Emerging Threats: Russia and China Lead in Electromagnetic Warfare, Leaving U.S. Forces Vulnerable
Published on: 2026-03-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
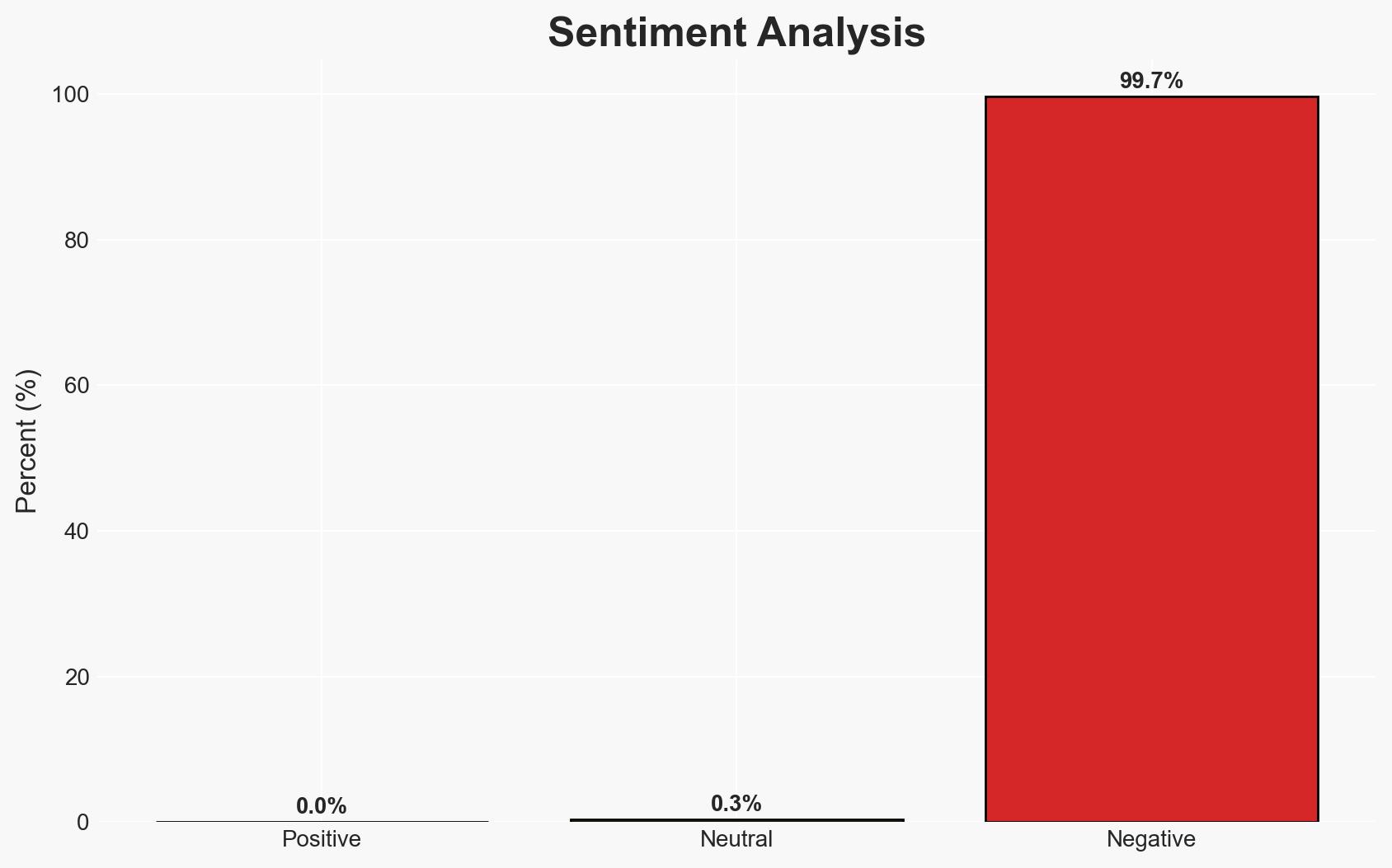
Intelligence Report: Shadows of the Electromagnetic Apocalypse A wake-up call to the invisible battlefield
1. BLUF (Bottom Line Up Front)
The report suggests that Russia and China have developed superior electromagnetic warfare capabilities, potentially rendering U.S. military technology obsolete. This poses a significant threat to Western military infrastructure and strategic stability. The analysis is presented with moderate confidence due to potential bias and lack of corroborative evidence.
2. Competing Hypotheses
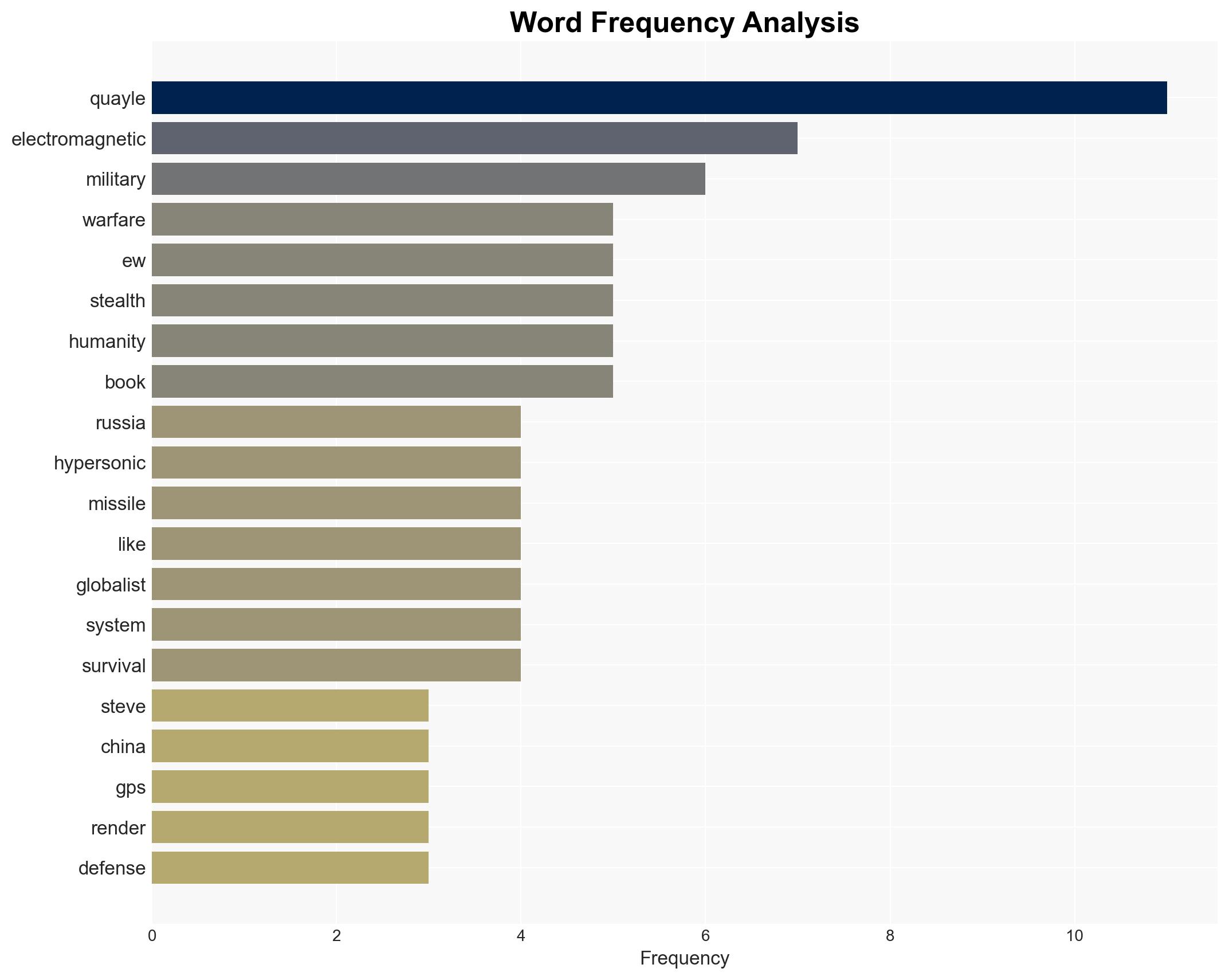
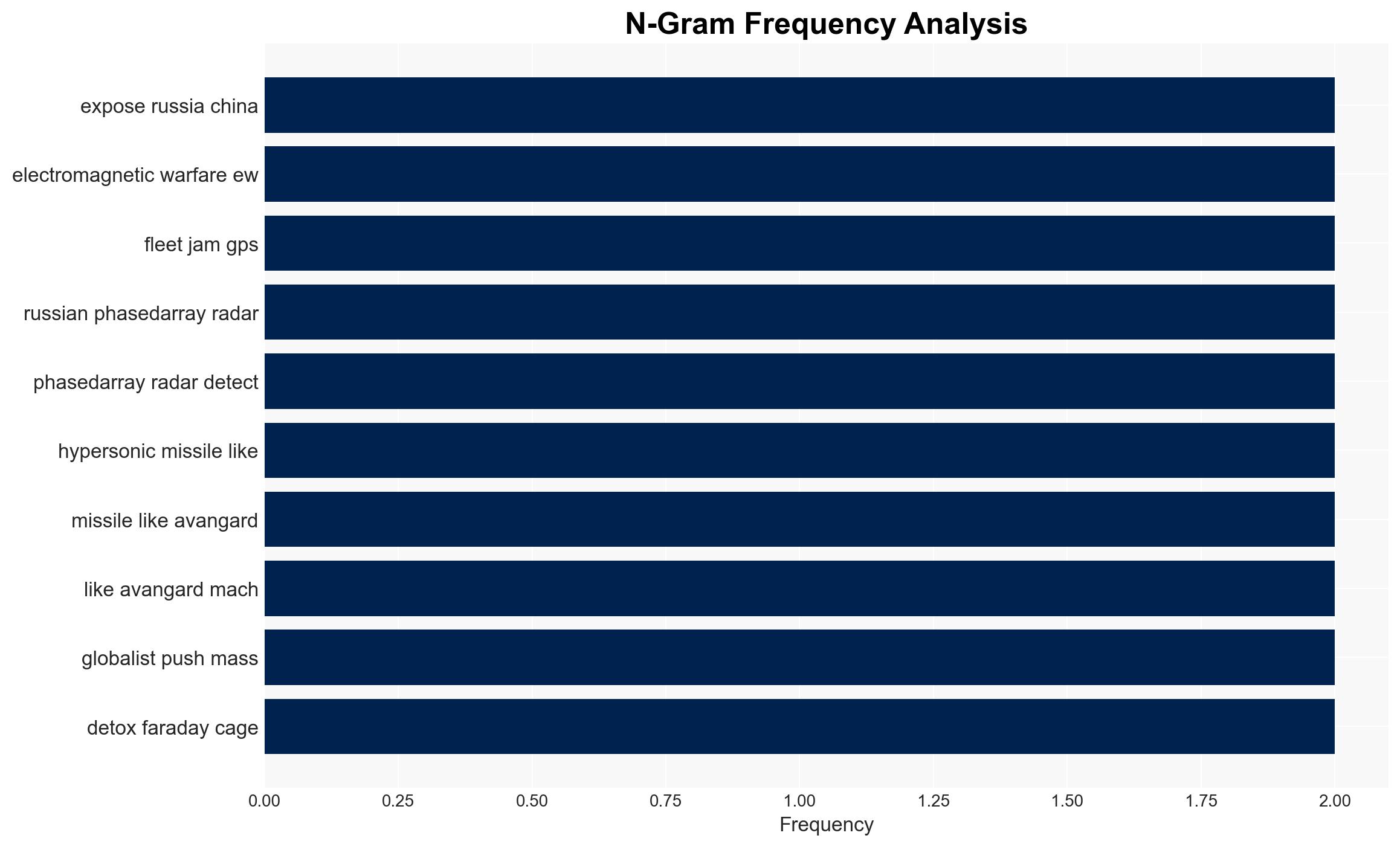
- Hypothesis A: Russia and China have indeed surpassed the U.S. in electromagnetic warfare capabilities, posing a direct threat to Western military dominance. This hypothesis is supported by reports of advanced Russian EW systems and hypersonic missile capabilities. However, it lacks independent verification and relies heavily on anecdotal evidence.
- Hypothesis B: The claims of Russian and Chinese superiority in EW are exaggerated, possibly as part of a psychological operation to induce strategic caution or panic within Western military circles. This hypothesis considers the possibility of misinformation and the absence of concrete, independently verified incidents.
- Assessment: Hypothesis A is currently better supported due to specific references to Russian EW systems and hypersonic capabilities, though this assessment could shift with new intelligence or verification of claims.
3. Key Assumptions and Red Flags
- Assumptions: The technological capabilities of Russia and China are accurately reported; Western military responses are not adequately adaptive; geopolitical tensions will continue to escalate.
- Information Gaps: Lack of independent verification of the reported EW incidents; insufficient data on U.S. countermeasures and technological advancements.
- Bias & Deception Risks: Potential bias from the source due to ideological perspectives; risk of exaggeration or misinformation intended to manipulate Western strategic decisions.
4. Implications and Strategic Risks
The development of advanced EW capabilities by Russia and China could lead to a strategic imbalance, prompting shifts in military alliances and defense postures.
- Political / Geopolitical: Increased tensions between NATO and Russia/China, potential for arms races or new military alliances.
- Security / Counter-Terrorism: Vulnerability of Western military assets could embolden adversarial actions or asymmetric warfare tactics.
- Cyber / Information Space: Potential for increased cyber operations targeting EW systems and misinformation campaigns to exploit perceived vulnerabilities.
- Economic / Social: Defense spending may increase, impacting economic priorities; public perception of security could shift, affecting social cohesion.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive assessment of U.S. EW capabilities and vulnerabilities; enhance intelligence sharing with allies.
- Medium-Term Posture (1–12 months): Invest in research and development to counter EW threats; strengthen alliances and joint exercises focusing on EW scenarios.
- Scenario Outlook: Best: Strengthened deterrence through technological parity; Worst: Strategic imbalance leading to conflict; Most-Likely: Continued technological competition with episodic tensions.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
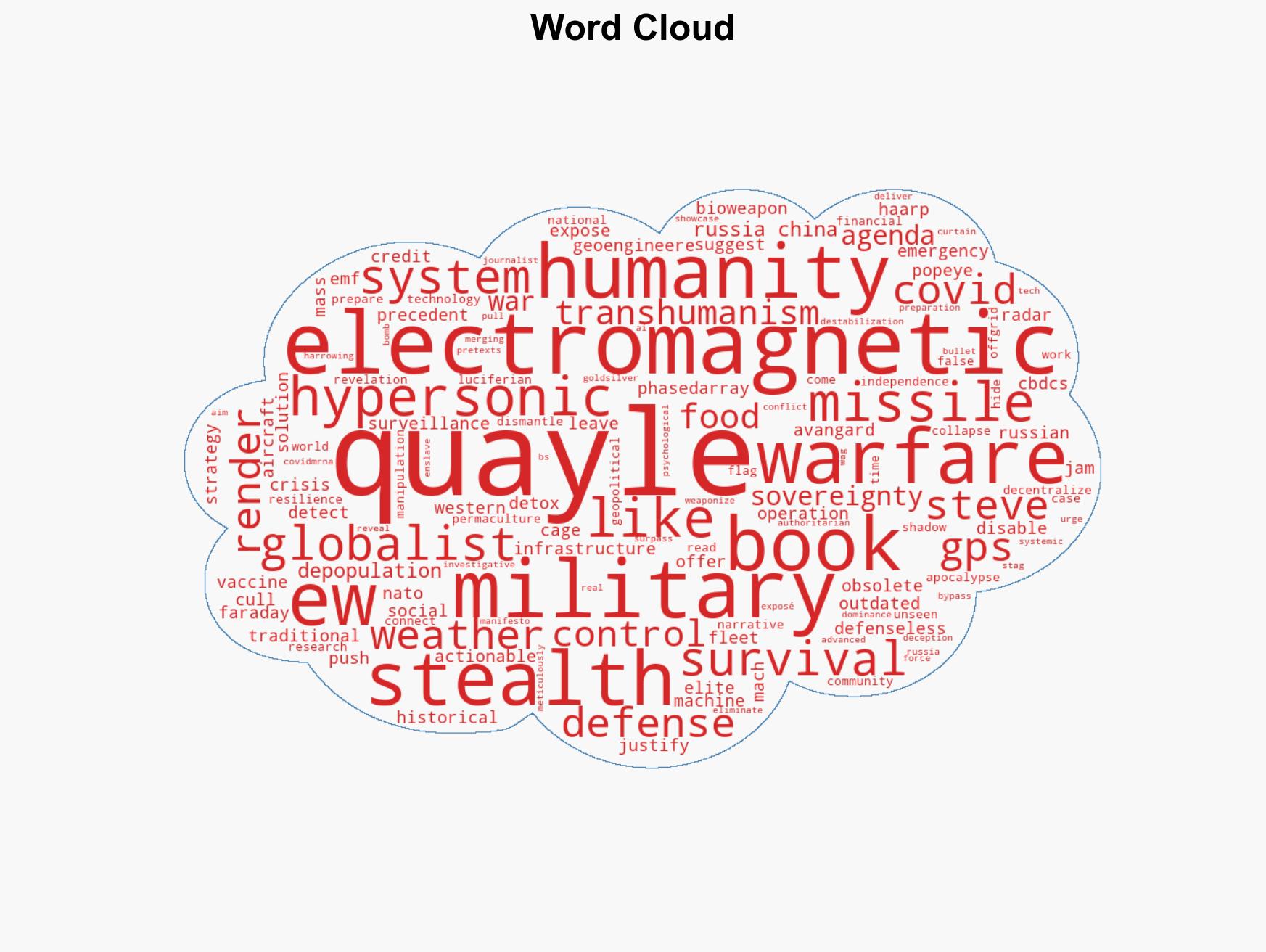
national security threats, electromagnetic warfare, military strategy, geopolitical tensions, defense technology, misinformation, strategic imbalance
Structured Analytic Techniques Applied
- Cognitive Bias Stress Test: Expose and correct potential biases in assessments through red-teaming and structured challenge.
- Bayesian Scenario Modeling: Use probabilistic forecasting for conflict trajectories or escalation likelihood.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
National Security Threats Briefs ·
Daily Summary ·
Support us