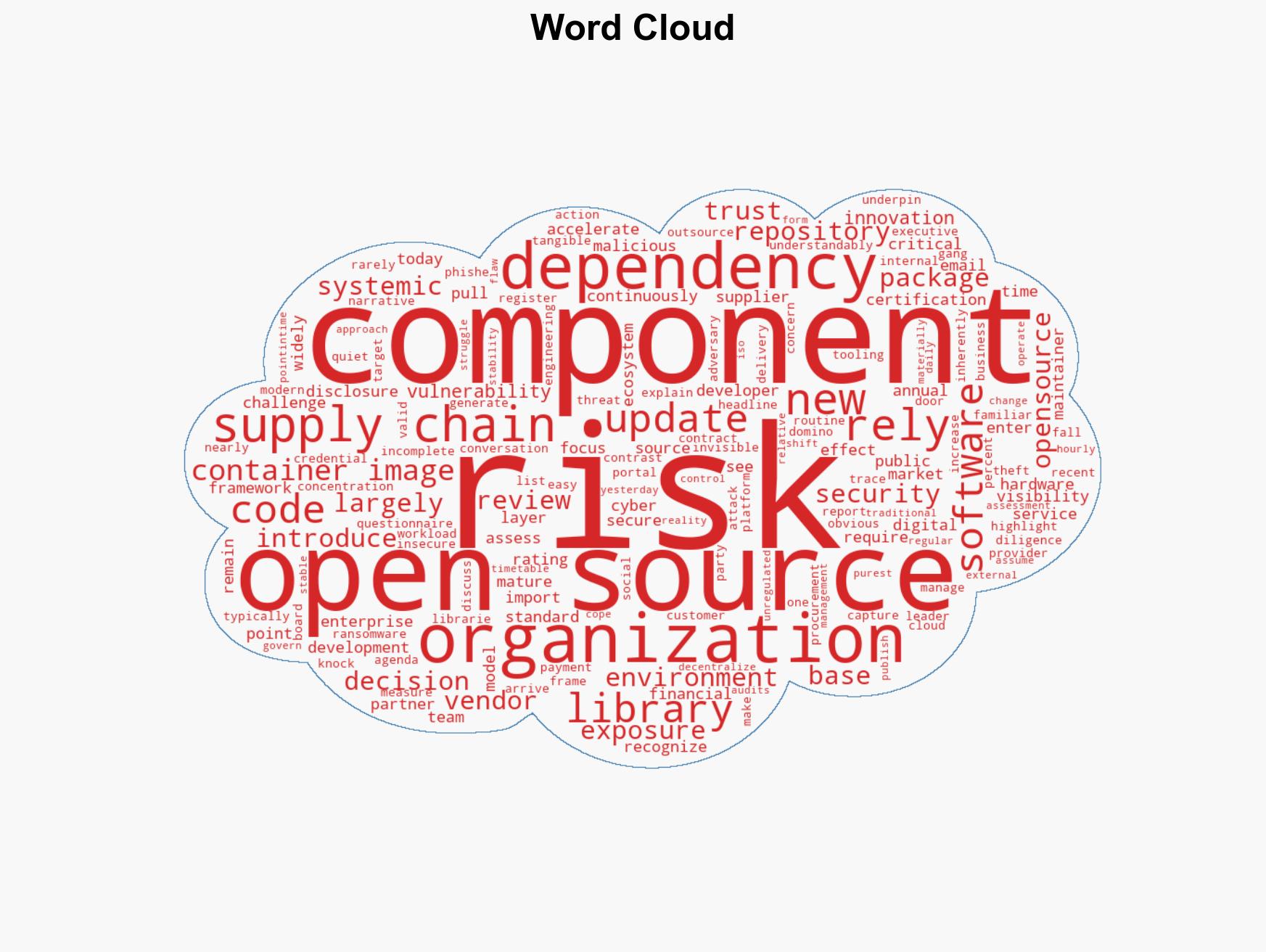
Overlooked Open Source Risks Threaten Supply Chain Security Amid Rising Cyber Attacks
Published on: 2026-03-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: The open source blind spot in our supply chains
1. BLUF (Bottom Line Up Front)
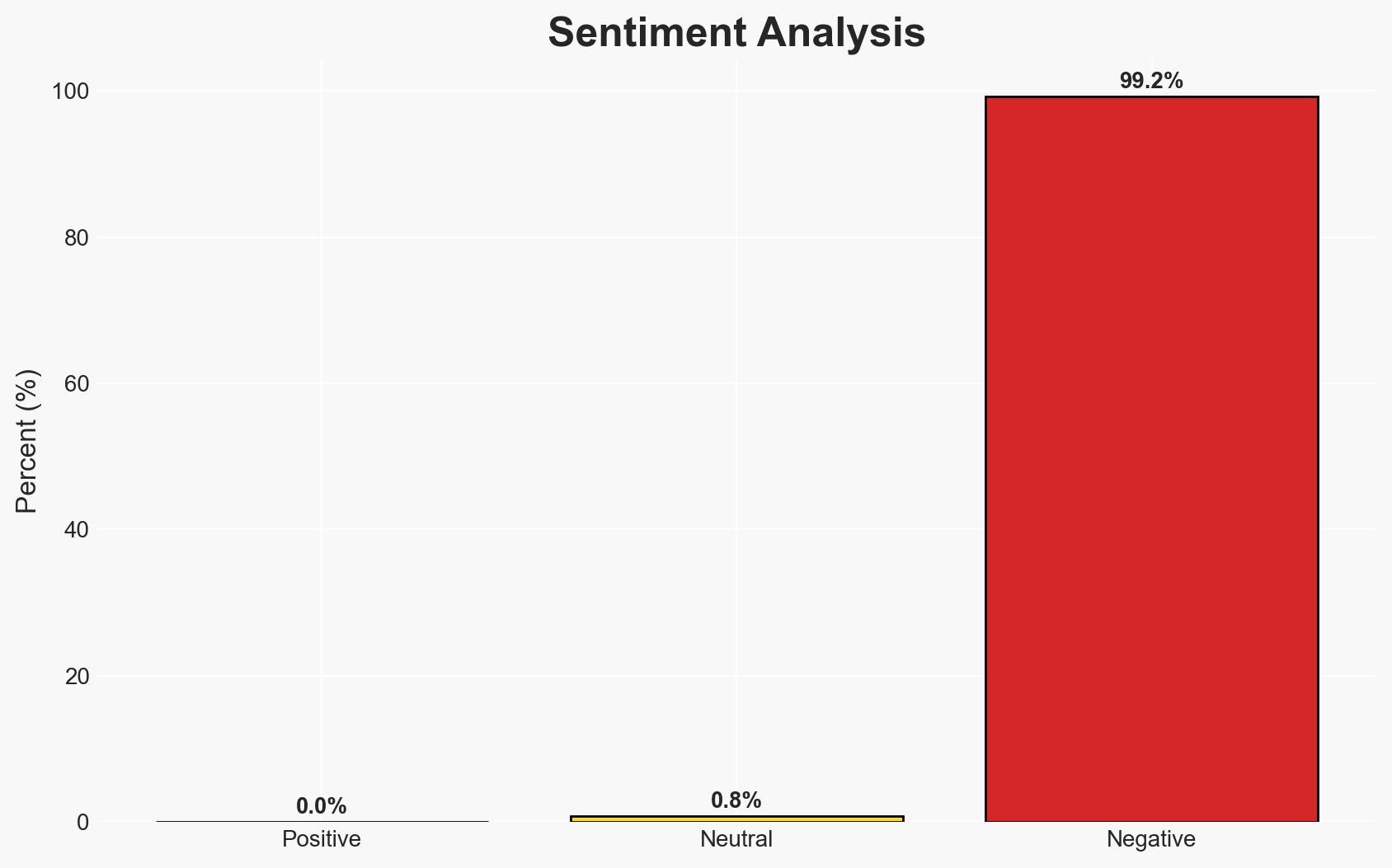
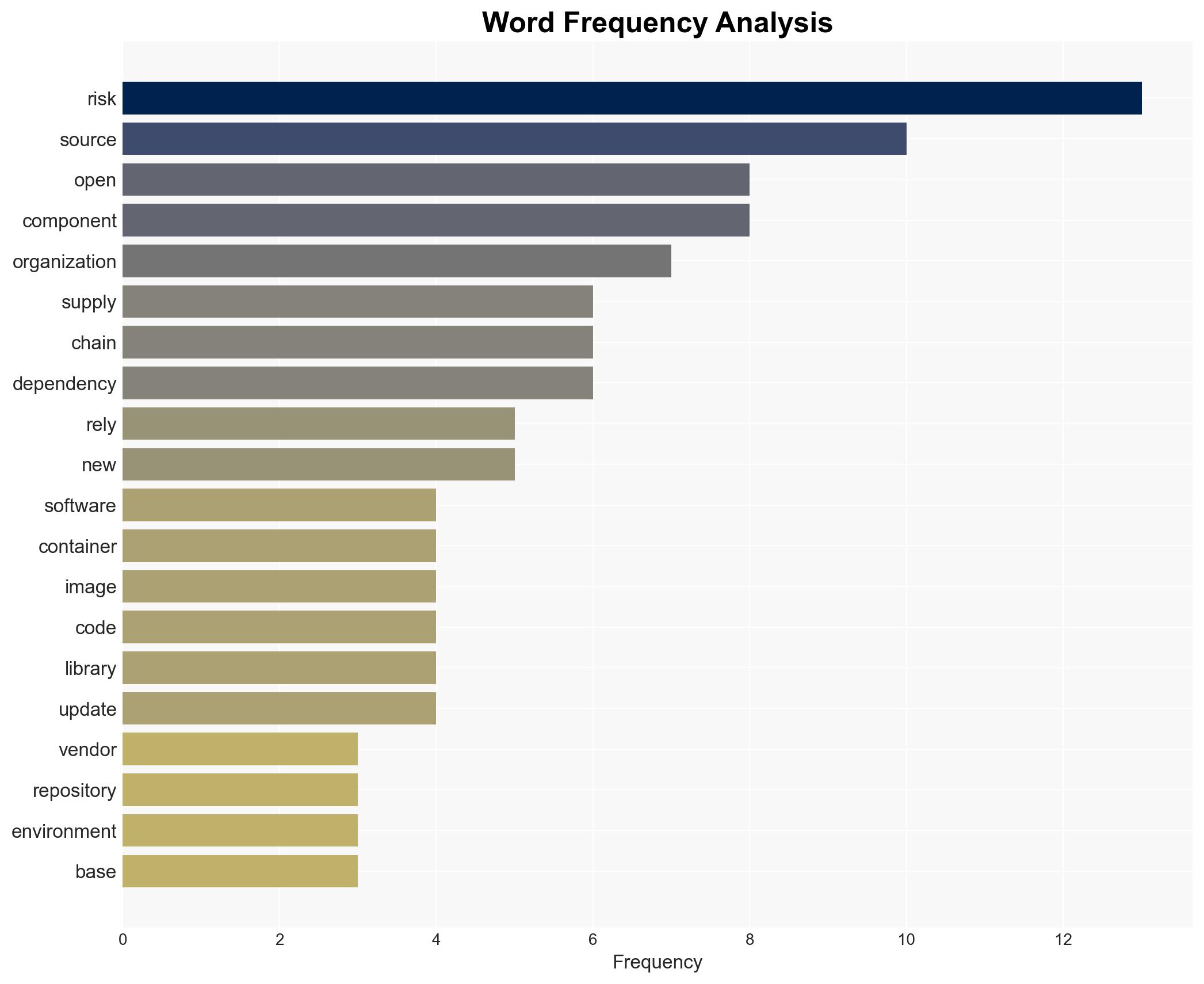
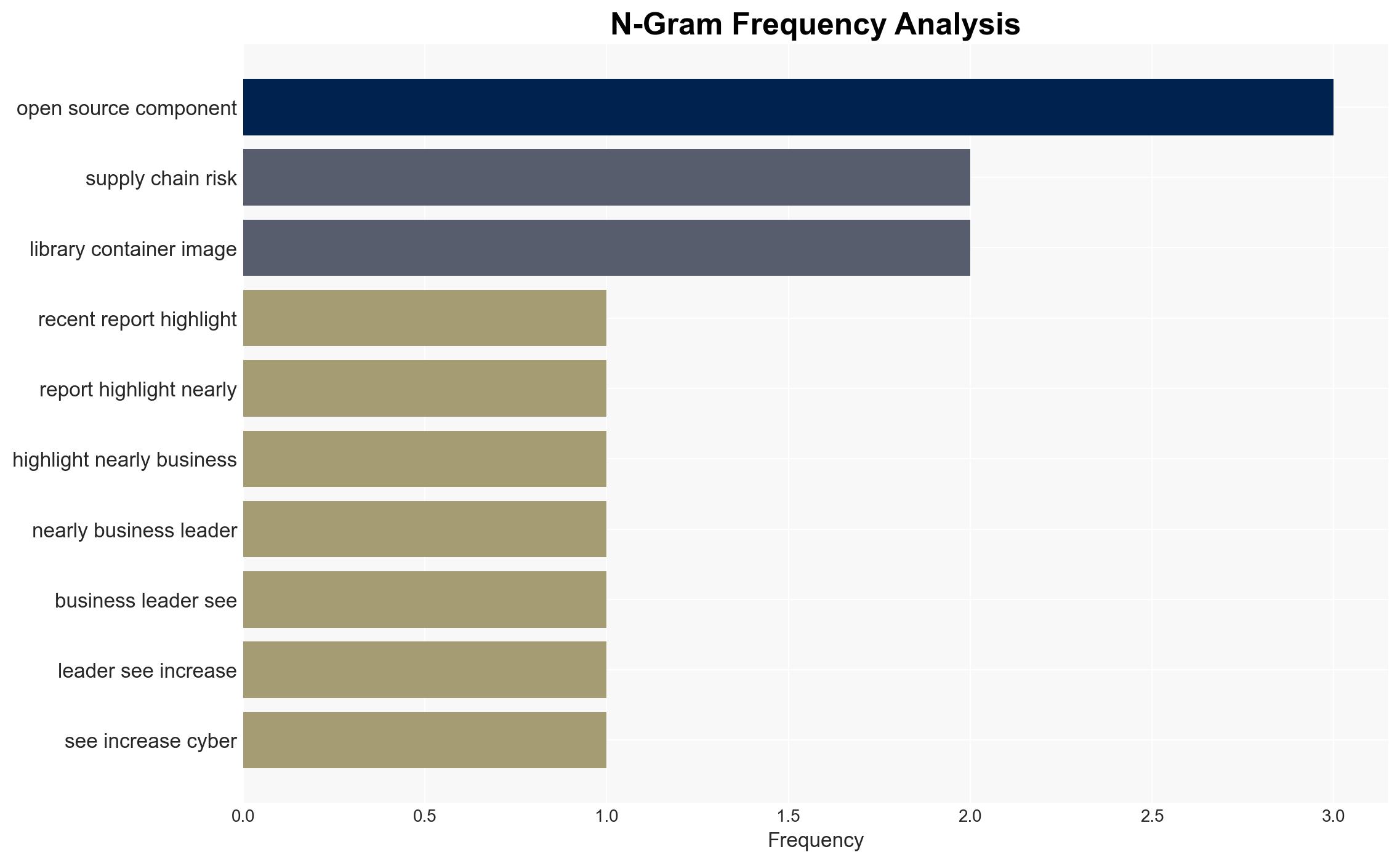
The increasing reliance on open source software components in supply chains presents a significant, yet often overlooked, cybersecurity risk. This risk is exacerbated by the decentralized and unregulated nature of open source ecosystems, which traditional risk management models fail to adequately address. Organizations across various sectors are affected, with moderate confidence in the assessment that this risk will continue to grow if not properly managed.
2. Competing Hypotheses
- Hypothesis A: The primary risk in supply chains is from traditional managed service providers and hardware dependencies. Evidence includes the focus of current risk management practices and the visibility of these risks in board discussions. However, this hypothesis overlooks the systemic risk posed by open source components.
- Hypothesis B: Open source software components represent a critical and underappreciated risk in supply chains. This is supported by the widespread use of open source in digital services and the lack of governance over these components. Contradictory evidence is limited, but includes the absence of high-profile incidents directly attributed to open source vulnerabilities.
- Assessment: Hypothesis B is currently better supported due to the pervasive use of open source software and the inherent challenges in monitoring and controlling these components. Indicators such as increased cyber incidents linked to open source vulnerabilities could further support this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will continue to rely heavily on open source components; traditional risk management models remain unchanged; cyber threats will increasingly target supply chain vulnerabilities.
- Information Gaps: Detailed data on the frequency and impact of open source-related security incidents; comprehensive mapping of open source dependencies within critical infrastructure.
- Bias & Deception Risks: Potential bias in underestimating open source risks due to lack of visibility; risk of manipulation by adversaries exploiting open source vulnerabilities without detection.
4. Implications and Strategic Risks
The continued neglect of open source risks could lead to significant vulnerabilities in national and corporate cybersecurity postures. As these risks evolve, they may interact with broader geopolitical and economic dynamics.
- Political / Geopolitical: Potential for state actors to exploit open source vulnerabilities for espionage or sabotage, escalating geopolitical tensions.
- Security / Counter-Terrorism: Increased risk of cyber attacks on critical infrastructure, potentially disrupting essential services.
- Cyber / Information Space: Growing threat landscape as adversaries target open source dependencies; potential for misinformation campaigns exploiting open source vulnerabilities.
- Economic / Social: Economic disruptions from cyber incidents affecting supply chains; potential loss of trust in digital services impacting social cohesion.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of open source dependencies; conduct rapid assessments of critical systems for open source vulnerabilities.
- Medium-Term Posture (1–12 months): Develop partnerships with open source communities for better threat intelligence; invest in automated tools for real-time vulnerability detection.
- Scenario Outlook:
- Best: Improved governance and monitoring reduce open source risks significantly.
- Worst: Major cyber incident exploiting open source vulnerabilities causes widespread disruption.
- Most-Likely: Incremental improvements in risk management, but open source risks remain a persistent challenge.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, supply chain risk, open source software, digital infrastructure, risk management, cyber threats, software vulnerabilities
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us