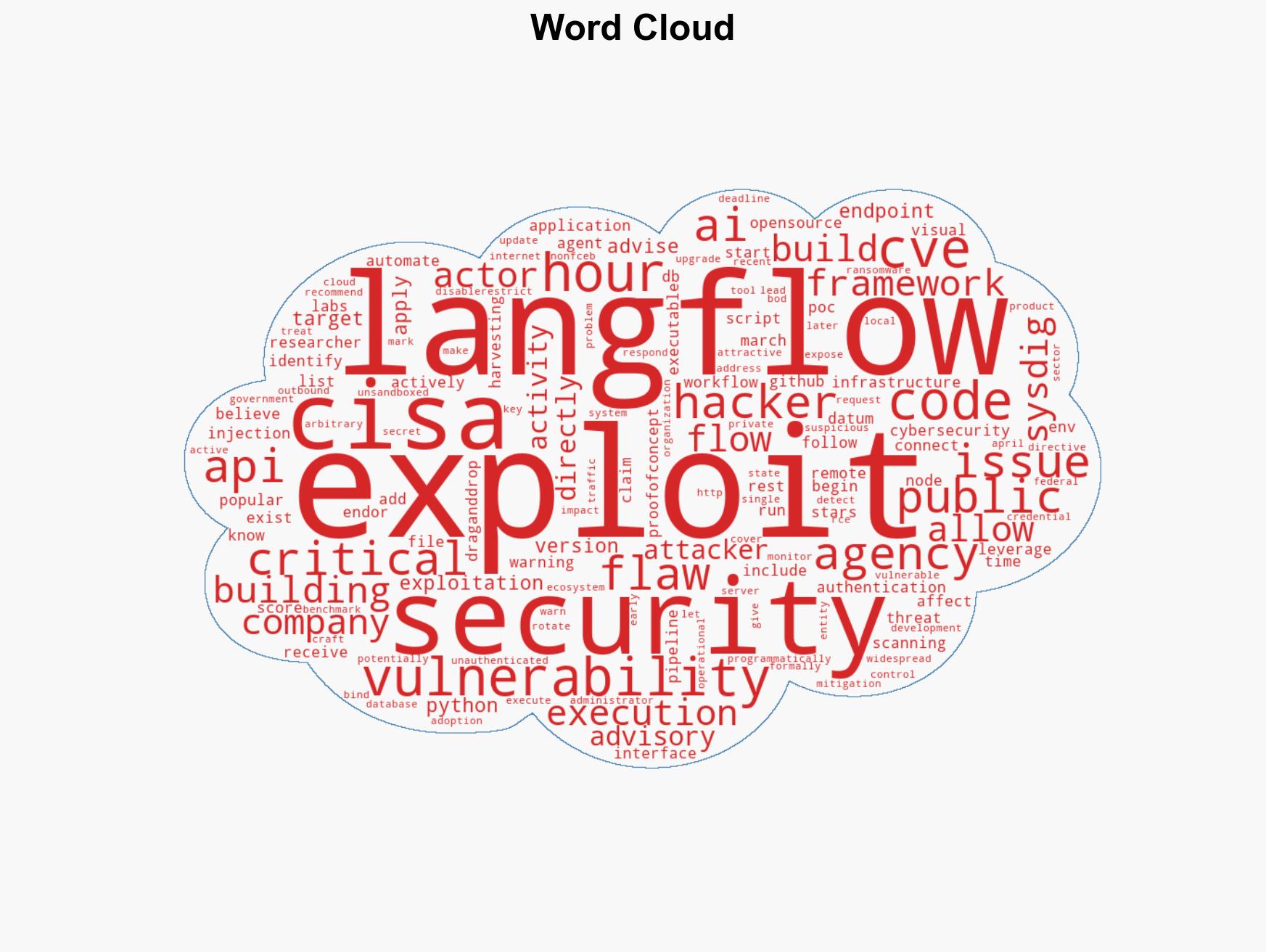
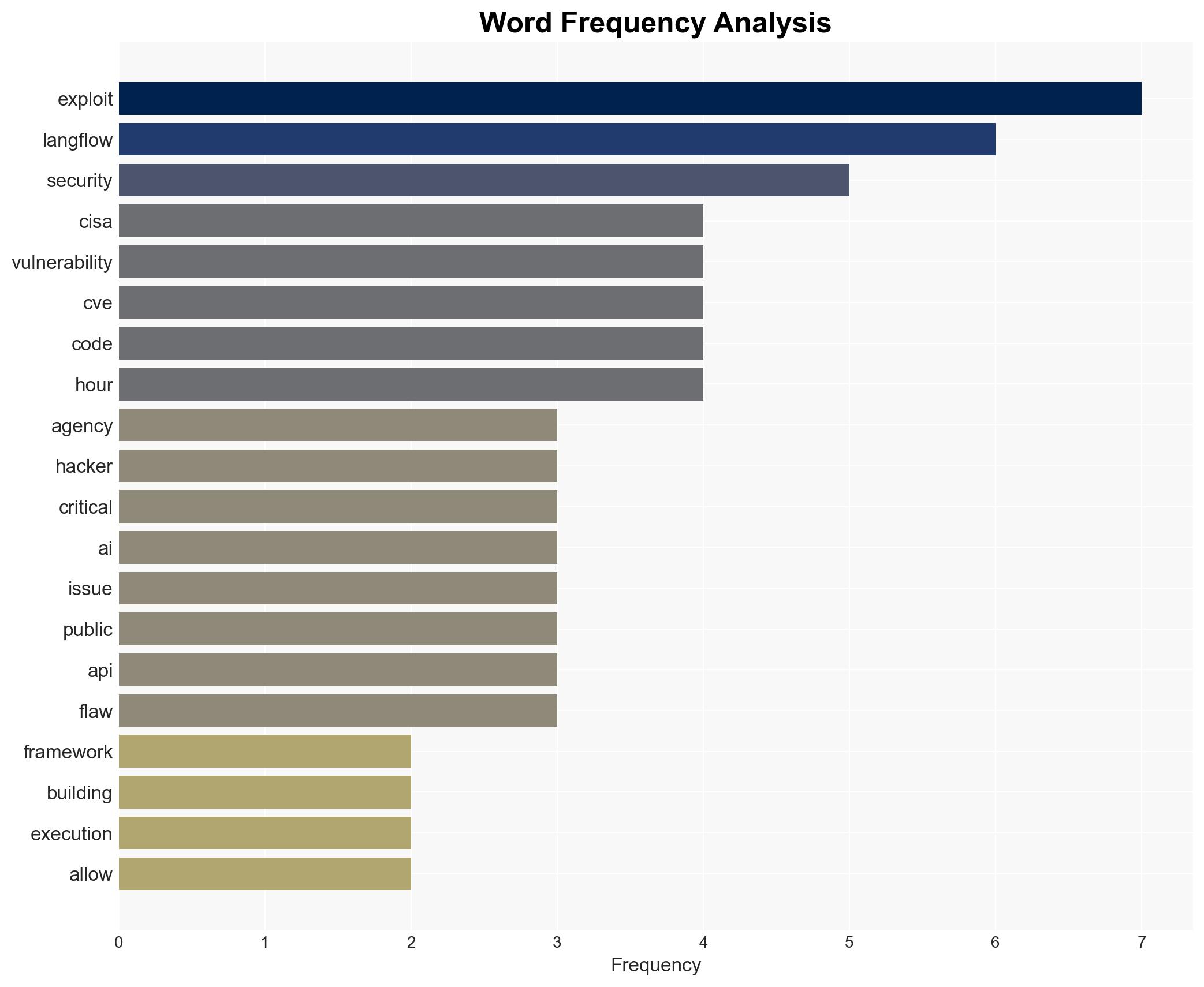
CISA Alerts on Exploitation of Critical Langflow Vulnerability for AI Workflow Hijacking
Published on: 2026-03-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: CISA New Langflow flaw actively exploited to hijack AI workflows
1. BLUF (Bottom Line Up Front)
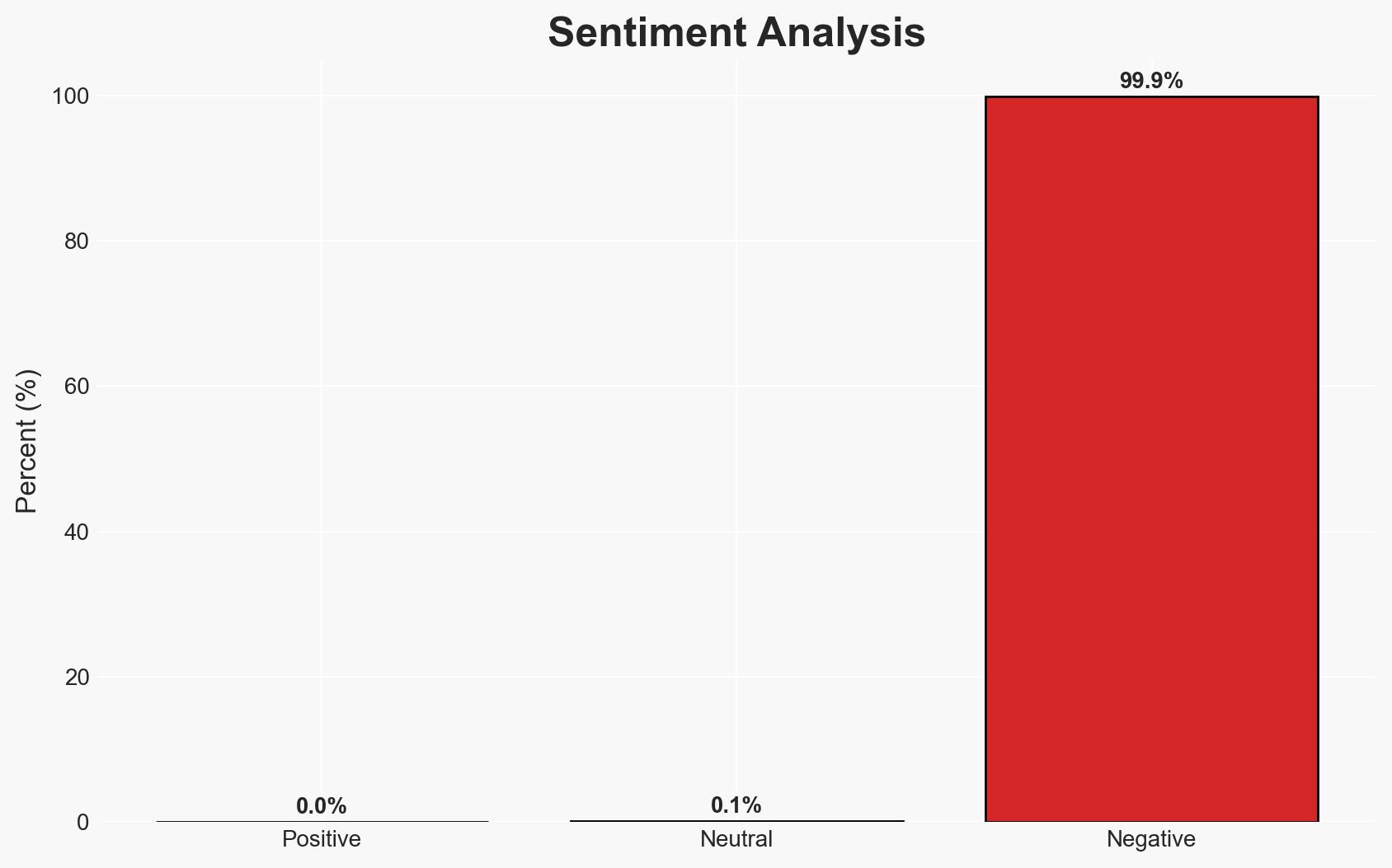
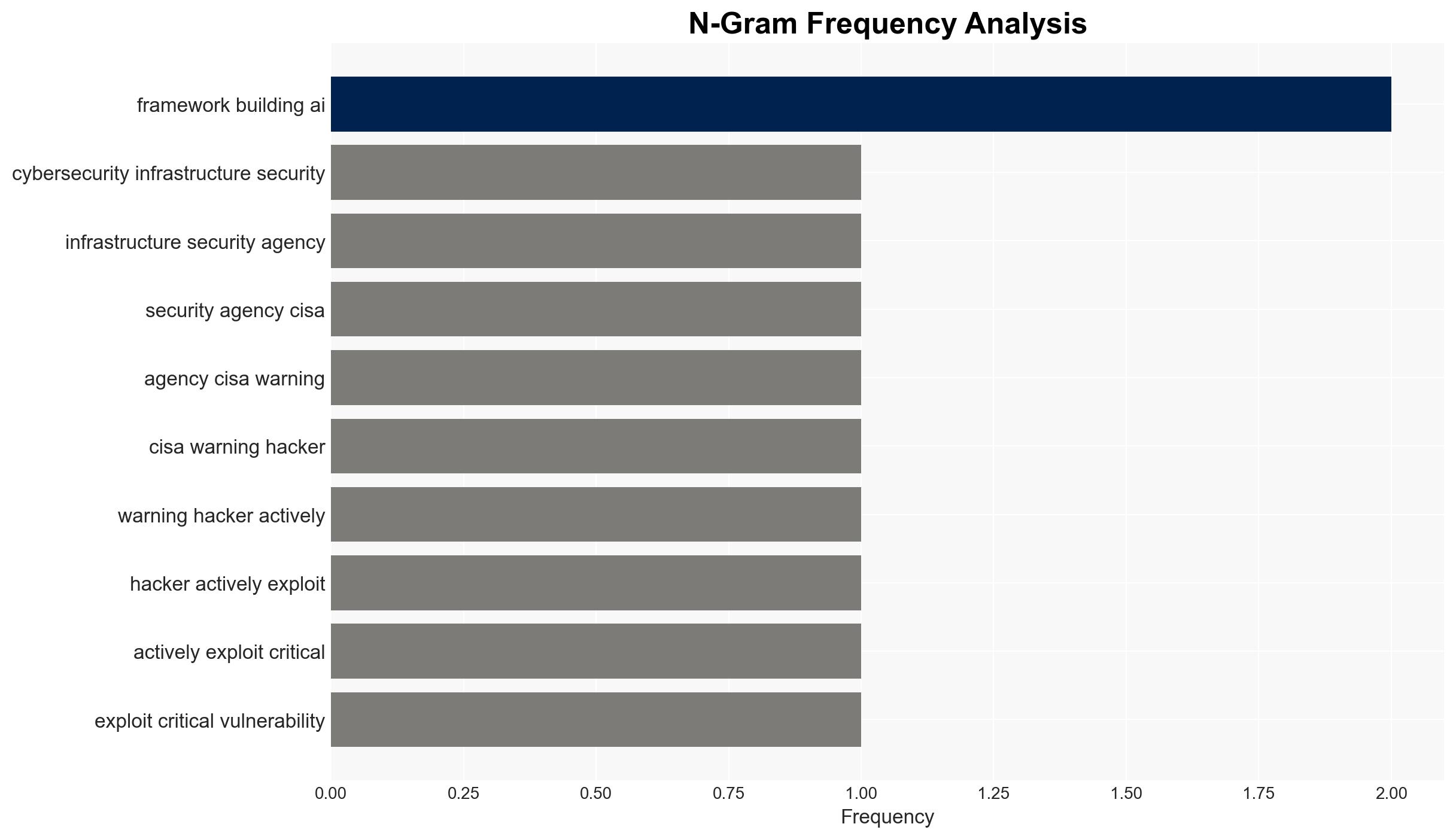
The exploitation of CVE-2026-33017 in the Langflow framework poses a significant cybersecurity threat, allowing unauthorized remote code execution. This vulnerability affects AI development environments, with potential widespread impact on both public and private sectors. The most likely hypothesis is that attackers are leveraging the flaw for data exfiltration and unauthorized access. Overall confidence in this assessment is moderate, given the rapid exploitation timeline and lack of public PoC.
2. Competing Hypotheses
- Hypothesis A: Attackers are exploiting CVE-2026-33017 primarily for data exfiltration and unauthorized access to sensitive environments. This is supported by the rapid timeline of exploitation and the lack of ransomware activity, suggesting a focus on stealth and data acquisition. However, the absence of detailed attribution or specific targets introduces uncertainty.
- Hypothesis B: The exploitation is a precursor to broader ransomware campaigns, with initial data exfiltration serving as reconnaissance. This is less supported due to CISA’s non-association with ransomware actors and the lack of immediate ransom demands, but remains plausible given historical patterns of similar exploits.
- Assessment: Hypothesis A is currently better supported due to the rapid exploitation timeline and focus on data harvesting. Indicators such as increased ransomware activity linked to this vulnerability could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Attackers have the technical capability to exploit the vulnerability without public PoC; Langflow’s widespread use increases the attractiveness of the target; CISA’s advisories accurately reflect the threat landscape.
- Information Gaps: Specific threat actor attribution; detailed impact on affected organizations; long-term intentions of the attackers.
- Bias & Deception Risks: Potential over-reliance on initial reports from Sysdig and Endor Labs; possibility of misinformation or disinformation campaigns by threat actors to obscure true intentions.
4. Implications and Strategic Risks
This development could lead to increased scrutiny and regulation of AI development frameworks, impacting innovation and collaboration. The vulnerability’s exploitation may prompt enhanced cybersecurity measures across sectors, influencing both policy and operational practices.
- Political / Geopolitical: Potential for increased international cooperation on cybersecurity standards; risk of diplomatic tensions if state-sponsored actors are implicated.
- Security / Counter-Terrorism: Heightened threat environment for AI development sectors; possible targeting of critical infrastructure if AI workflows are compromised.
- Cyber / Information Space: Increased cyber espionage activities; potential for misinformation campaigns leveraging AI workflow disruptions.
- Economic / Social: Potential economic impact on companies reliant on Langflow; increased costs for cybersecurity enhancements and incident response.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urge organizations to apply patches or mitigations; monitor for signs of exploitation; restrict internet exposure of Langflow instances.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing; invest in AI security research and development; enhance incident response capabilities.
- Scenario Outlook:
- Best Case: Vulnerability is fully mitigated with no significant breaches, leading to improved security practices.
- Worst Case: Widespread exploitation results in significant data breaches and operational disruptions.
- Most Likely: Continued targeted exploitation with gradual improvements in defensive measures and threat intelligence.
6. Key Individuals and Entities
- Cybersecurity and Infrastructure Security Agency (CISA)
- Sysdig (Application Security Company)
- Endor Labs
- Langflow (AI Workflow Framework)
7. Thematic Tags
cybersecurity, AI workflows, remote code execution, data exfiltration, vulnerability management, threat intelligence, open-source security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us