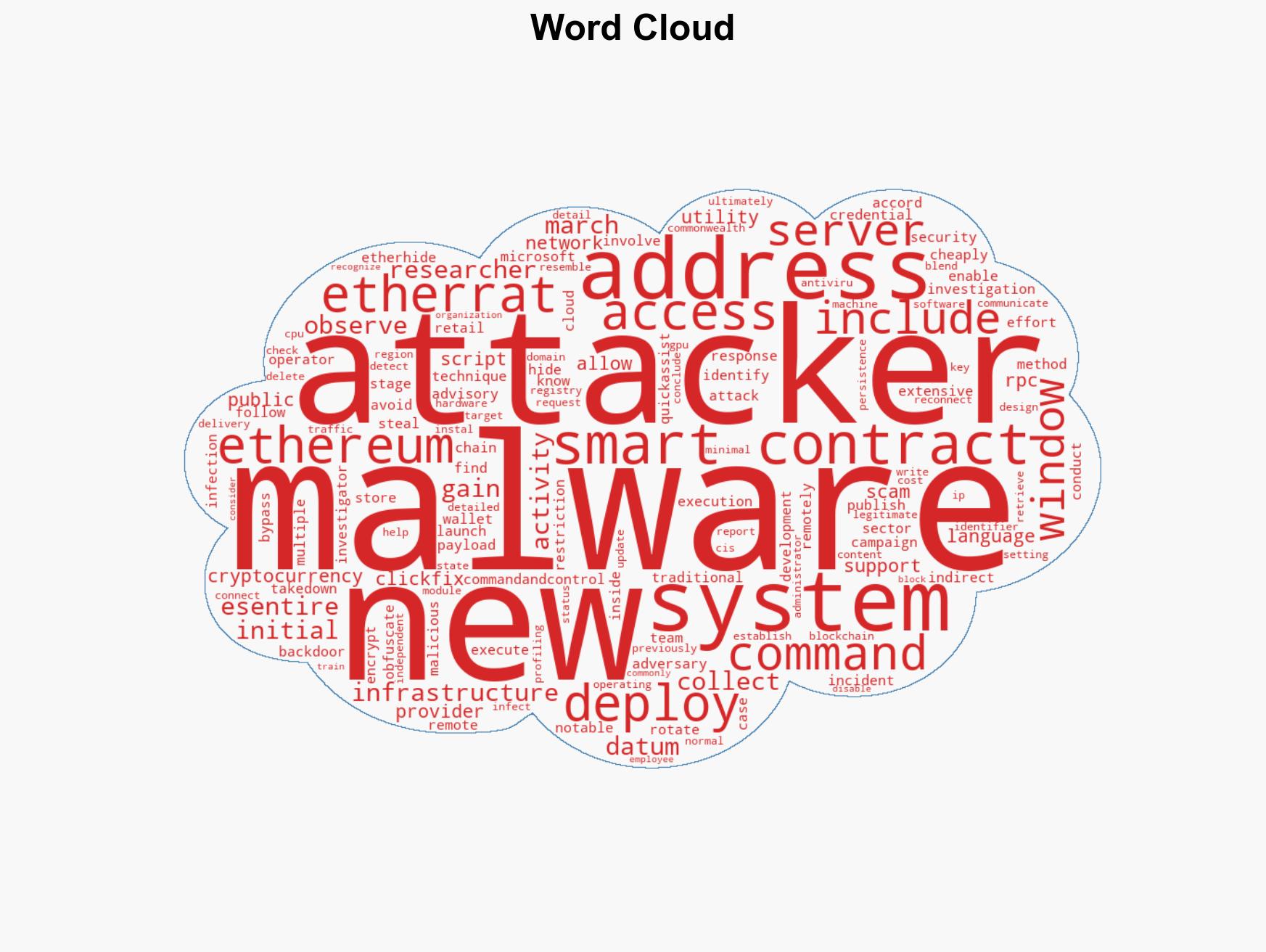
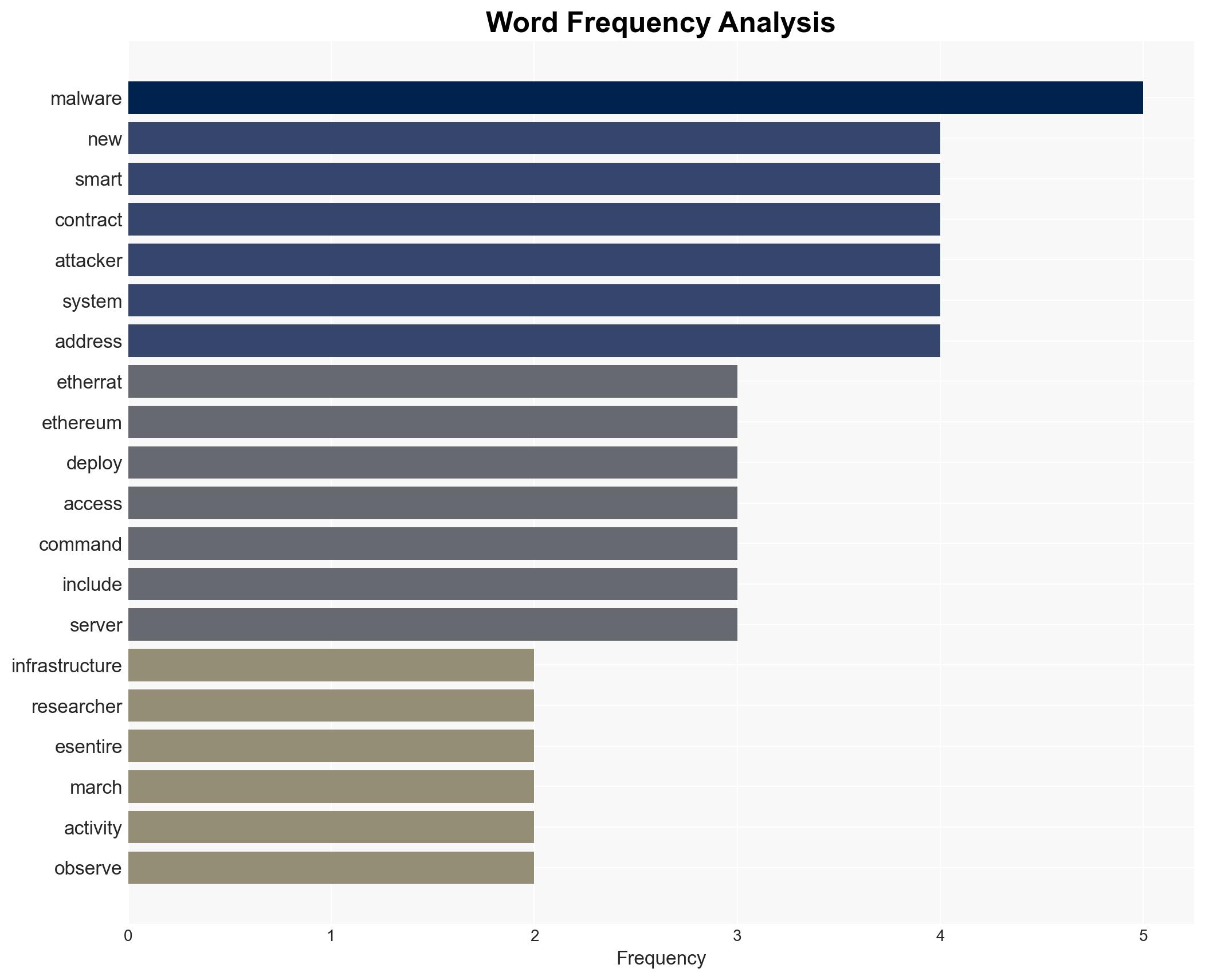
New EtherRAT Malware Leverages Ethereum Smart Contracts to Evade Security Measures and Execute Remote Attacks
Published on: 2026-03-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: EtherRAT Techniques Bypass Security Via Ethereum Smart Contracts
1. BLUF (Bottom Line Up Front)
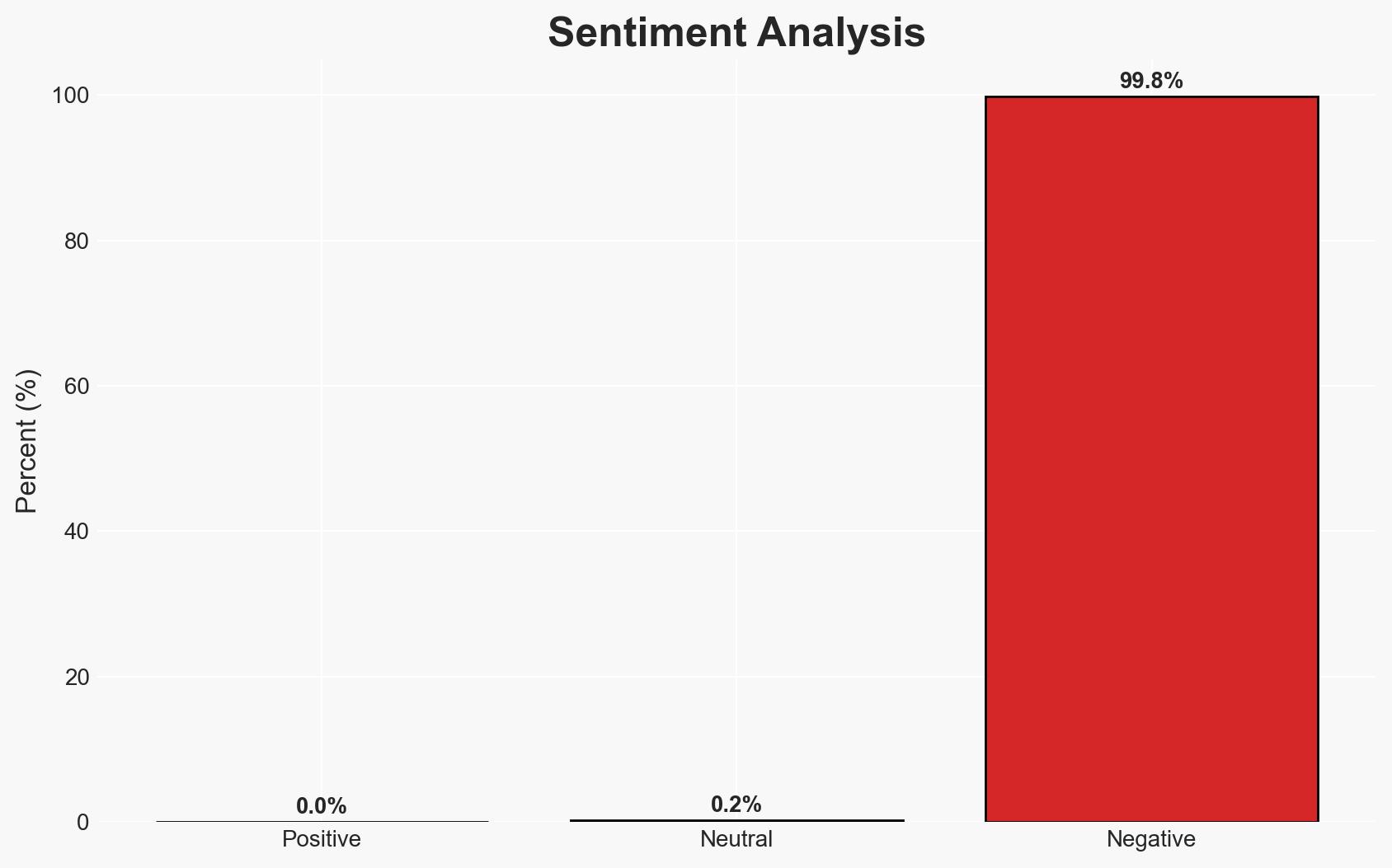
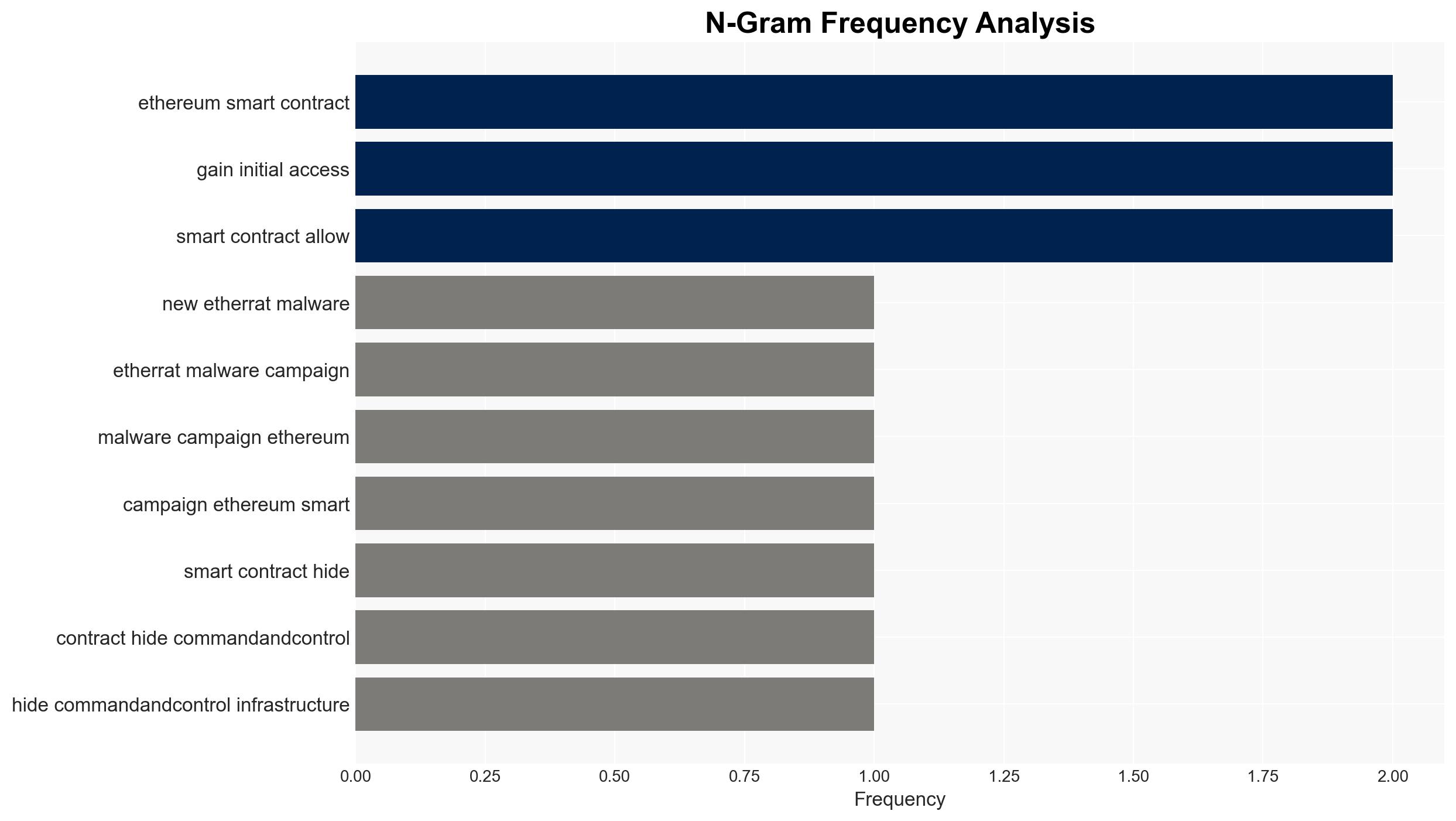
The EtherRAT malware campaign leverages Ethereum smart contracts to obscure its command-and-control infrastructure, posing a significant threat to cybersecurity, particularly in the retail sector. The use of EtherHiding allows for cost-effective and resilient infrastructure rotation, complicating traditional takedown efforts. This development could lead to increased cyber threats across various sectors. Overall confidence in this assessment is moderate due to existing information gaps.
2. Competing Hypotheses
- Hypothesis A: The primary goal of the EtherRAT campaign is financial gain through cryptocurrency theft and data exfiltration. This is supported by the malware’s capabilities to steal cryptocurrency wallets and cloud credentials. However, the lack of specific attribution to a known threat actor introduces uncertainty.
- Hypothesis B: The campaign is a broader espionage effort targeting corporate information and infrastructure, using financial theft as a secondary objective. The detailed system profiling and persistence mechanisms support this, but the focus on cryptocurrency theft contradicts this hypothesis.
- Assessment: Hypothesis A is currently better supported due to the direct evidence of cryptocurrency theft and the use of financial scams for initial access. Indicators such as changes in target sectors or tactics could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The attackers have a high level of technical sophistication; the use of Ethereum smart contracts is primarily for C2 obfuscation; the campaign is financially motivated.
- Information Gaps: Specific attribution to a threat actor; the full extent of affected sectors beyond retail; the potential for state sponsorship.
- Bias & Deception Risks: Potential bias from reliance on a single source (eSentire); deception risk from attackers using false flags or misleading tactics.
4. Implications and Strategic Risks
The EtherRAT campaign could set a precedent for future malware using blockchain technology for C2 obfuscation, complicating cybersecurity defenses. This could lead to increased costs for cybersecurity measures and potential regulatory responses.
- Political / Geopolitical: Potential for increased tensions if state-sponsored links are identified, leading to diplomatic challenges.
- Security / Counter-Terrorism: Heightened threat environment as similar techniques are adopted by other malicious actors.
- Cyber / Information Space: Increased difficulty in tracking and mitigating malware due to blockchain-based C2 infrastructure.
- Economic / Social: Potential financial losses for affected organizations and increased cybersecurity insurance costs.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Ethereum smart contract activity, train employees on recognizing IT support scams, and disable unnecessary Windows utilities.
- Medium-Term Posture (1–12 months): Develop partnerships with blockchain analysis firms, invest in advanced threat detection capabilities, and consider policy advocacy for blockchain regulation.
- Scenario Outlook:
- Best: Effective countermeasures lead to a decline in similar attacks.
- Worst: Widespread adoption of blockchain-based C2 techniques by various threat actors.
- Most-Likely: Continued use of blockchain for C2 by financially motivated cybercriminals, with incremental improvements in detection and response.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, malware, blockchain, financial crime, cyber-espionage, threat intelligence, retail sector
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us