CISA warns of rapid exploitation of Langflow and Trivy vulnerabilities in supply chain security threats
Published on: 2026-03-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: CISA sounds alarm on Langflow RCE Trivy supply chain compromise after rapid exploitation
1. BLUF (Bottom Line Up Front)
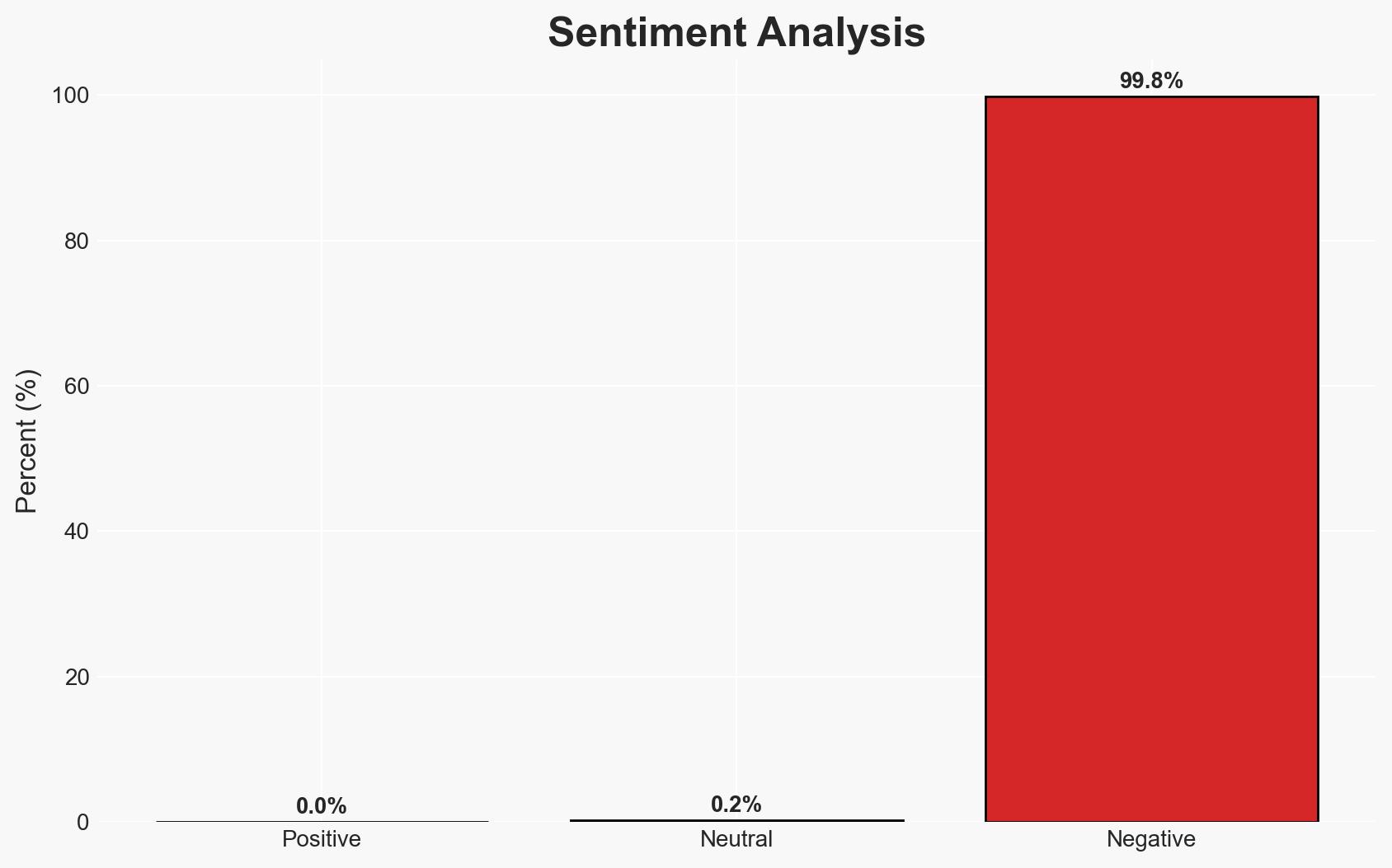
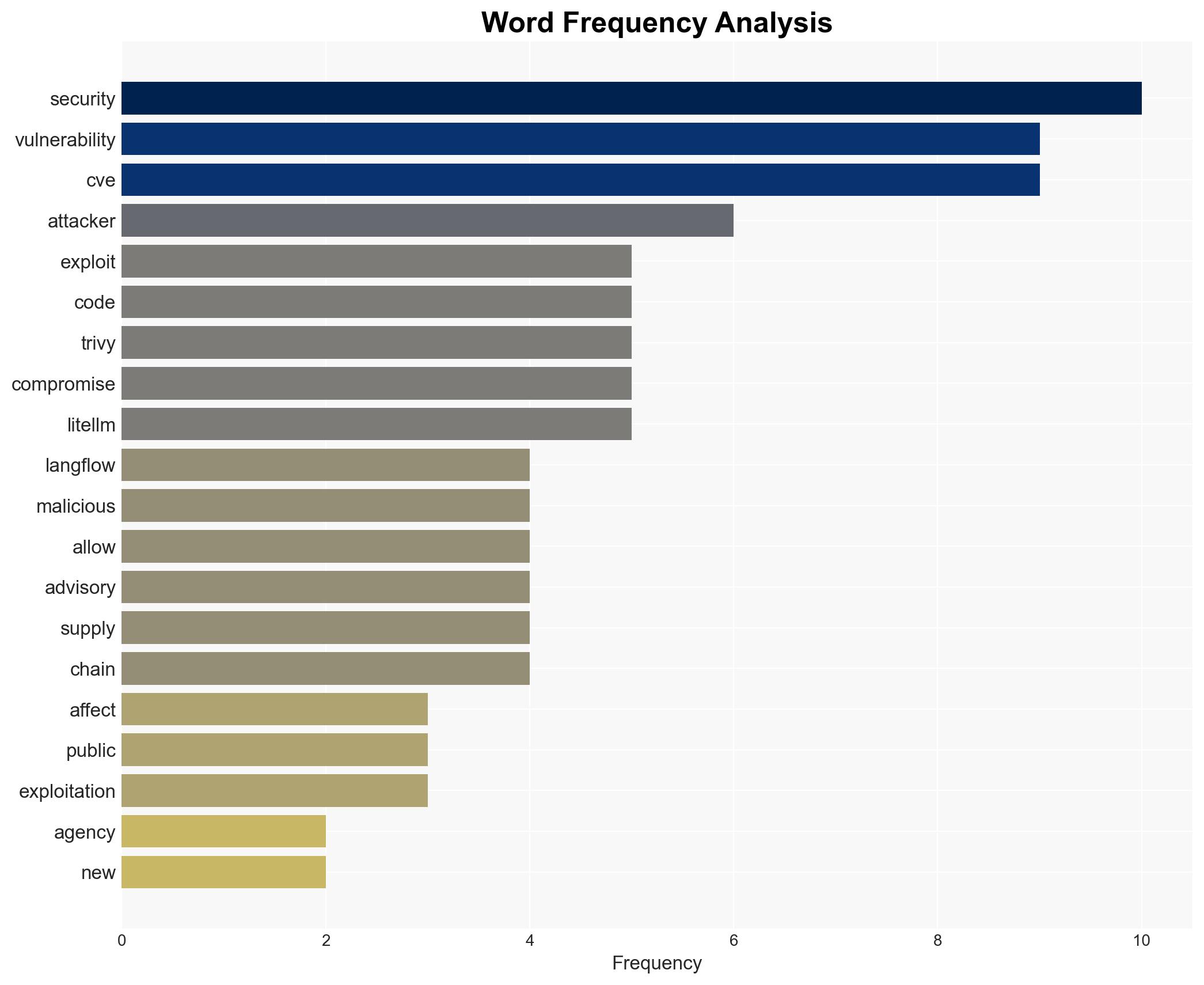
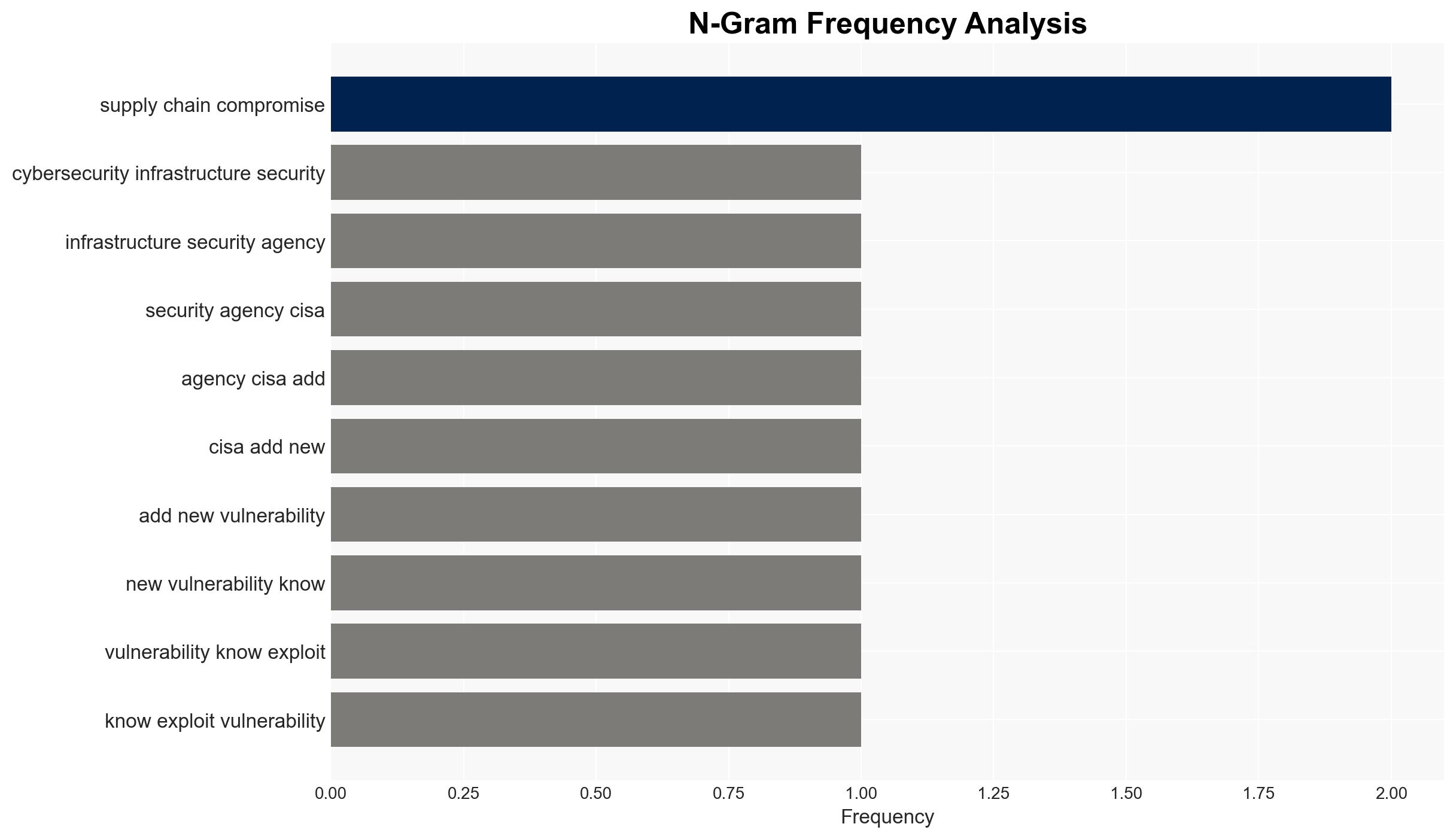
The rapid exploitation of vulnerabilities CVE-2026-33017 in Langflow and CVE-2026-33634 in Trivy represents a significant threat to US federal civilian agencies, necessitating immediate remediation. The exploitation underscores a structural shift towards faster weaponization of vulnerabilities. Moderate confidence in the assessment that attackers are leveraging detailed advisories to expedite exploit development.
2. Competing Hypotheses
- Hypothesis A: Attackers rapidly developed exploits based on the detailed security advisory for CVE-2026-33017, leading to immediate exploitation attempts. This is supported by the timeline of events and the lack of public PoC code.
- Hypothesis B: The exploitation was premeditated, with attackers having prior knowledge of the vulnerabilities, possibly through insider information or parallel discovery. This is less supported due to the absence of evidence indicating prior knowledge before the advisory’s publication.
- Assessment: Hypothesis A is currently better supported due to the documented timeline and the rapid development of exploits post-advisory. Indicators such as discovery of pre-existing exploit tools or insider leaks could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The security advisory was the primary source for exploit development; attackers have the capability to act on such advisories quickly; federal agencies will comply with CISA’s remediation deadlines.
- Information Gaps: Details on the full extent of the compromise and the identity of the attackers; specific impacts on affected systems and data.
- Bias & Deception Risks: Potential bias in relying on public advisories as the sole source of vulnerability information; risk of underestimating attackers’ capabilities or overestimating agency response effectiveness.
4. Implications and Strategic Risks
The rapid exploitation of these vulnerabilities could lead to increased scrutiny on open-source security practices and pressure on agencies to enhance their patch management processes.
- Political / Geopolitical: Potential for increased regulatory measures on software security standards, affecting international software collaborations.
- Security / Counter-Terrorism: Heightened risk of similar rapid exploitation in critical infrastructure sectors, necessitating enhanced threat monitoring.
- Cyber / Information Space: Acceleration of exploit development timelines may drive demand for advanced threat detection and response solutions.
- Economic / Social: Potential economic impact from compromised supply chains and loss of trust in affected software solutions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Agencies should prioritize patching affected systems, enhance monitoring for unusual activity, and conduct thorough audits of access logs.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing, and invest in automated patch management systems.
- Scenario Outlook:
- Best: Rapid patching and enhanced monitoring prevent further exploitation, restoring system integrity.
- Worst: Continued exploitation leads to significant data breaches and operational disruptions.
- Most-Likely: Agencies manage to patch systems in time, but face ongoing challenges from similar vulnerabilities.
6. Key Individuals and Entities
- US Cybersecurity and Infrastructure Security Agency (CISA)
- Sysdig Threat Research Team (TRT)
- Aviral Srivastava (discoverer of CVE-2026-33017)
- TeamPCP (attributed to Trivy compromise)
7. Thematic Tags
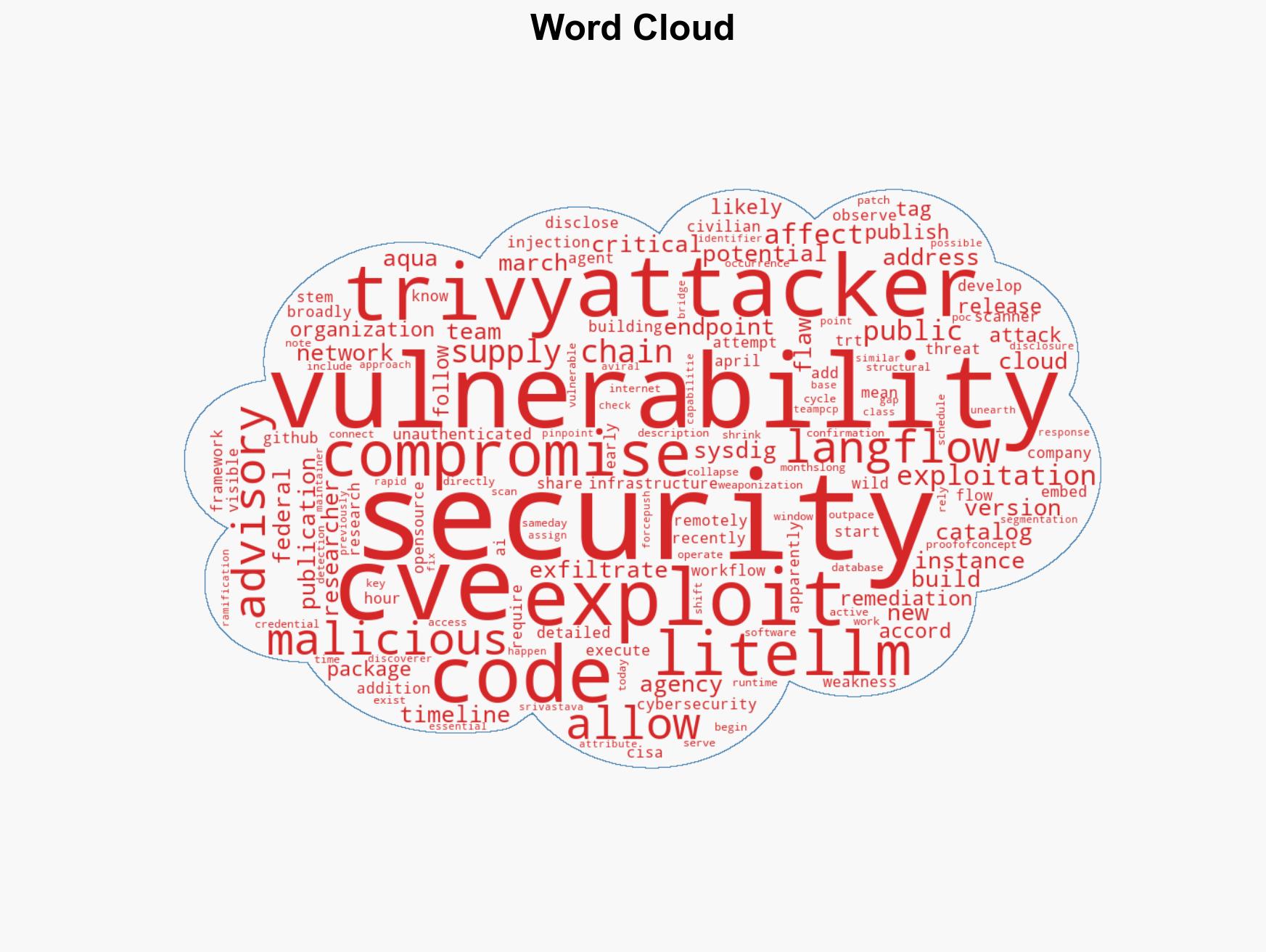
cybersecurity, vulnerability exploitation, supply chain security, federal agency compliance, open-source software risks
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us