Key Vulnerabilities Addressed in iOS 26.4 Security Update, Including Critical Bypass Risk for Biometric Apps
Published on: 2026-03-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
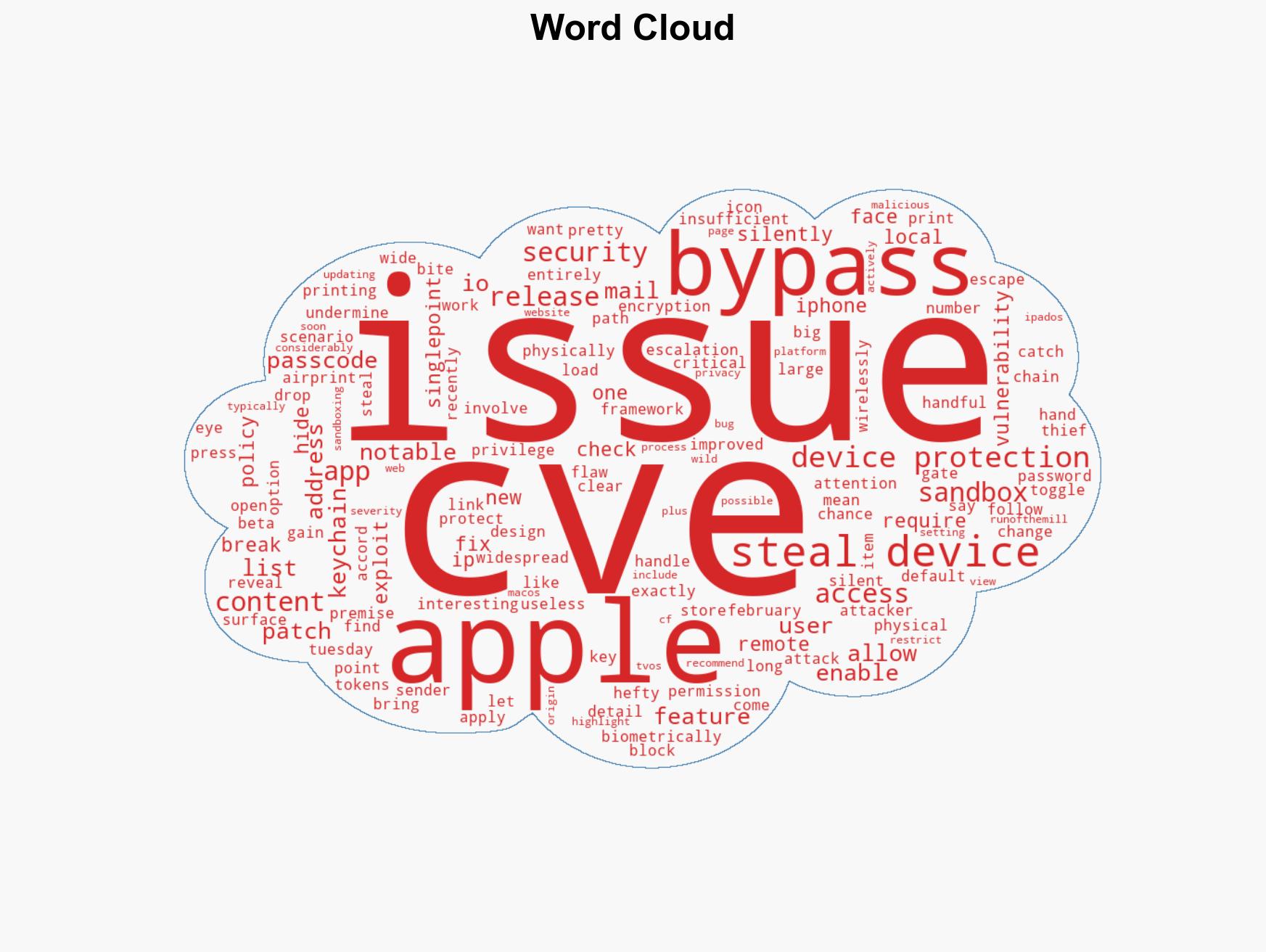
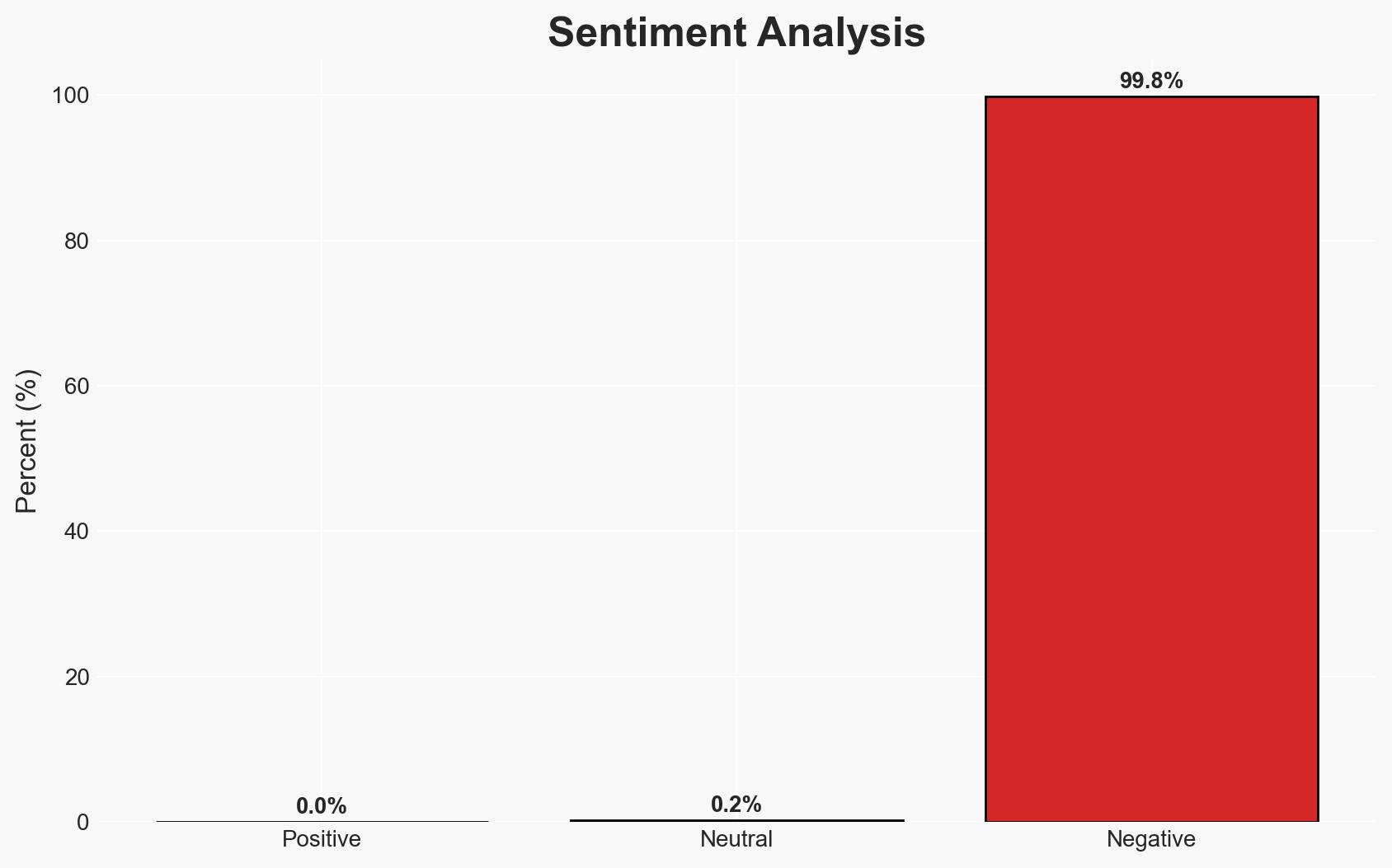
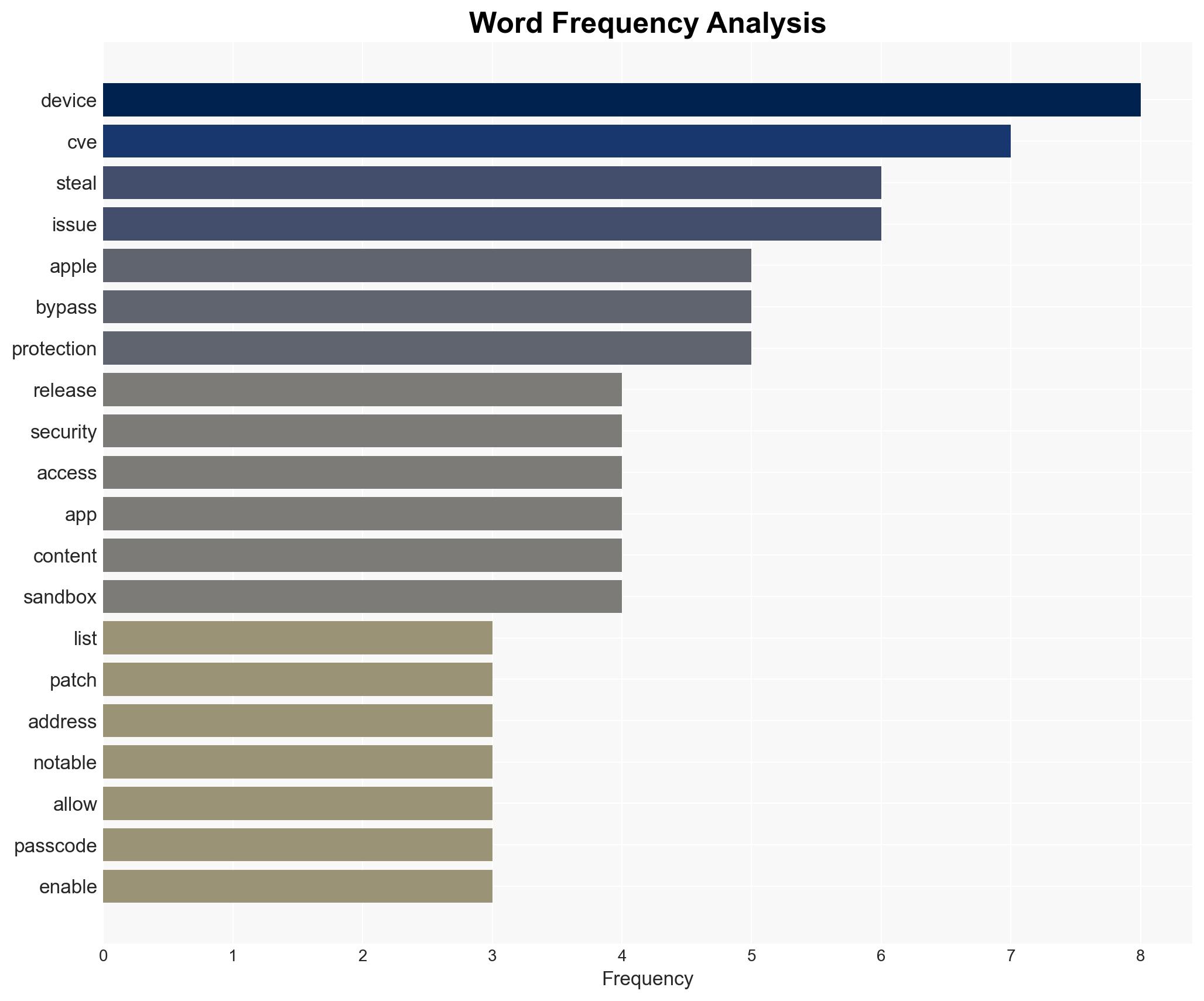
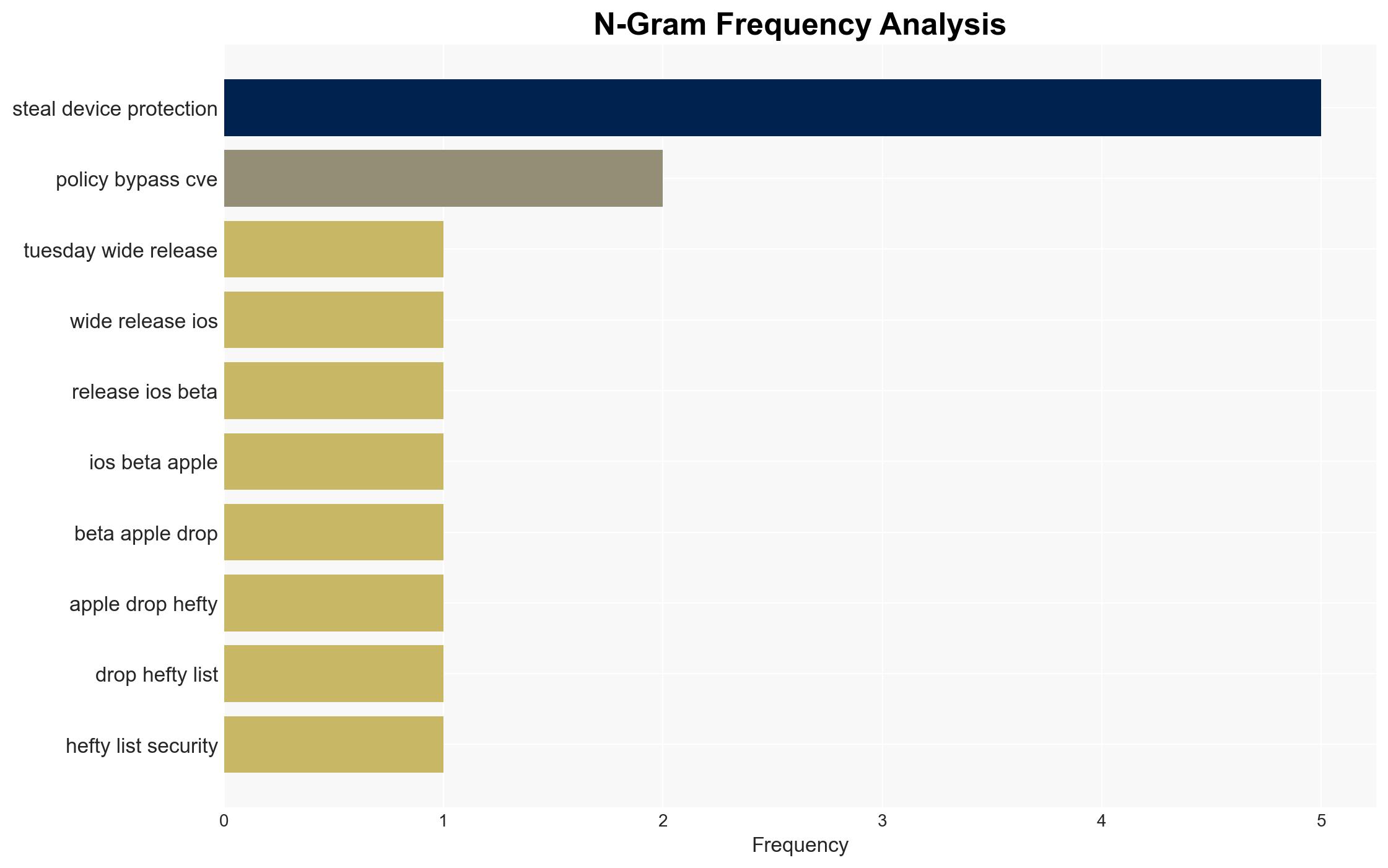
Intelligence Report: Security Bite What stands out in the iOS 264 security release notes
1. BLUF (Bottom Line Up Front)
The iOS 26.4 security release addresses critical vulnerabilities that could undermine device security, particularly the Stolen Device Protection feature, with moderate confidence. These vulnerabilities, if exploited, could affect iPhone users globally by allowing unauthorized access to sensitive data. The most likely hypothesis is that these vulnerabilities were not actively exploited in the wild, but the potential for exploitation remains significant.
2. Competing Hypotheses
- Hypothesis A: The vulnerabilities were discovered and patched before any significant exploitation occurred. Supporting evidence includes the lack of reports of active exploitation and Apple’s proactive patching. However, the absence of detailed exploitation data introduces uncertainty.
- Hypothesis B: The vulnerabilities were actively exploited but not widely reported due to limited detection capabilities or underreporting. Contradicting evidence includes Apple’s statement that there is no active exploitation, but this could be due to limited visibility into all attack vectors.
- Assessment: Hypothesis A is currently better supported due to the absence of evidence of active exploitation and Apple’s swift response. Key indicators that could shift this judgment include new reports of exploitation or further technical analysis revealing past incidents.
3. Key Assumptions and Red Flags
- Assumptions: Apple’s security measures are generally effective; the vulnerabilities were not exploited in the wild; users will update their devices promptly.
- Information Gaps: Detailed technical data on the exploitation attempts and the scope of affected devices are missing.
- Bias & Deception Risks: Potential bias in relying on vendor-provided information; risk of underreporting due to lack of detection tools.
4. Implications and Strategic Risks
The patching of these vulnerabilities could stabilize user trust in Apple’s security measures, but failure to address them promptly could lead to significant security breaches.
- Political / Geopolitical: Limited direct implications, but could affect perceptions of U.S. tech company reliability globally.
- Security / Counter-Terrorism: Enhanced device security reduces the risk of unauthorized access that could be exploited by malicious actors.
- Cyber / Information Space: Potential increase in cyber threat actor interest in exploiting similar vulnerabilities in the future.
- Economic / Social: Potential economic impact if consumer trust in Apple products diminishes, affecting sales and market share.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage users to update devices immediately; monitor for any reports of exploitation; engage with Apple for detailed technical briefings.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies for early vulnerability detection; invest in user education on security practices.
- Scenario Outlook:
- Best: No significant exploitation occurs, and user trust is maintained.
- Worst: Exploitation occurs leading to data breaches and loss of consumer confidence.
- Most-Likely: Vulnerabilities remain unexploited, but similar issues arise, requiring ongoing vigilance.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, vulnerability management, mobile security, information security, software patching, Apple, iOS
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us