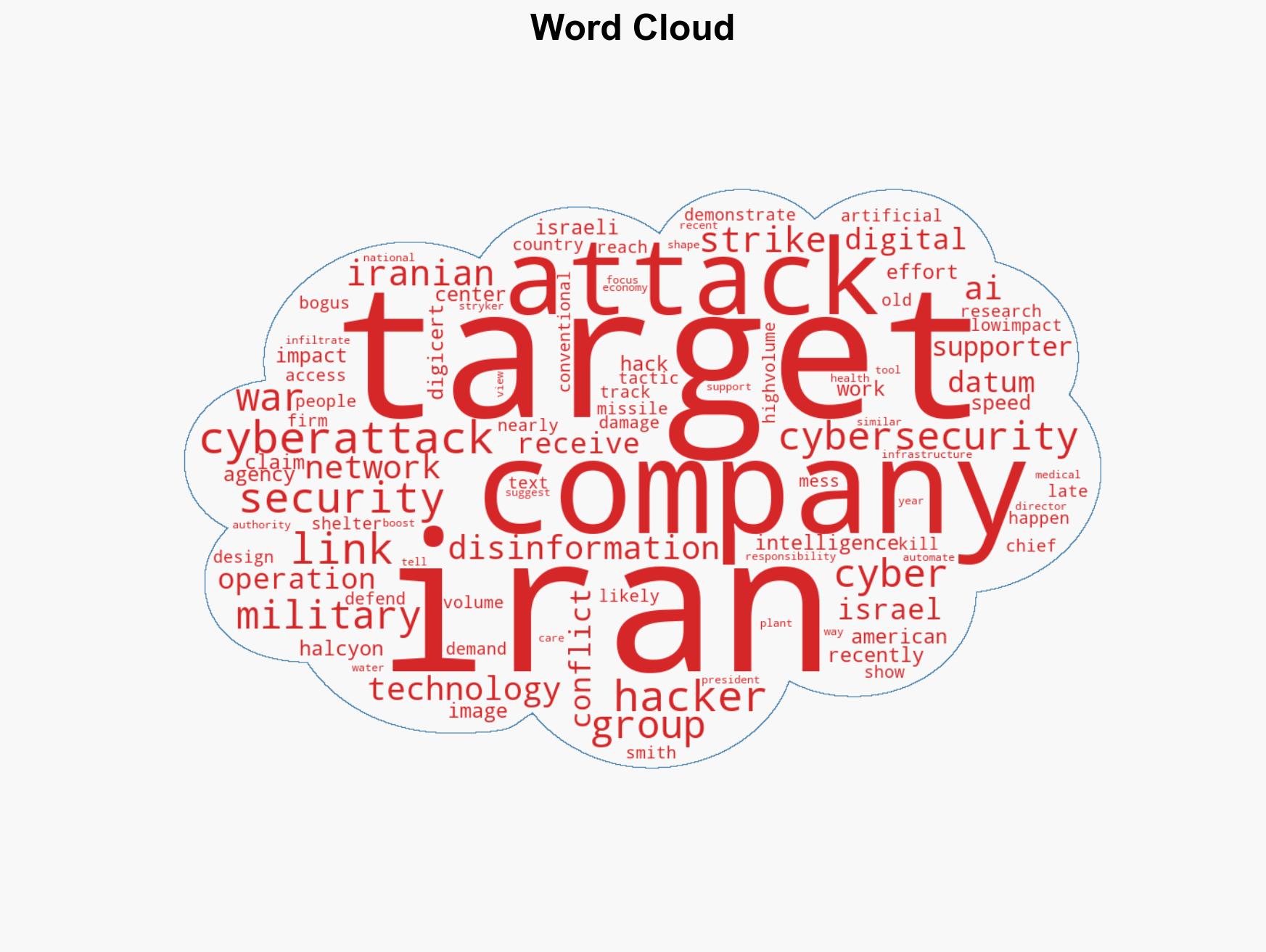
Iran’s Cyber Tactics: Spyware Targeting Israelis Amid Missile Strikes Highlights Digital Warfare Evolution
Published on: 2026-03-29
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Hacked hospitals hidden spyware Iran conflict shows how digital fight is ingrained in warfare
1. BLUF (Bottom Line Up Front)
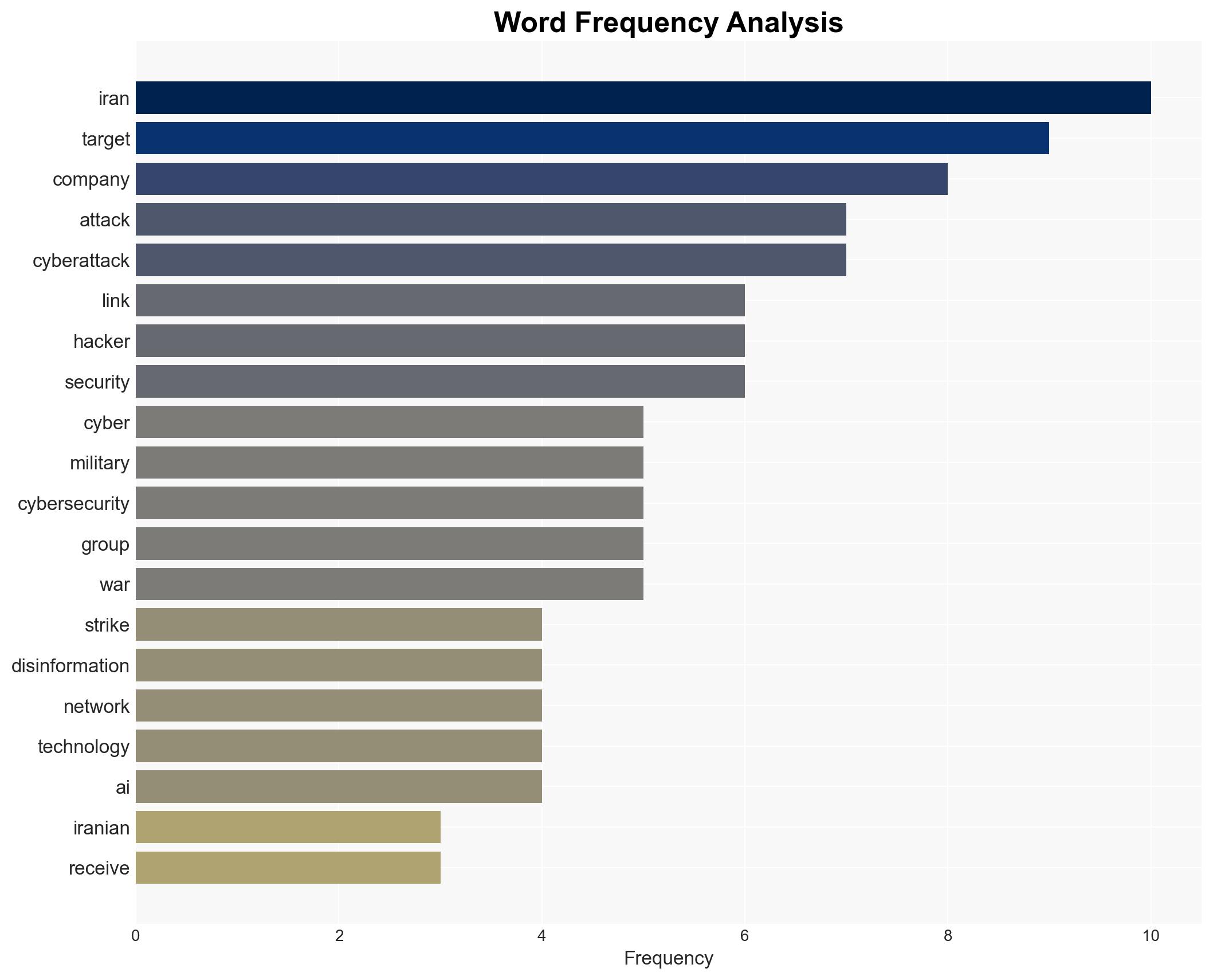
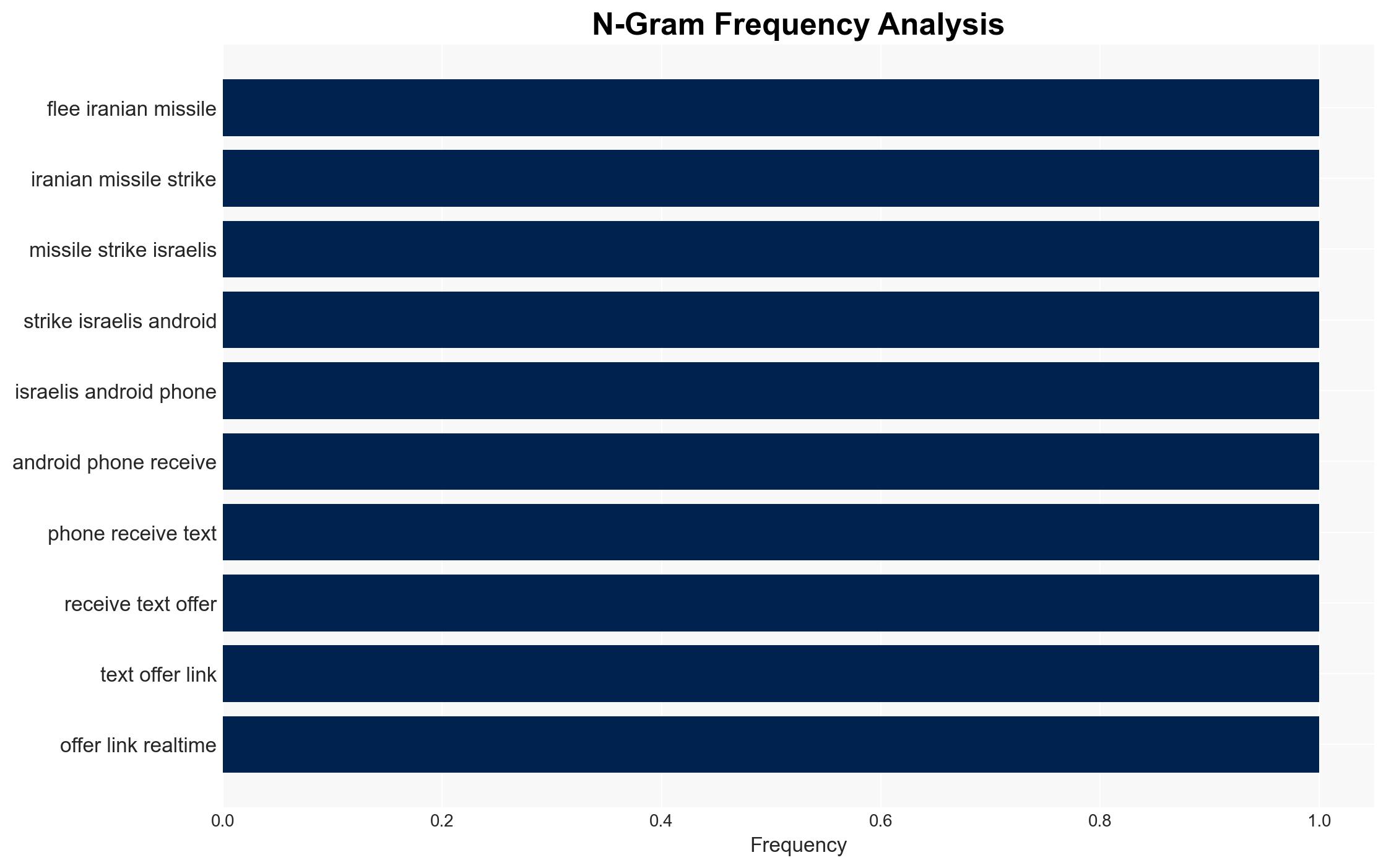
The recent cyber operation attributed to Iran, involving spyware disguised as bomb shelter information during missile strikes, highlights the integration of digital tactics in modern warfare. This development affects US and Israeli entities and demonstrates Iran’s strategic use of cyber capabilities to offset military disadvantages. The overall confidence level in this assessment is moderate.
2. Competing Hypotheses
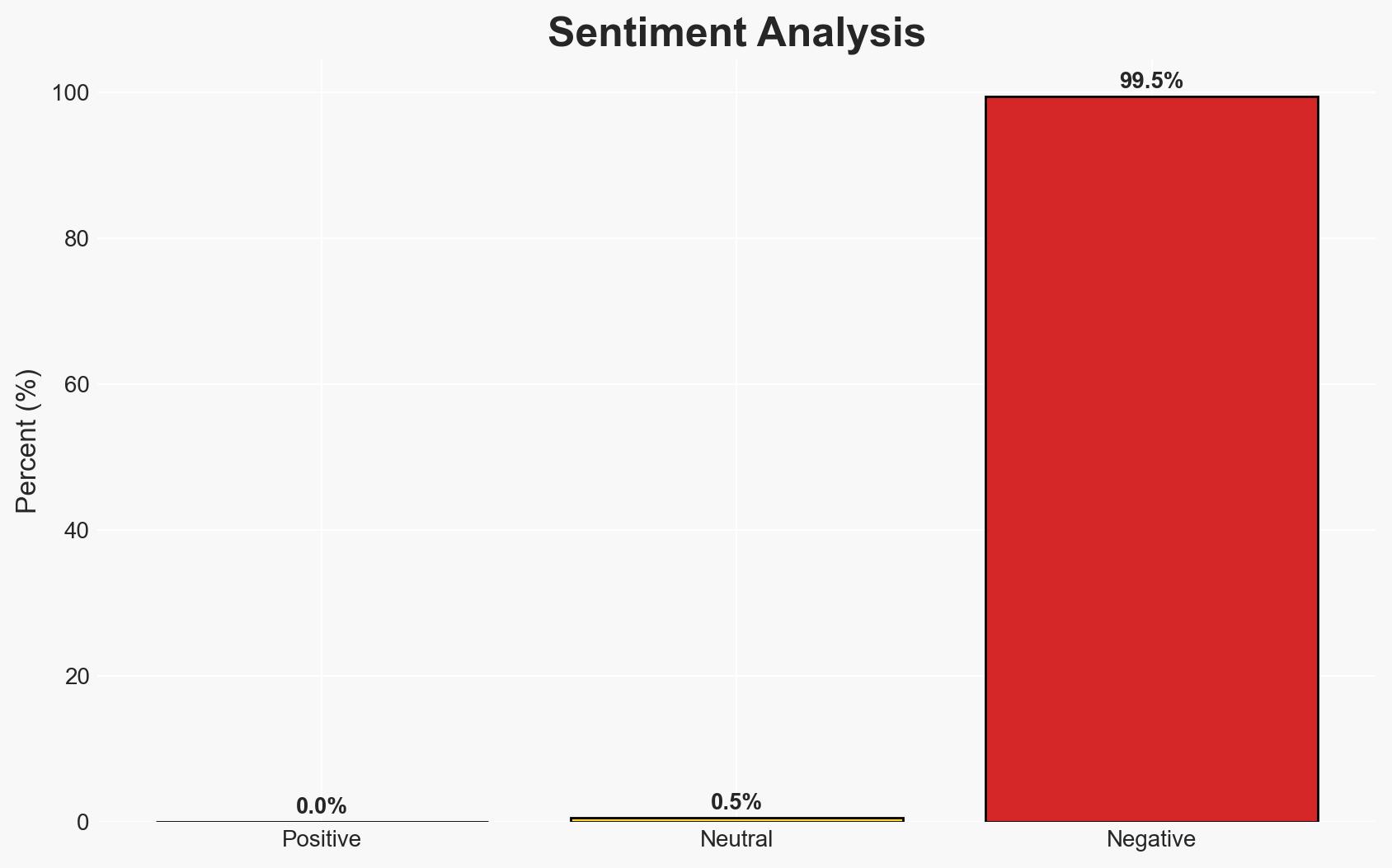
- Hypothesis A: Iran is using cyber operations as a strategic tool to compensate for conventional military weaknesses. This is supported by the timing of the spyware attack with missile strikes and the volume of cyberattacks attributed to Iran. However, the sophistication of these attacks varies, and many are low-impact.
- Hypothesis B: The cyber operations are primarily psychological operations aimed at boosting morale among Iranian supporters and undermining confidence in US and Israeli defenses. This is supported by the splashy nature of some attacks, such as the infiltration of an FBI Director’s account, which may not have significant operational impact but serves propaganda purposes.
- Assessment: Hypothesis A is currently better supported due to the coordinated nature of the cyber and physical attacks, indicating a strategic intent beyond mere psychological operations. Key indicators that could shift this judgment include evidence of increased sophistication or impact of attacks, or a shift in target selection towards more strategic assets.
3. Key Assumptions and Red Flags
- Assumptions: Iran has the capability and intent to conduct coordinated cyber operations; US and Israeli defenses are generally robust but have exploitable vulnerabilities; cyber operations are a cost-effective means for Iran to exert influence.
- Information Gaps: Detailed attribution of specific cyber operations to Iranian state actors; comprehensive impact assessments of the cyber operations on targeted entities.
- Bias & Deception Risks: Potential confirmation bias in attributing all cyber operations to Iran; possibility of false flag operations by other actors to escalate tensions.
4. Implications and Strategic Risks
The integration of cyber tactics in the Iran-Israel conflict could lead to a prolonged digital confrontation, affecting regional stability and international relations.
- Political / Geopolitical: Escalation of cyber operations could lead to broader geopolitical tensions, involving allies and adversaries in the region.
- Security / Counter-Terrorism: Increased cyber threats may necessitate enhanced security measures and collaboration among affected nations.
- Cyber / Information Space: The conflict underscores the need for robust cybersecurity frameworks and real-time threat intelligence sharing.
- Economic / Social: Persistent cyber threats could disrupt economic activities and erode public trust in digital infrastructures.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber threats, patch known vulnerabilities, and increase public awareness of phishing tactics.
- Medium-Term Posture (1–12 months): Develop resilience measures through international partnerships, invest in cybersecurity capabilities, and conduct regular threat assessments.
- Scenario Outlook:
- Best: De-escalation of cyber operations with diplomatic engagement.
- Worst: Intensification of cyber and physical attacks leading to regional instability.
- Most-Likely: Continued low-level cyber operations with periodic spikes in activity.
6. Key Individuals and Entities
- Gil Messing, Check Point Research
- Michael Smith, DigiCert
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cyber warfare, Iran-Israel conflict, digital espionage, psychological operations, regional stability, cyber defense
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us