Seed Phrase Exposure Triggers $176 Million Bitcoin Theft in UK High Court Case
Published on: 2026-03-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: How a seed phrase leak led to a 176M Bitcoin theft case
1. BLUF (Bottom Line Up Front)
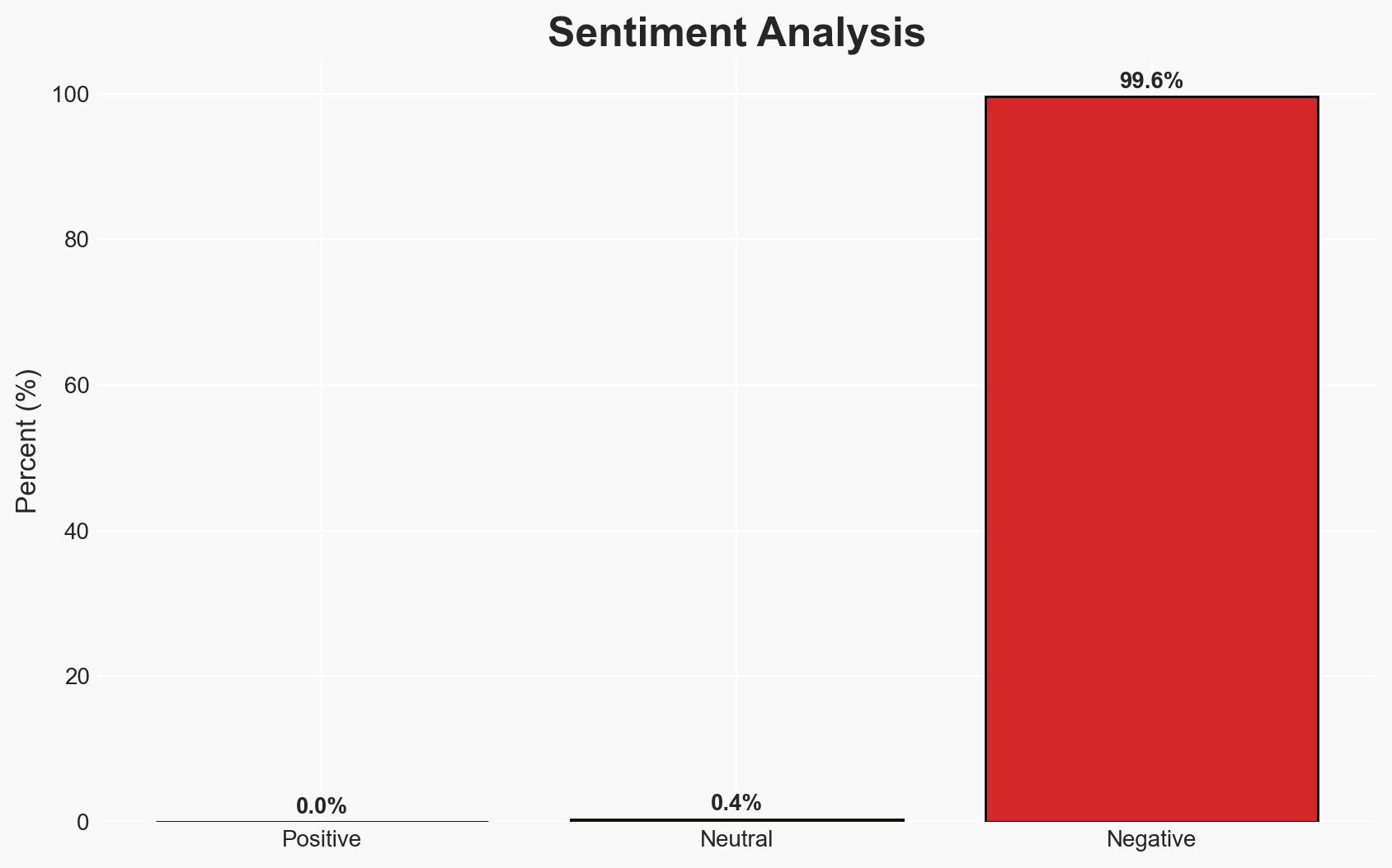
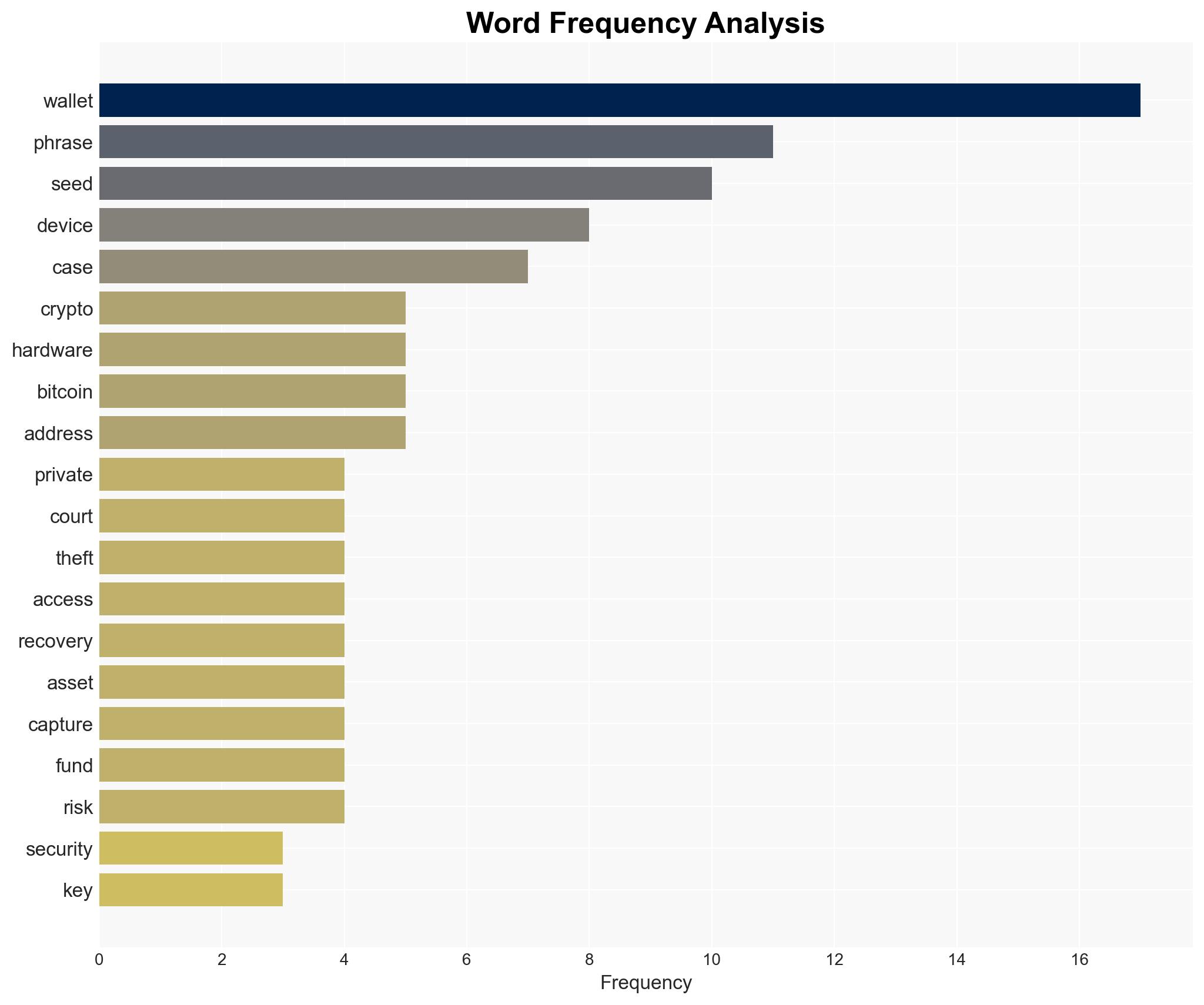
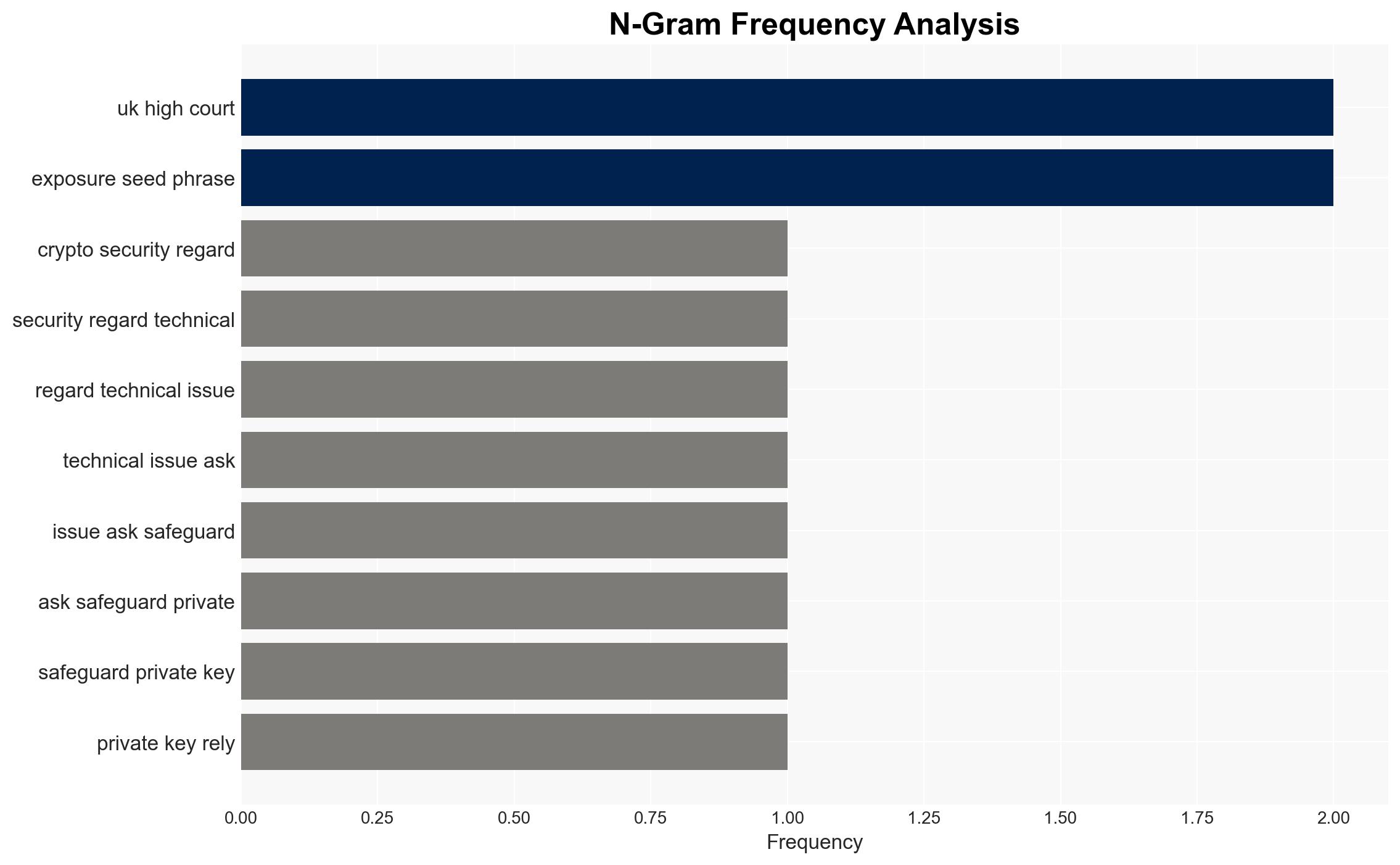
The alleged theft of 2,323 Bitcoin, valued at approximately $176 million, highlights a critical vulnerability in cryptocurrency security: the exposure of seed phrases. The case involves a personal dispute leading to the alleged unauthorized access and transfer of assets. Moderate confidence is placed in the hypothesis that the theft was facilitated by covert surveillance rather than digital intrusion.
2. Competing Hypotheses
- Hypothesis A: The theft was executed through covert surveillance of the seed phrase, involving physical observation or recording. This is supported by the absence of digital intrusion evidence and the reported use of recording devices. Uncertainties include the precise method and timing of the surveillance.
- Hypothesis B: The theft involved some form of digital compromise or insider assistance, despite the lack of direct evidence. This hypothesis is contradicted by the lack of malware or phishing activity and the focus on physical capture methods.
- Assessment: Hypothesis A is currently better supported due to the specific allegations of visual or audio capture and the lack of digital intrusion indicators. Key indicators that could shift this judgment include new evidence of digital compromise or insider involvement.
3. Key Assumptions and Red Flags
- Assumptions: The seed phrase was not shared willingly by the owner; the accused individuals had the capability to execute the surveillance; the hardware wallet functioned as intended without technical failure.
- Information Gaps: Details on the exact method of surveillance, the timeline of events, and the involvement of any additional parties are lacking.
- Bias & Deception Risks: Potential bias in the claimant’s narrative due to personal disputes; risk of deception in the accused parties’ statements or actions to mislead investigators.
4. Implications and Strategic Risks
This development underscores the need for enhanced security measures around seed phrase management and highlights potential vulnerabilities in personal and financial security practices.
- Political / Geopolitical: Limited direct political implications, but potential for regulatory scrutiny on cryptocurrency security practices.
- Security / Counter-Terrorism: No immediate counter-terrorism implications, but highlights the importance of physical security in safeguarding digital assets.
- Cyber / Information Space: Raises awareness of non-digital attack vectors in cyber security, emphasizing the need for comprehensive security protocols.
- Economic / Social: Potential impact on public trust in cryptocurrency security, influencing market stability and adoption rates.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of similar cases; enhance public awareness campaigns on seed phrase security; engage with law enforcement for case updates.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms to improve physical security measures; advocate for industry standards on seed phrase management.
- Scenario Outlook:
- Best: Enhanced security measures lead to reduced incidents of similar thefts.
- Worst: Continued vulnerabilities result in increased thefts and decreased trust in cryptocurrency.
- Most-Likely: Incremental improvements in security practices with ongoing incidents highlighting gaps.
6. Key Individuals and Entities
- Ping Fai Yuen (Claimant)
- Fun Yung Li (Accused)
- Not clearly identifiable from open sources in this snippet (Other involved parties)
7. Thematic Tags
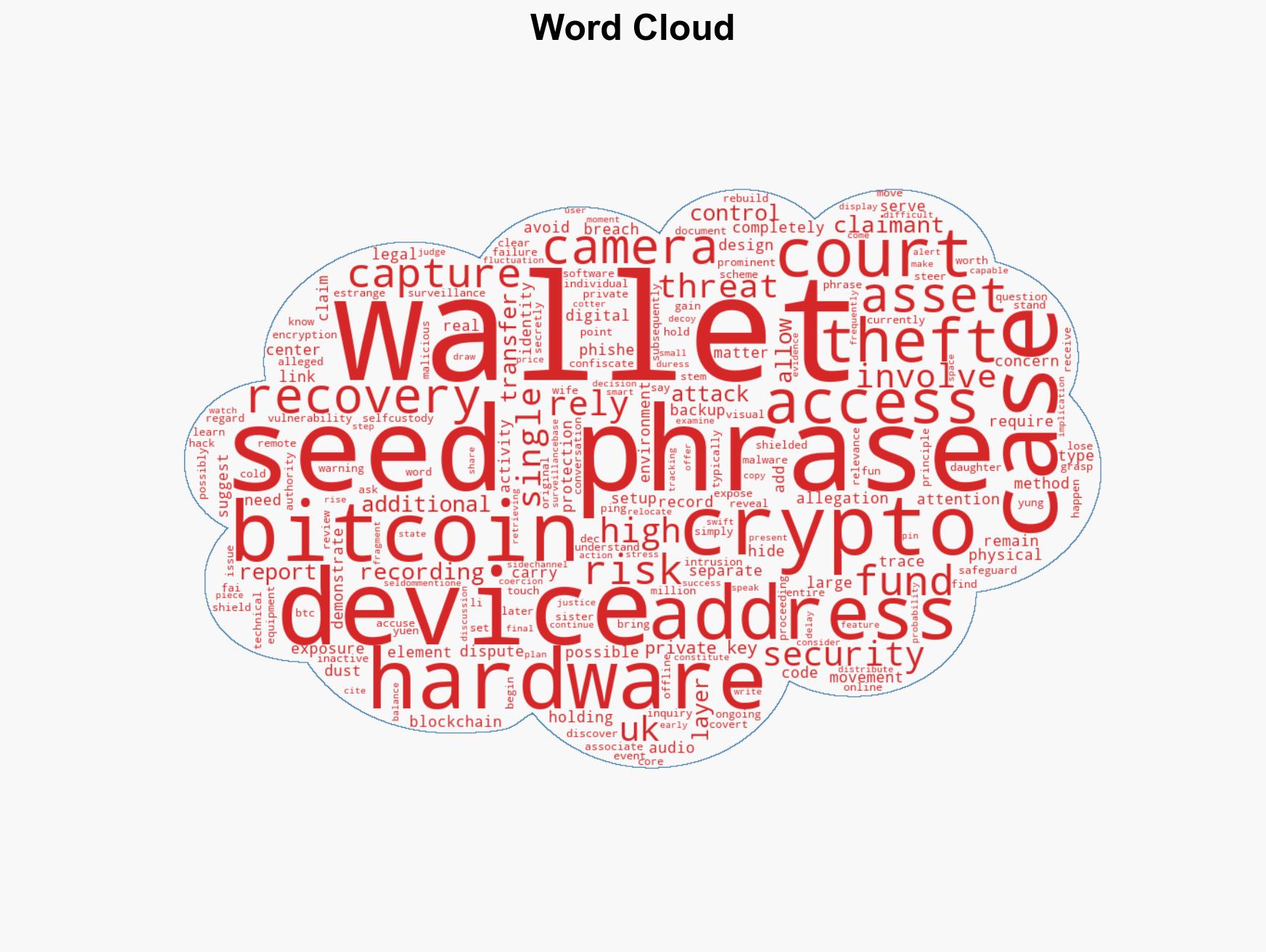
cybersecurity, cryptocurrency security, seed phrase vulnerability, cyber security, financial crime, surveillance, personal security, blockchain technology
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us