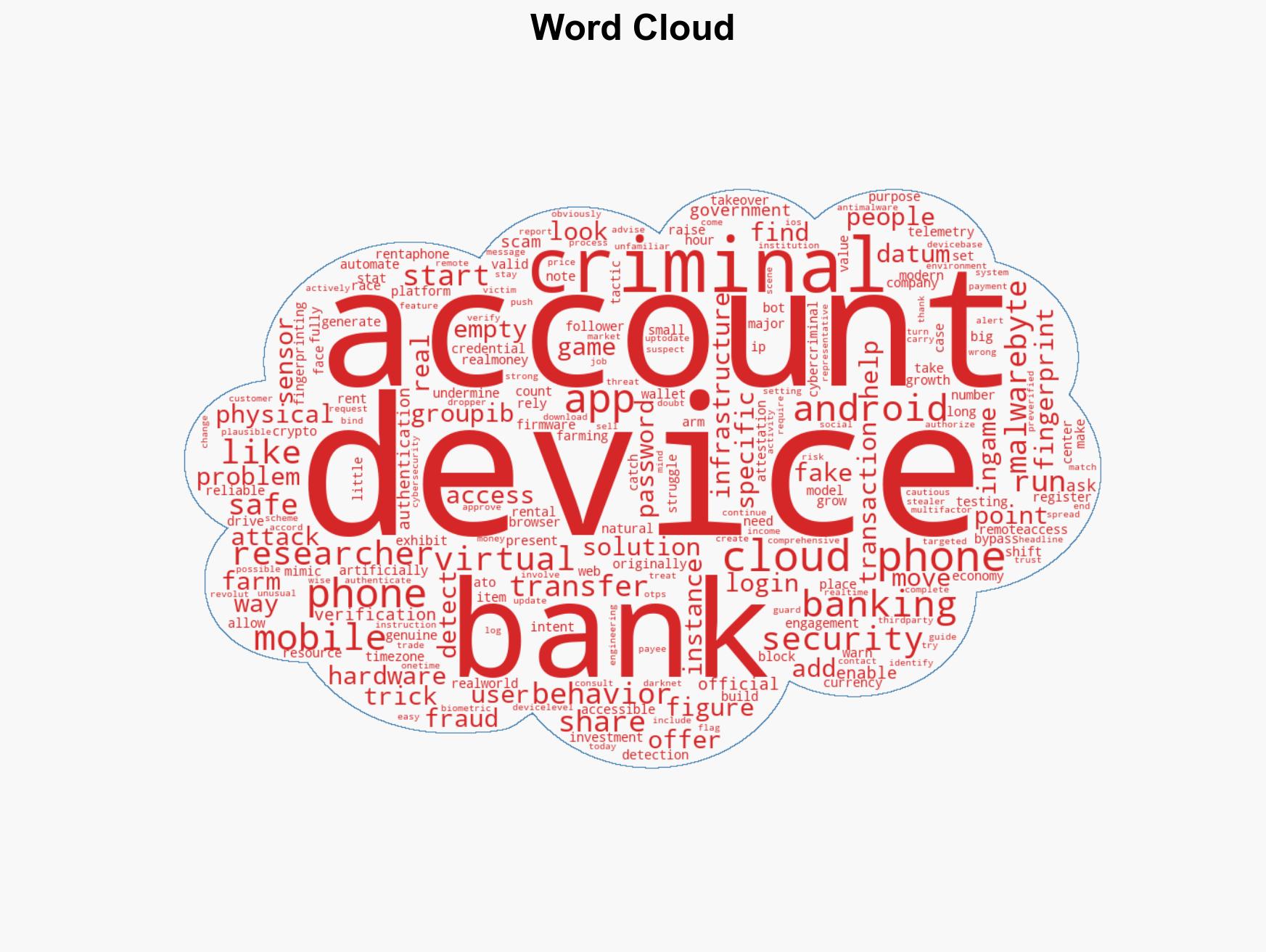
Cybercriminals exploit virtual phones to circumvent bank security measures
Published on: 2026-03-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Criminals are renting virtual phones to bypass bank security
1. BLUF (Bottom Line Up Front)
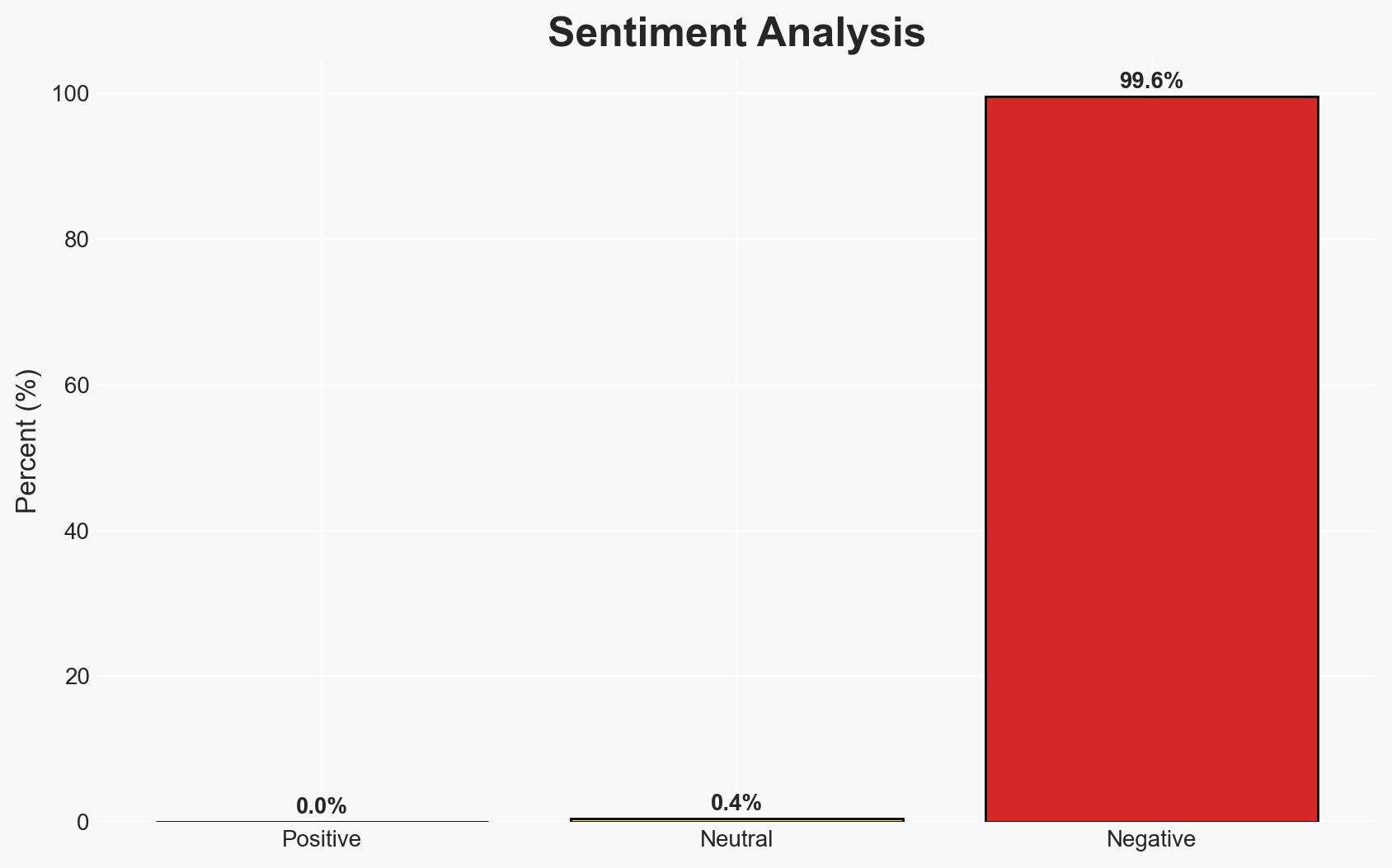
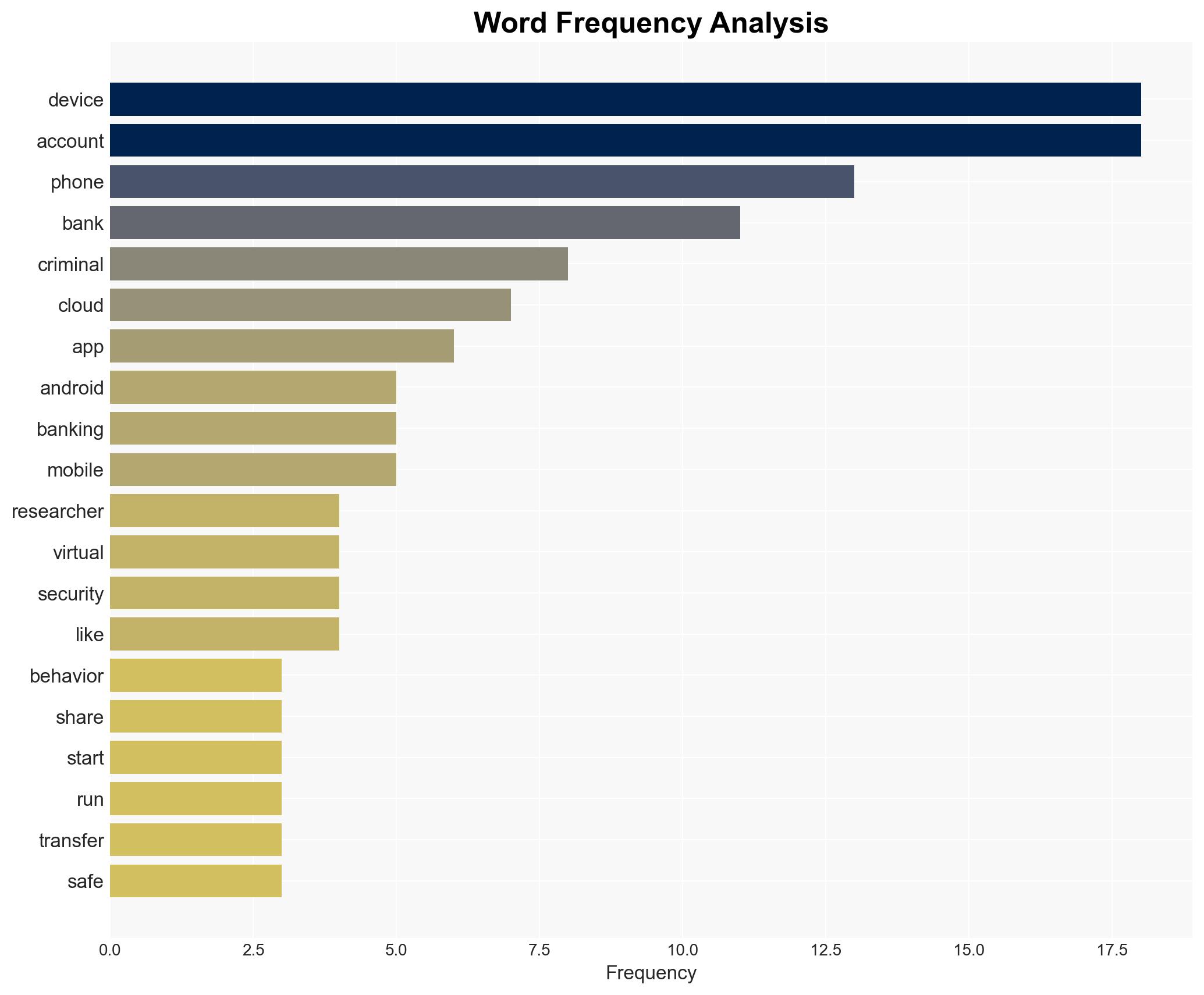
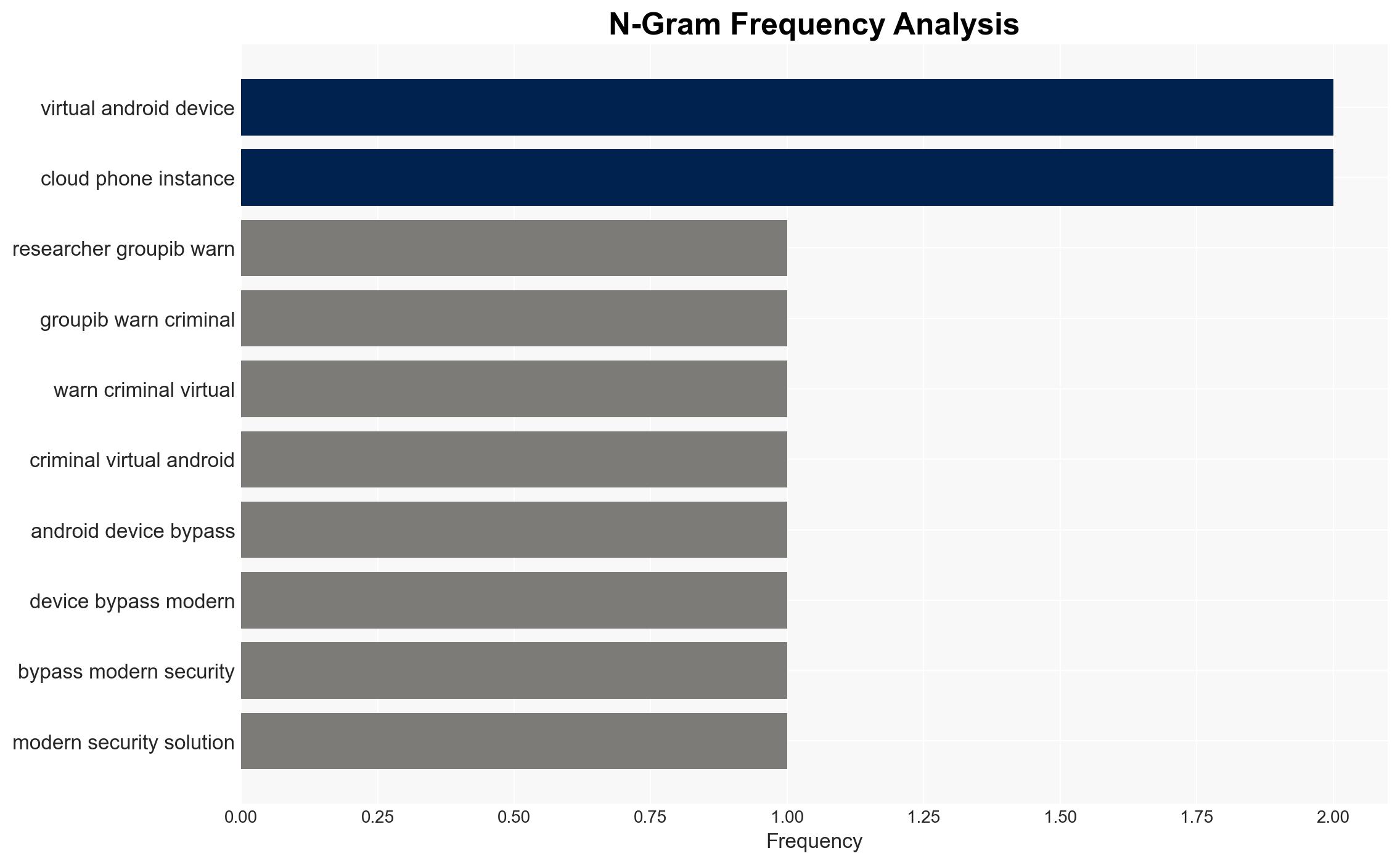
Criminals are exploiting virtual Android devices, or cloud phones, to bypass bank security measures by mimicking legitimate device fingerprints. This tactic undermines device-based fraud detection and facilitates account take-over attacks. The primary victims are financial institutions and their customers. This assessment is made with moderate confidence due to the evolving nature of cyber tactics and limited visibility into criminal networks.
2. Competing Hypotheses
- Hypothesis A: Criminals are primarily using virtual phones to bypass bank security by exploiting device fingerprinting vulnerabilities. This is supported by the reported use of cloud phones to mimic real device attributes, making them appear legitimate to banks’ security systems. However, the extent of adoption across different criminal networks remains uncertain.
- Hypothesis B: The use of virtual phones is a broader trend in cybercrime, with applications beyond banking fraud, such as in gaming and social media manipulation. While this hypothesis is supported by the mention of virtual phones in gaming economies, it lacks direct evidence of prioritization over banking fraud.
- Assessment: Hypothesis A is currently better supported due to the specific targeting of banking systems and the detailed methods described for bypassing security. Indicators that could shift this judgment include evidence of significant use in other sectors or new countermeasures by banks.
3. Key Assumptions and Red Flags
- Assumptions: Criminals have the technical capability to effectively mimic device fingerprints; banks primarily rely on device fingerprinting for fraud detection; cloud phone services remain accessible and affordable to criminals.
- Information Gaps: The scale of virtual phone use in banking fraud; effectiveness of banks’ countermeasures; detailed profiles of criminal groups involved.
- Bias & Deception Risks: Potential bias in reporting from security firms with vested interests; criminals may intentionally mislead about their methods to obscure detection.
4. Implications and Strategic Risks
The use of virtual phones in fraud schemes is likely to increase, potentially leading to more sophisticated attacks and requiring banks to enhance their security measures. This development could have broader impacts on digital security and trust in financial systems.
- Political / Geopolitical: Increased pressure on governments to regulate cloud phone services and enhance cybersecurity frameworks.
- Security / Counter-Terrorism: Potential for similar tactics to be adapted for use in cyber-terrorism or state-sponsored espionage.
- Cyber / Information Space: Escalation of the arms race between cybercriminals and security providers, leading to more advanced cyber defenses and tactics.
- Economic / Social: Potential erosion of consumer trust in digital banking, impacting financial stability and consumer behavior.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Financial institutions should enhance monitoring of device telemetry and improve user education on social engineering risks.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms to innovate detection methods and share threat intelligence.
- Scenario Outlook:
- Best: Effective countermeasures reduce fraud incidents, restoring trust in digital banking.
- Worst: Widespread adoption of virtual phones in fraud leads to significant financial losses and regulatory crackdowns.
- Most-Likely: Incremental improvements in security measures lead to a temporary reduction in fraud, but criminals adapt over time.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, banking fraud, virtual devices, financial crime, social engineering, device fingerprinting, cloud technology
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us