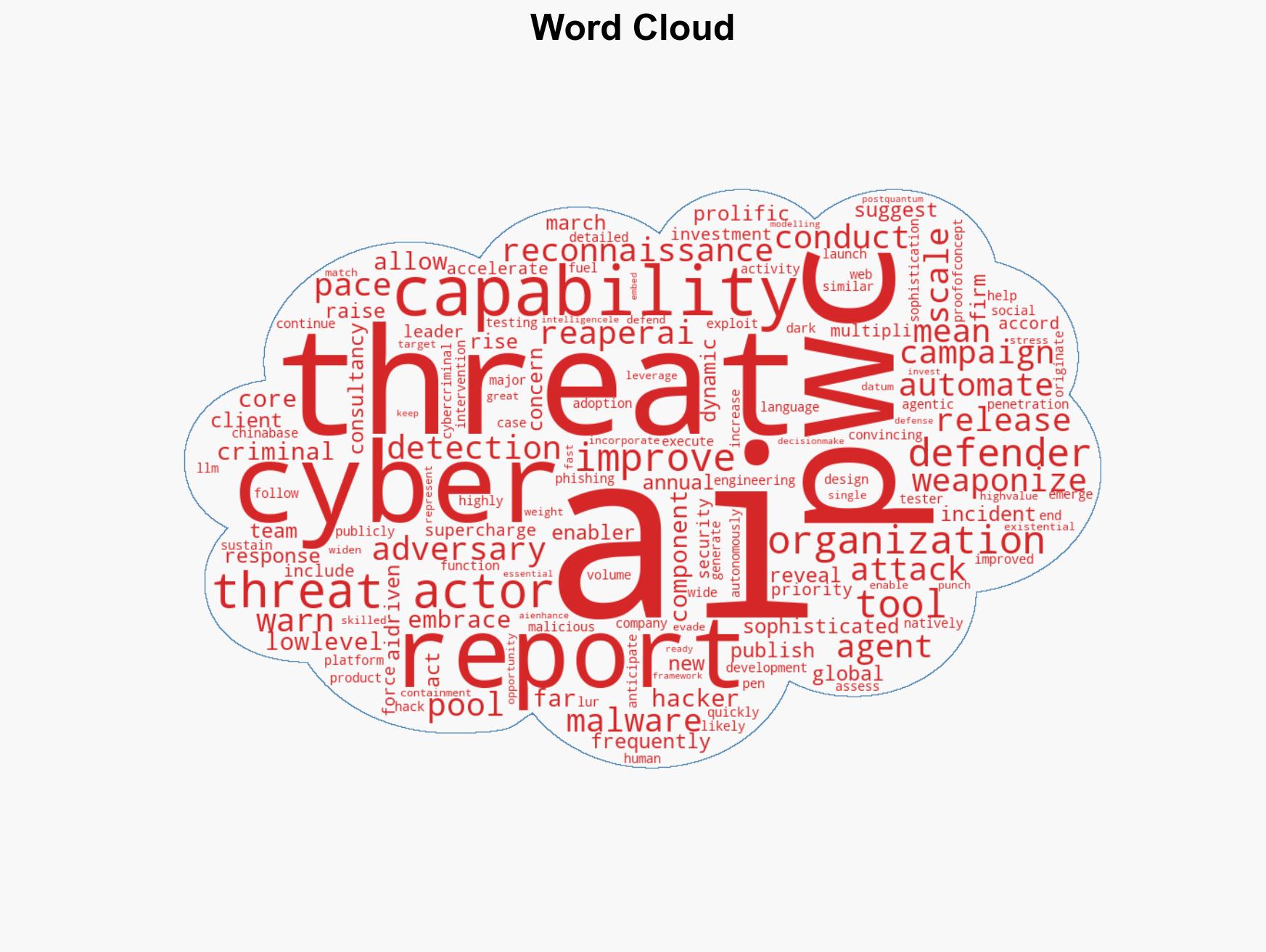
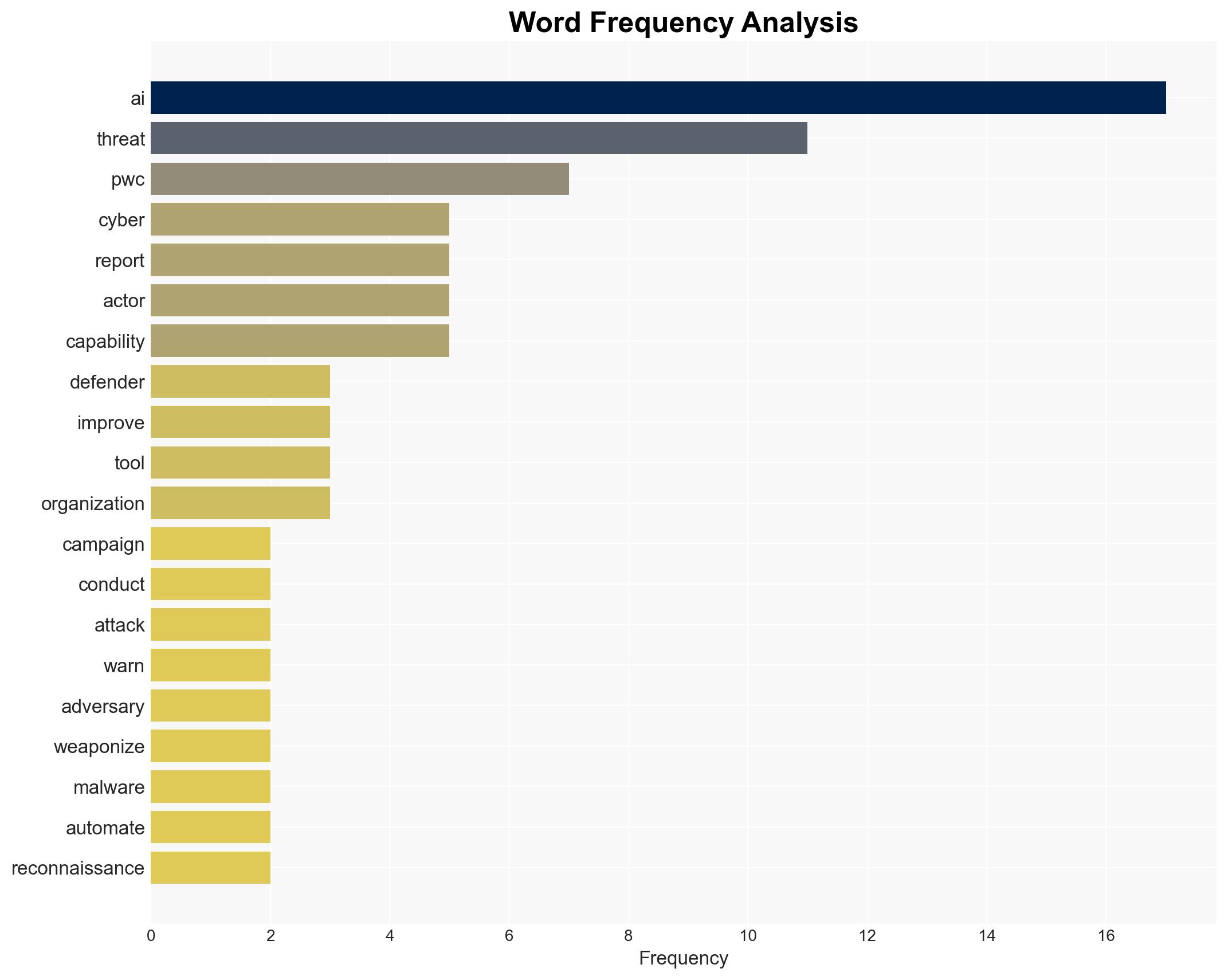
Cybersecurity Leaders Prioritize AI as Cybercriminals Leverage Technology for Advanced Attacks, PwC Reports
Published on: 2026-03-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: AI Becomes the Top Cybersecurity Priority for Defenders as Criminals Exploit It PwC Warns
1. BLUF (Bottom Line Up Front)
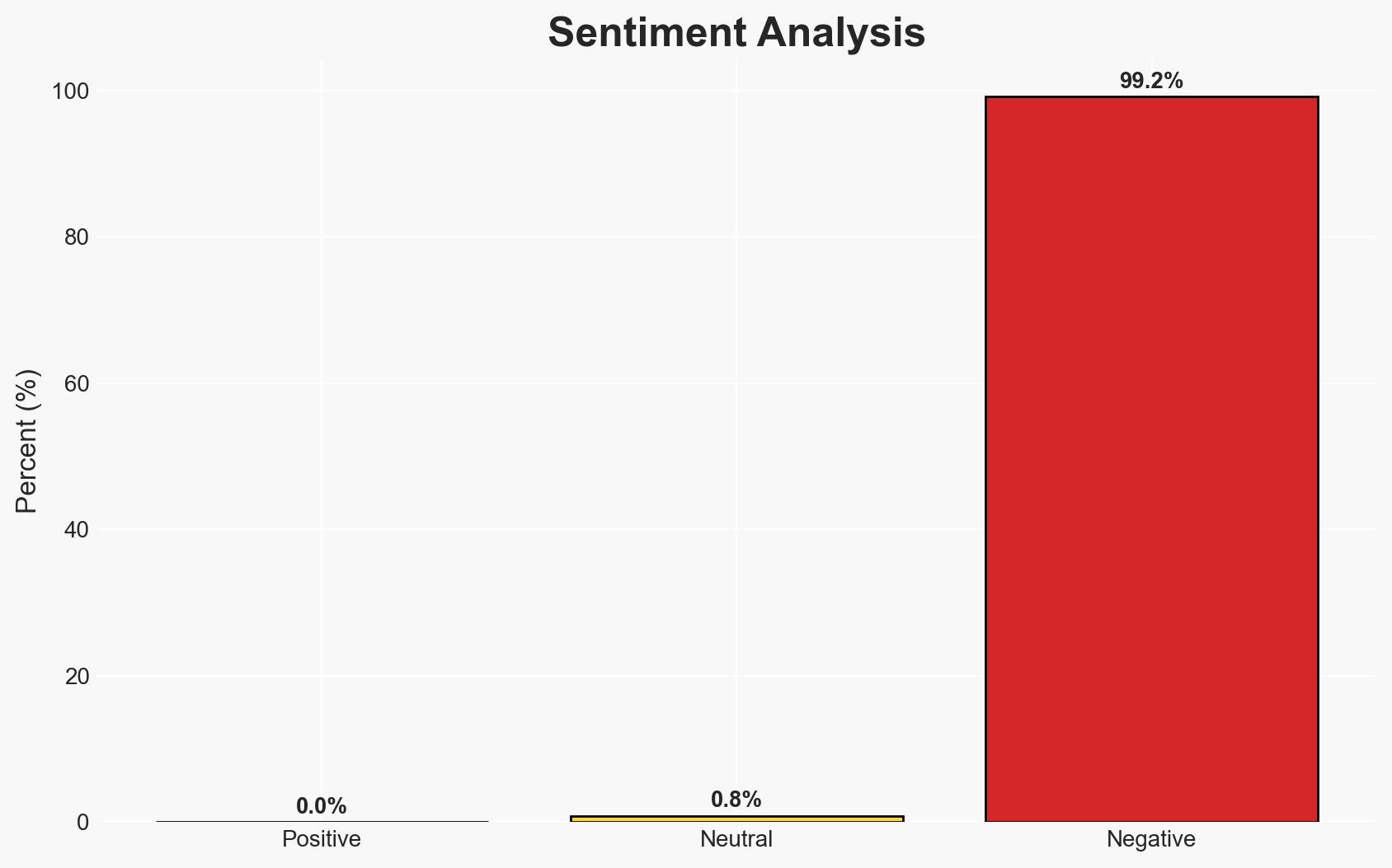
The integration of AI into cyber operations is significantly enhancing both offensive and defensive capabilities, with AI-driven threats becoming a primary concern for cybersecurity stakeholders. The dual-use nature of AI presents both risks and opportunities, necessitating strategic investments in AI-enhanced defenses. This assessment is made with moderate confidence due to existing information gaps and potential biases in reporting.
2. Competing Hypotheses
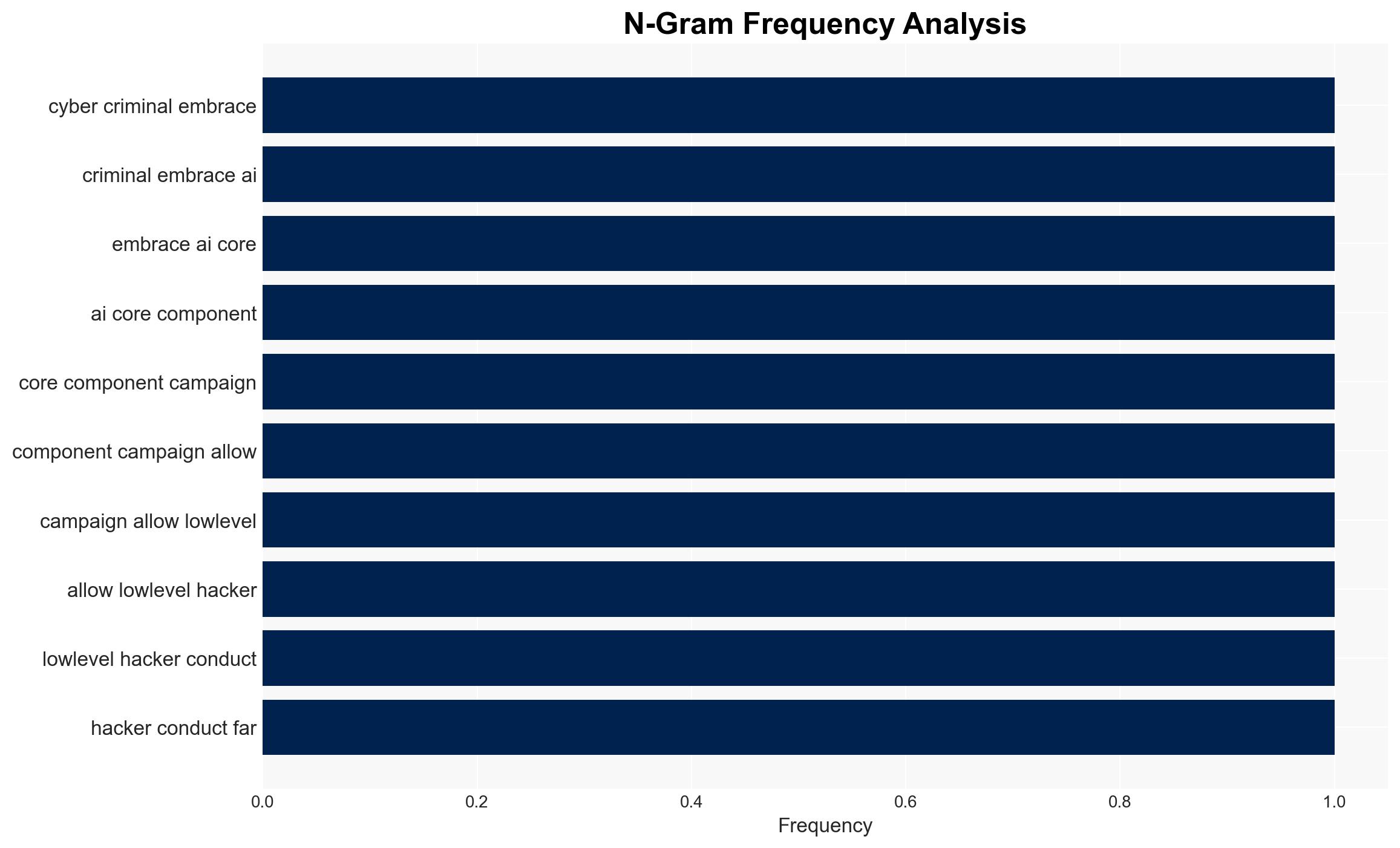
- Hypothesis A: AI is primarily a threat multiplier for cyber adversaries, enabling a broader range of actors to execute sophisticated attacks. This is supported by the reported use of AI to automate reconnaissance and develop advanced malware. However, the extent of AI’s impact on the threat landscape remains uncertain due to potential exaggeration of capabilities.
- Hypothesis B: AI serves as a critical enabler for cybersecurity defenses, allowing for faster threat detection and response. PwC’s emphasis on AI as a top investment priority for defenders supports this view, although the effectiveness of these AI tools in real-world scenarios is not fully validated.
- Assessment: Hypothesis B is currently better supported, as the strategic focus on AI for defense by cybersecurity leaders suggests a proactive stance. However, indicators such as successful AI-driven attacks could shift this judgment towards Hypothesis A.
3. Key Assumptions and Red Flags
- Assumptions: AI capabilities will continue to advance rapidly; cybersecurity stakeholders will have access to necessary AI tools; threat actors will prioritize AI integration.
- Information Gaps: Detailed case studies of AI-driven attacks and defenses; quantitative data on AI’s impact on attack success rates.
- Bias & Deception Risks: Potential over-reliance on PwC’s analysis; confirmation bias towards AI as a solution; possible exaggeration of AI capabilities by vendors.
4. Implications and Strategic Risks
The dual-use nature of AI in cybersecurity could lead to an arms race in AI capabilities, influencing global cyber norms and regulations.
- Political / Geopolitical: Increased tensions as states leverage AI for cyber operations, potentially leading to calls for international AI governance frameworks.
- Security / Counter-Terrorism: Enhanced threat landscape with more actors capable of sophisticated attacks, challenging traditional defense mechanisms.
- Cyber / Information Space: Proliferation of AI-driven tools may lead to more frequent and complex cyber incidents, necessitating advanced threat intelligence capabilities.
- Economic / Social: Potential economic impacts from successful AI-driven cyber attacks on critical infrastructure; societal concerns over privacy and AI ethics.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of AI-driven threat activities; initiate AI capability assessments within cybersecurity frameworks.
- Medium-Term Posture (1–12 months): Develop partnerships with AI research entities; invest in AI talent and training for cybersecurity teams.
- Scenario Outlook:
- Best: Effective AI defenses mitigate threats, leading to reduced cyber incidents.
- Worst: AI-driven attacks overwhelm defenses, causing significant disruptions.
- Most-Likely: Gradual improvement in AI defenses with periodic successful AI-driven attacks.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, AI integration, threat intelligence, cyber defense, AI ethics, cyber norms, digital transformation
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us