FCC Blocks New Approvals for Foreign-Made Consumer Routers Citing National Security Concerns
Published on: 2026-03-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: US FCC Prohibits Approval of New Foreign-Made Consumer Routers
1. BLUF (Bottom Line Up Front)
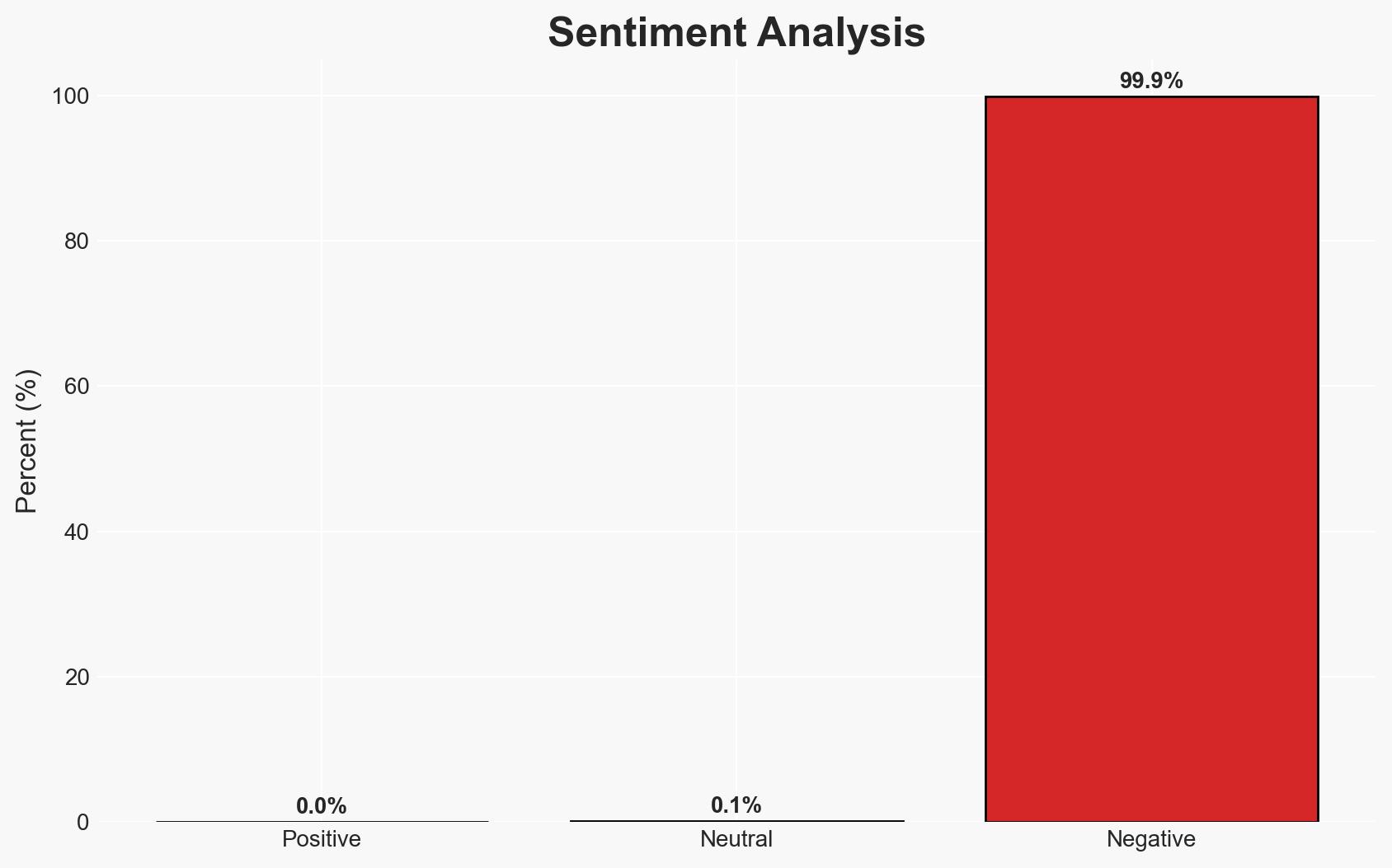
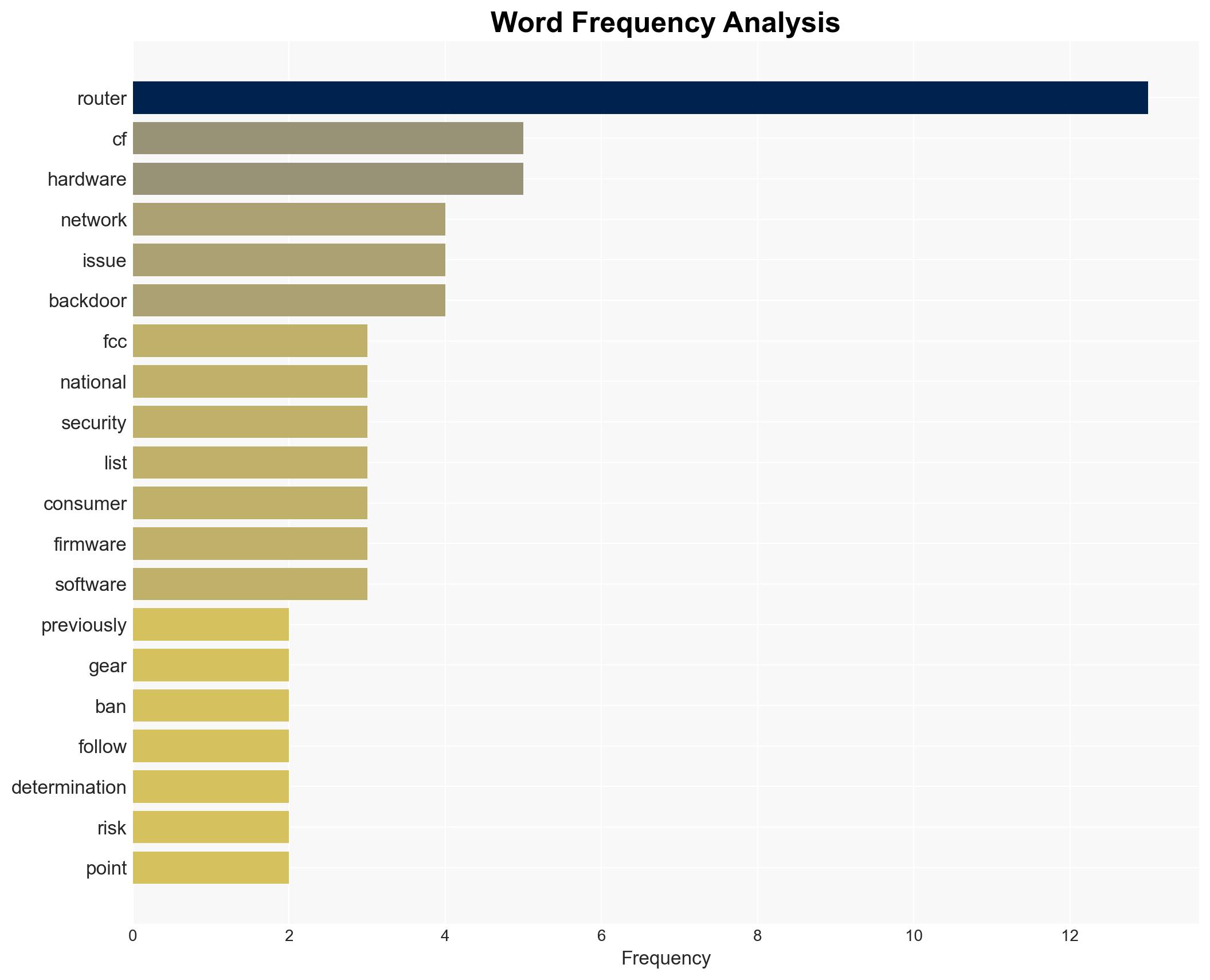
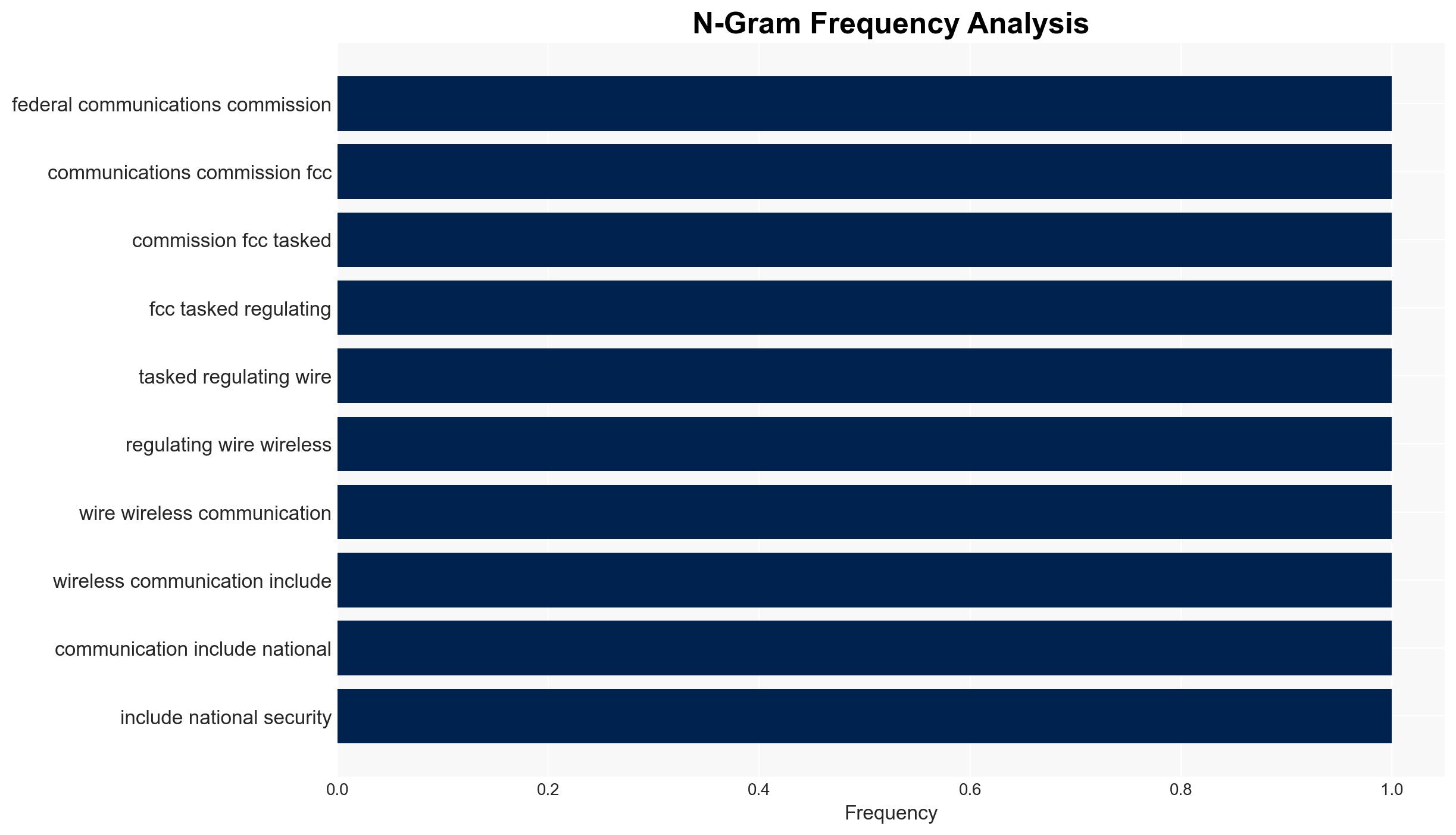
The US FCC’s decision to prohibit the approval of new foreign-made consumer routers is primarily driven by national security concerns over potential vulnerabilities. This move affects foreign manufacturers and could lead to increased domestic production demands. The most likely hypothesis is that this policy aims to mitigate risks associated with foreign supply chains. Overall confidence in this assessment is moderate, given the lack of specific implementation details and potential for geopolitical repercussions.
2. Competing Hypotheses
- Hypothesis A: The FCC’s prohibition is a strategic move to enhance national security by reducing reliance on foreign technology, which is perceived as vulnerable to cyber threats. Supporting evidence includes the interagency determination of unacceptable risks and historical precedence with Huawei. Contradicting evidence is the lack of specific details on how US-manufactured routers will be developed and secured.
- Hypothesis B: The prohibition is primarily an economic protectionist measure aimed at boosting domestic manufacturing under the guise of national security. This is supported by the implication of onshoring industrial bases. However, the focus on firmware vulnerabilities suggests genuine security concerns.
- Assessment: Hypothesis A is currently better supported due to the explicit national security rationale provided by the interagency body. Key indicators that could shift this judgment include the emergence of detailed economic incentives for domestic production or revelations of economic motivations behind the policy.
3. Key Assumptions and Red Flags
- Assumptions: The FCC’s actions are primarily motivated by security concerns; US-manufactured routers will inherently be more secure; foreign routers pose a significant risk.
- Information Gaps: Specific criteria for router approval, details on the transition phase, and the extent of required onshoring are unclear.
- Bias & Deception Risks: Potential confirmation bias in assessing foreign technology as inherently riskier; possible economic motivations masked as security concerns.
4. Implications and Strategic Risks
This development could lead to increased tensions with foreign technology providers and impact global supply chains. Over time, it may drive innovation in domestic manufacturing but also risks retaliatory measures from affected countries.
- Political / Geopolitical: Potential for strained US relations with countries whose manufacturers are affected, leading to diplomatic disputes.
- Security / Counter-Terrorism: Short-term increase in security as foreign vulnerabilities are reduced; long-term risk if domestic production fails to meet security standards.
- Cyber / Information Space: Shift in cyber threat landscape as focus moves to securing domestic supply chains; potential for increased cyber espionage targeting US manufacturers.
- Economic / Social: Possible economic boost from increased domestic production; risk of supply shortages or increased costs during transition.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor foreign government reactions and assess potential retaliatory measures; engage with domestic manufacturers to understand capacity and readiness.
- Medium-Term Posture (1–12 months): Develop partnerships with trusted allies for technology sharing; enhance domestic cybersecurity standards and capabilities.
- Scenario Outlook:
- Best: Successful transition to secure domestic router production, enhancing national security and economic growth.
- Worst: Supply chain disruptions and increased costs lead to economic strain and diplomatic conflicts.
- Most-Likely: Gradual adaptation with moderate economic and security improvements, but ongoing geopolitical tensions.
6. Key Individuals and Entities
- US Federal Communications Commission (FCC)
- Foreign router manufacturers (not specifically named)
- US domestic manufacturing sector (not specifically named)
7. Thematic Tags
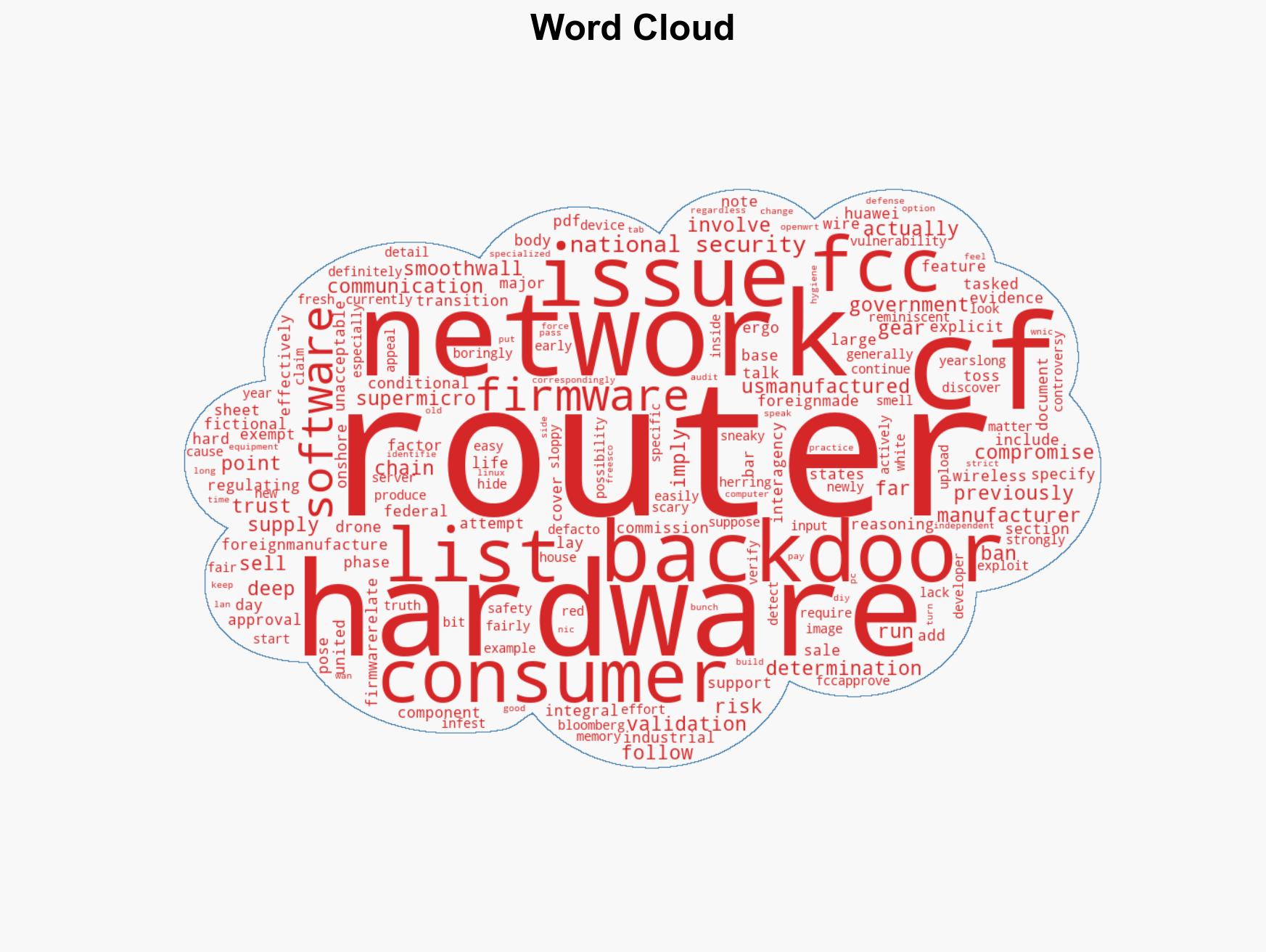
cybersecurity, national security, FCC regulation, supply chain security, cyber vulnerabilities, economic protectionism, US manufacturing, foreign relations
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us