India Enhances Cybersecurity Measures Amid Rising Threats to Critical Infrastructure
Published on: 2026-03-31
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
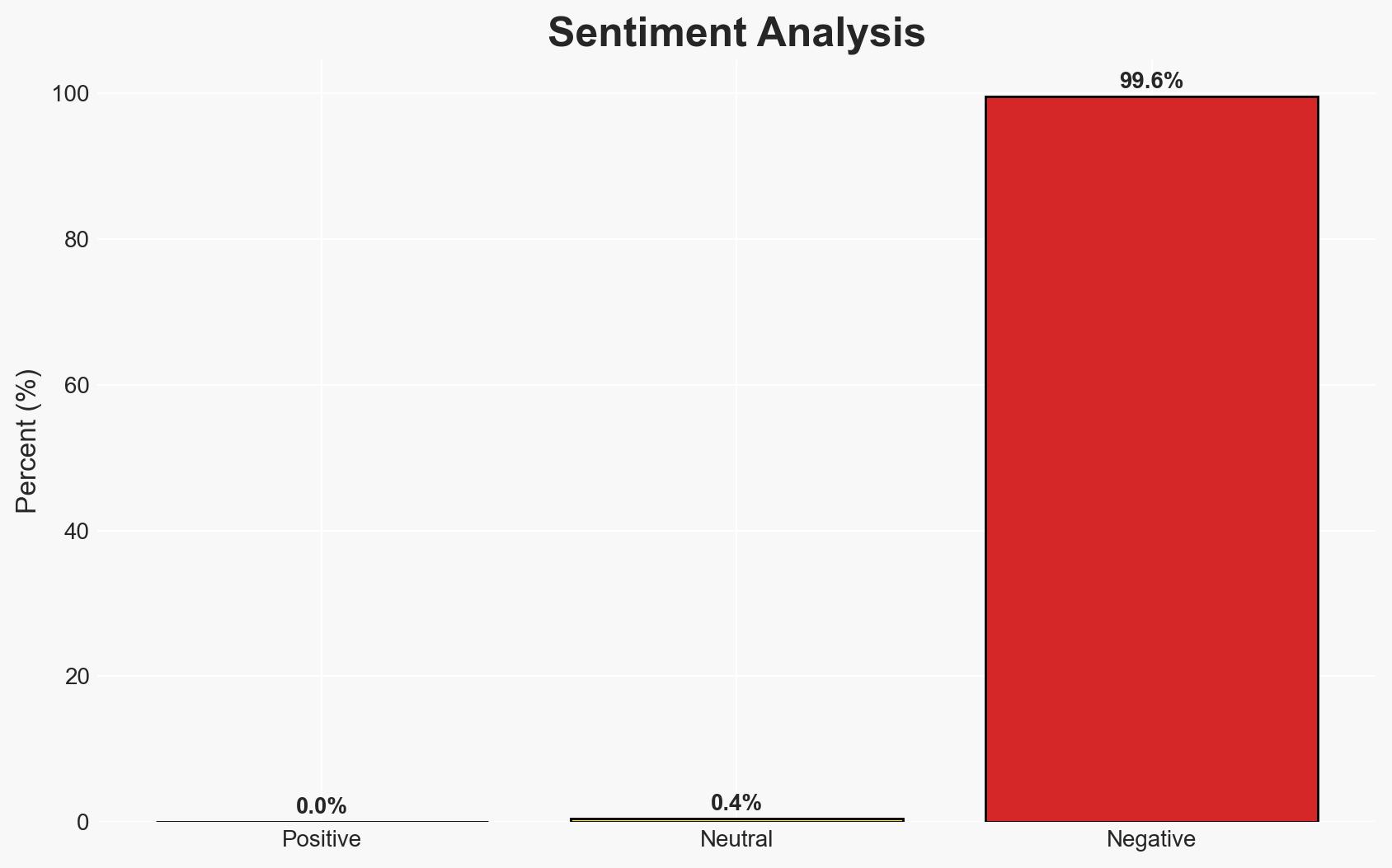
Intelligence Report: Cyber pirates at large India readies moats
1. BLUF (Bottom Line Up Front)
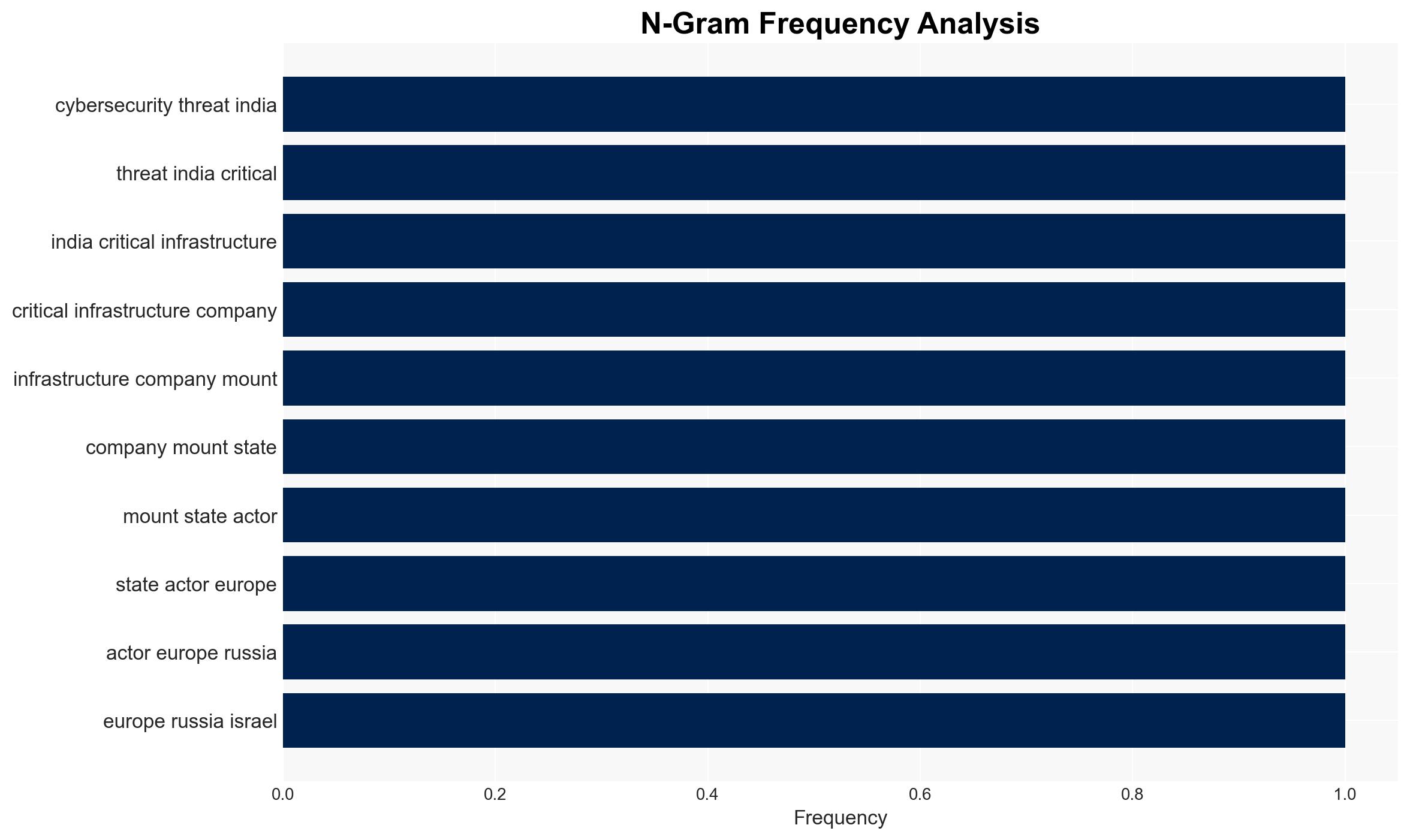
India’s critical infrastructure is increasingly vulnerable to cyber threats from state and non-state actors, with potential implications for national security and economic stability. The most likely hypothesis is that these threats are part of a broader strategy by hostile states to exploit vulnerabilities for strategic gain. This assessment is made with moderate confidence, given the current evidence and ongoing geopolitical tensions.
2. Competing Hypotheses
- Hypothesis A: The cyber threats are primarily state-sponsored efforts aimed at espionage and potential disruption of India’s critical infrastructure. This is supported by the involvement of known APT groups and the geopolitical context, but lacks detailed attribution to specific states.
- Hypothesis B: The threats are opportunistic actions by independent cybercriminal groups seeking financial gain through ransomware and data theft. While possible, this is less supported due to the strategic nature of the targets and the involvement of state-linked entities.
- Assessment: Hypothesis A is currently better supported due to the strategic targeting of critical infrastructure and the involvement of state-linked APT groups. Future attribution of specific attacks to state actors or a shift in target selection could alter this assessment.
3. Key Assumptions and Red Flags
- Assumptions: State actors have the capability and intent to target India’s infrastructure; current geopolitical tensions increase the likelihood of cyber operations; India’s legacy systems are vulnerable to sophisticated attacks.
- Information Gaps: Specific attribution of attacks to particular state actors; detailed technical analysis of the cyber incidents; the full scope of vulnerabilities in India’s infrastructure.
- Bias & Deception Risks: Potential bias in attributing attacks to state actors without conclusive evidence; risk of deception through false-flag operations by cybercriminals or other states.
4. Implications and Strategic Risks
The escalation of cyber threats could lead to significant disruptions in India’s critical infrastructure, affecting national security and economic stability. The situation may evolve with increased geopolitical tensions and potential retaliatory cyber operations.
- Political / Geopolitical: Increased tensions between India and suspected state actors; potential for diplomatic confrontations or sanctions.
- Security / Counter-Terrorism: Heightened threat environment requiring enhanced defensive measures and intelligence sharing.
- Cyber / Information Space: Increased cyber defense initiatives and potential for retaliatory cyber operations by India.
- Economic / Social: Potential economic disruptions from attacks on financial and energy sectors; public concern over cybersecurity resilience.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring and incident response capabilities; conduct vulnerability assessments of critical infrastructure; increase intelligence sharing with allies.
- Medium-Term Posture (1–12 months): Develop and implement comprehensive cybersecurity strategies; invest in upgrading legacy systems; strengthen international cybersecurity partnerships.
- Scenario Outlook:
- Best: Successful mitigation of threats with minimal disruption, leading to improved cybersecurity posture.
- Worst: Major cyber incident causing significant infrastructure damage and economic loss.
- Most-Likely: Continued low-level cyber incidents with gradual improvements in defense capabilities.
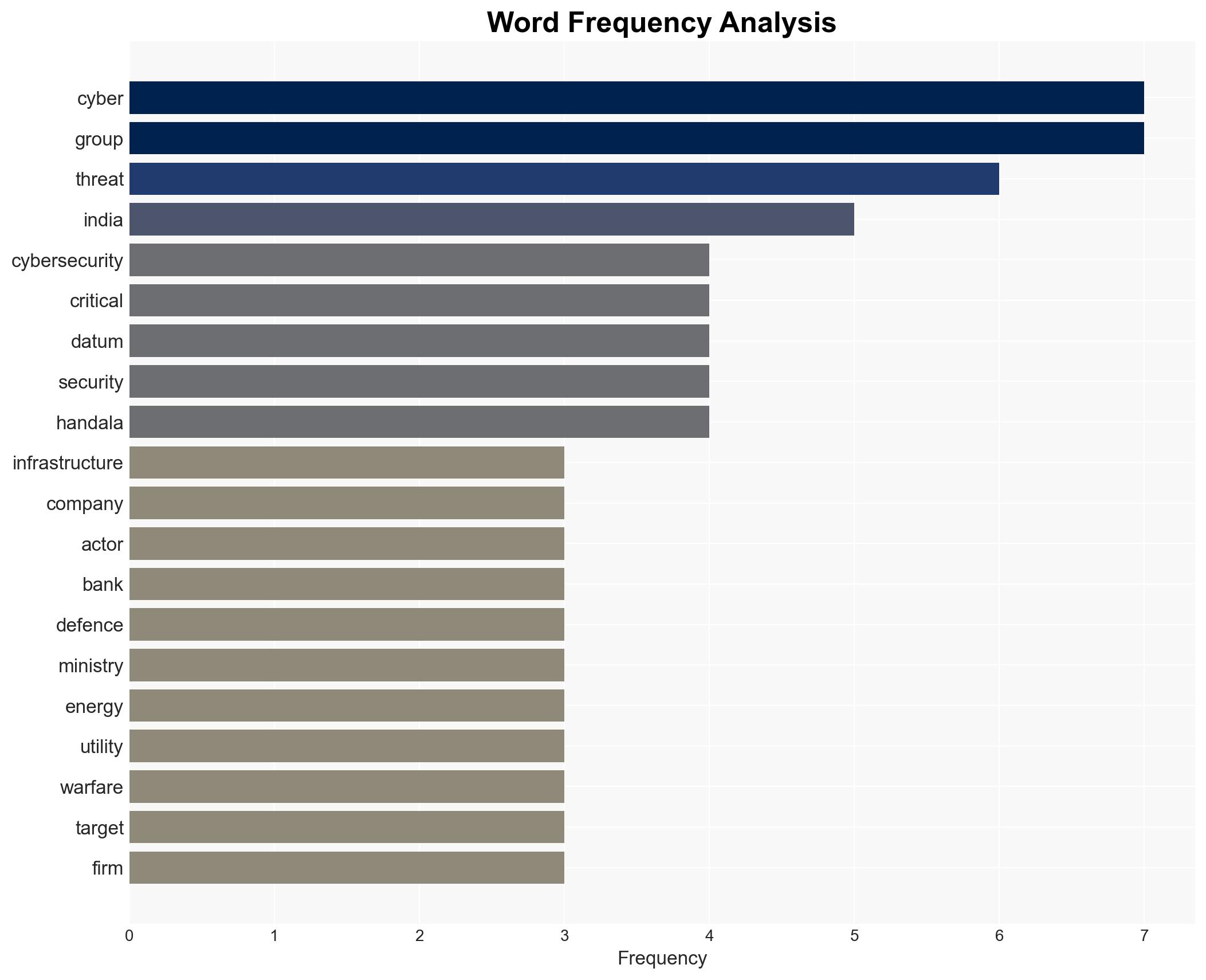
6. Key Individuals and Entities
- Indian Computer Emergency Response Team (CERT-In)
- Reserve Bank of India (RBI)
- Securities and Exchange Board of India (Sebi)
- Handala Hack Team
- Seedworm
- Seqrite
- Quick Heal Technologies
- Sundareshwar Krishnamurthy, PwC India
7. Thematic Tags
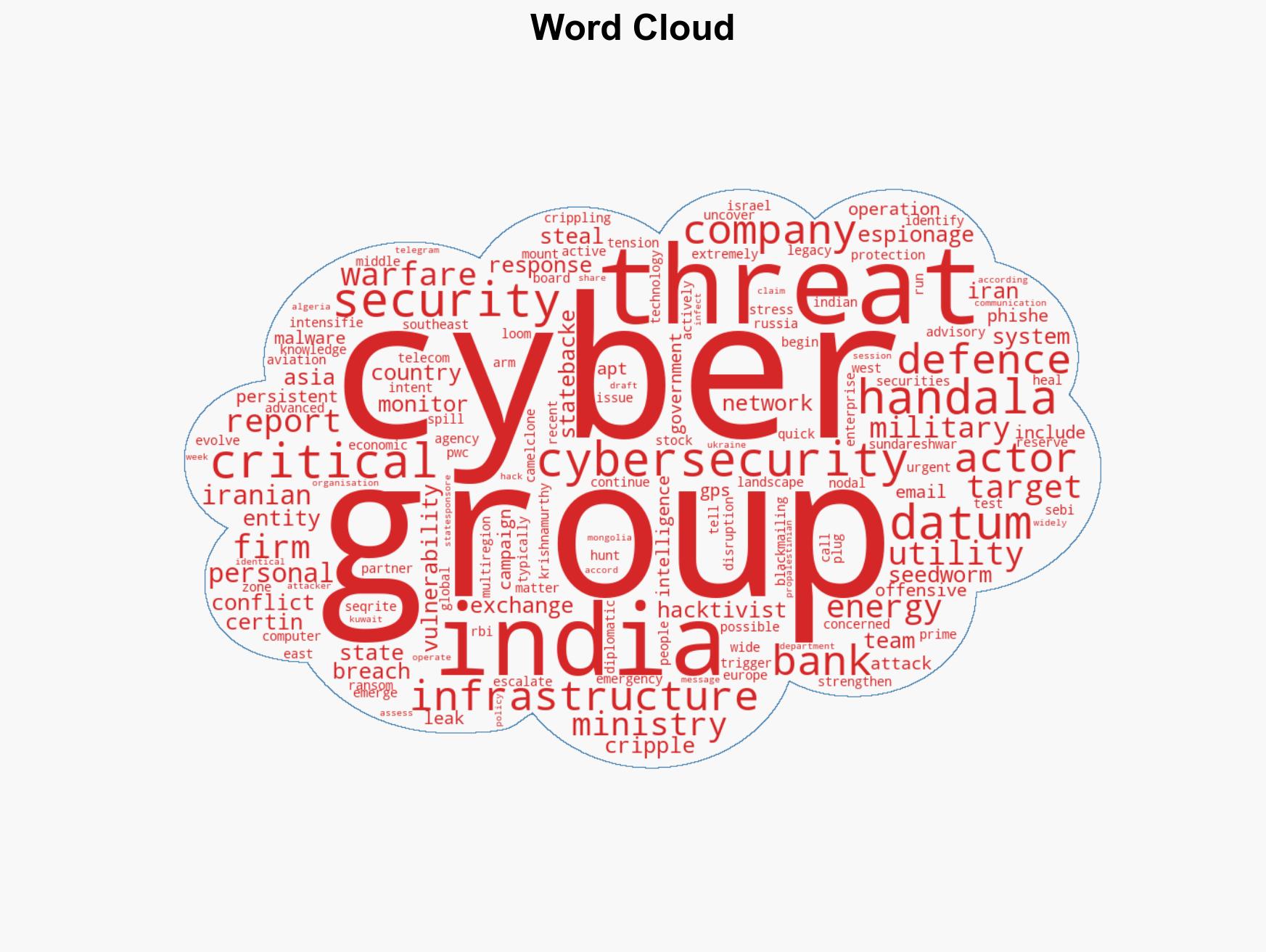
cybersecurity, state-sponsored threats, critical infrastructure, cyber espionage, geopolitical tensions, APT groups, cyber warfare
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us