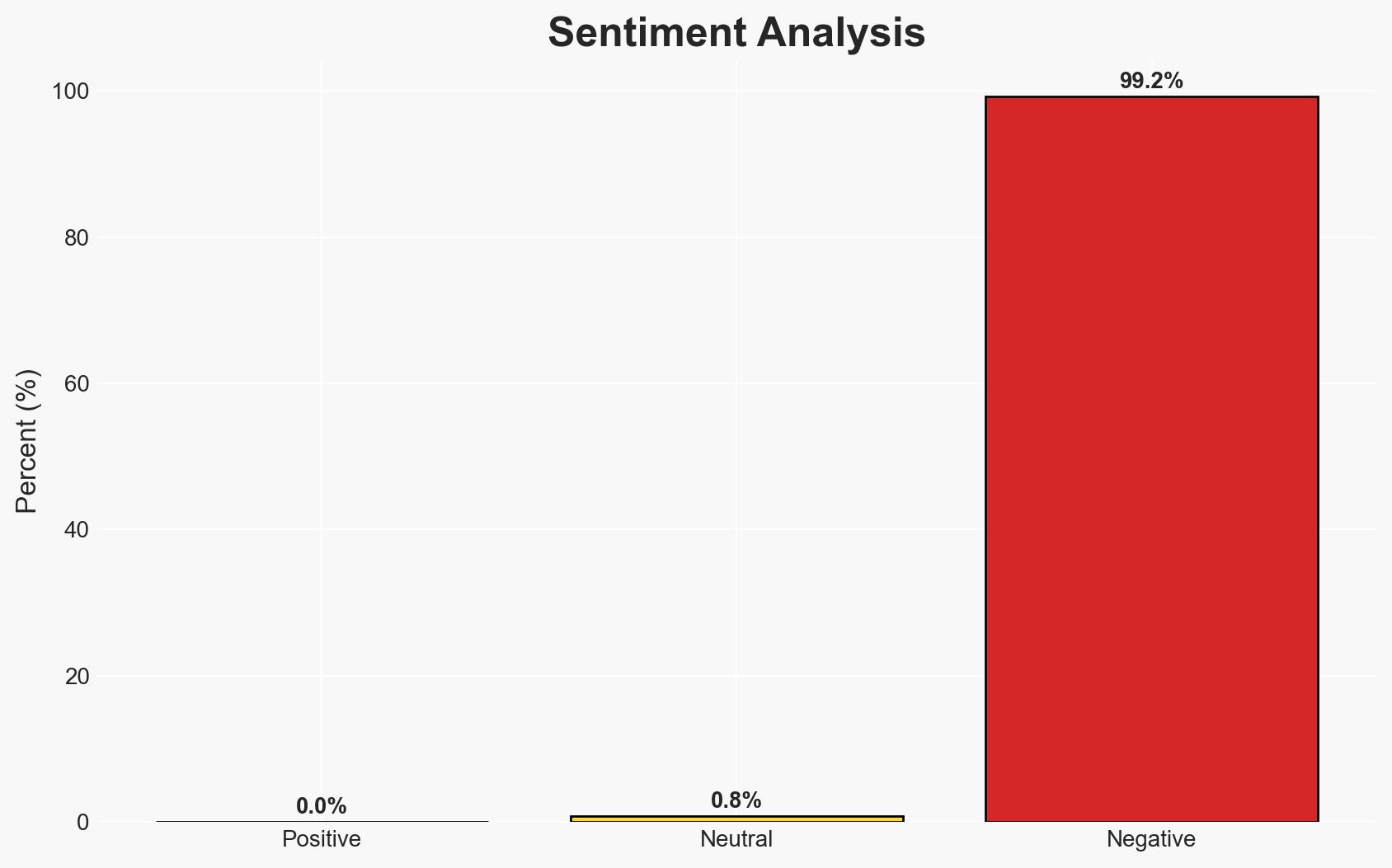
Intelligence Report: Poland faced a surge in cyberattacks in 2025 including a major assault on the energy sector
1. BLUF (Bottom Line Up Front)
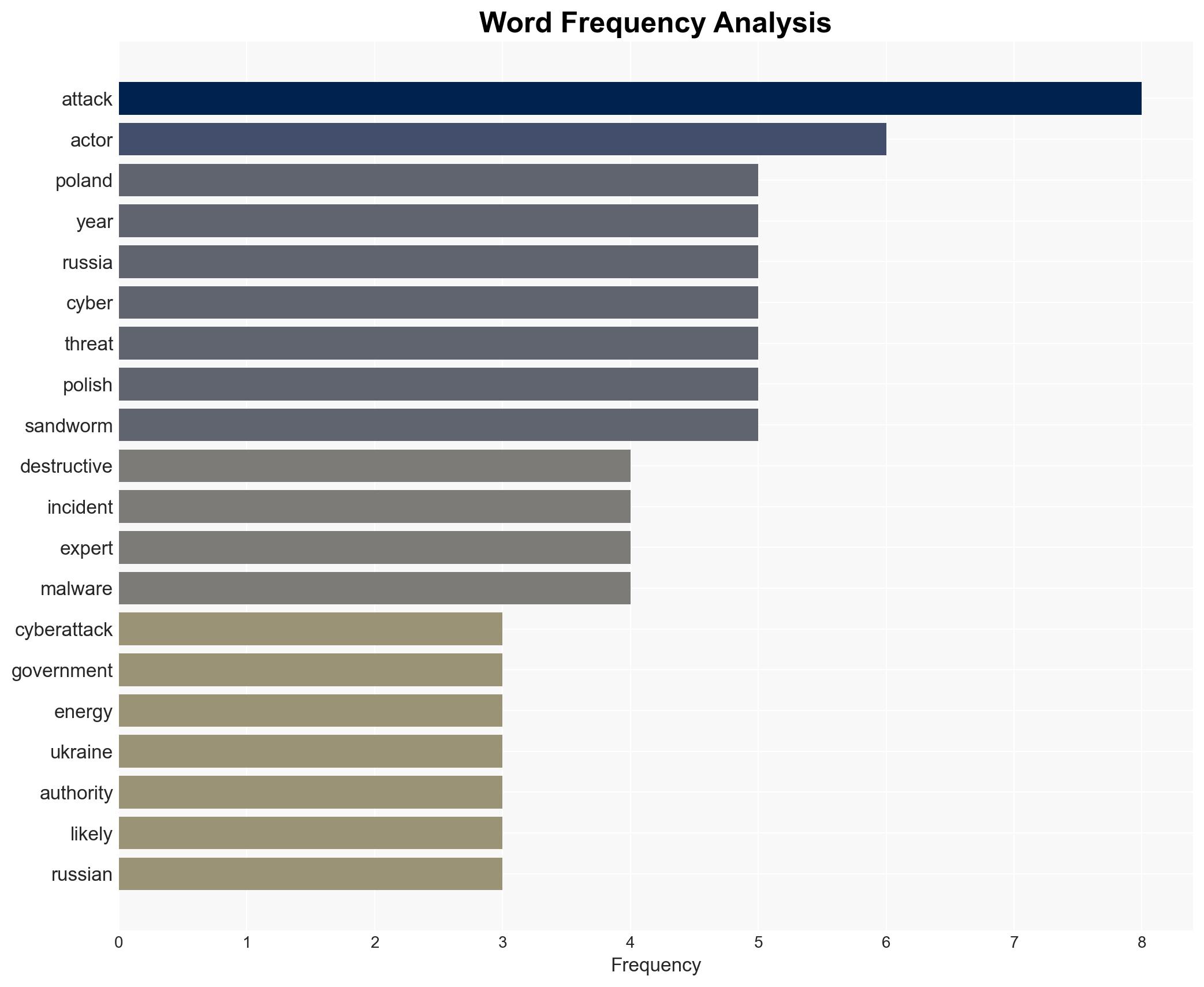
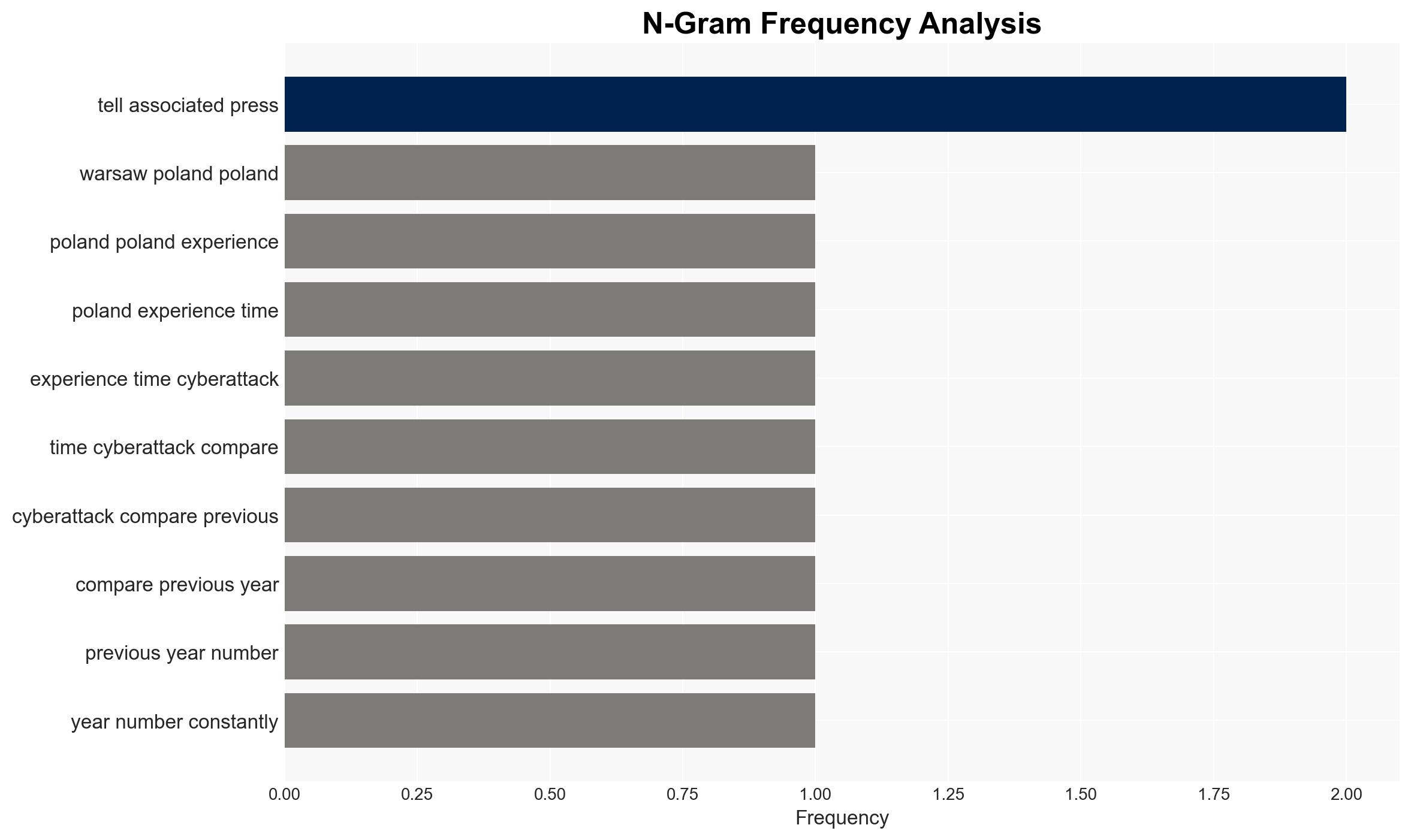
In 2025, Poland experienced a significant increase in cyberattacks, notably a destructive assault on its energy sector, suspected to originate from Russian state-linked actors. The attack did not disrupt electricity supply but marked an escalation in cyber aggression. This development poses a heightened threat to Poland’s national security and regional stability. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The cyberattacks on Poland’s energy sector were orchestrated by Russian state-linked actors, specifically the Dragonfly group, as part of a broader strategy to destabilize NATO and EU member states. Supporting evidence includes the identification of malware patterns linked to Russian cyber units and historical precedents of Russian cyber operations targeting critical infrastructure. However, the exact attribution remains uncertain due to the complex nature of cyber forensics.
- Hypothesis B: The attacks were conducted by non-state actors or independent cybercriminal groups using Russian tools and techniques to mimic state-sponsored operations, potentially for financial gain or to create geopolitical tension. This hypothesis is less supported due to the sophistication of the attack and the strategic targeting of Poland’s energy infrastructure, which aligns more closely with state-level objectives.
- Assessment: Hypothesis A is currently better supported due to the alignment of the attack’s characteristics with known Russian cyber capabilities and strategic interests. Indicators such as further similar attacks or additional intelligence linking the actors to Russian state entities could reinforce this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The cyberattack was strategically planned and executed with state-level resources; Poland’s cyber defenses are currently insufficient to deter such threats; Russian state actors have a vested interest in destabilizing EU and NATO countries.
- Information Gaps: Detailed technical analysis of the malware used; direct evidence linking the attack to Russian state actors; insights into Poland’s internal cybersecurity capabilities and response strategies.
- Bias & Deception Risks: Attribution bias towards Russia due to historical tensions; potential for misdirection by the attackers to obscure true origins; reliance on open-source intelligence which may be incomplete or manipulated.
4. Implications and Strategic Risks
This development could lead to increased geopolitical tensions between Poland and Russia, potentially drawing in NATO and EU responses. The persistent threat of cyberattacks may necessitate enhanced regional cybersecurity collaboration and investment.
- Political / Geopolitical: Potential for diplomatic confrontations and increased sanctions against Russia; strengthening of NATO’s cyber defense posture.
- Security / Counter-Terrorism: Heightened alert levels and resource allocation towards cyber defense; potential for retaliatory cyber operations.
- Cyber / Information Space: Increased focus on securing critical infrastructure; potential for misinformation campaigns exploiting the incident.
- Economic / Social: Possible economic impacts from increased cybersecurity spending; public concern over energy security and government response capabilities.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of critical infrastructure networks; engage with international cybersecurity partners for threat intelligence sharing; conduct a comprehensive review of current cyber defenses.
- Medium-Term Posture (1–12 months): Invest in cybersecurity infrastructure and workforce; develop public-private partnerships for cyber resilience; strengthen legal frameworks for cyber incident response.
- Scenario Outlook:
- Best Case: Strengthened defenses deter future attacks, leading to regional stability.
- Worst Case: Escalation of cyberattacks leads to significant infrastructure disruptions and geopolitical conflict.
- Most Likely: Continued cyber threats necessitate ongoing vigilance and international cooperation.
6. Key Individuals and Entities
- Paweł Olszewski, Deputy Minister of Digital Affairs
- Marcin Dudek, Head of CERT Polska
- Dragonfly Group, linked to FSB Center 16
- ESET, cybersecurity company
- Sandworm, cyber threat actor
7. Thematic Tags
cybersecurity, energy sector, Russia, NATO, cyber defense, information warfare, geopolitical tension
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us