Cyber Warfare Escalates: Iran’s Spyware Tactics Target Israelis Amid Missile Strikes
Published on: 2026-03-29
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Hacked hospitals hidden spyware Israel-Iran conflict shows how digital fight is ingrained in warfare
1. BLUF (Bottom Line Up Front)
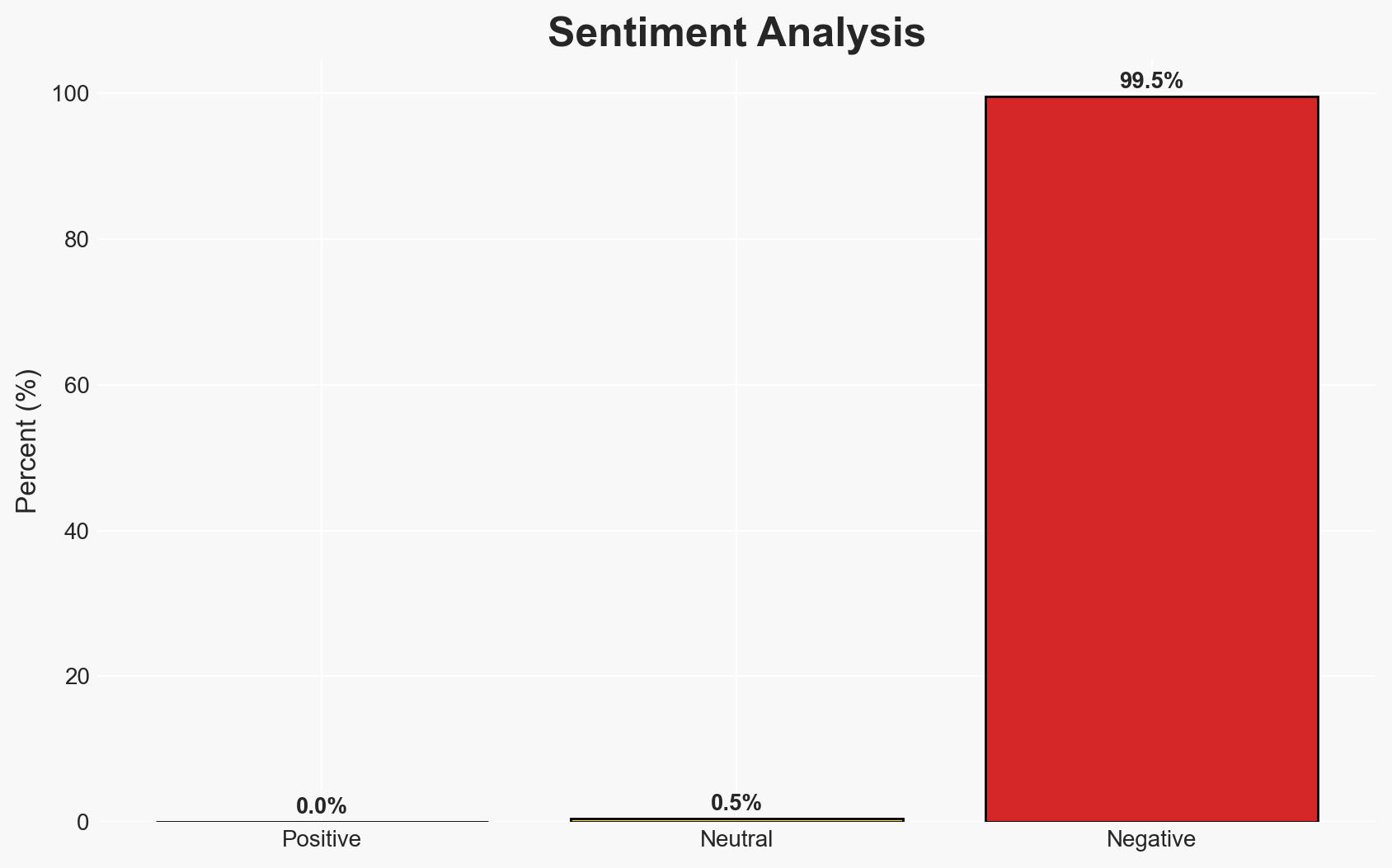
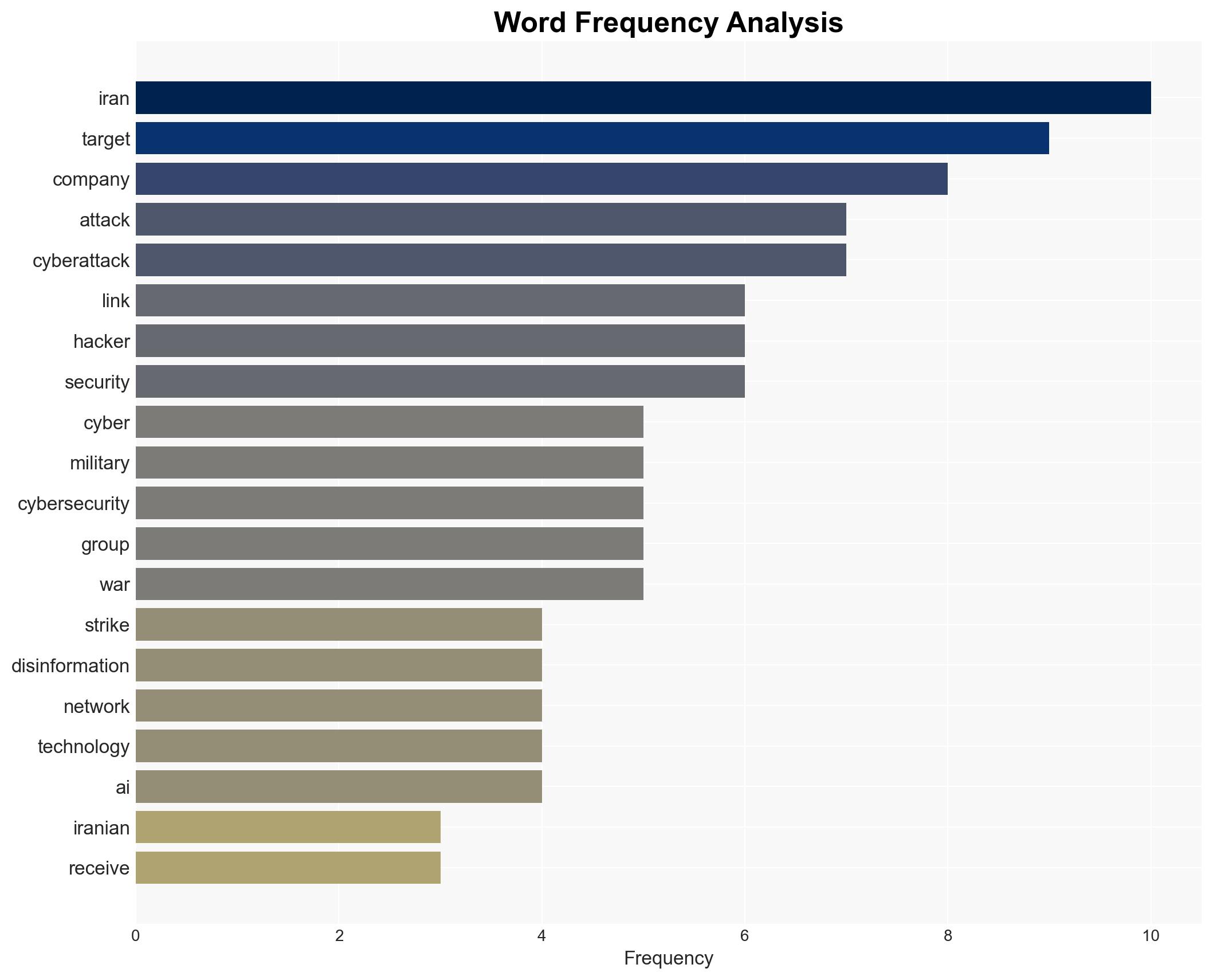
The ongoing cyber conflict between Iran and Israel, exemplified by recent spyware attacks on Israeli civilians, highlights the integration of cyber operations into modern warfare. This conflict is characterized by high-volume, low-impact cyberattacks that aim to disrupt and intimidate rather than cause physical harm. The primary hypothesis is that Iran is leveraging cyber capabilities to compensate for conventional military disadvantages. This assessment is made with moderate confidence due to the sophistication and timing of the attacks.
2. Competing Hypotheses
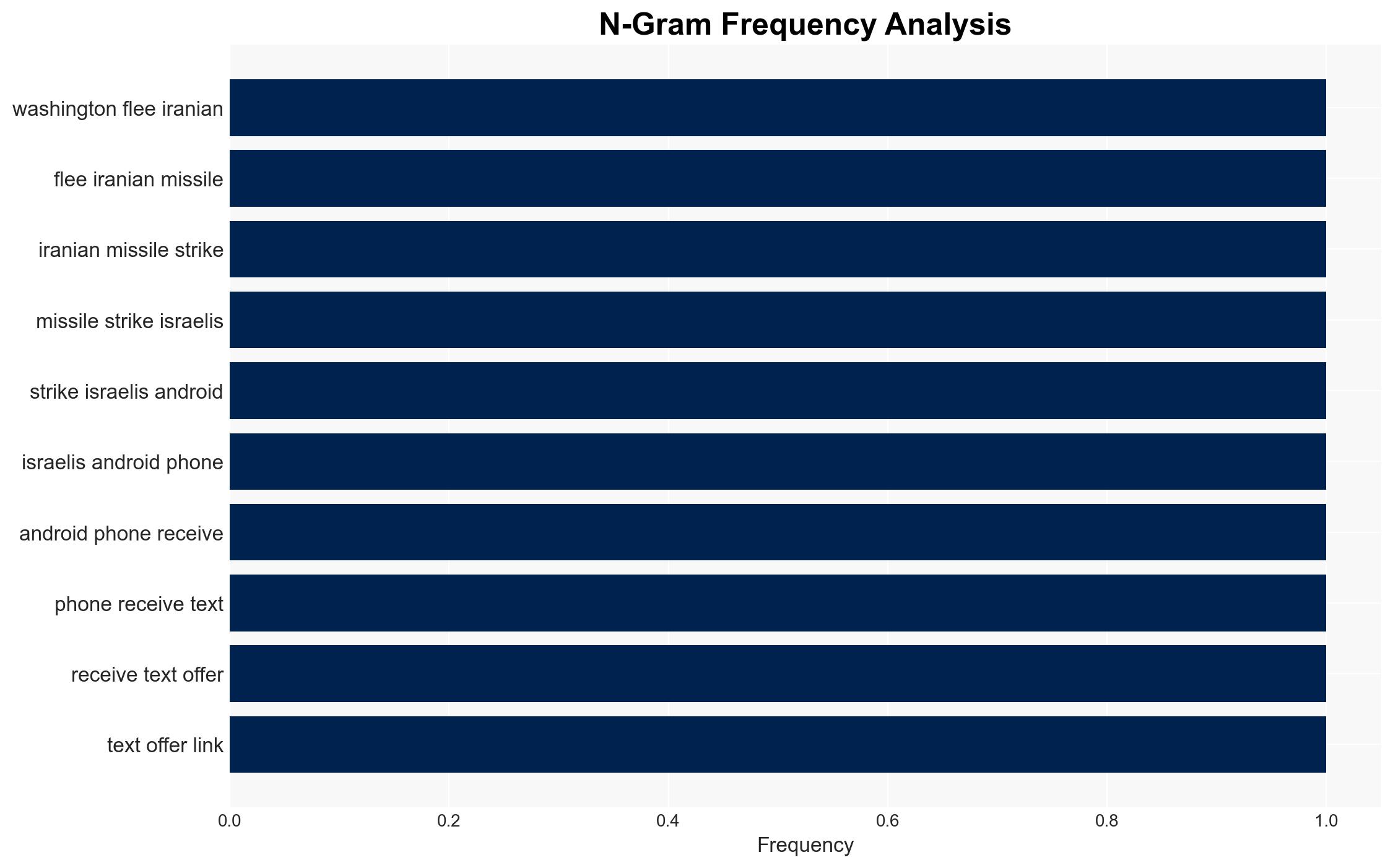
- Hypothesis A: Iran is using cyber operations as a strategic tool to offset its military limitations, focusing on psychological and informational impacts. This is supported by the sophisticated coordination of cyber and physical attacks, such as the spyware linked to missile strikes. However, the full extent of Iran’s cyber capabilities remains uncertain.
- Hypothesis B: The cyber operations are primarily intended to boost domestic and regional morale among Iran’s supporters, rather than achieve strategic military objectives. This is supported by the low-impact nature of many attacks and the focus on symbolic targets. Contradicting this is the strategic timing and coordination with physical attacks.
- Assessment: Hypothesis A is currently better supported due to the evidence of coordinated cyber and physical operations, indicating a strategic intent beyond mere morale boosting. Indicators such as increased sophistication or targeting of critical infrastructure could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Iran’s cyber capabilities are sufficiently advanced to coordinate with physical military operations; Israel and the U.S. remain primary targets; cyber operations are cost-effective for Iran.
- Information Gaps: Detailed understanding of Iran’s cyber infrastructure and command structure; the extent of coordination between Iranian state and proxy actors.
- Bias & Deception Risks: Potential overestimation of Iran’s capabilities due to limited visibility into unsuccessful attacks; possible manipulation of public perception by both Iranian and Israeli sources.
4. Implications and Strategic Risks
This development could lead to an escalation in cyber operations, potentially involving more critical infrastructure and broader geopolitical tensions.
- Political / Geopolitical: Increased tensions between Iran and Israel, with potential spillover effects in the broader Middle East region.
- Security / Counter-Terrorism: Heightened threat environment for Israeli and U.S. entities, necessitating increased cybersecurity measures.
- Cyber / Information Space: Potential for more sophisticated cyber operations, including disinformation campaigns targeting public trust.
- Economic / Social: Increased cybersecurity costs for businesses and potential disruptions to economic activities, particularly in sectors linked to national security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber threats, particularly those targeting critical infrastructure; increase public awareness and readiness for potential cyber incidents.
- Medium-Term Posture (1–12 months): Strengthen international partnerships for cybersecurity intelligence sharing; invest in resilience measures for critical sectors.
- Scenario Outlook:
- Best: De-escalation of cyber activities through diplomatic engagement, indicated by a reduction in attack frequency.
- Worst: Escalation to critical infrastructure attacks, potentially triggering broader regional conflict.
- Most-Likely: Continued low-impact cyber operations with periodic spikes in activity, driven by geopolitical events.
6. Key Individuals and Entities
- Gil Messing, Chief of Staff at Check Point Research
- Michael Smith, Field Chief Technology Officer at DigiCert
- Pro-Iranian hacking groups (specific names not clearly identifiable from open sources in this snippet)
7. Thematic Tags
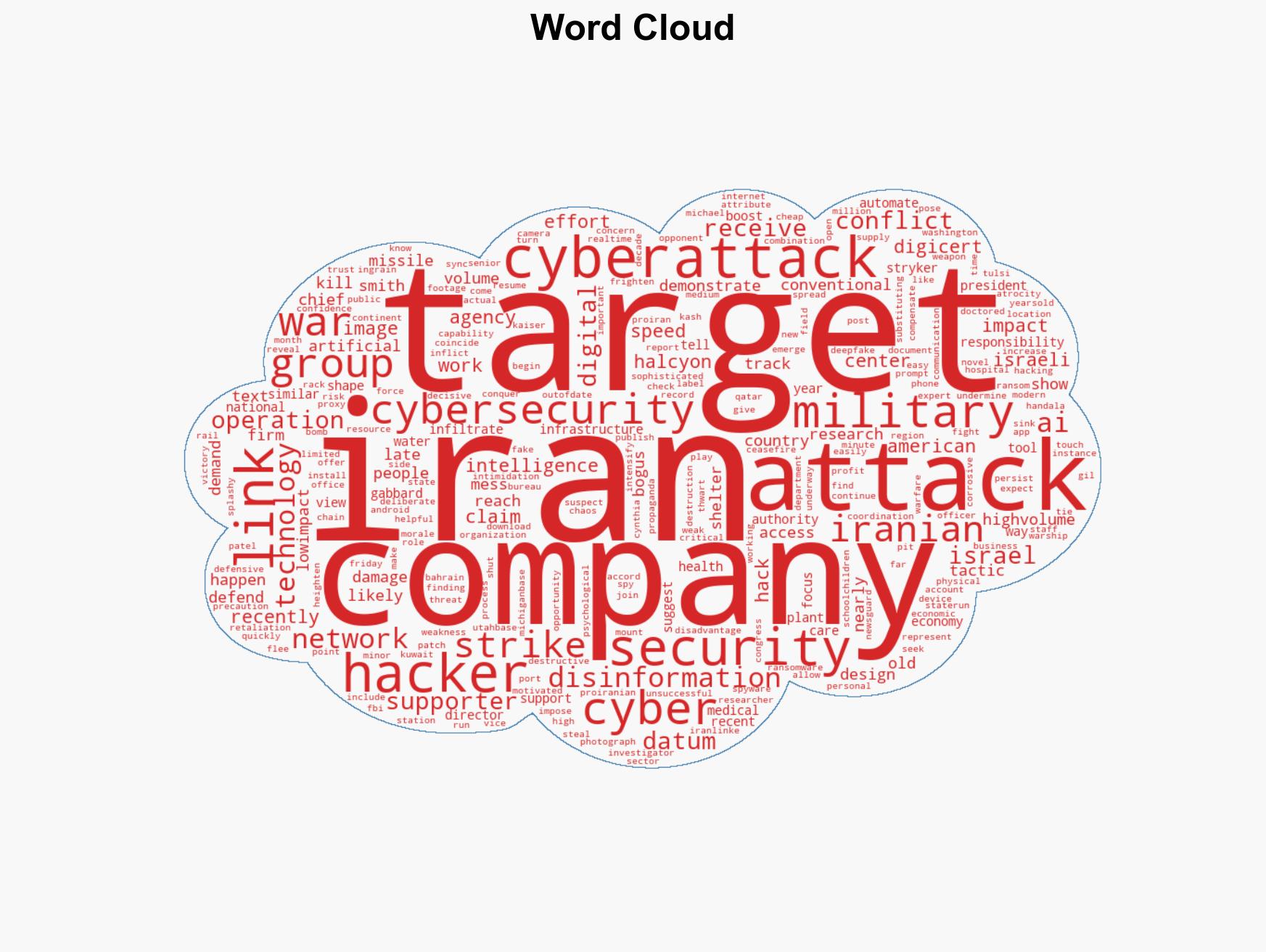
cybersecurity, cyber warfare, Iran-Israel conflict, cyber espionage, psychological operations, information warfare, regional security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us