CanisterWorm malware targets Iranian systems for destruction, leveraging npm packages and ICP canisters for c…
Published on: 2026-03-26
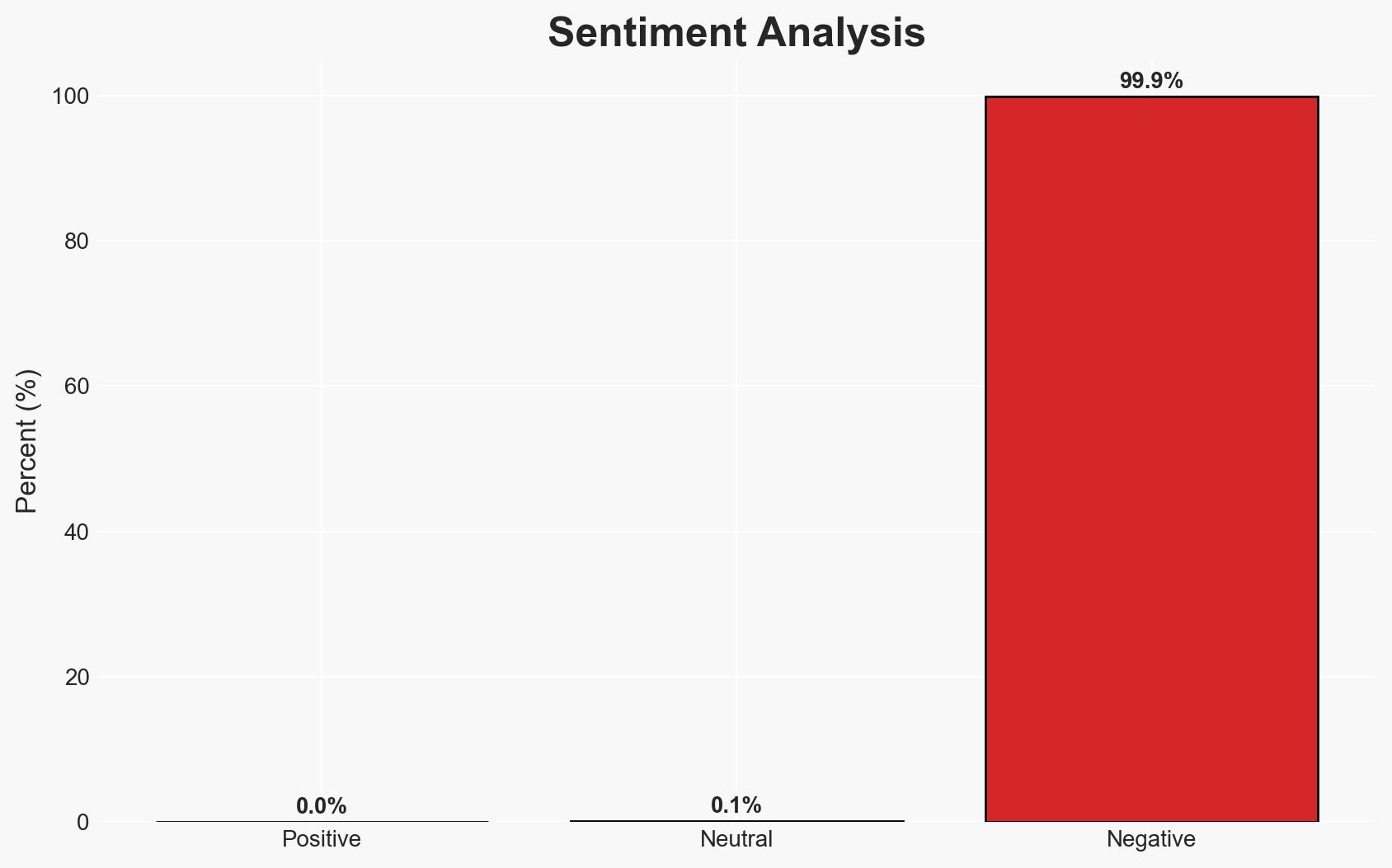
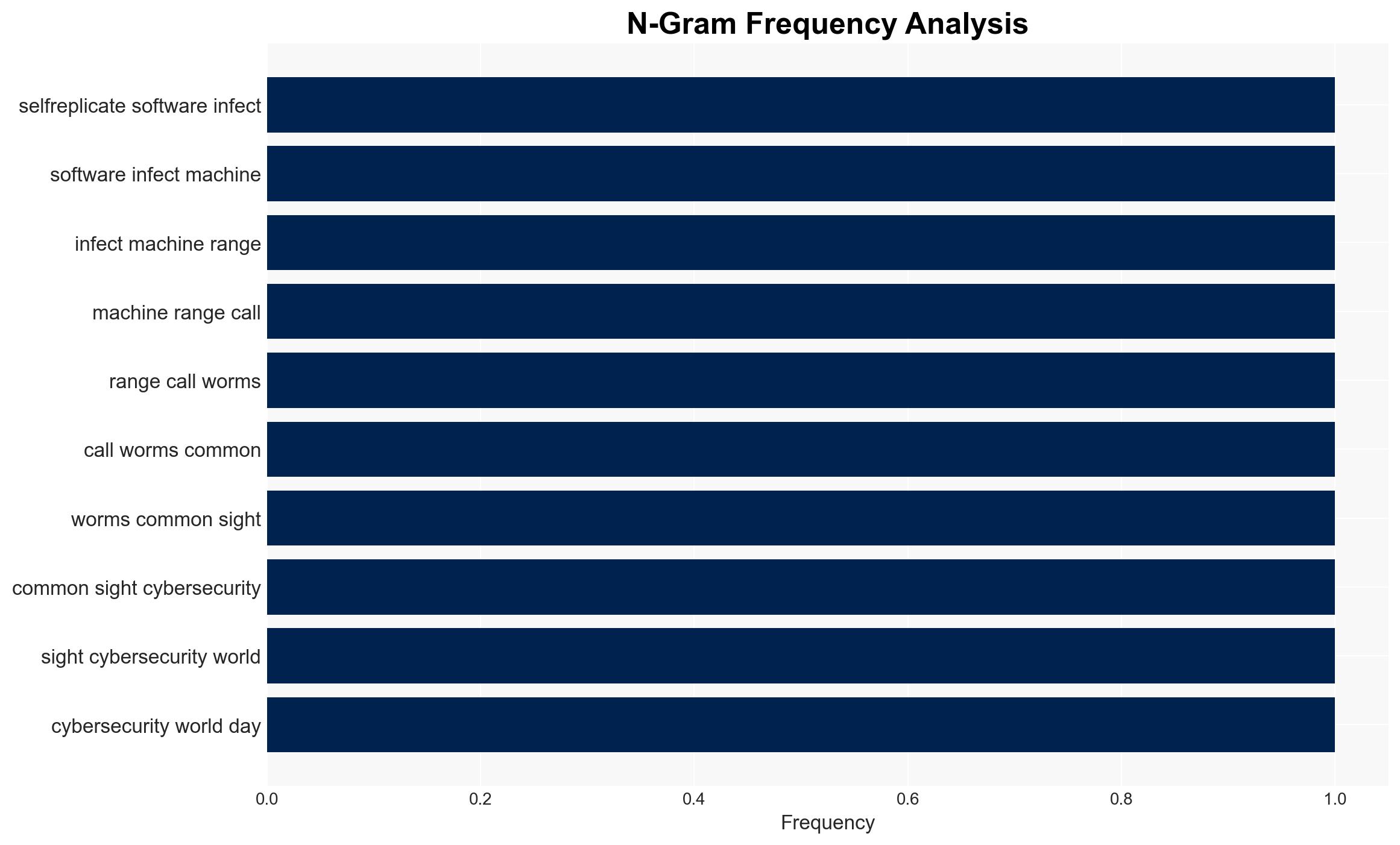
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
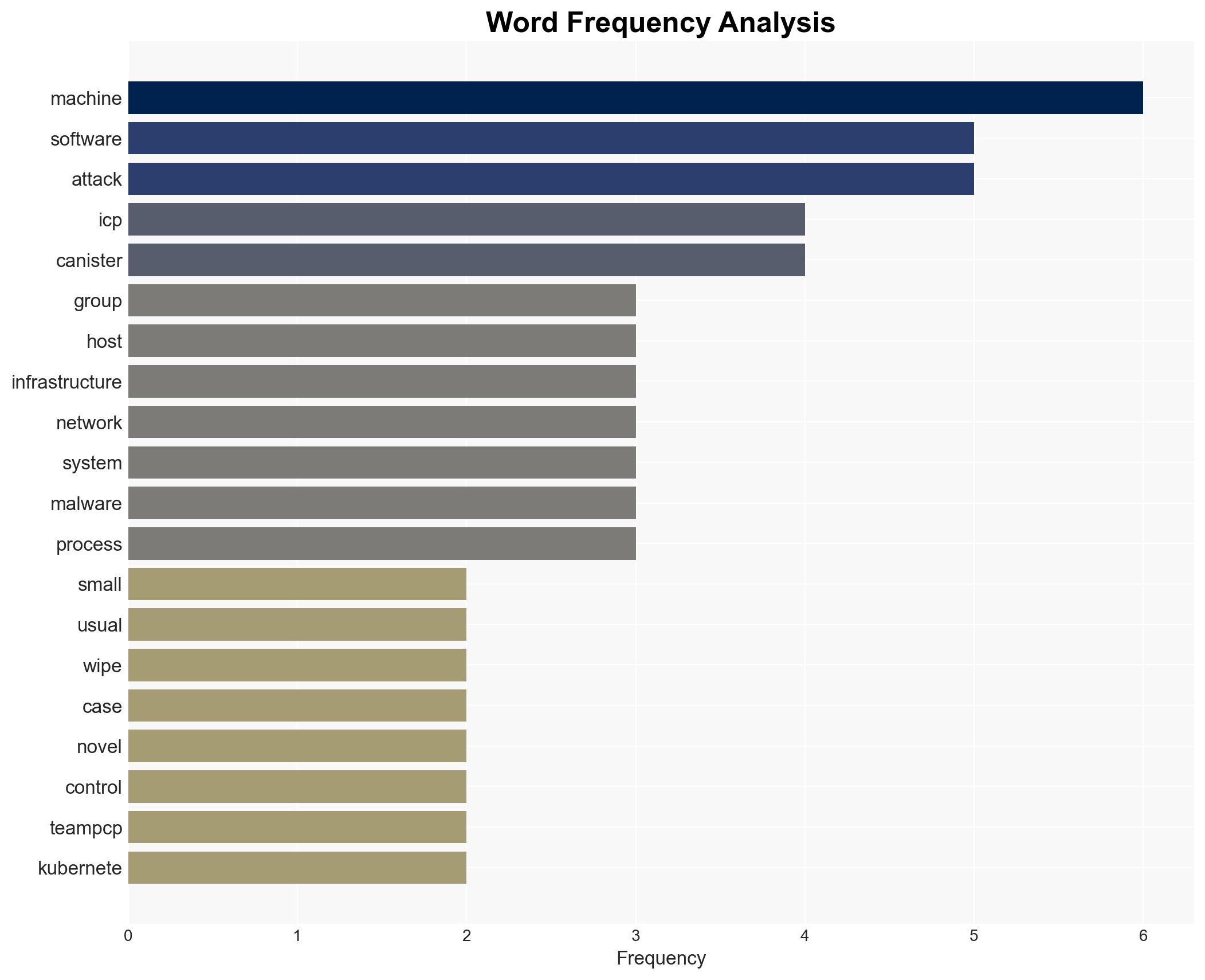
Intelligence Report: CanisterWorm malware wipes Iranian machines for no apparent reason sophisticated attack spreads through npm packages and uses ICP canister as control surface
1. BLUF (Bottom Line Up Front)
The CanisterWorm malware attack, attributed to the TeamPCP collective, specifically targets and wipes Iranian machines using a novel control mechanism via ICP canisters. The attack’s motivation remains unclear, raising concerns about potential geopolitical implications. The most likely hypothesis is that the attack serves as a demonstration of capability rather than a financially motivated operation. Overall confidence in this assessment is moderate due to significant information gaps.
2. Competing Hypotheses
- Hypothesis A: The attack is a demonstration of technical capability by TeamPCP, aimed at showcasing their control over a large number of systems. Supporting evidence includes the lack of financial gain from wiping Iranian systems and the use of sophisticated control mechanisms. Key uncertainties include the group’s ultimate objectives and potential undisclosed motivations.
- Hypothesis B: The attack is part of a broader geopolitical strategy to destabilize or send a message to Iran. Supporting evidence is limited, but the targeted nature of the attack against Iranian systems suggests a possible political motive. Contradicting evidence includes the absence of explicit political statements or demands.
- Assessment: Hypothesis A is currently better supported due to the technical sophistication and lack of immediate financial or political gain. Key indicators that could shift this judgment include emerging evidence of political motives or further attacks aligned with geopolitical tensions.
3. Key Assumptions and Red Flags
- Assumptions: TeamPCP has the technical capability to control a large network of compromised systems; the attack is not financially motivated; ICP canisters provide a resilient control mechanism.
- Information Gaps: The specific motivations behind targeting Iranian systems; the full extent of TeamPCP’s network control; potential undisclosed affiliations or backers.
- Bias & Deception Risks: Potential bias in attributing the attack solely to TeamPCP without considering other actors; risk of deception in the group’s public statements or claimed capabilities.
4. Implications and Strategic Risks
This development could influence regional cybersecurity dynamics and provoke retaliatory measures. The use of ICP canisters as a control mechanism may inspire similar tactics by other groups.
- Political / Geopolitical: Potential escalation in cyber operations targeting Iran; increased tensions between Iran and perceived adversaries.
- Security / Counter-Terrorism: Heightened alertness in cybersecurity communities; potential for copycat attacks using similar methods.
- Cyber / Information Space: Increased scrutiny on ICP canisters and blockchain-based control mechanisms; potential regulatory responses.
- Economic / Social: Disruption to Iranian digital infrastructure; potential economic impacts if critical systems are affected.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of ICP canister activity; enhance defenses against similar malware propagation methods; engage with international partners for intelligence sharing.
- Medium-Term Posture (1–12 months): Develop resilience measures against blockchain-based control mechanisms; foster partnerships with cybersecurity firms for threat intelligence.
- Scenario Outlook:
- Best: No further attacks occur, and defensive measures are strengthened.
- Worst: Escalation of attacks leading to significant geopolitical tensions.
- Most-Likely: Continued low-level cyber operations with sporadic incidents.
6. Key Individuals and Entities
- TeamPCP (hacking group)
- Charlie Eriksen (Aikido researcher)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
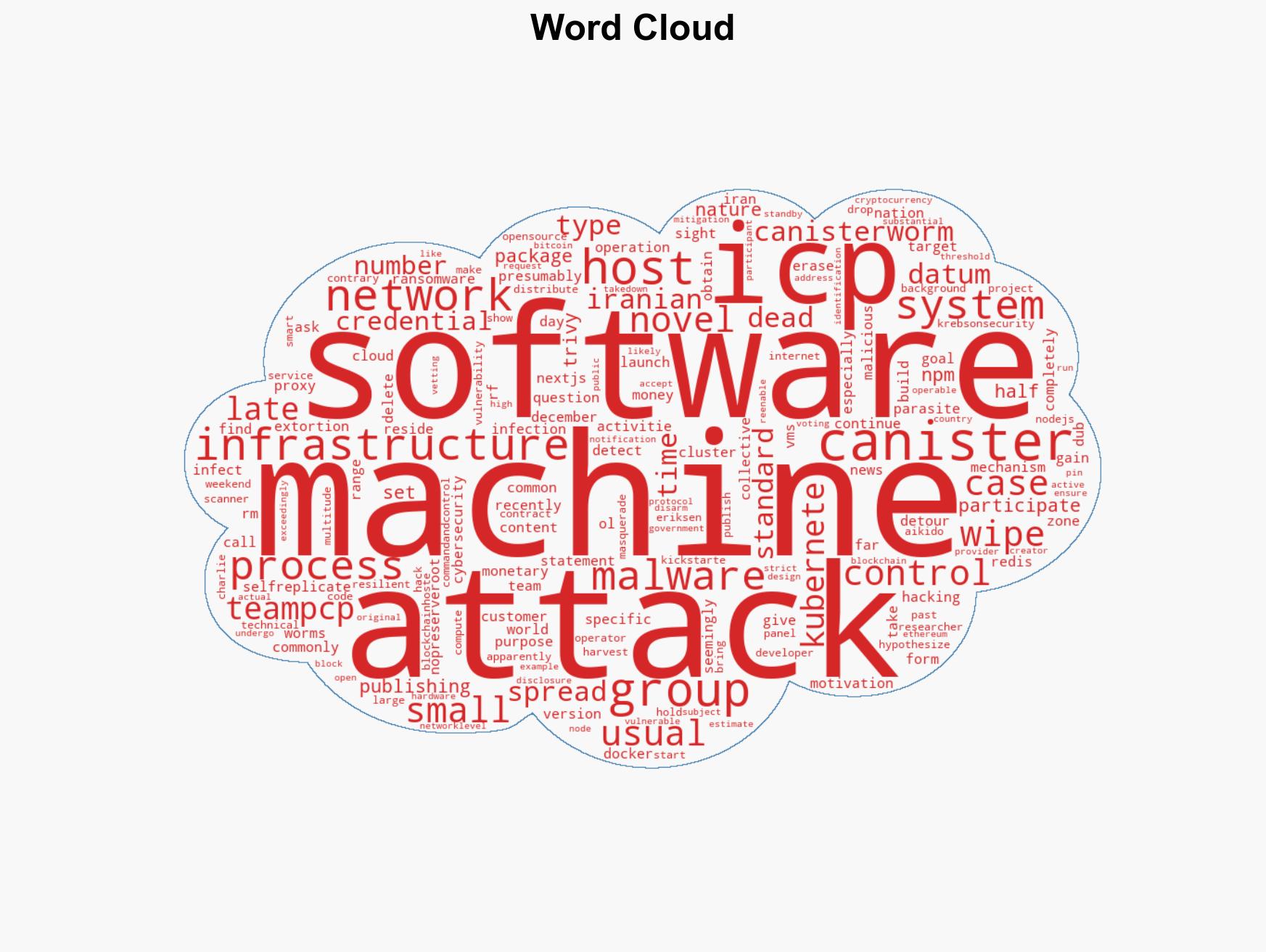
cybersecurity, malware, Iran, ICP canister, blockchain, geopolitical tensions, TeamPCP
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us