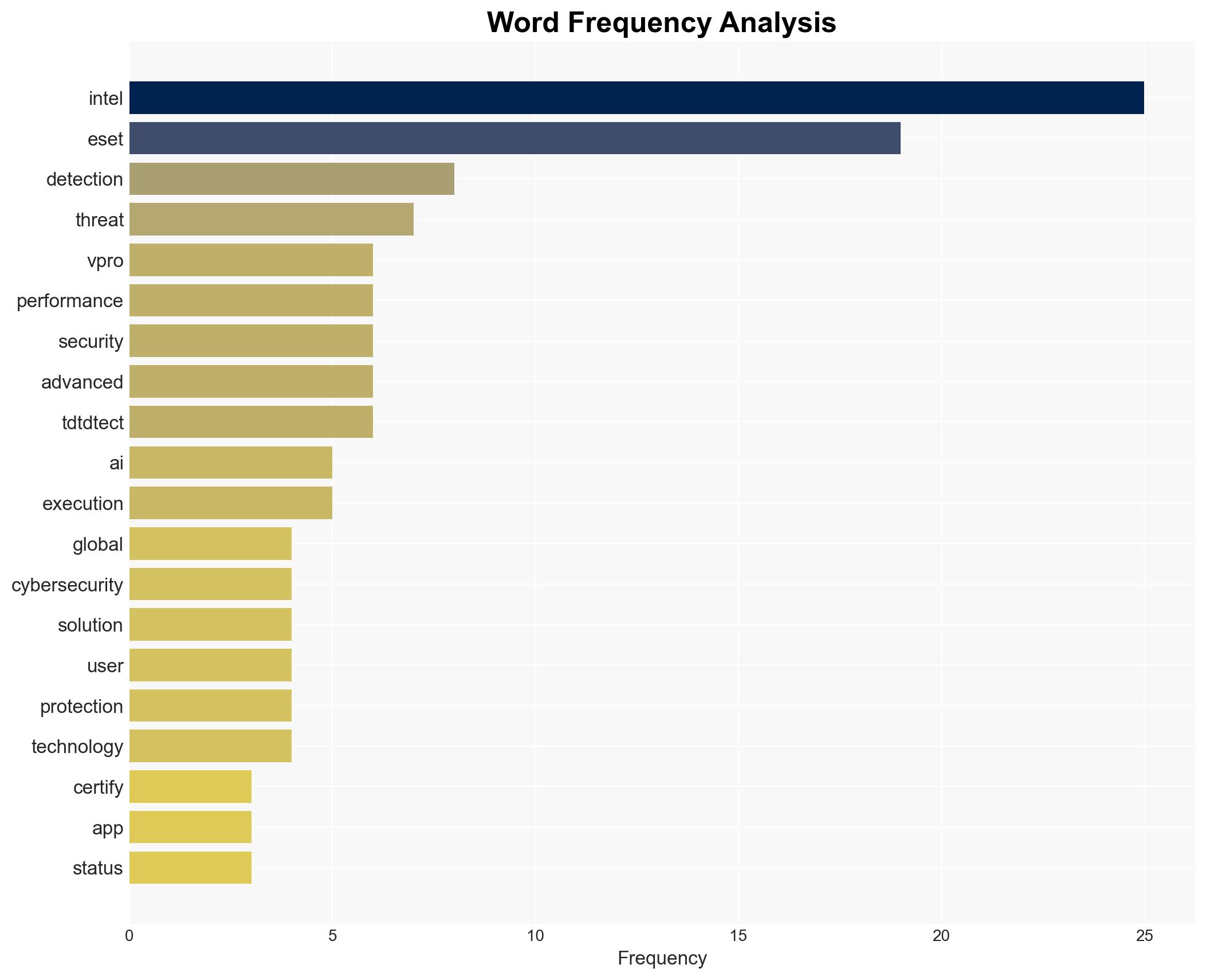
ESET Achieves Intel vPro Certification, Enhancing Cybersecurity Performance for Business Clients
Published on: 2026-03-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: ESET Receives Intel vPro Certified App Status Delivering Performance Benefits for Business Customers While Advancing Threat Detection Capability
1. BLUF (Bottom Line Up Front)
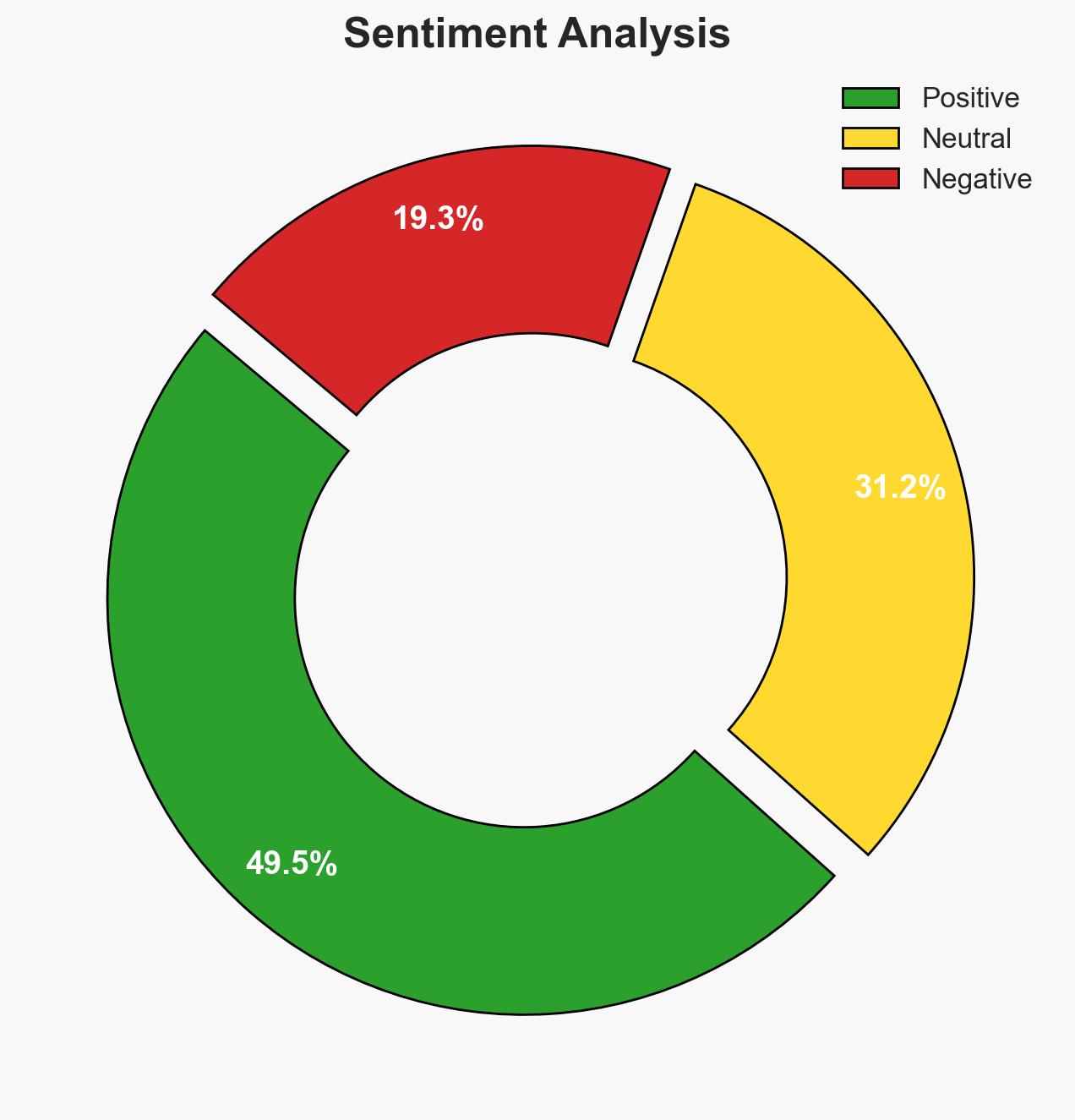
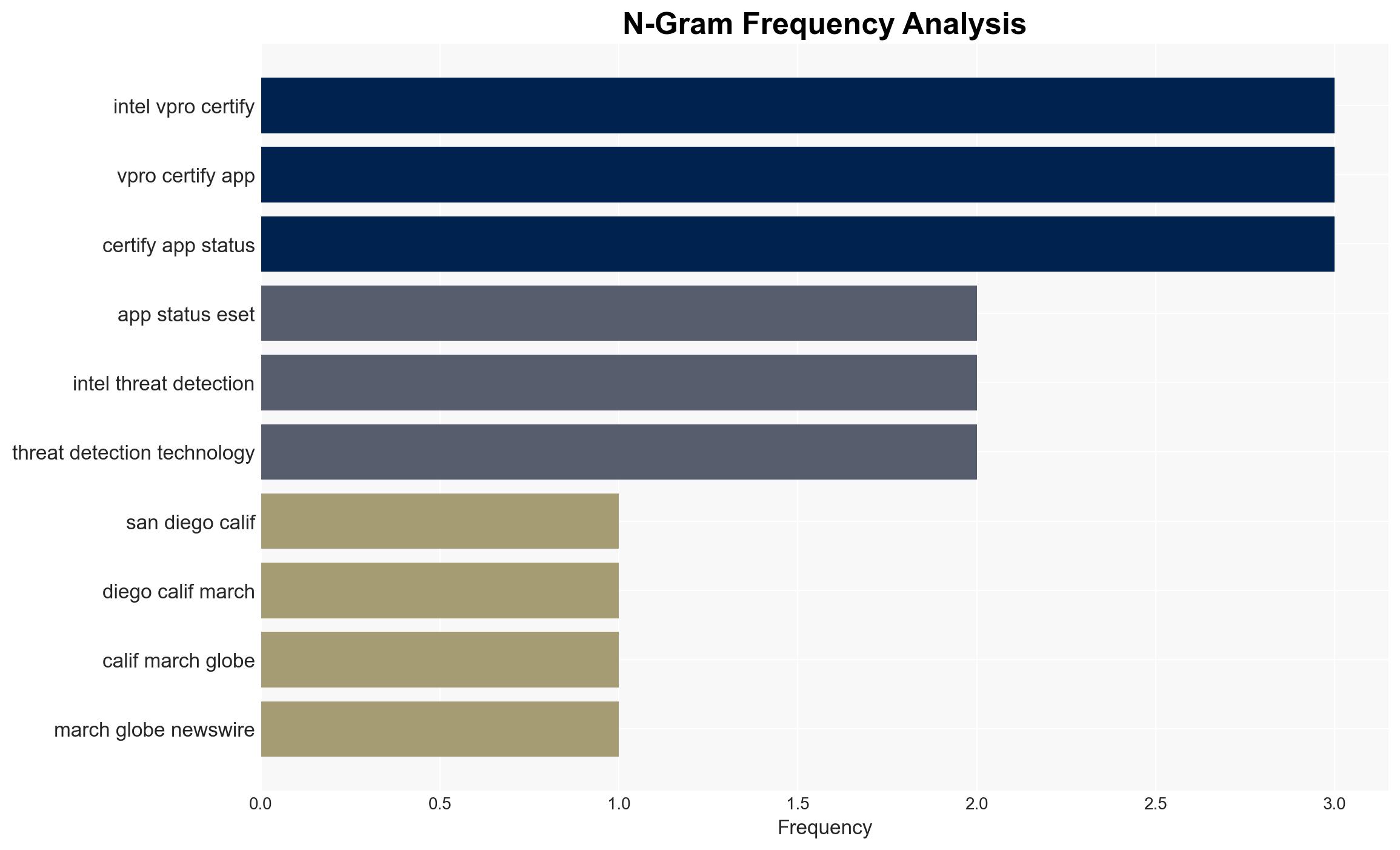
ESET’s attainment of Intel vPro Certified App status signifies a strategic enhancement in cybersecurity capabilities, particularly in threat detection and system performance for business customers. This development is likely to strengthen ESET’s market position and expand its influence in the cybersecurity domain. The collaboration with Intel on advanced threat detection technologies suggests a significant shift towards hardware-based security solutions. Overall, this assessment is made with moderate confidence due to limited visibility into the broader competitive landscape and potential technological challenges.
2. Competing Hypotheses
- Hypothesis A: ESET’s collaboration with Intel and the vPro certification will lead to a significant competitive advantage in the cybersecurity market, enhancing its ability to protect against advanced threats. Supporting evidence includes the reported reduction in CPU utilization and increased power efficiency. However, uncertainties remain regarding the scalability and adoption rate of these technologies across diverse business environments.
- Hypothesis B: The partnership and certification may not significantly alter ESET’s market position due to potential challenges in integrating these advanced technologies into existing IT infrastructures and the competitive responses from other cybersecurity firms. This hypothesis is supported by the complexity of hardware-based security solutions and potential resistance from businesses to adopt new technologies.
- Assessment: Hypothesis A is currently better supported due to the tangible performance improvements and strategic alignment with Intel’s advanced technologies. Key indicators that could shift this judgment include market adoption rates and competitive innovations in similar technologies.
3. Key Assumptions and Red Flags
- Assumptions: ESET’s solutions will be compatible with a wide range of business IT environments; Intel’s hardware advancements will continue to support these security enhancements; businesses will prioritize performance and security improvements.
- Information Gaps: Detailed market analysis on the adoption rate of Intel vPro certified applications; competitive responses from other cybersecurity firms; long-term performance data of ESET’s solutions in diverse operational settings.
- Bias & Deception Risks: Potential over-reliance on vendor-provided performance metrics; confirmation bias in evaluating the efficacy of hardware-based security solutions; possible strategic marketing exaggerations.
4. Implications and Strategic Risks
This development could lead to a paradigm shift in cybersecurity strategies, emphasizing hardware-based solutions. Over time, this may influence industry standards and customer expectations.
- Political / Geopolitical: Minimal direct impact, though increased cybersecurity capabilities could indirectly affect national security postures.
- Security / Counter-Terrorism: Enhanced threat detection capabilities could improve resilience against cyber-attacks, potentially reducing the risk of cyber-terrorism.
- Cyber / Information Space: The shift towards hardware-based security may drive innovation and competition in the cybersecurity sector, influencing cyber defense strategies.
- Economic / Social: Improved cybersecurity could bolster business confidence, but the cost of adopting new technologies may strain smaller enterprises.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor market reactions and adoption rates of ESET’s solutions; assess competitive responses and technological developments in hardware-based security.
- Medium-Term Posture (1–12 months): Develop partnerships with technology providers to enhance cybersecurity capabilities; invest in training and infrastructure to support new security technologies.
- Scenario Outlook: Best: Widespread adoption of ESET’s solutions leads to improved cybersecurity standards. Worst: Integration challenges and competitive pressures limit impact. Most-Likely: Gradual adoption with incremental improvements in security posture.
6. Key Individuals and Entities
- Juraj Malcho, CTO at ESET
- Dennis Luo, Sr. Director and GM, Worldwide AI PC Developer Relations at Intel
- Intel Corporation
- ESET
7. Thematic Tags
cybersecurity, threat detection, Intel vPro, hardware-based security, business performance, AI integration, cybersecurity market
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us