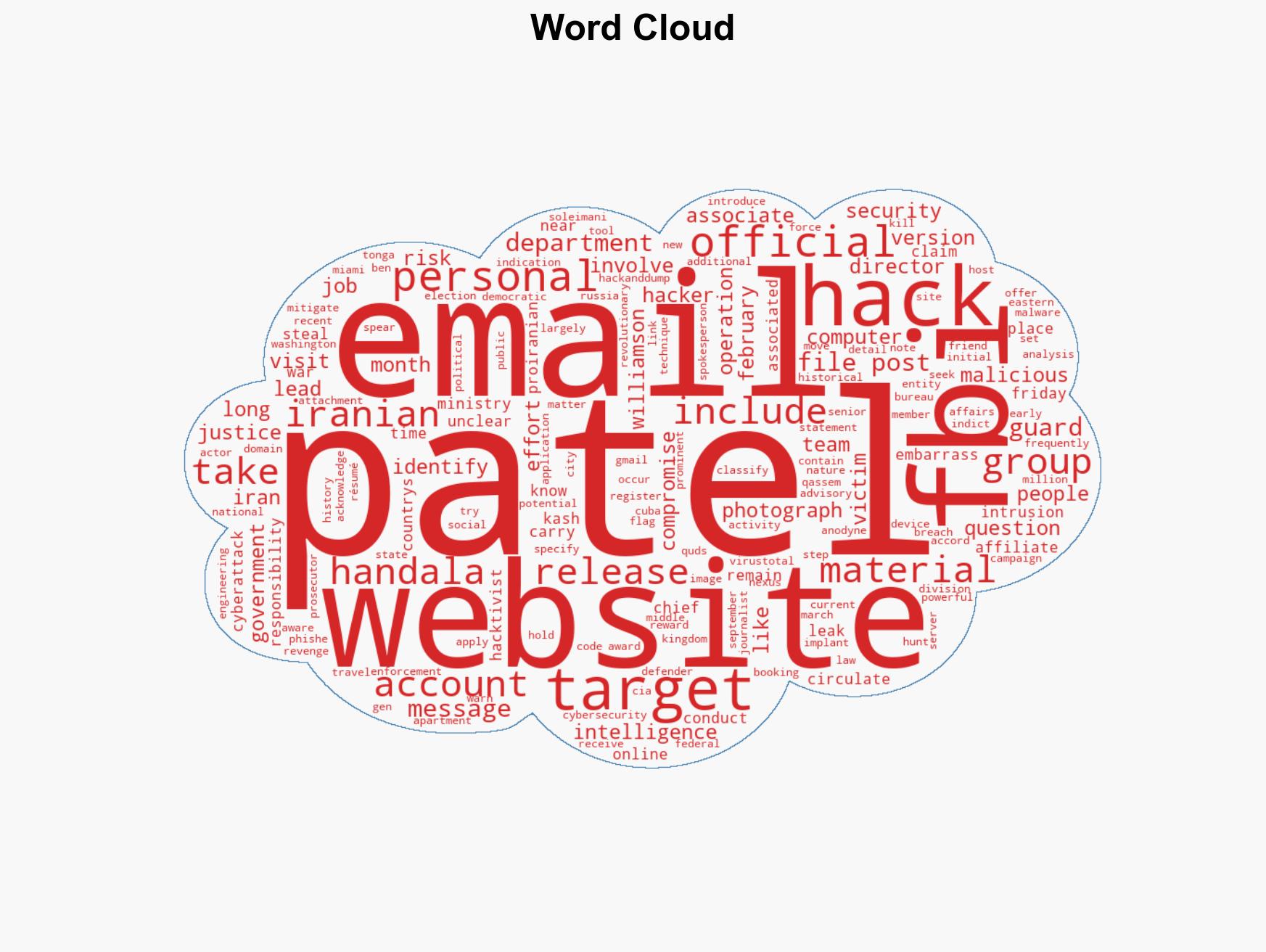
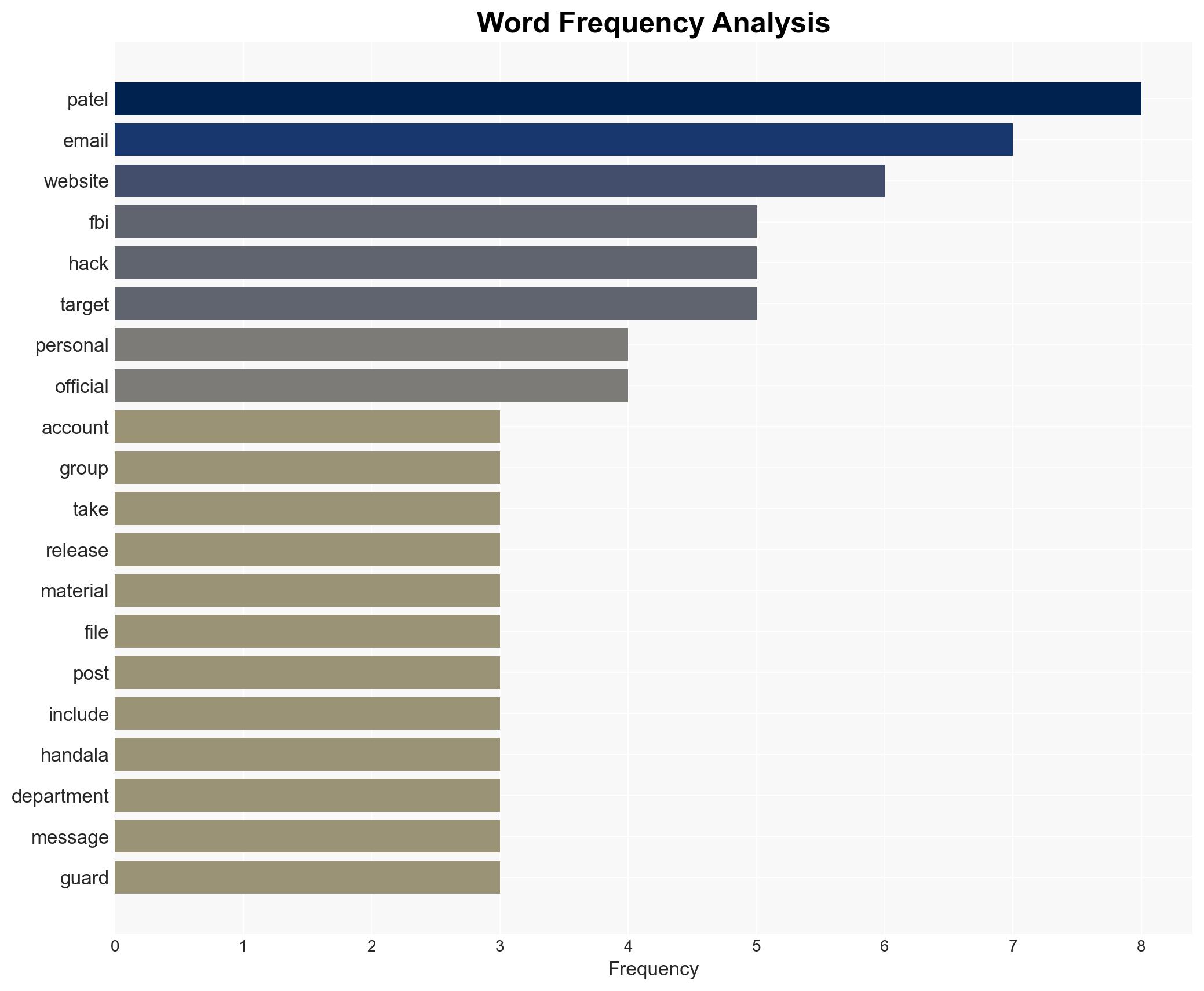
FBI Director Kash Patel’s Stolen Emails and Photos Leak Online Amid Claims of Iranian Hackers’ Involvement
Published on: 2026-03-28
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Hacked files of FBI director Kash Patel circulate online
1. BLUF (Bottom Line Up Front)
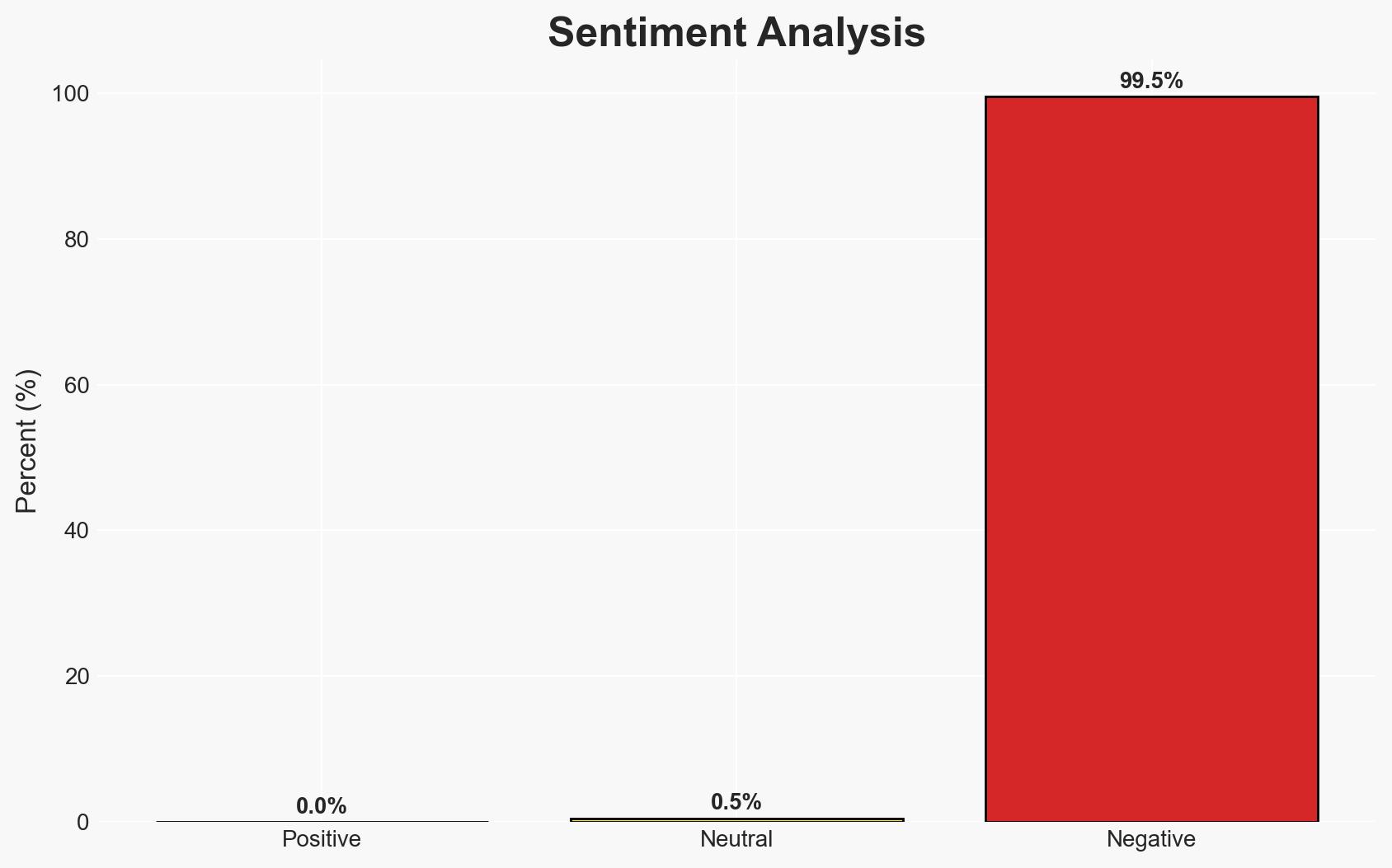
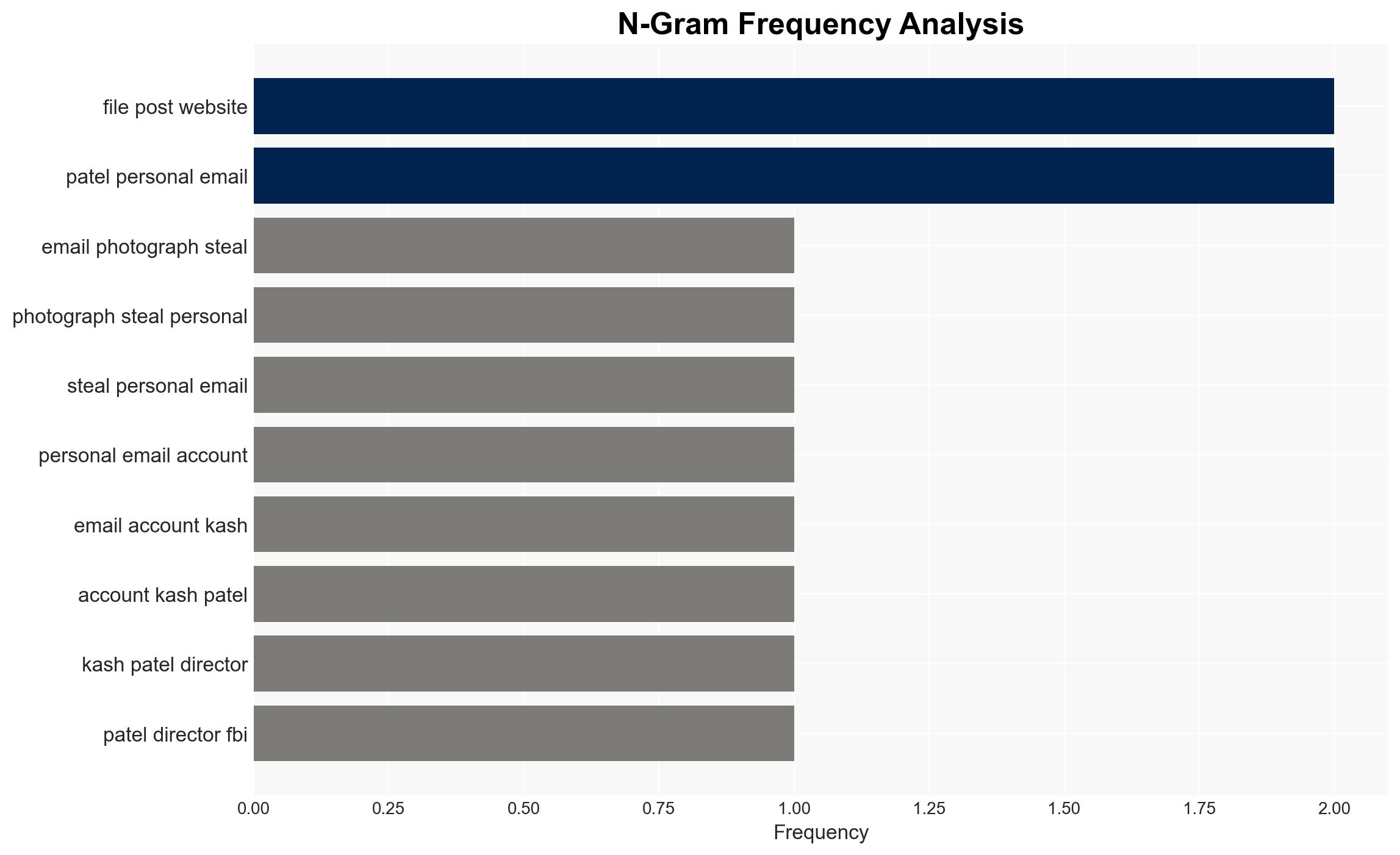
The hacking and subsequent release of personal emails belonging to FBI Director Kash Patel, attributed to a group allegedly linked to Iranian intelligence, suggests a potential attempt to embarrass U.S. leadership amid geopolitical tensions. The involvement of multiple international actors complicates attribution. This assessment is made with moderate confidence due to the presence of conflicting indicators and information gaps.
2. Competing Hypotheses
- Hypothesis A: The Handala Team, affiliated with Iranian intelligence, conducted the hack to undermine U.S. credibility and sow discord. Supporting evidence includes the group’s known history of targeting U.S. officials and the geopolitical context. Contradicting evidence includes the hosting of the website on Russian servers, which could suggest misdirection.
- Hypothesis B: The operation was conducted by a third-party actor, possibly Russian, using the guise of an Iranian group to obscure true attribution and exploit geopolitical tensions. Supporting evidence includes the Russian server hosting and historical context of Russian hack-and-dump operations. Lack of direct evidence linking Russian actors to this specific event contradicts this hypothesis.
- Assessment: Hypothesis A is currently better supported due to the direct claim of responsibility by the Handala Team and their known affiliations. However, indicators such as server location and domain registration suggest potential misdirection, warranting further investigation.
3. Key Assumptions and Red Flags
- Assumptions: The Handala Team is genuinely affiliated with Iranian intelligence; the hack was politically motivated; the server location in Russia is not coincidental.
- Information Gaps: Precise timing of the breach; confirmation of the Handala Team’s direct involvement; motivations behind using a Russian server.
- Bias & Deception Risks: Potential bias in attributing the attack to Iran without conclusive evidence; risk of deception due to the use of Russian infrastructure, which may be intended to mislead attribution.
4. Implications and Strategic Risks
This incident could exacerbate existing geopolitical tensions and influence public perception of U.S. leadership’s security posture. It may also impact ongoing cyber defense strategies and international relations.
- Political / Geopolitical: Potential for increased tensions between the U.S. and Iran, with possible diplomatic repercussions.
- Security / Counter-Terrorism: Heightened alert for further cyber operations targeting U.S. officials, necessitating increased security measures.
- Cyber / Information Space: Risk of further leaks and misinformation campaigns, requiring robust cyber defense and information integrity efforts.
- Economic / Social: Limited direct economic impact, but potential for social unrest if public confidence in government cybersecurity is undermined.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber threats related to U.S.-Iran relations; increase security for personal accounts of high-ranking officials; engage with international partners for intelligence sharing.
- Medium-Term Posture (1–12 months): Develop resilience measures against similar cyber threats; strengthen partnerships with allies to counteract misinformation and cyber operations.
- Scenario Outlook:
- Best Case: Attribution clarifies, leading to diplomatic resolution and improved cyber defenses.
- Worst Case: Escalation of cyber operations and geopolitical tensions, potentially leading to broader conflict.
- Most-Likely: Continued cyber skirmishes with periodic escalations, necessitating ongoing vigilance and strategic responses.
6. Key Individuals and Entities
- Kash Patel – Director of the FBI
- Handala Team – Pro-Iranian hacktivist group
- Ben Williamson – FBI spokesperson
- Not clearly identifiable from open sources in this snippet for other involved entities.
7. Thematic Tags
cybersecurity, cyber-espionage, geopolitical tensions, information security, Iran-U.S. relations, hack-and-leak operations, attribution challenges, misinformation
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us