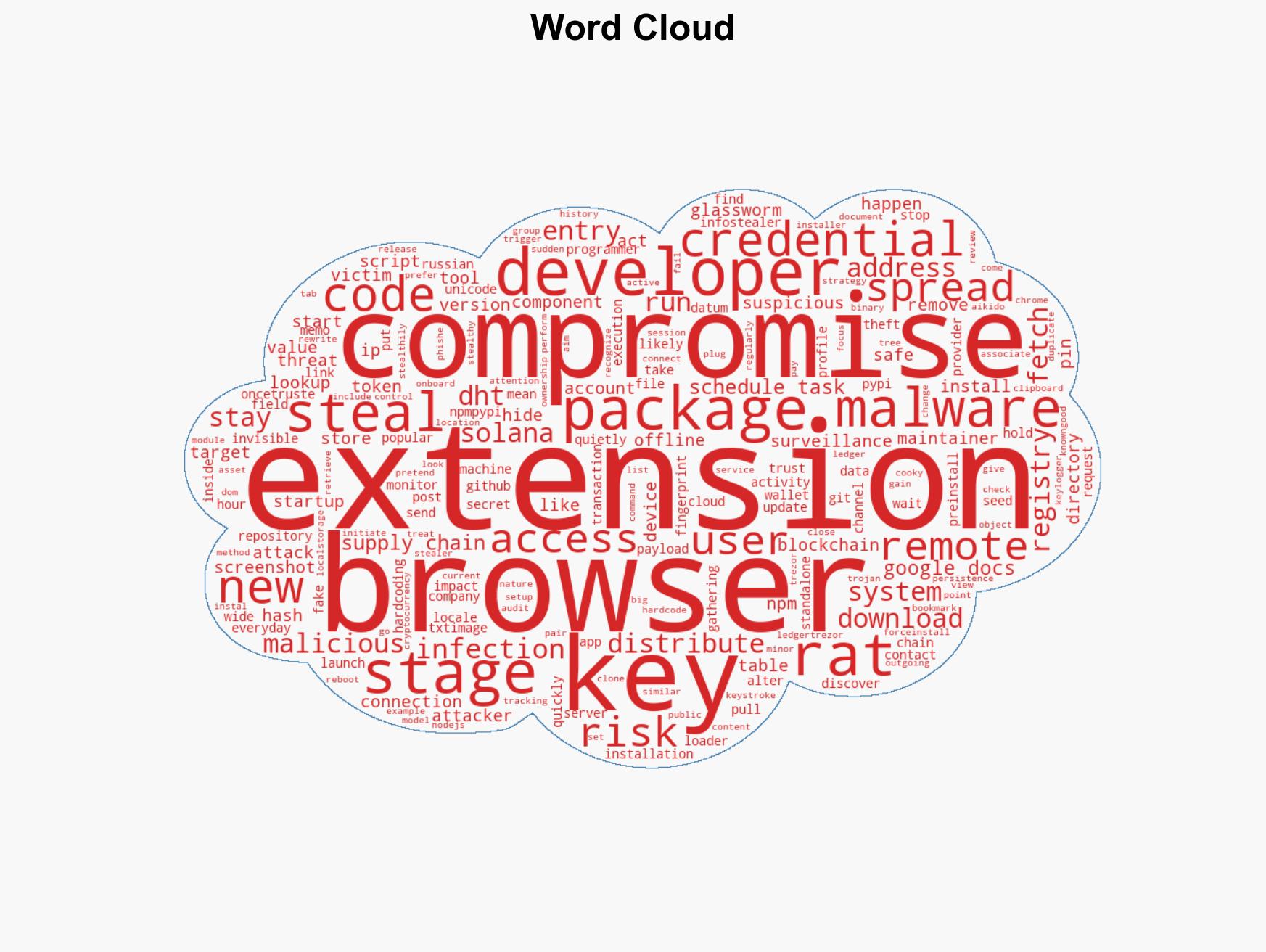
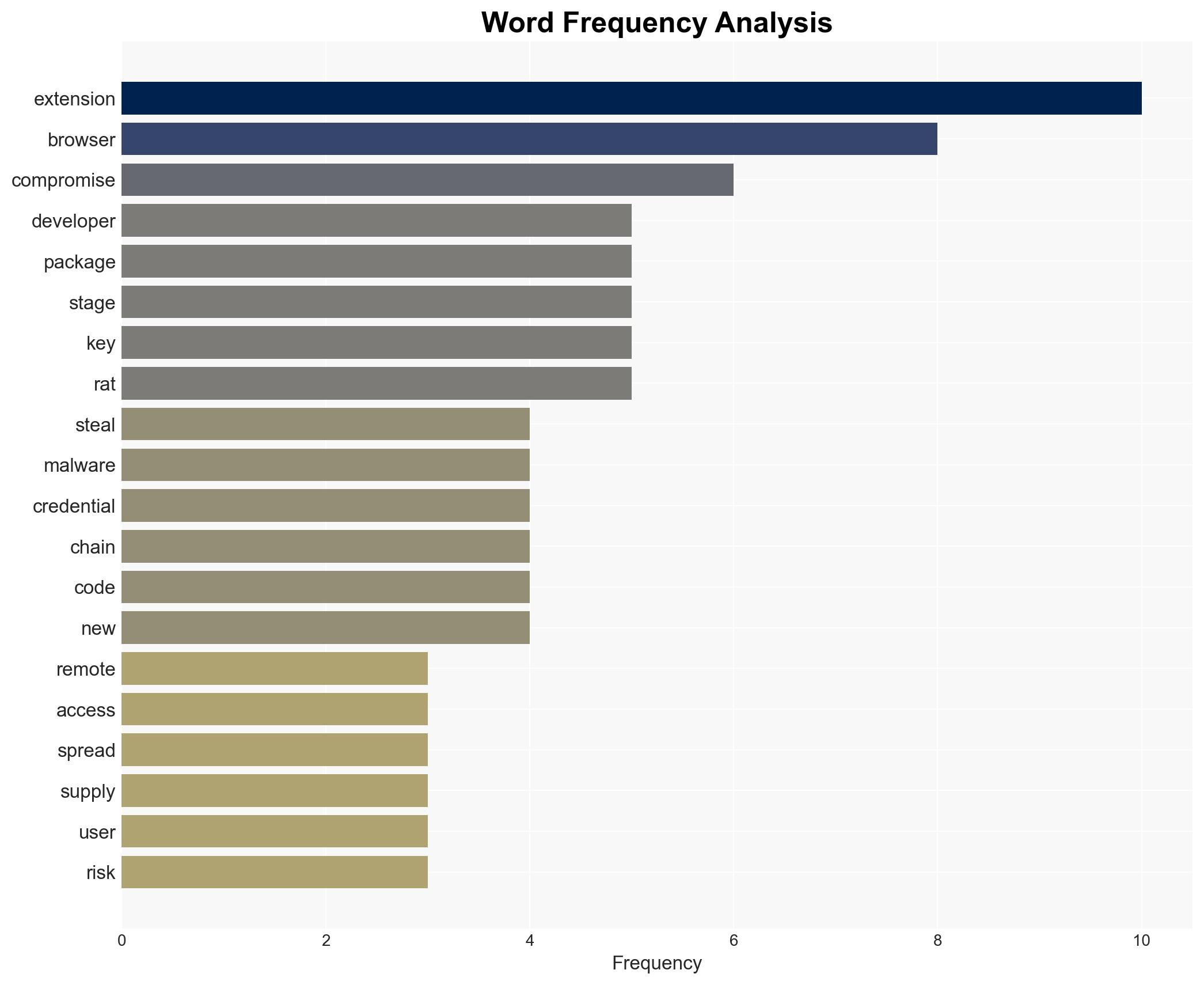
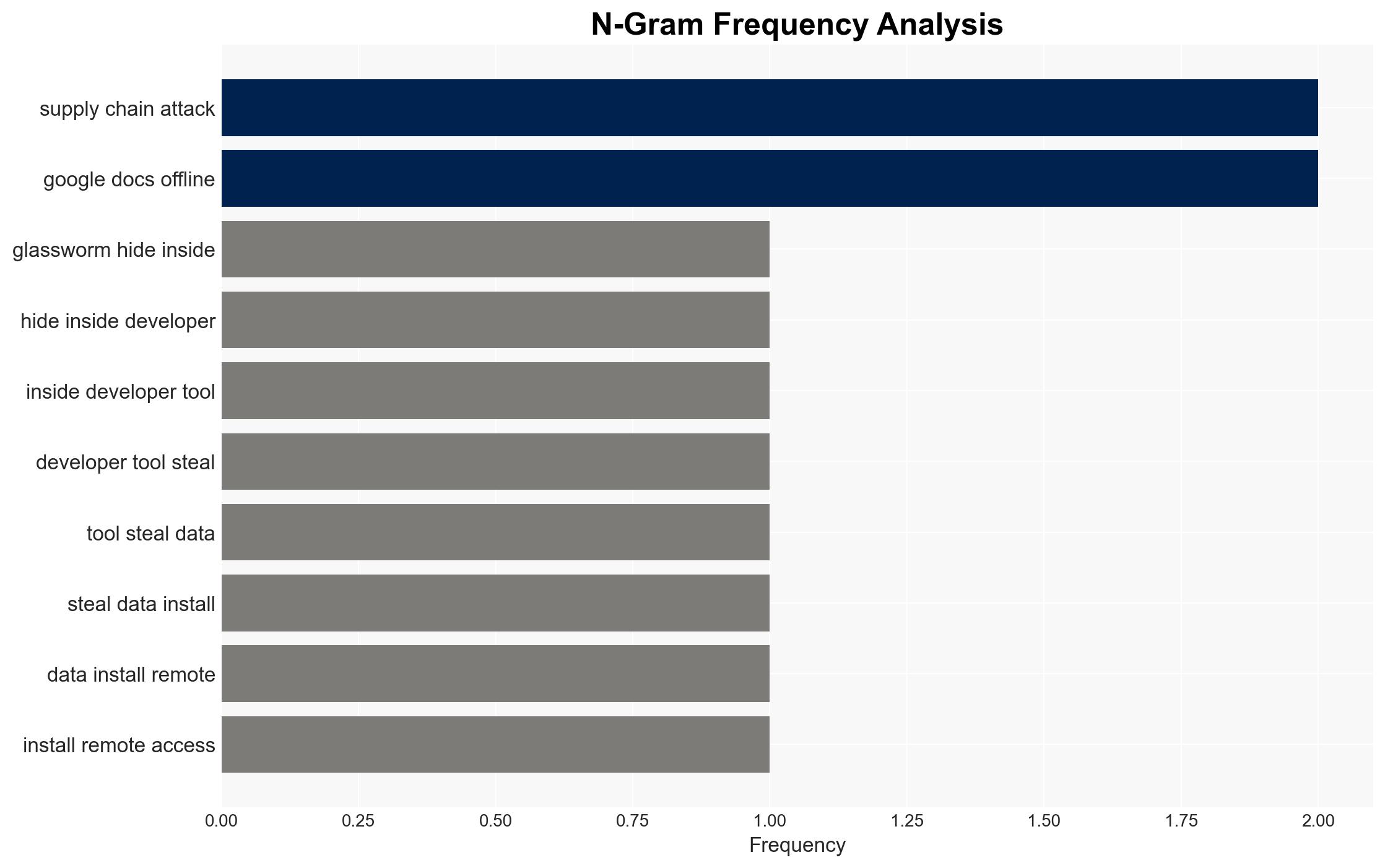
GlassWorm malware infiltrates systems via developer tools, deploying fake browser extensions for data theft.
Published on: 2026-03-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: GlassWorm attack installs fake browser extension for surveillance
1. BLUF (Bottom Line Up Front)
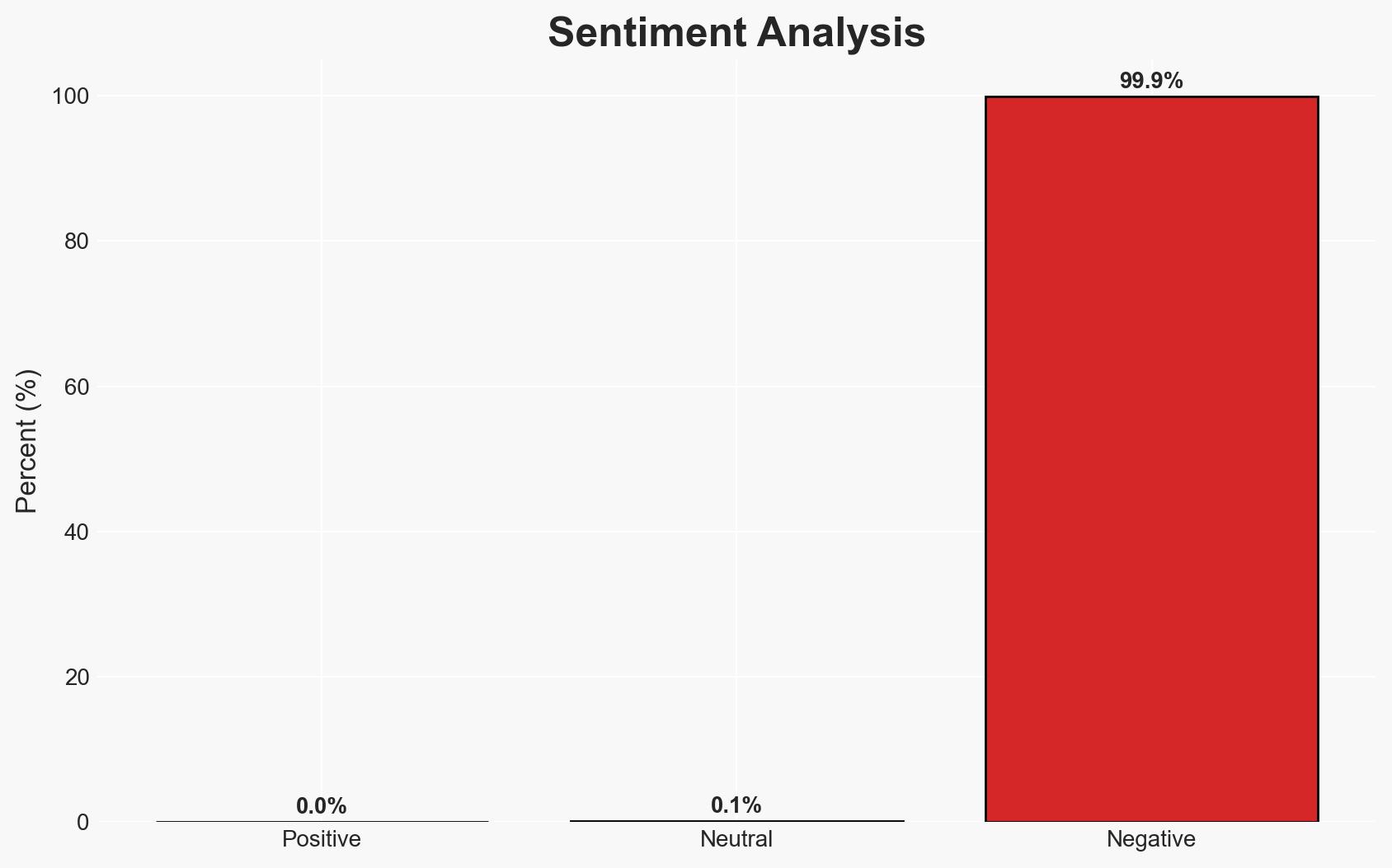
The GlassWorm cyber attack leverages compromised developer tools to install surveillance malware, posing significant risks to supply chains and end-users. The attack is likely part of a broader campaign targeting developers to facilitate widespread data theft and system compromise. This assessment is made with moderate confidence due to the complexity of the attack vector and the potential for broader impacts.
2. Competing Hypotheses
- Hypothesis A: GlassWorm is primarily a cyber-espionage tool aimed at gathering sensitive data from developers and their networks. Supporting evidence includes the targeted nature of the attack on developer tools and the sophisticated multi-stage infection process. However, the lack of specific attribution and the broad potential impact on supply chains remain uncertainties.
- Hypothesis B: GlassWorm is part of a financially motivated cybercrime operation focused on stealing credentials and financial data. This is supported by the inclusion of phishing binaries and credential-stealing components. Contradicting evidence includes the complex infrastructure and use of blockchain for command and control, which are more typical of espionage operations.
- Assessment: Hypothesis A is currently better supported due to the strategic targeting of developers and the sophisticated nature of the attack, which suggests a focus on long-term data collection rather than immediate financial gain. Indicators that could shift this judgment include evidence of direct financial transactions or ransom demands linked to the attack.
3. Key Assumptions and Red Flags
- Assumptions: The attack is state-sponsored or supported by a state actor; developers are the primary initial targets; the use of blockchain for C2 is intended to evade detection.
- Information Gaps: Specific attribution to a threat actor or group; detailed analysis of the blockchain transactions used for C2; full scope of compromised developer accounts.
- Bias & Deception Risks: Potential bias in assuming state sponsorship due to the sophistication of the attack; deception risk in the use of blockchain to obscure attacker identity and intentions.
4. Implications and Strategic Risks
The GlassWorm attack could significantly disrupt software supply chains and compromise sensitive data across multiple sectors. Over time, this may lead to increased geopolitical tensions if state sponsorship is confirmed.
- Political / Geopolitical: Potential attribution to a nation-state could escalate cyber tensions and lead to diplomatic conflicts.
- Security / Counter-Terrorism: Increased vulnerability of critical infrastructure and potential for cascading supply chain attacks.
- Cyber / Information Space: Enhanced focus on securing developer tools and repositories; potential for increased regulatory scrutiny on software supply chains.
- Economic / Social: Potential economic impact from compromised business operations and loss of consumer trust in digital services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of developer tool repositories; implement stricter access controls and code verification processes.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to improve supply chain security; invest in threat intelligence capabilities focused on developer-targeted attacks.
- Scenario Outlook:
- Best: Rapid identification and mitigation of the attack vector, leading to minimal disruption.
- Worst: Widespread compromise of critical infrastructure and prolonged geopolitical conflict.
- Most-Likely: Continued targeted attacks with incremental improvements in supply chain security.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cyber-espionage, supply chain security, malware, developer tools, blockchain, data theft, cybercrime
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us