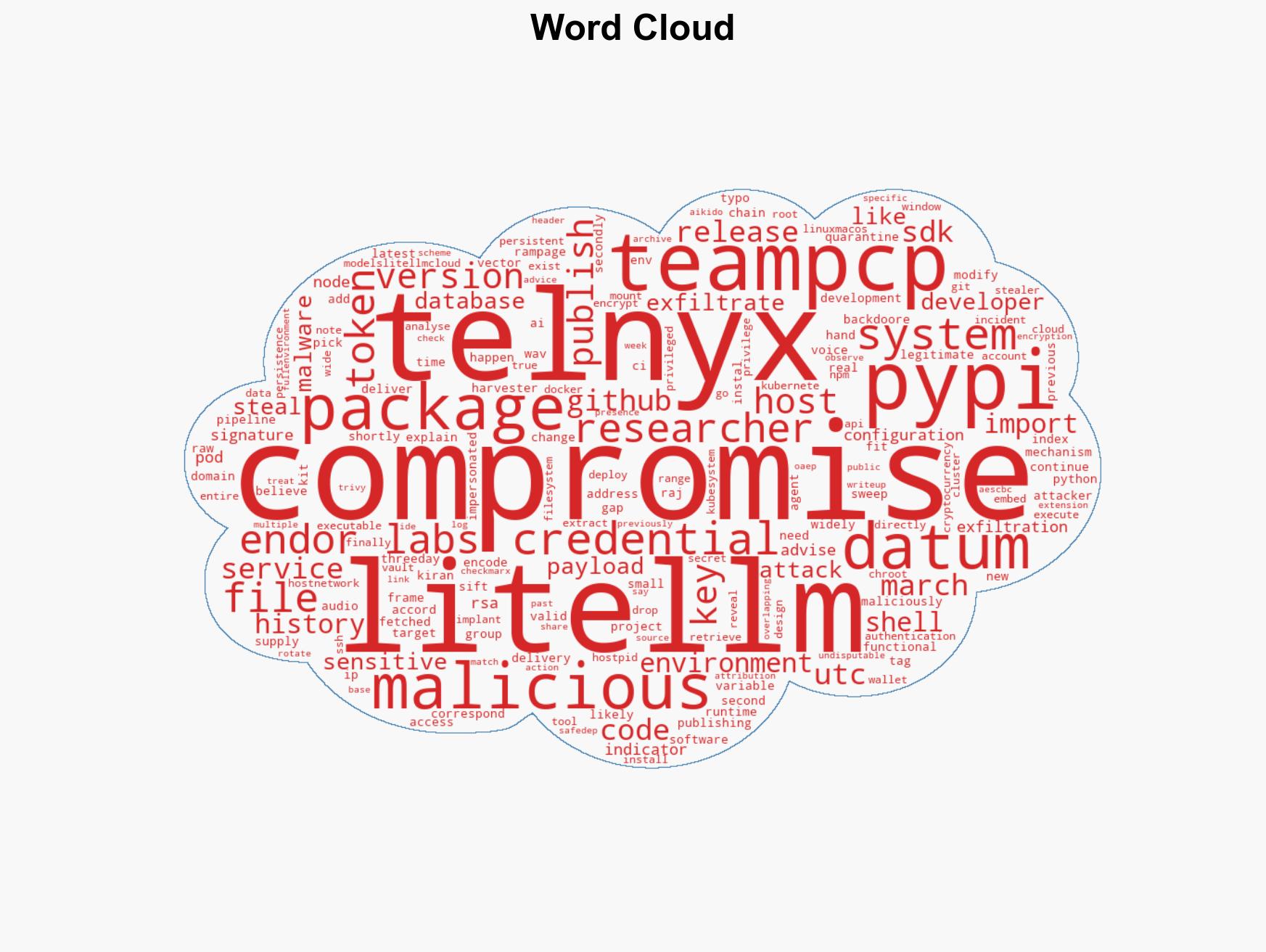
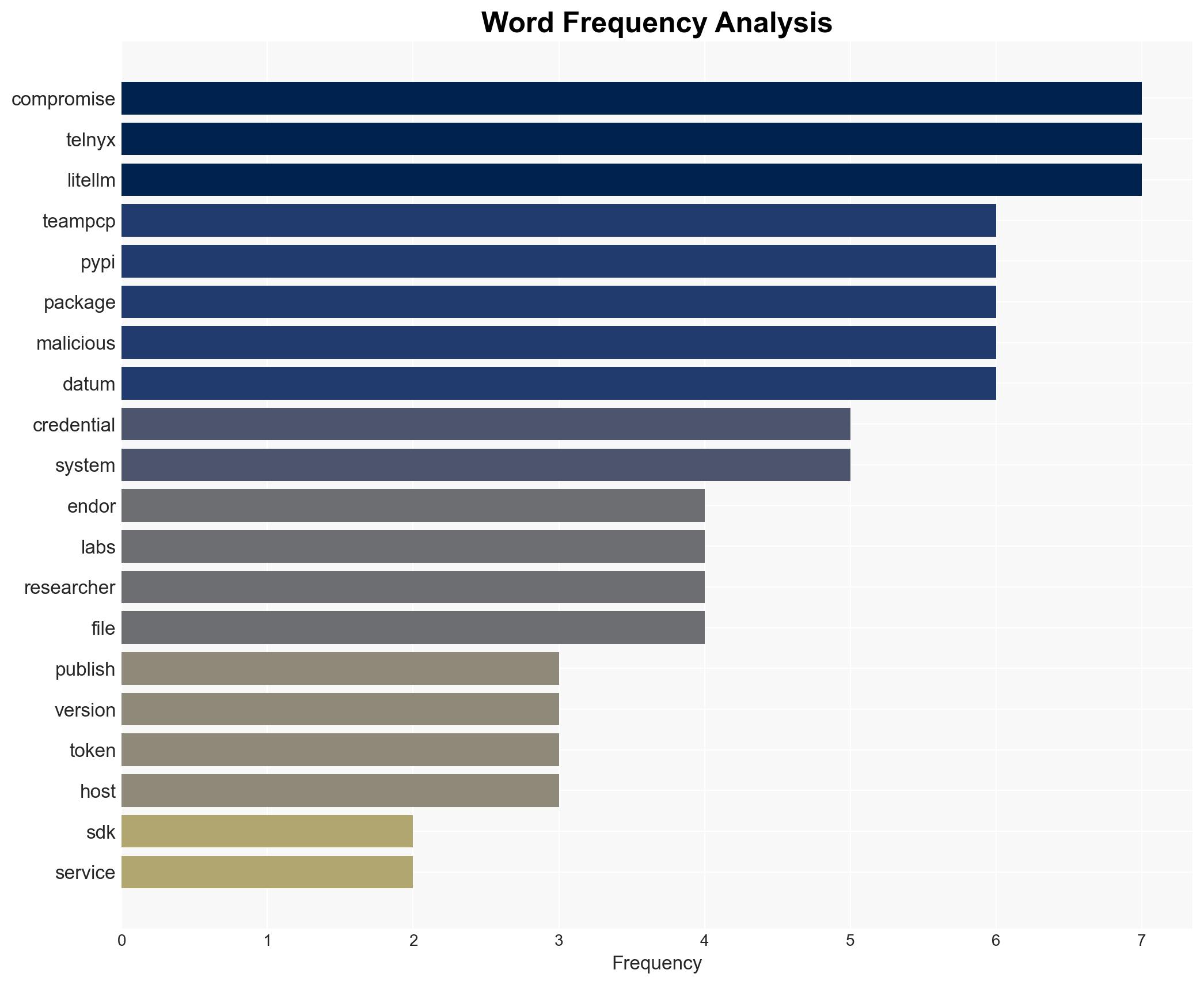
TeamPCP Compromises Telnyx SDK on PyPI, Distributing Malicious Backdoored Versions
Published on: 2026-03-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: TeamPCP strikes again Backdoored Telnyx PyPI package delivers malware
1. BLUF (Bottom Line Up Front)
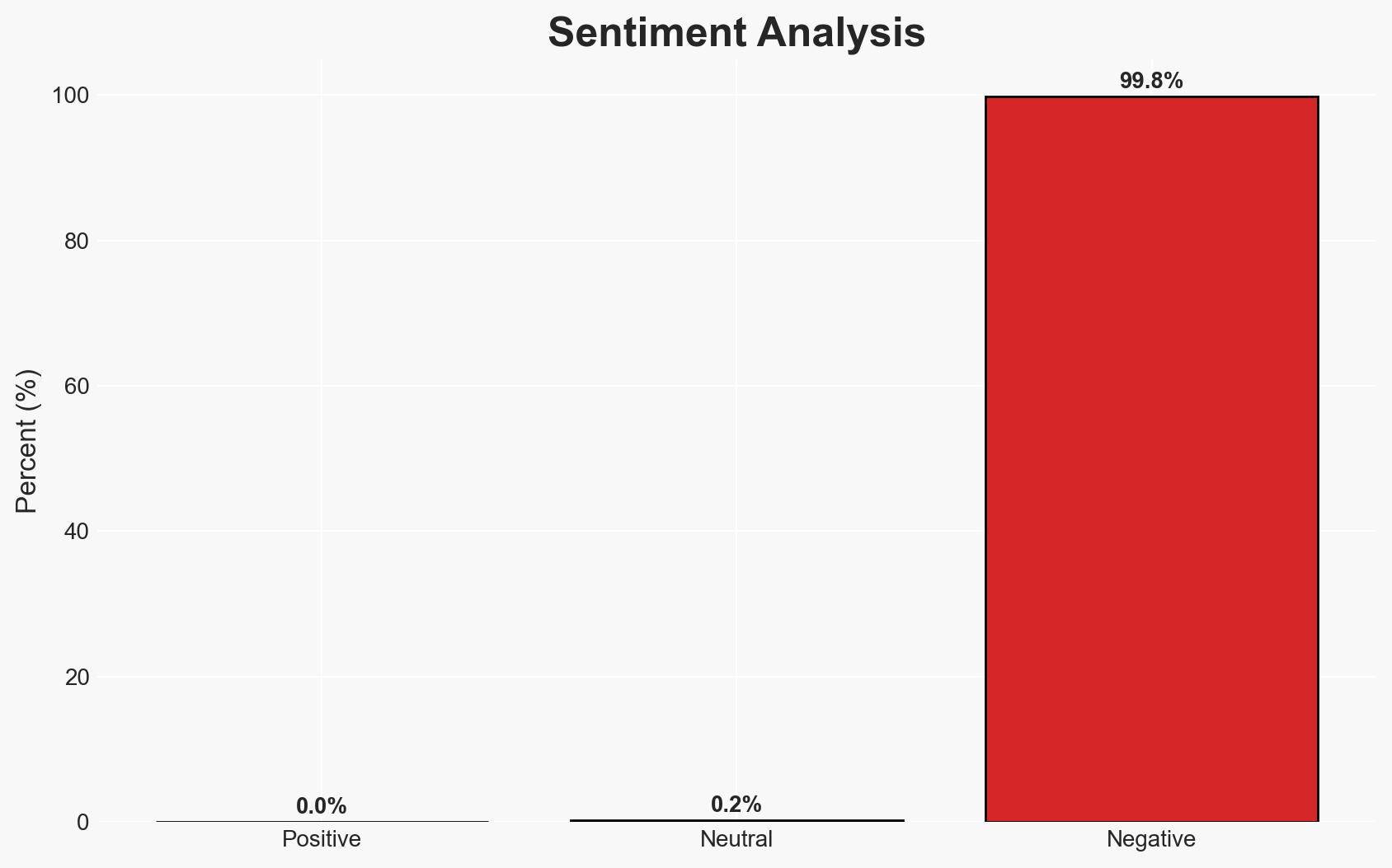
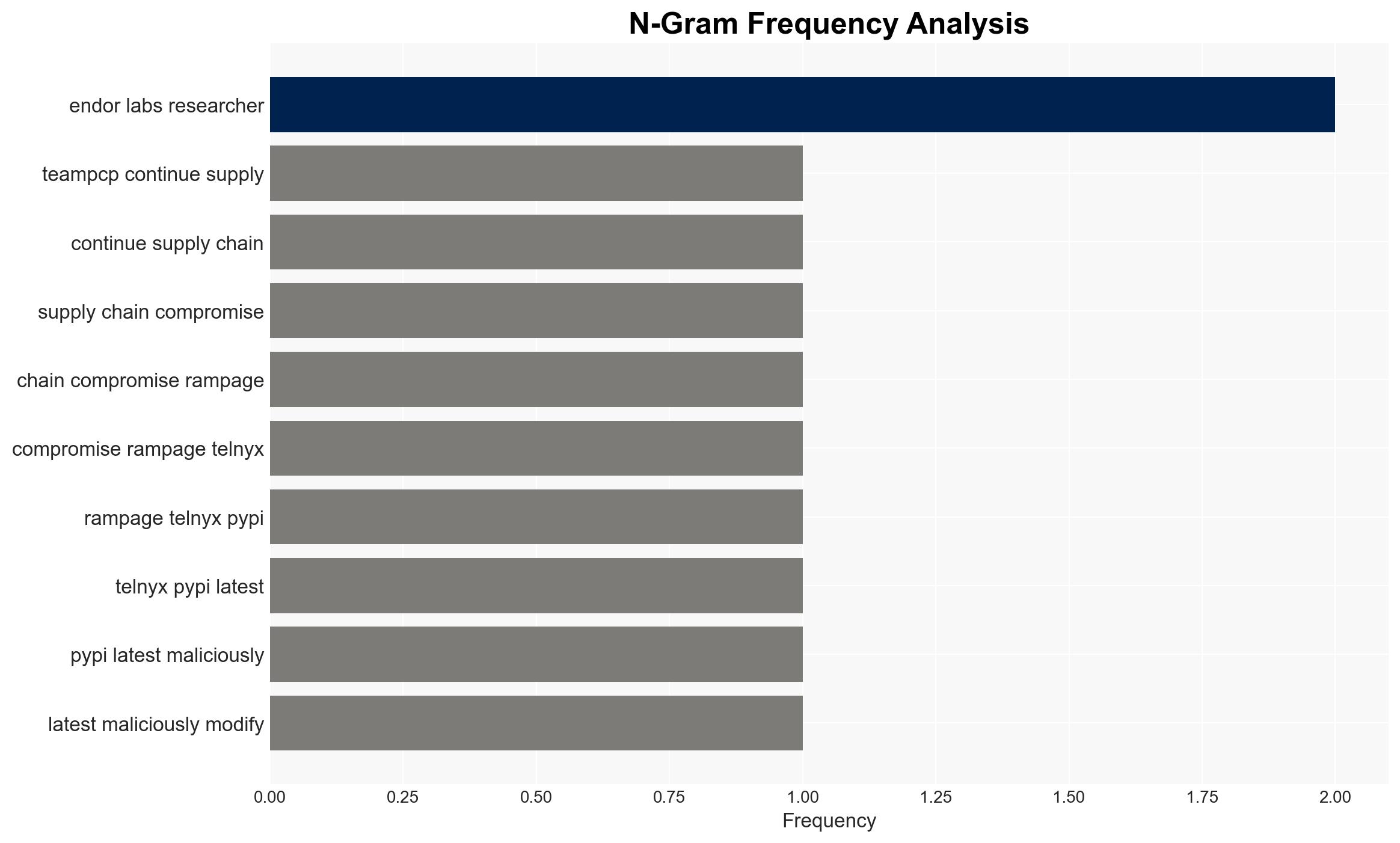
TeamPCP has executed another supply chain attack by backdooring the Telnyx SDK on PyPI, affecting developers and organizations using this package. The attack involved sophisticated techniques to exfiltrate sensitive data, posing significant security risks. The most likely hypothesis is that TeamPCP exploited compromised credentials from previous attacks to target Telnyx. Overall confidence in this assessment is moderate due to existing information gaps and potential deception.
2. Competing Hypotheses
- Hypothesis A: TeamPCP exploited compromised credentials from the LiteLLM attack to backdoor the Telnyx package. Supporting evidence includes the timeline and method of credential harvesting. Contradicting evidence is limited but includes the possibility of independent credential compromise.
- Hypothesis B: The Telnyx compromise was an independent incident, unrelated to previous attacks, possibly due to a separate vulnerability or insider threat. This is less supported due to the lack of evidence for an independent breach and the established pattern of TeamPCP’s operations.
- Assessment: Hypothesis A is currently better supported due to the consistent pattern of credential exploitation by TeamPCP and the timeline of events. Indicators such as new attack vectors or unrelated breaches could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: TeamPCP has access to sophisticated tools for credential harvesting; the Telnyx SDK is widely used in sensitive environments; PyPI security measures are insufficient to prevent such attacks.
- Information Gaps: Specific methods of initial credential compromise; full extent of affected systems and data; potential insider involvement.
- Bias & Deception Risks: Confirmation bias towards linking incidents to TeamPCP; potential misinformation from compromised sources; lack of independent verification of claims.
4. Implications and Strategic Risks
The continued success of TeamPCP in executing supply chain attacks could embolden similar threat actors and undermine trust in open-source software repositories.
- Political / Geopolitical: Potential for increased international scrutiny and regulatory pressure on software supply chain security.
- Security / Counter-Terrorism: Heightened threat environment for developers and organizations relying on open-source software, necessitating enhanced security protocols.
- Cyber / Information Space: Increased risk of data breaches and intellectual property theft, with potential impacts on national security and corporate competitiveness.
- Economic / Social: Possible economic impacts due to disrupted operations and increased cybersecurity costs for affected organizations.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of PyPI and other repositories for anomalous activity; conduct security audits of systems using affected packages; increase awareness among developers.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing; invest in supply chain security technologies; enhance credential management practices.
- Scenario Outlook:
- Best: Improved security measures prevent further attacks, restoring trust in open-source repositories.
- Worst: Continued breaches lead to widespread data theft and economic damage, prompting regulatory intervention.
- Most-Likely: Incremental improvements in security reduce but do not eliminate the threat, with ongoing vigilance required.
6. Key Individuals and Entities
- TeamPCP
- Endor Labs
- Telnyx
- PyPI (Python Package Index)
- Kiran Raj (Endor Labs)
7. Thematic Tags
cybersecurity, supply chain attack, cyber-security, open-source software, credential compromise, malware delivery
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us