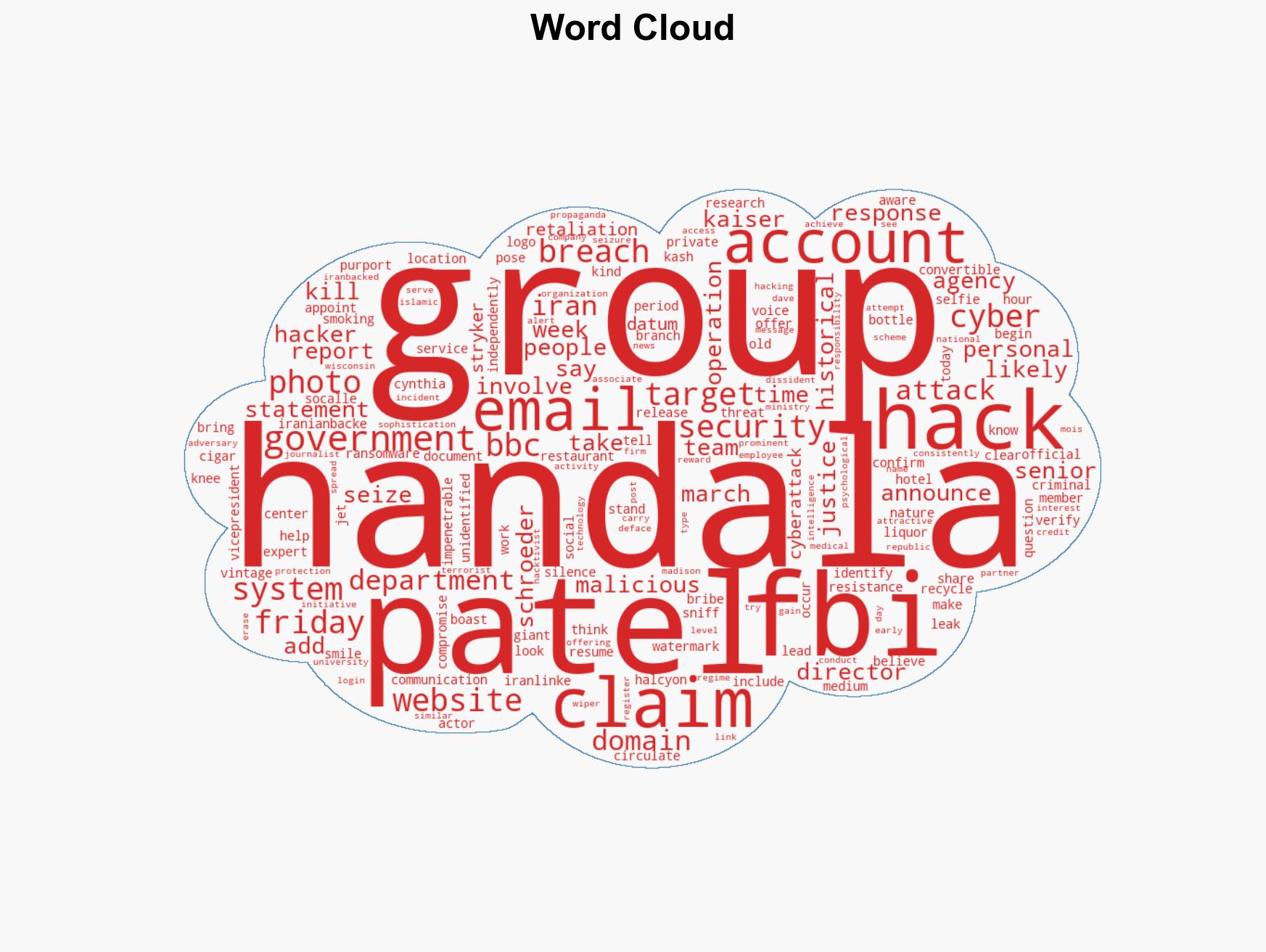
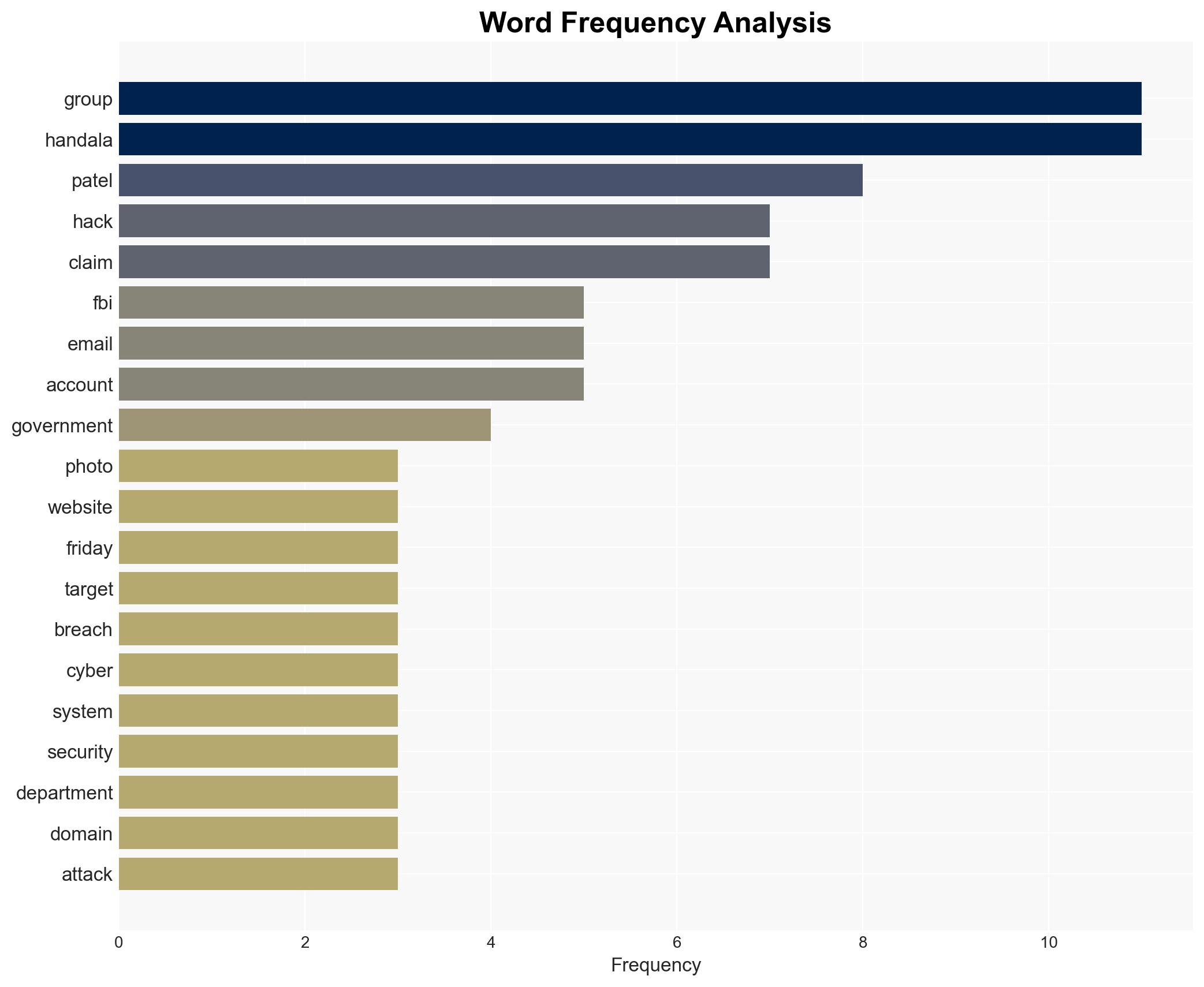
Iran-linked Handala hackers compromise FBI Director Kash Patel’s personal email account
Published on: 2026-03-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iran-backed Handala hackers breach FBI director Kash Patel’s emails
1. BLUF (Bottom Line Up Front)
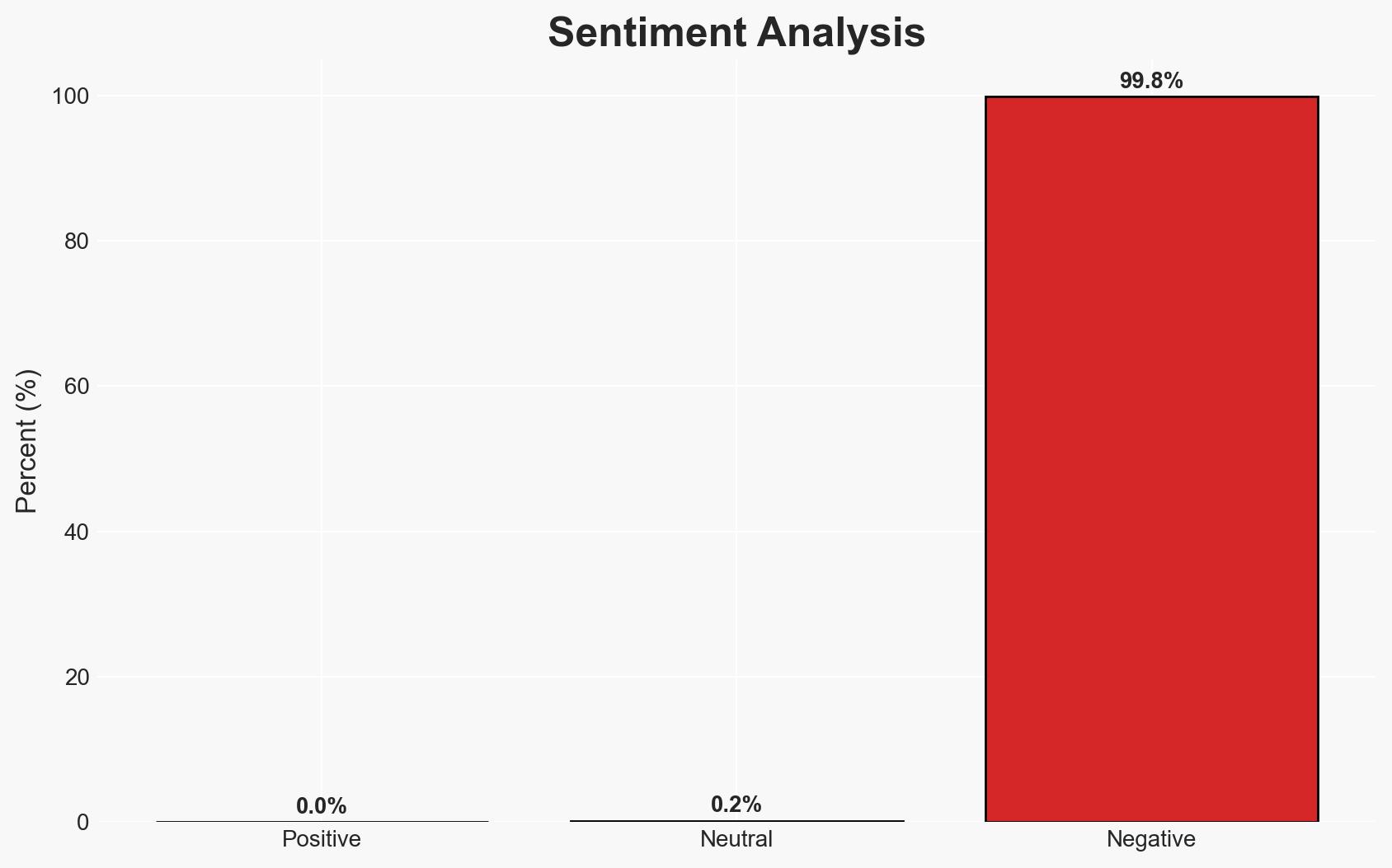
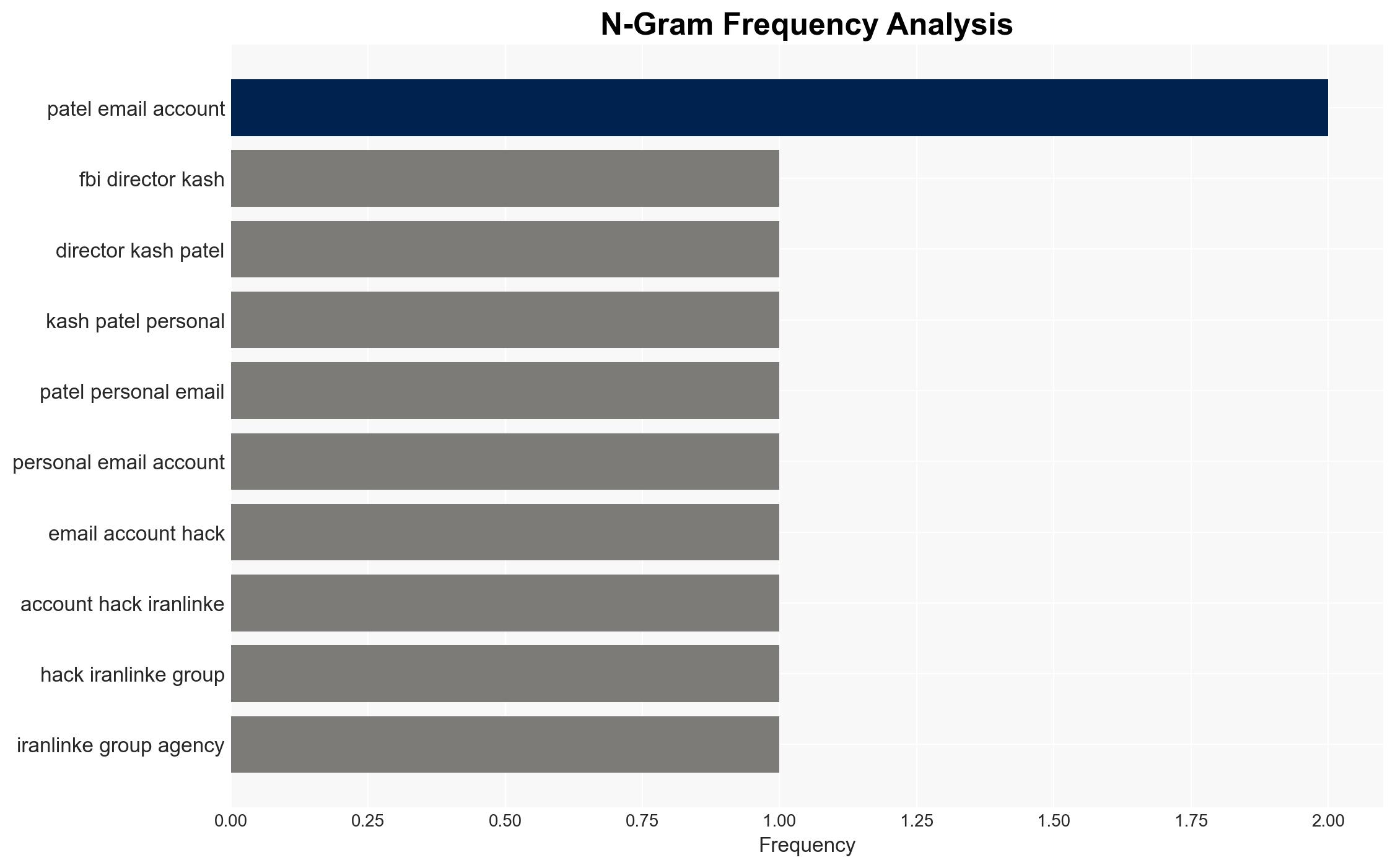
The Iran-linked Handala Hack Team has reportedly breached the personal email of FBI Director Kash Patel, potentially leveraging historical data. This incident underscores vulnerabilities in personal cybersecurity for high-profile officials. The breach’s implications are significant for U.S. national security and cyber defense posture, with moderate confidence in the assessment that this is a recycled breach rather than a new compromise.
2. Competing Hypotheses
- Hypothesis A: The Handala Hack Team accessed Kash Patel’s email through a recent breach, exploiting vulnerabilities in personal email security. Supporting evidence includes the group’s claim of recent activity and the release of personal photos. Contradicting evidence is the suggestion that the data is historical.
- Hypothesis B: The breach is a recycling of older data from a previous compromise, possibly by other groups, now used by Handala for propaganda. Supporting evidence includes expert analysis suggesting the data is old and the lack of new sensitive information. Contradicting evidence is the group’s claim of a recent breach.
- Assessment: Hypothesis B is currently better supported due to expert opinions indicating the data is historical and the absence of new sensitive information. Key indicators that could shift this judgment include the discovery of new data or confirmation of a recent breach.
3. Key Assumptions and Red Flags
- Assumptions: The data released is primarily historical; the breach does not involve government systems; Handala’s claims may be exaggerated for propaganda purposes.
- Information Gaps: Details on the exact timing and method of the breach; confirmation of whether the data is indeed historical or new.
- Bias & Deception Risks: Potential bias in Handala’s claims for propaganda; reliance on expert opinions without independent verification of data age.
4. Implications and Strategic Risks
This development could exacerbate tensions between the U.S. and Iran, highlighting vulnerabilities in personal cybersecurity for high-ranking officials. It may also influence public perception of U.S. cybersecurity capabilities.
- Political / Geopolitical: Potential escalation in U.S.-Iran cyber confrontations and diplomatic tensions.
- Security / Counter-Terrorism: Increased scrutiny on personal cybersecurity practices of government officials.
- Cyber / Information Space: Potential for increased cyber operations targeting personal accounts of officials; propaganda use by adversarial groups.
- Economic / Social: Limited direct economic impact, but potential erosion of public trust in cybersecurity measures.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance security protocols for personal accounts of government officials; conduct a thorough forensic analysis of the breach.
- Medium-Term Posture (1–12 months): Develop comprehensive training programs on personal cybersecurity for officials; strengthen international cyber cooperation to address state-sponsored threats.
- Scenario Outlook:
- Best: No further breaches occur, and cybersecurity measures are strengthened.
- Worst: Additional breaches of sensitive information lead to significant diplomatic fallout.
- Most-Likely: Continued propaganda use of historical data with moderate improvements in cybersecurity practices.
6. Key Individuals and Entities
- Kash Patel – FBI Director
- Handala Hack Team – Iran-linked hacking group
- Iran’s Ministry of Intelligence and Security (MOIS)
- Cynthia Kaiser – Senior Vice-President at Halcyon Ransomware Research Center
- Dave Schroeder – Director of National Security Initiatives at the University of Wisconsin–Madison
7. Thematic Tags
cybersecurity, Iran, cyber-espionage, national security, propaganda, personal data breach, U.S.-Iran relations
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us