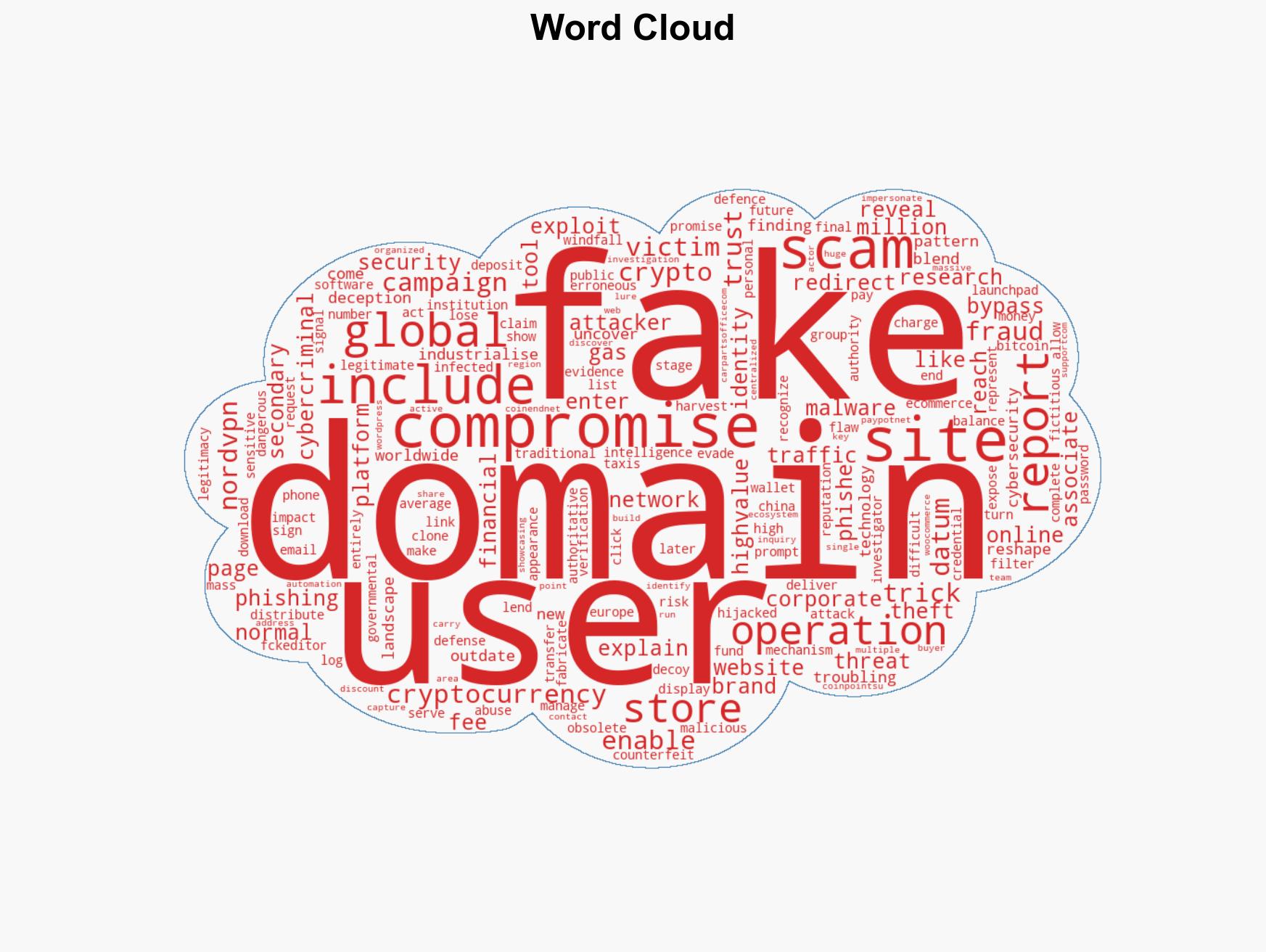
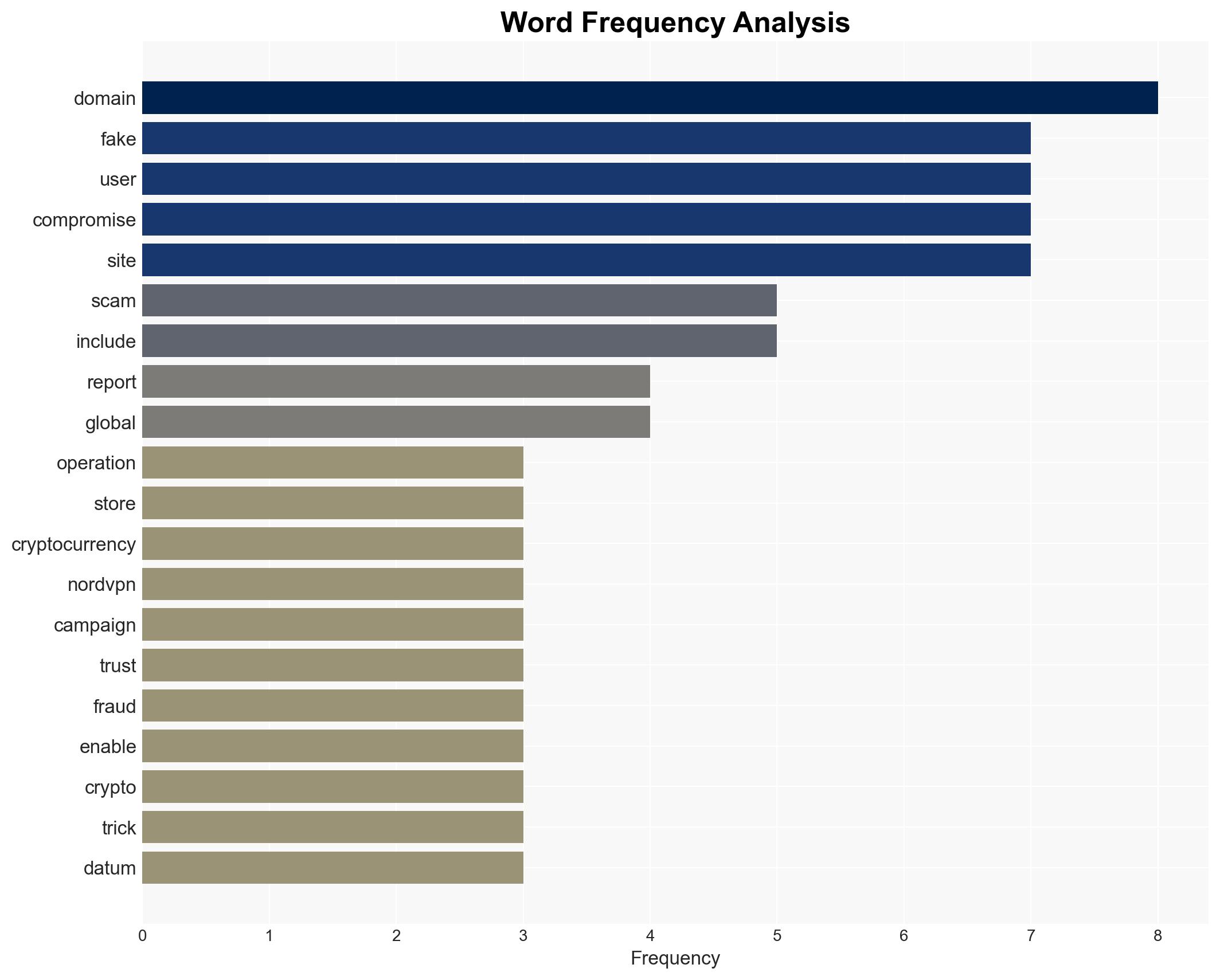
Global Cybercrime Report Reveals Extensive Scams Targeting Users Through Compromised Trusted Domains
Published on: 2026-03-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Report exposes industrialscale scams targeting everyday users
1. BLUF (Bottom Line Up Front)
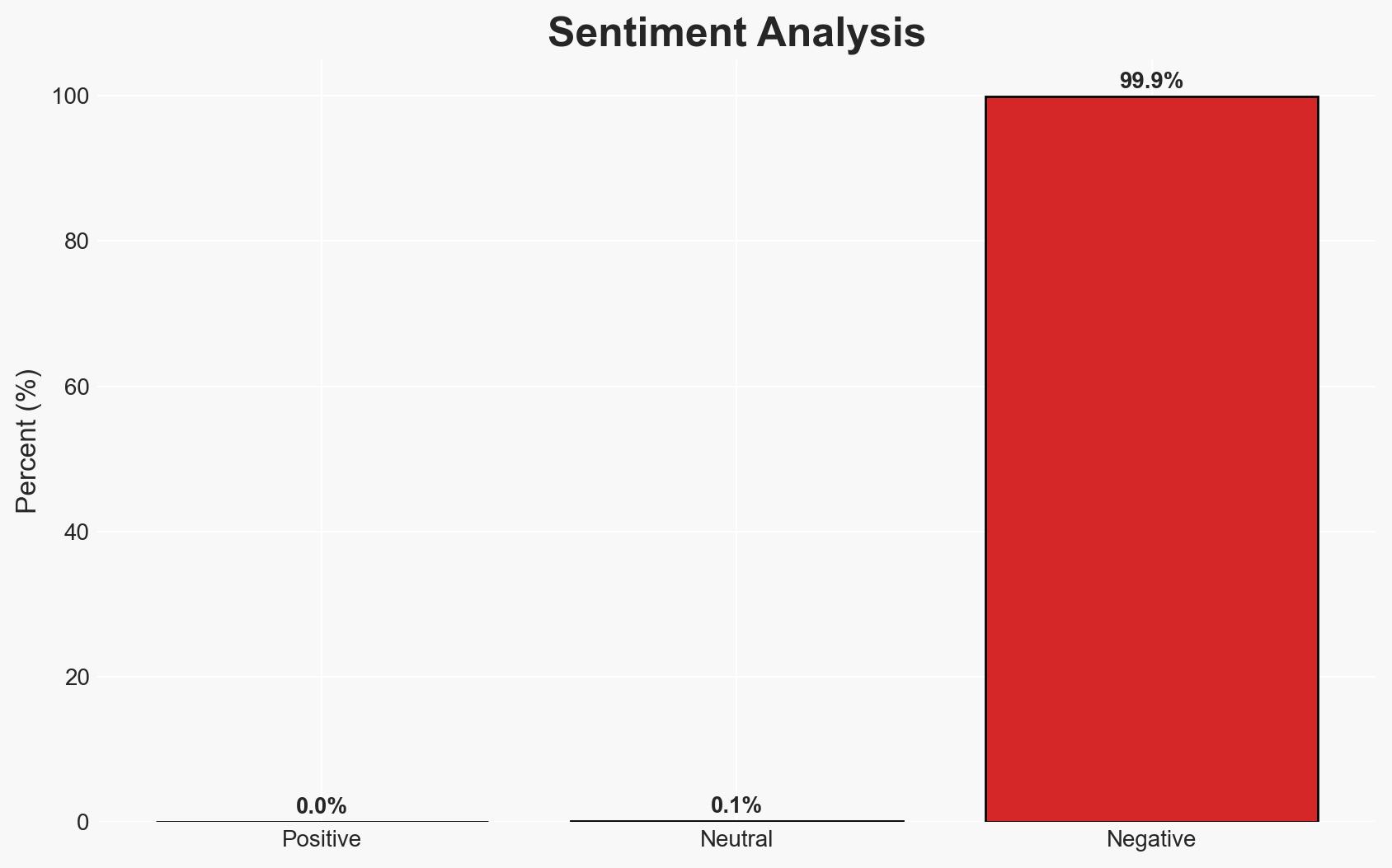
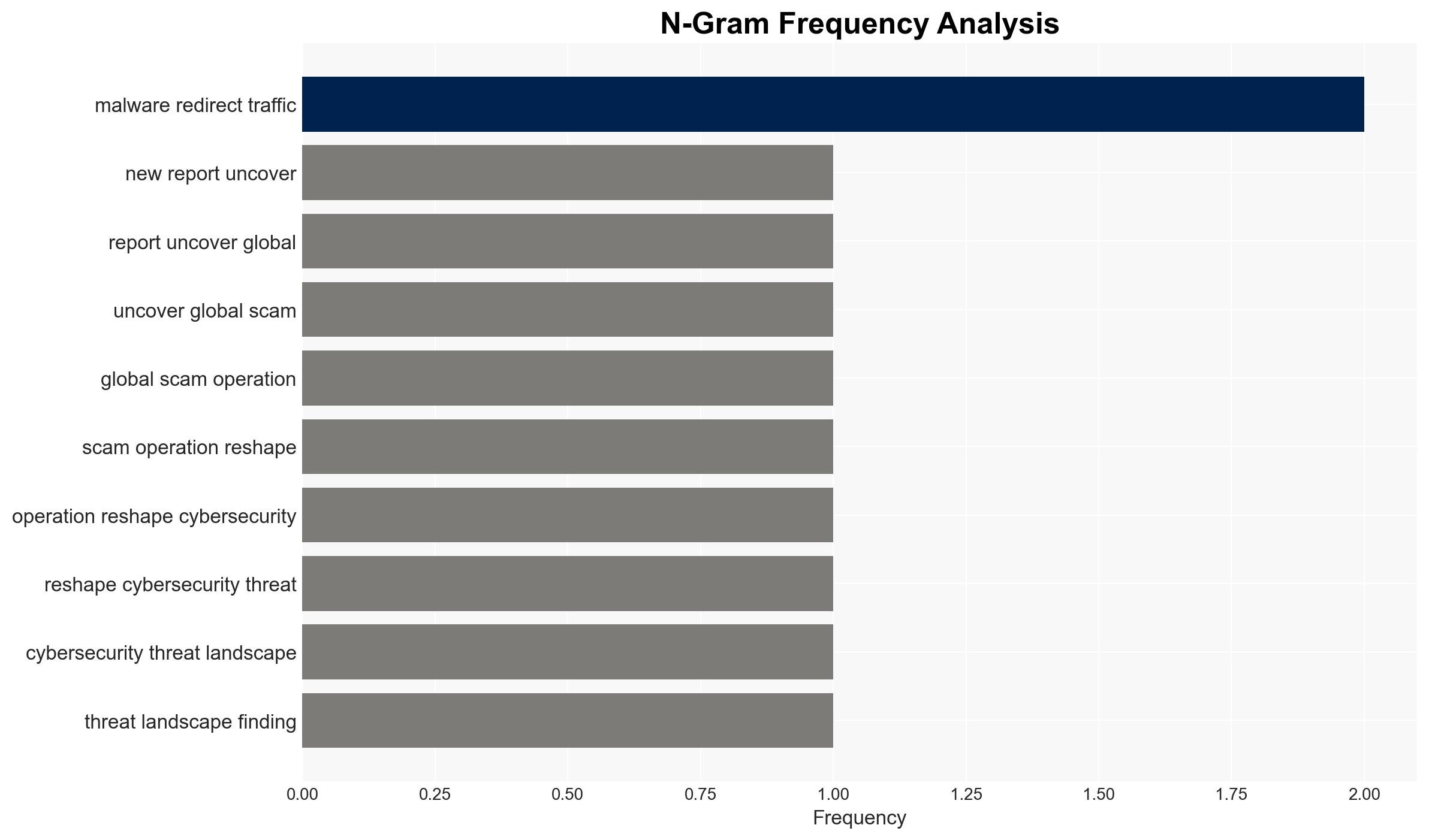
The report reveals a significant cybersecurity threat where cybercriminals exploit outdated vulnerabilities and trusted domains to conduct large-scale scams, affecting users globally, particularly in Europe, the U.S., and China. The most likely hypothesis is that these operations are primarily financially motivated. Overall confidence in this assessment is moderate, given the complexity and global reach of the operations.
2. Competing Hypotheses
- Hypothesis A: The primary motivation behind these scams is financial gain through exploiting outdated vulnerabilities and trusted domains. Supporting evidence includes the use of fake crypto wallets and phishing pages to extract financial and personal data. A key uncertainty is the full extent of the financial networks involved.
- Hypothesis B: The operations may also aim to destabilize trust in digital infrastructures and cause broader economic disruption. While plausible, there is limited direct evidence supporting this hypothesis compared to the financial motivations.
- Assessment: Hypothesis A is currently better supported due to the direct financial tactics observed, such as phishing for cryptocurrency and personal data. Indicators that could shift this judgment include evidence of state sponsorship or strategic targeting of critical infrastructure.
3. Key Assumptions and Red Flags
- Assumptions: The cybercriminals are primarily financially motivated; the exploitation of CVE-2009-2265 is a deliberate choice due to its obscurity; compromised domains are unaware of their involvement.
- Information Gaps: The identity and organizational structure of the perpetrators; the full scope of compromised domains and affected users; potential state involvement.
- Bias & Deception Risks: Potential bias in source reporting due to commercial interests; manipulation of data by cybercriminals to obfuscate true motives or scale.
4. Implications and Strategic Risks
This development could lead to increased scrutiny on digital security practices and regulatory measures globally. It may also prompt a reevaluation of legacy system vulnerabilities.
- Political / Geopolitical: Potential for increased international cooperation on cybersecurity; risk of diplomatic tensions if state involvement is suspected.
- Security / Counter-Terrorism: Heightened threat environment for digital infrastructure; potential for similar tactics to be adopted by terrorist organizations.
- Cyber / Information Space: Increased focus on patching legacy systems; potential rise in cyber insurance claims and premiums.
- Economic / Social: Possible loss of consumer trust in digital transactions; economic impact on affected businesses and individuals.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive audit of systems for outdated vulnerabilities; enhance monitoring of domain activities; increase public awareness campaigns on phishing threats.
- Medium-Term Posture (1–12 months): Develop partnerships for information sharing on cyber threats; invest in upgrading legacy systems; strengthen regulatory frameworks for cybersecurity.
- Scenario Outlook: Best: Rapid containment and mitigation of threats with minimal economic impact. Worst: Escalation of attacks leading to significant financial and reputational damage. Most-Likely: Continued sporadic attacks with gradual improvements in defensive measures.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, phishing, cryptocurrency scams, digital infrastructure, legacy systems, global threat, financial crime
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us